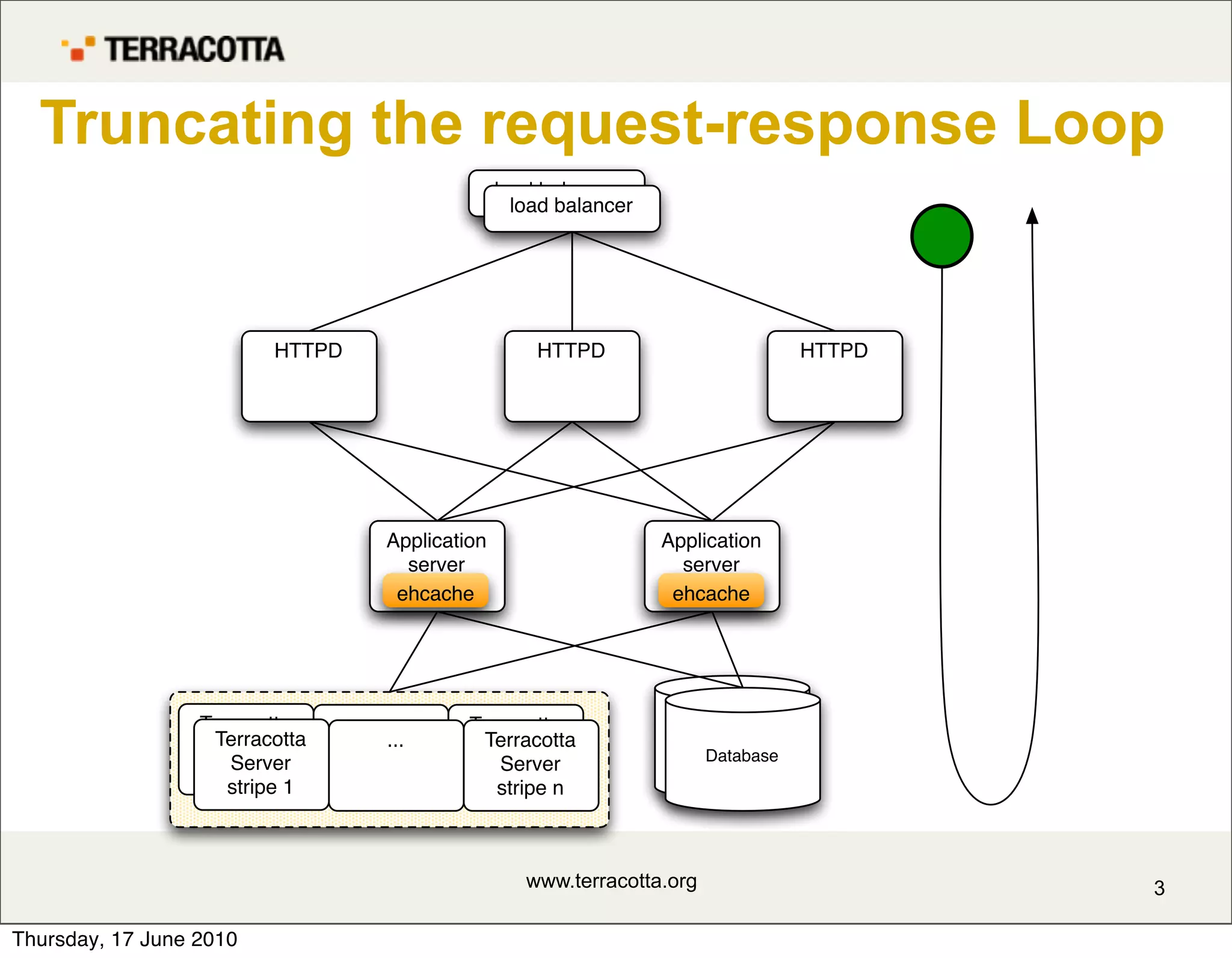
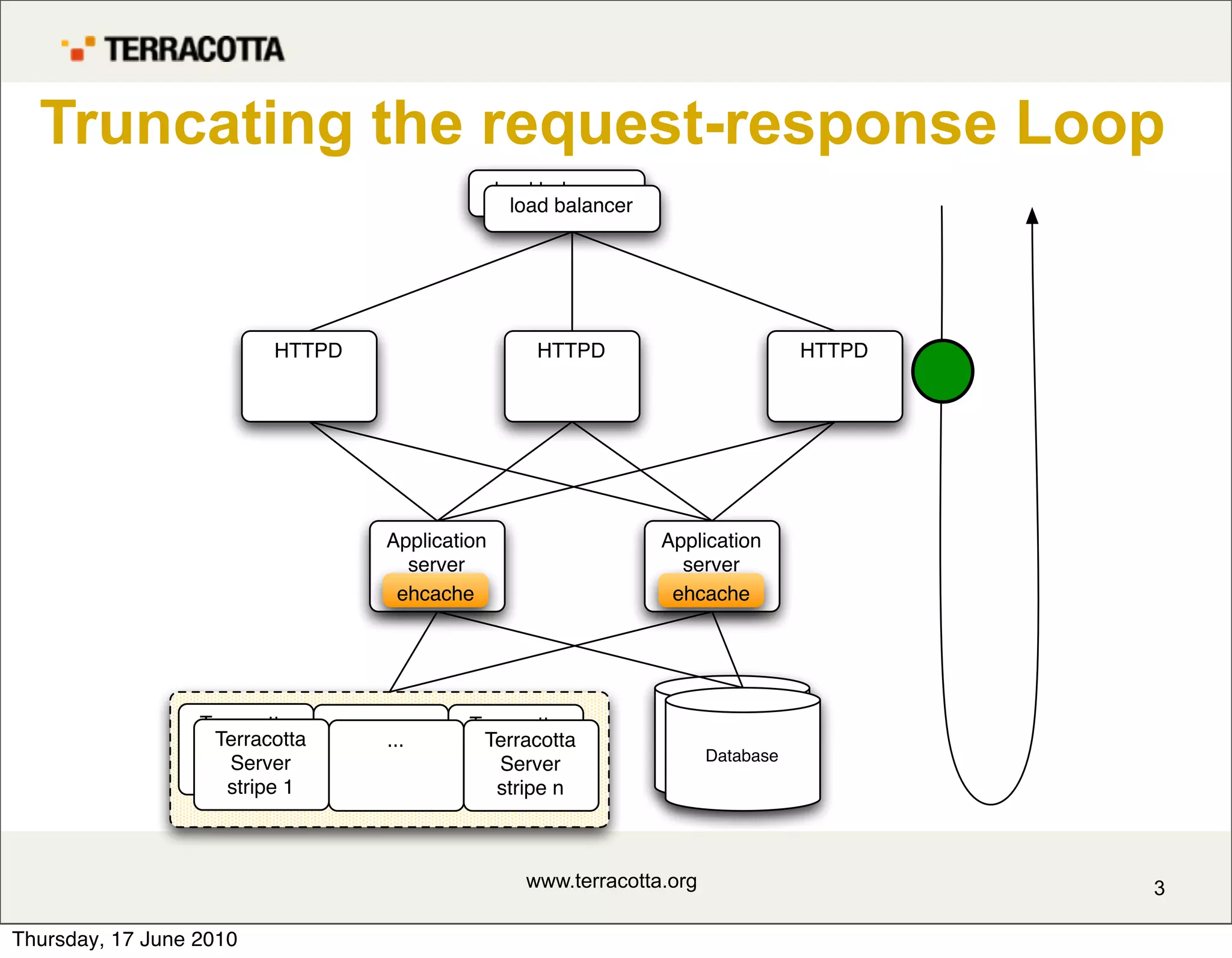
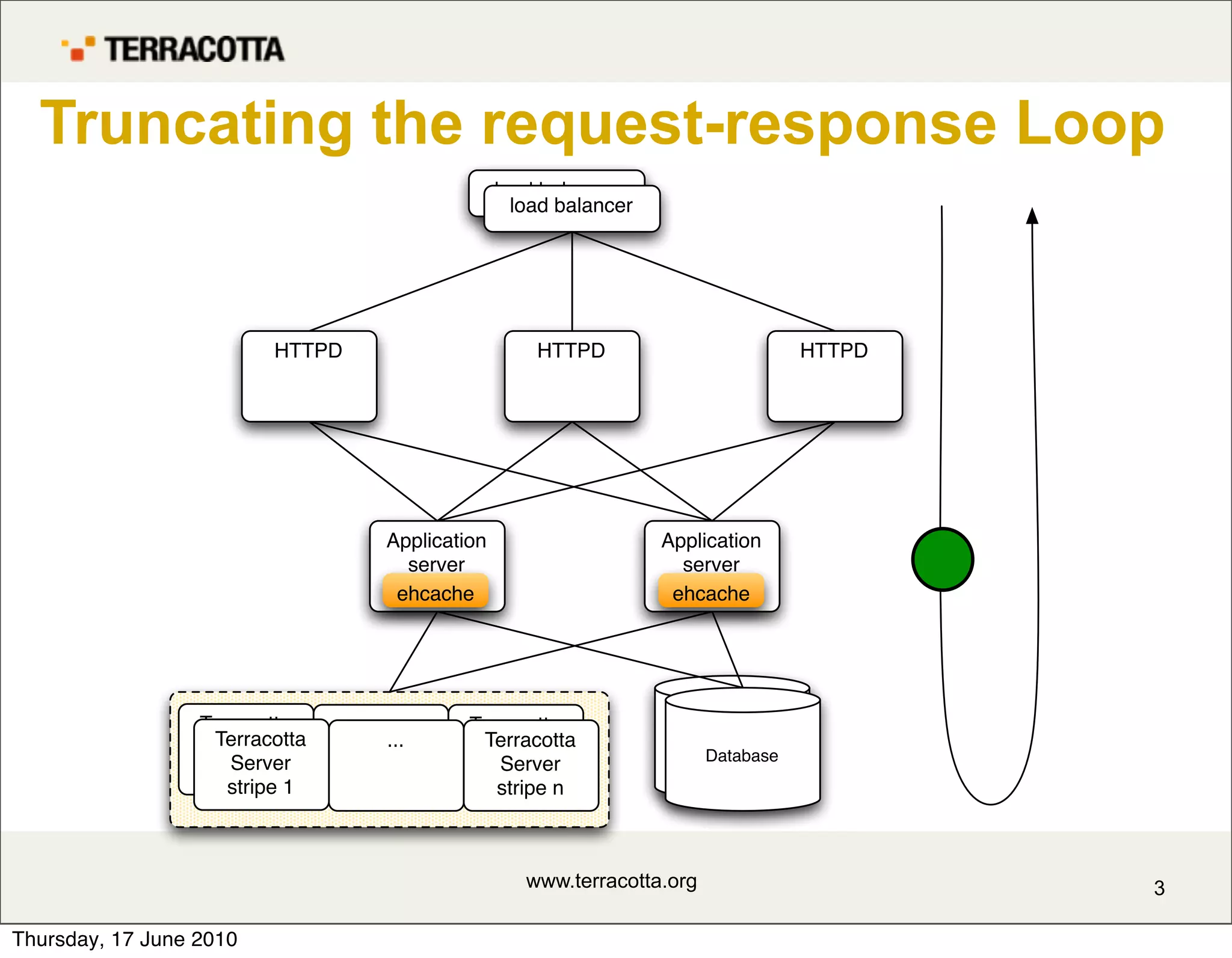
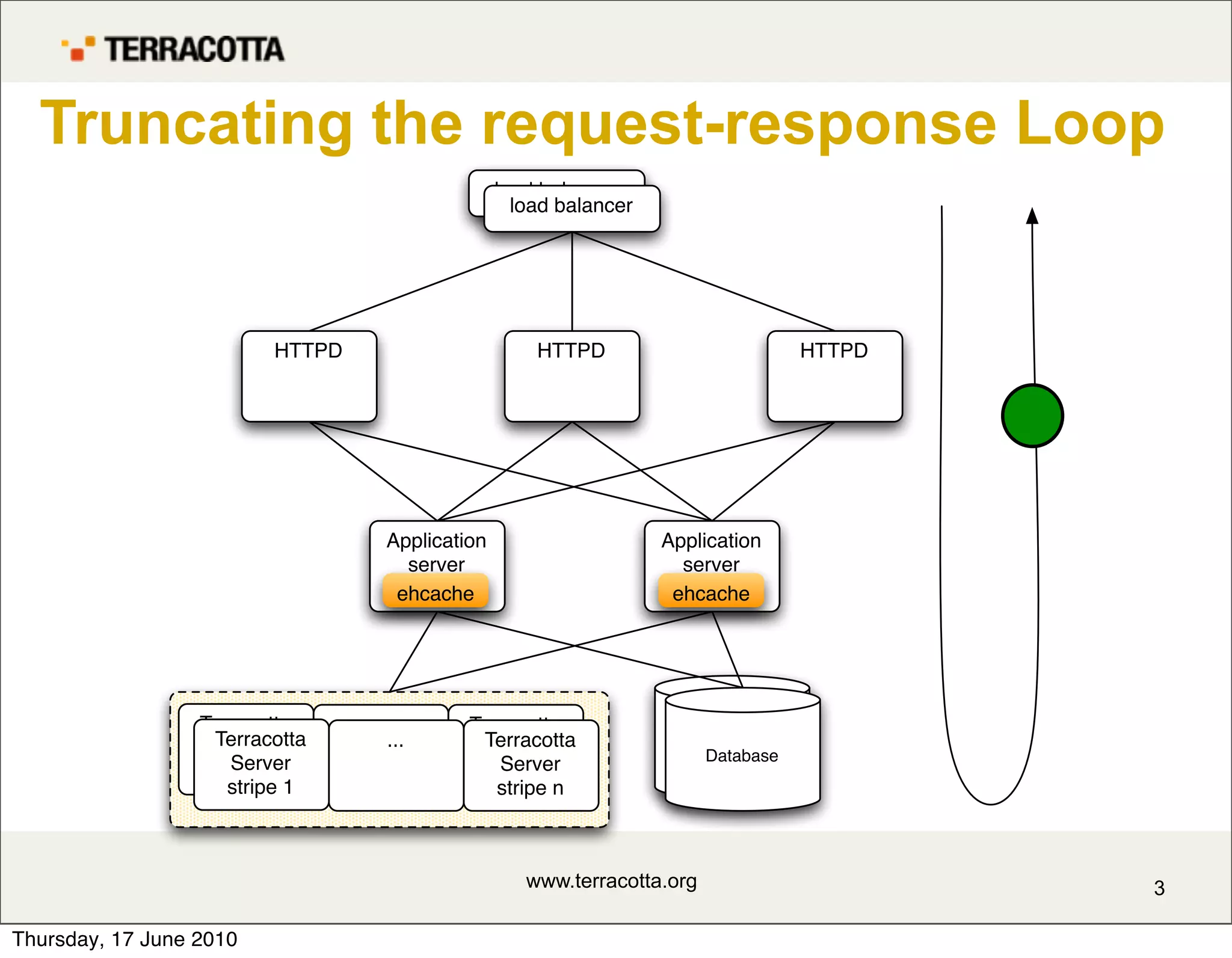
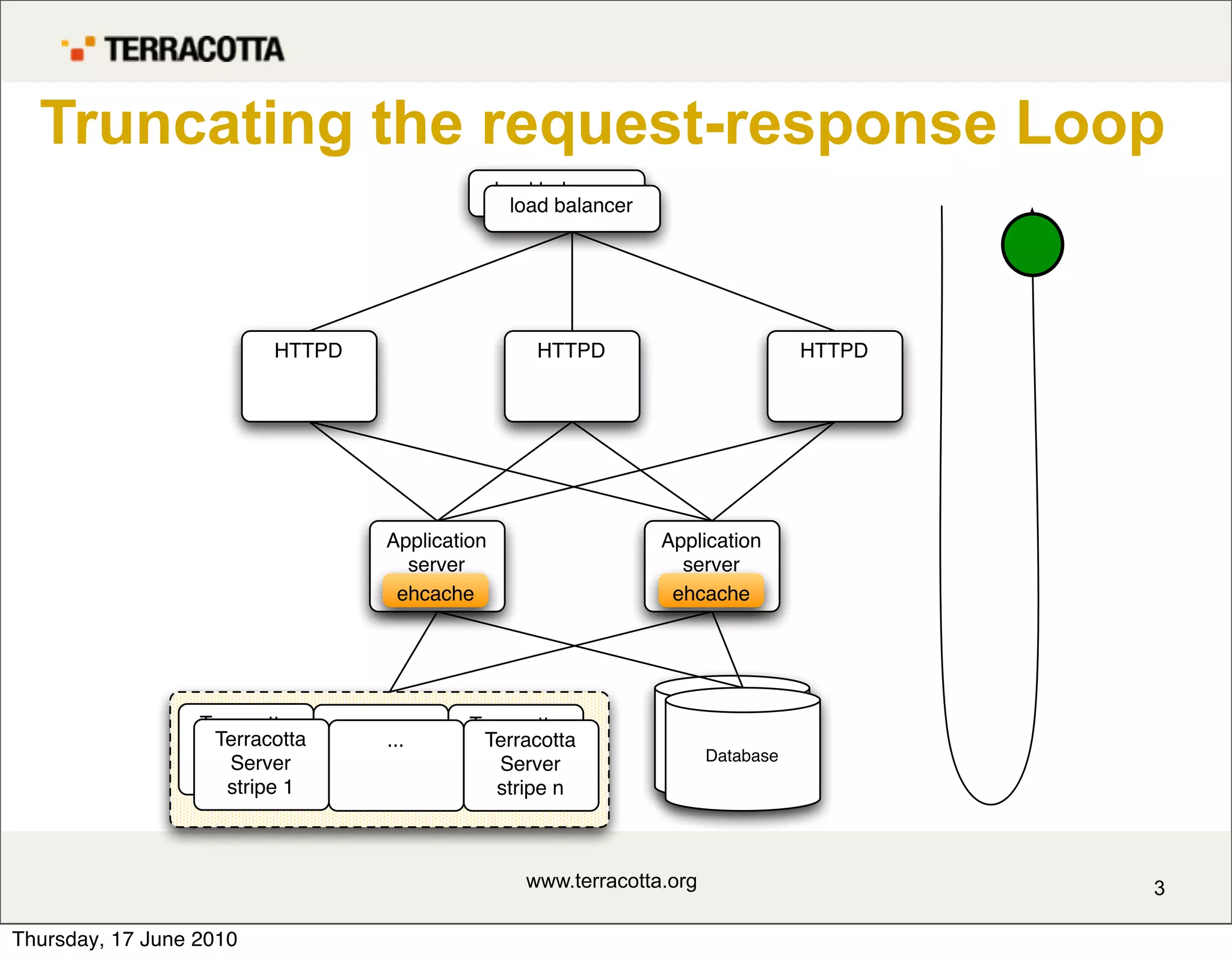
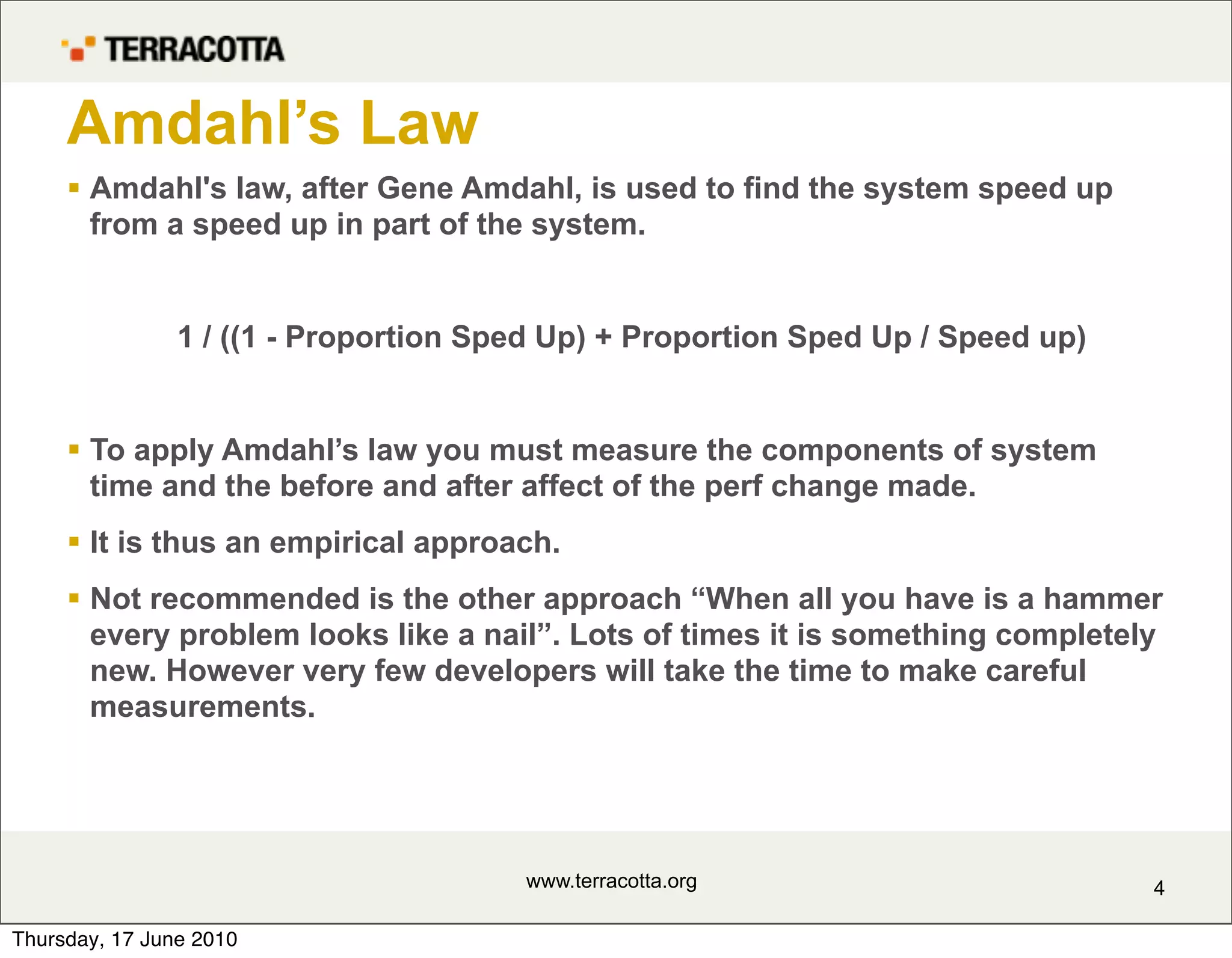
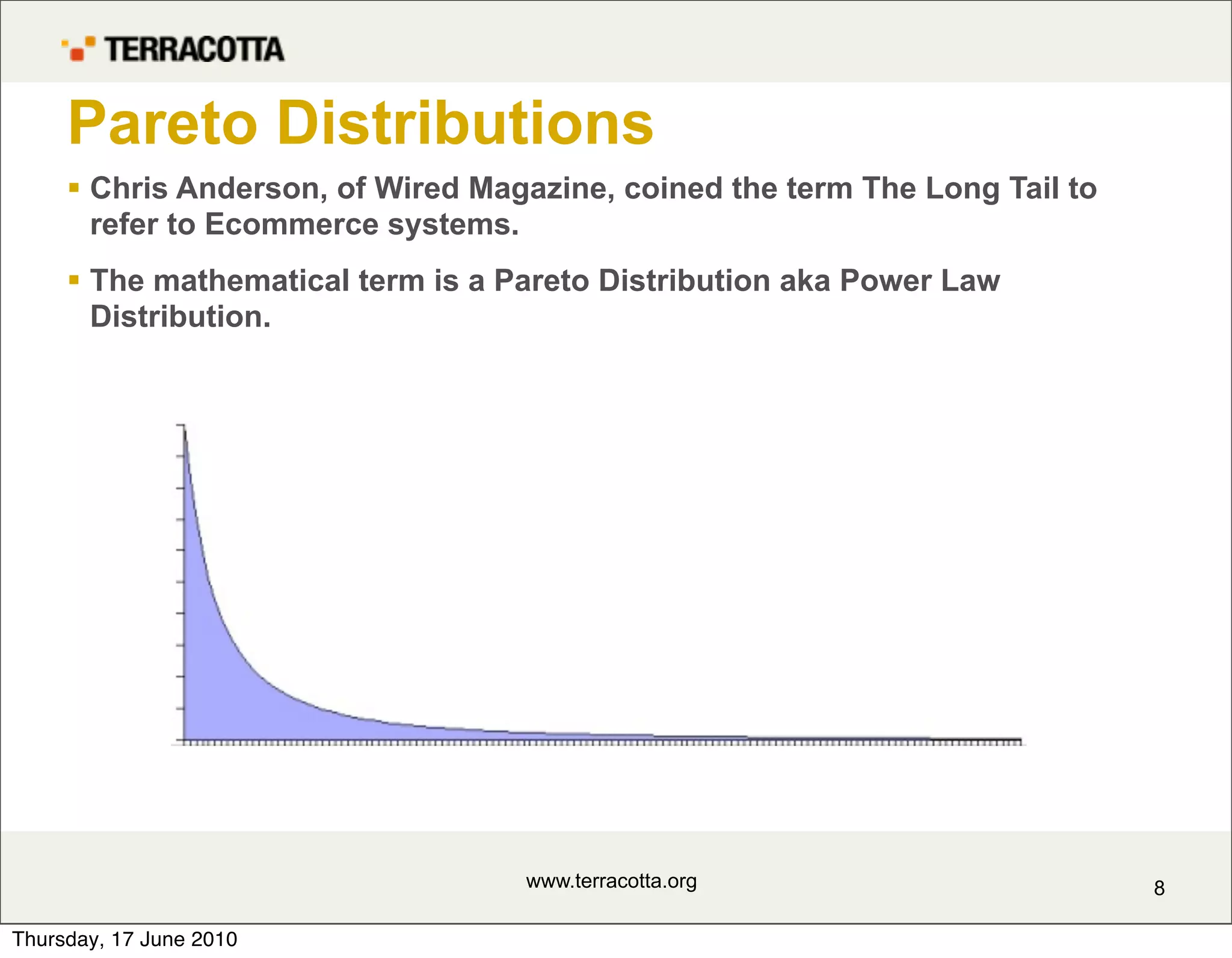
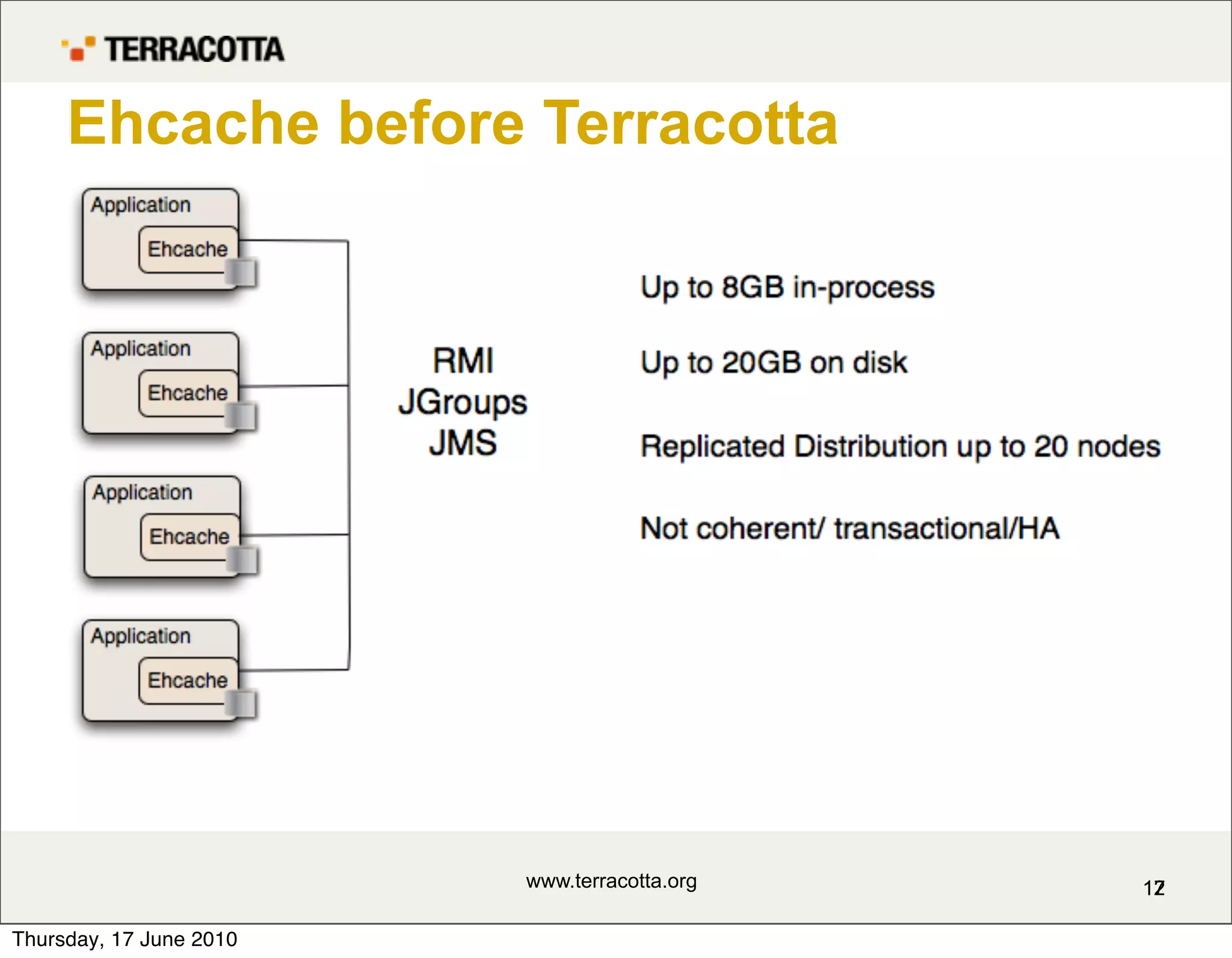
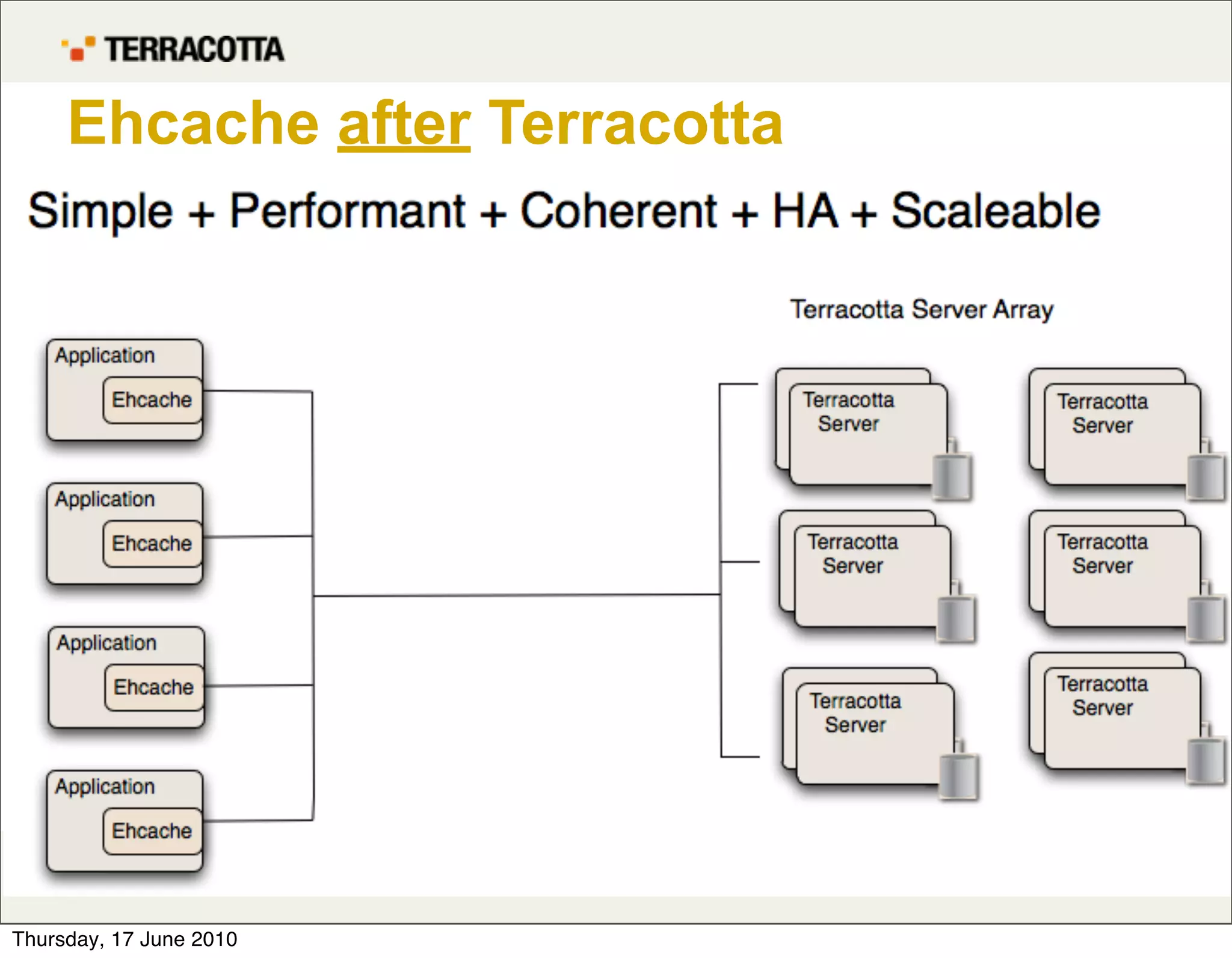
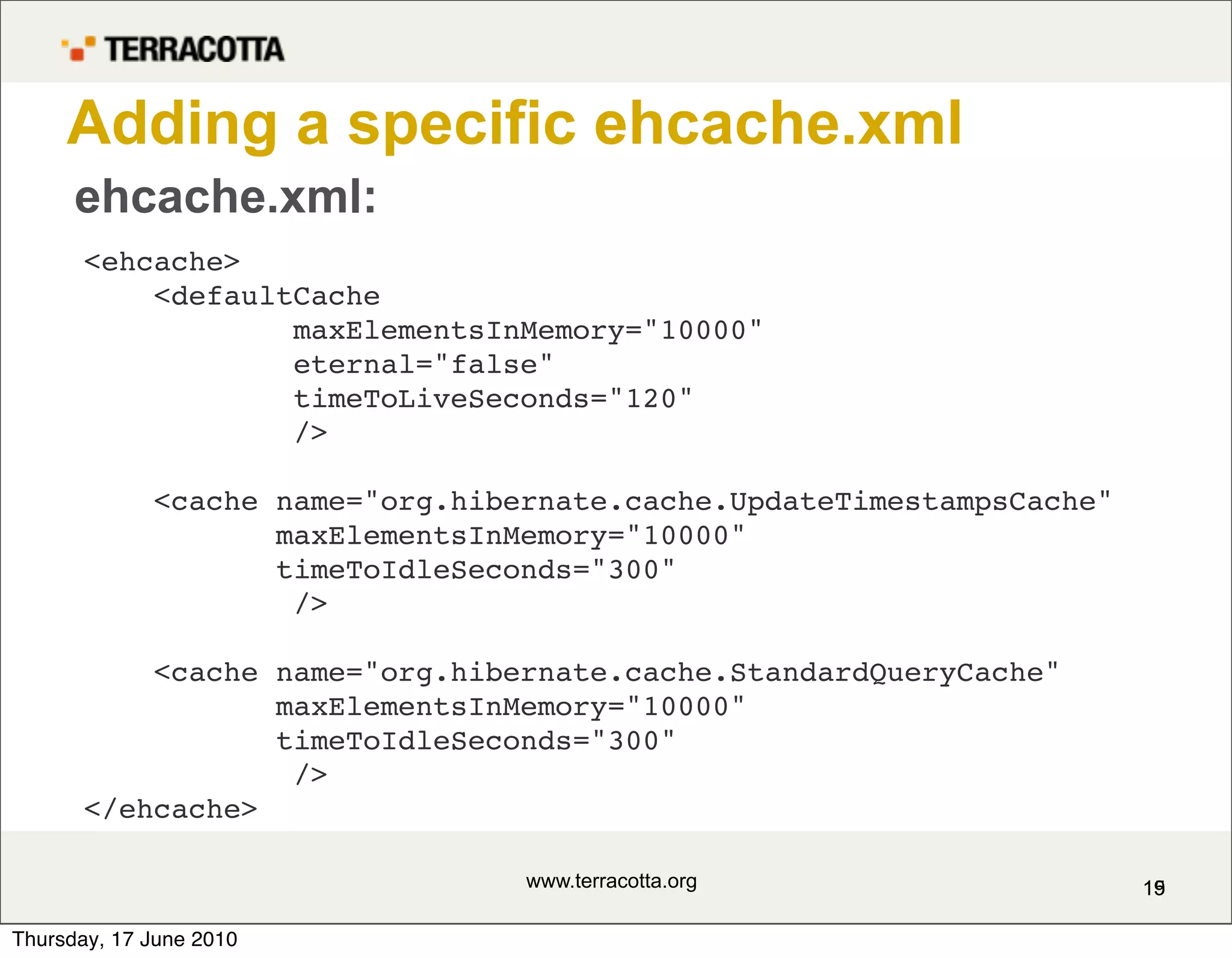
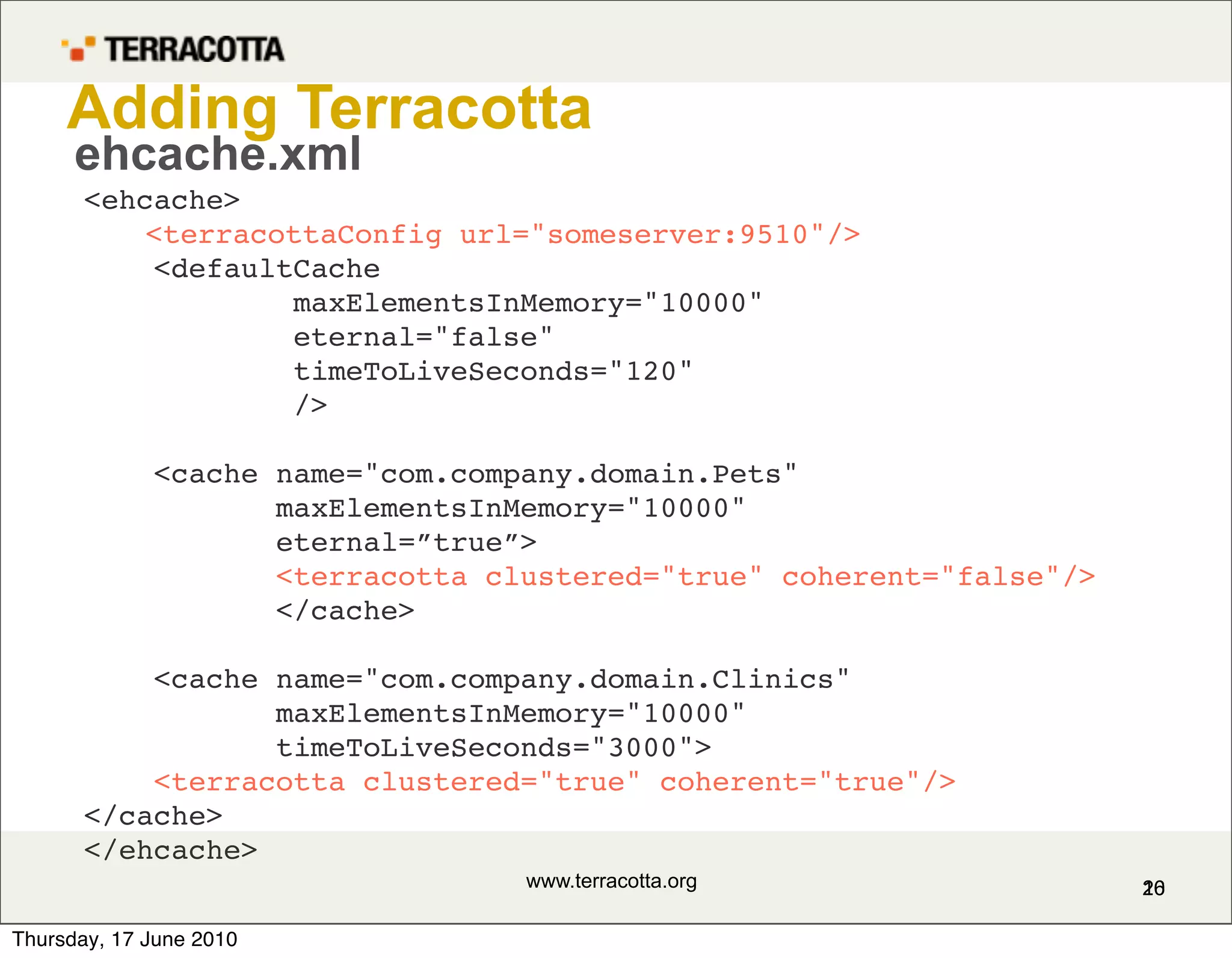
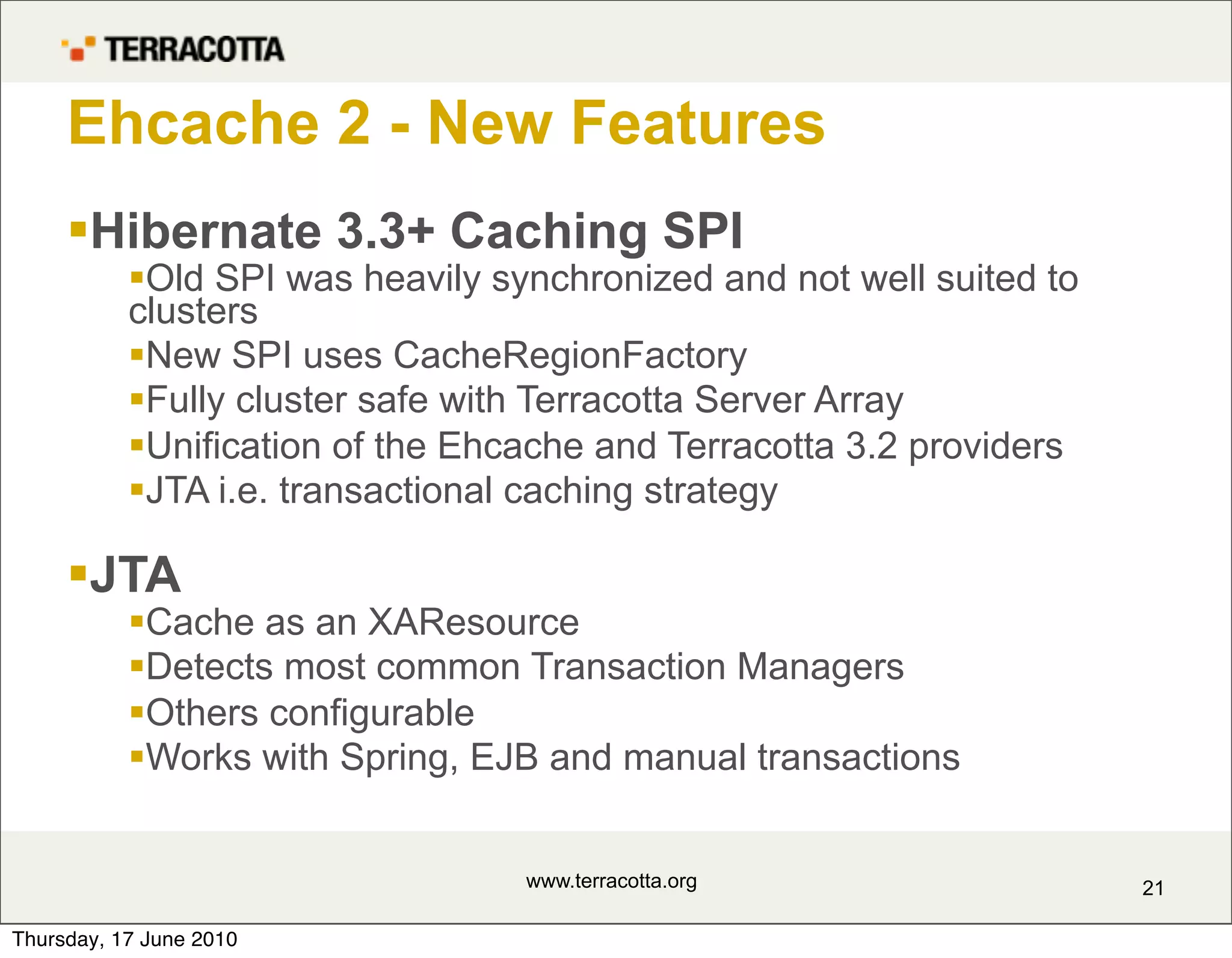
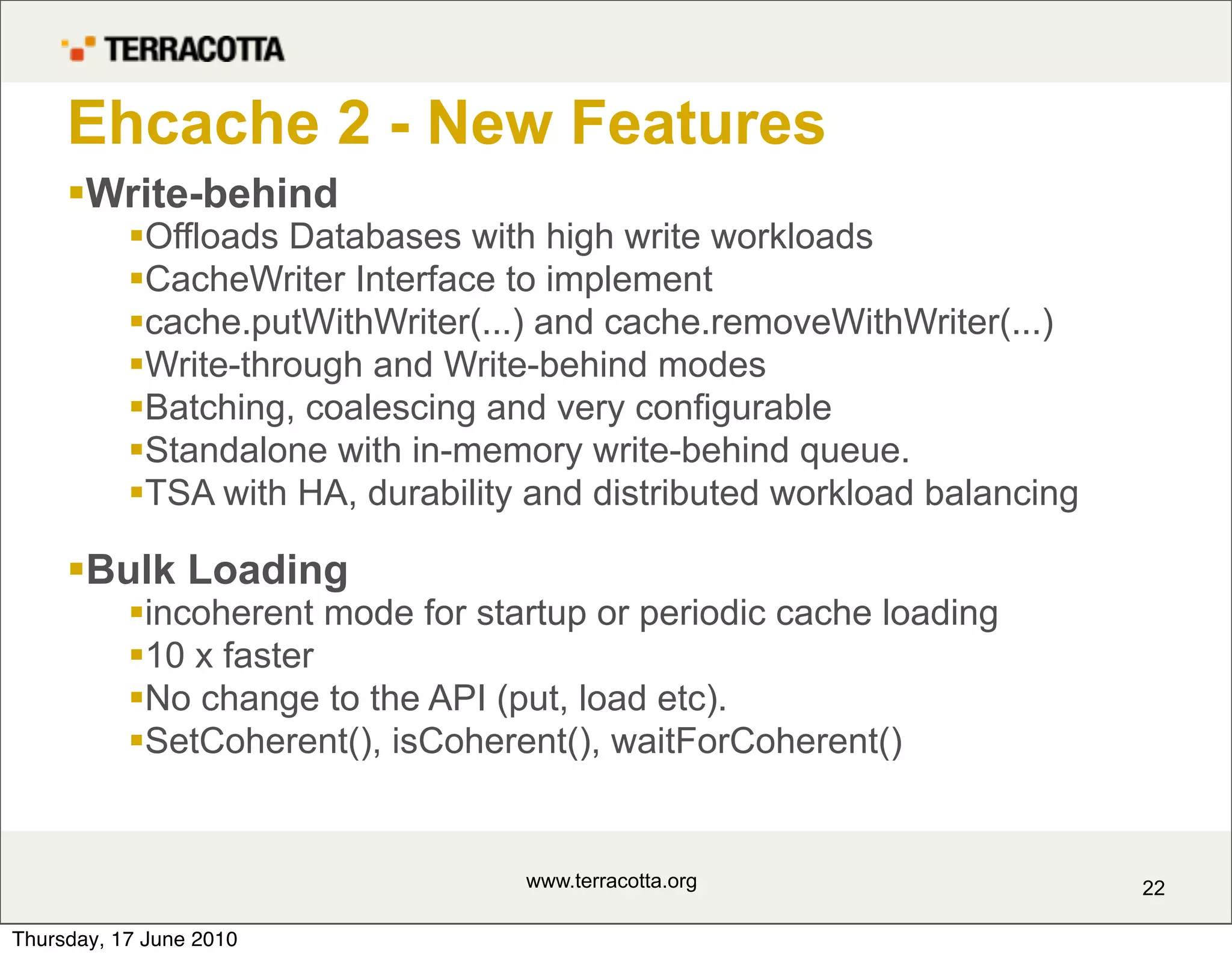
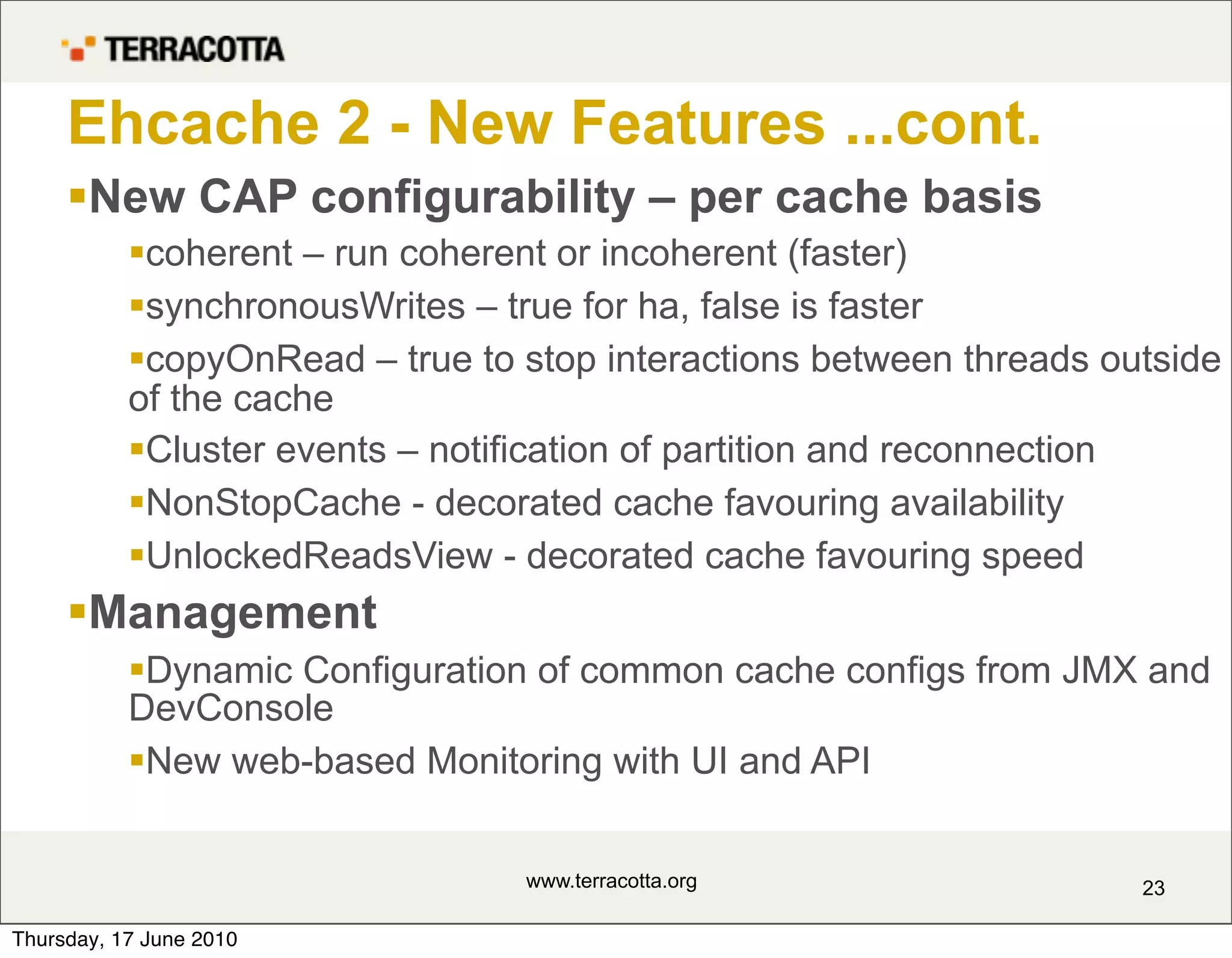
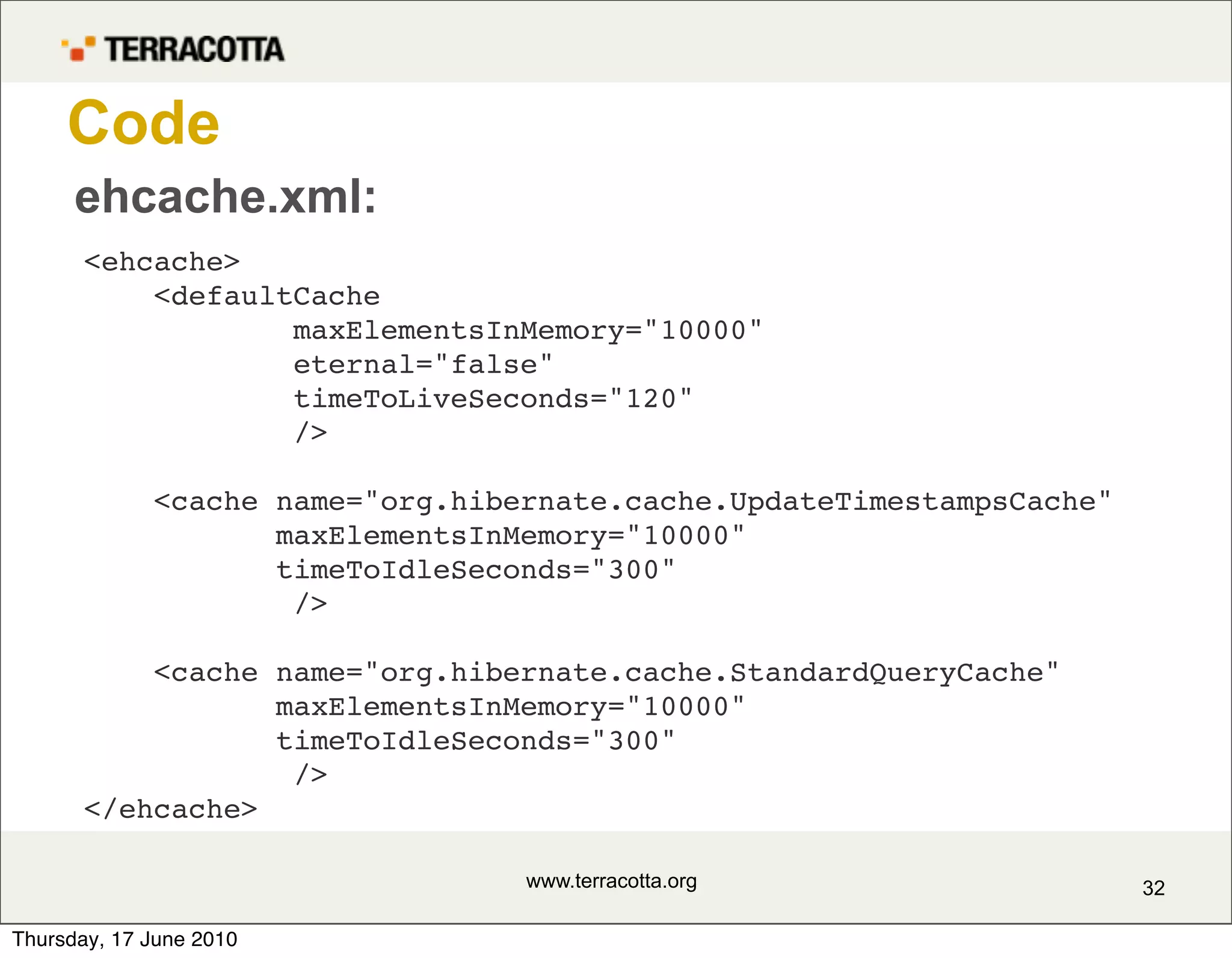
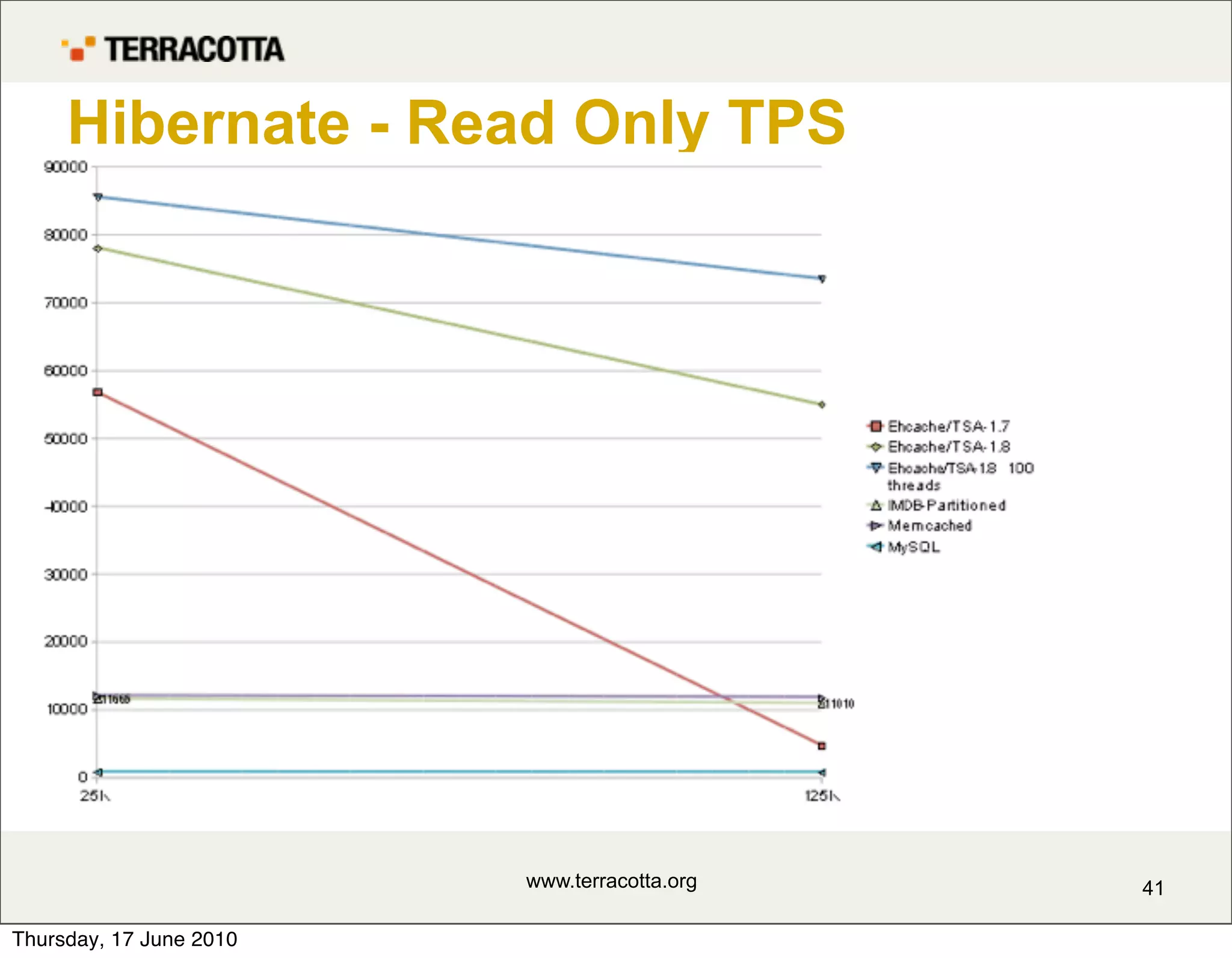
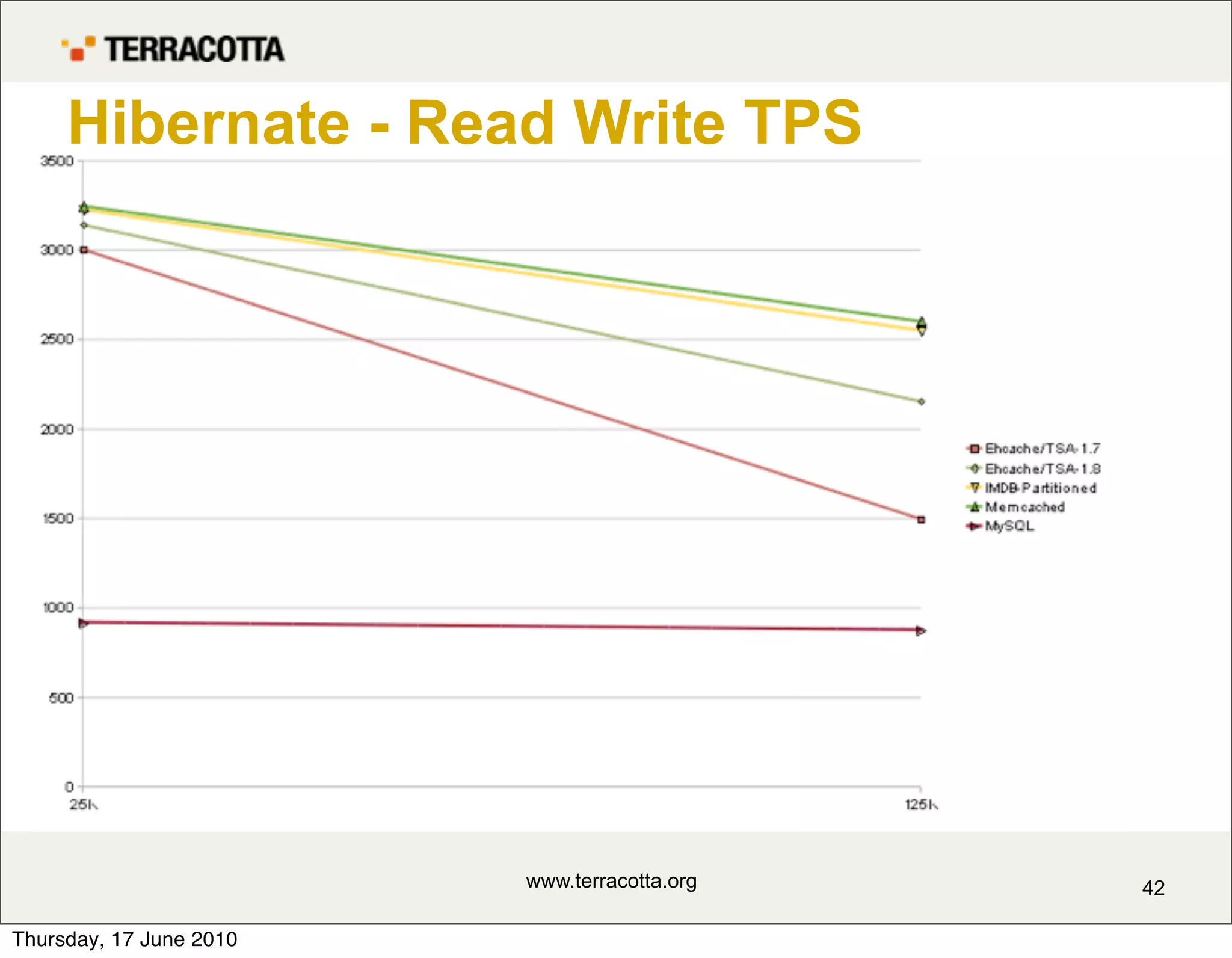
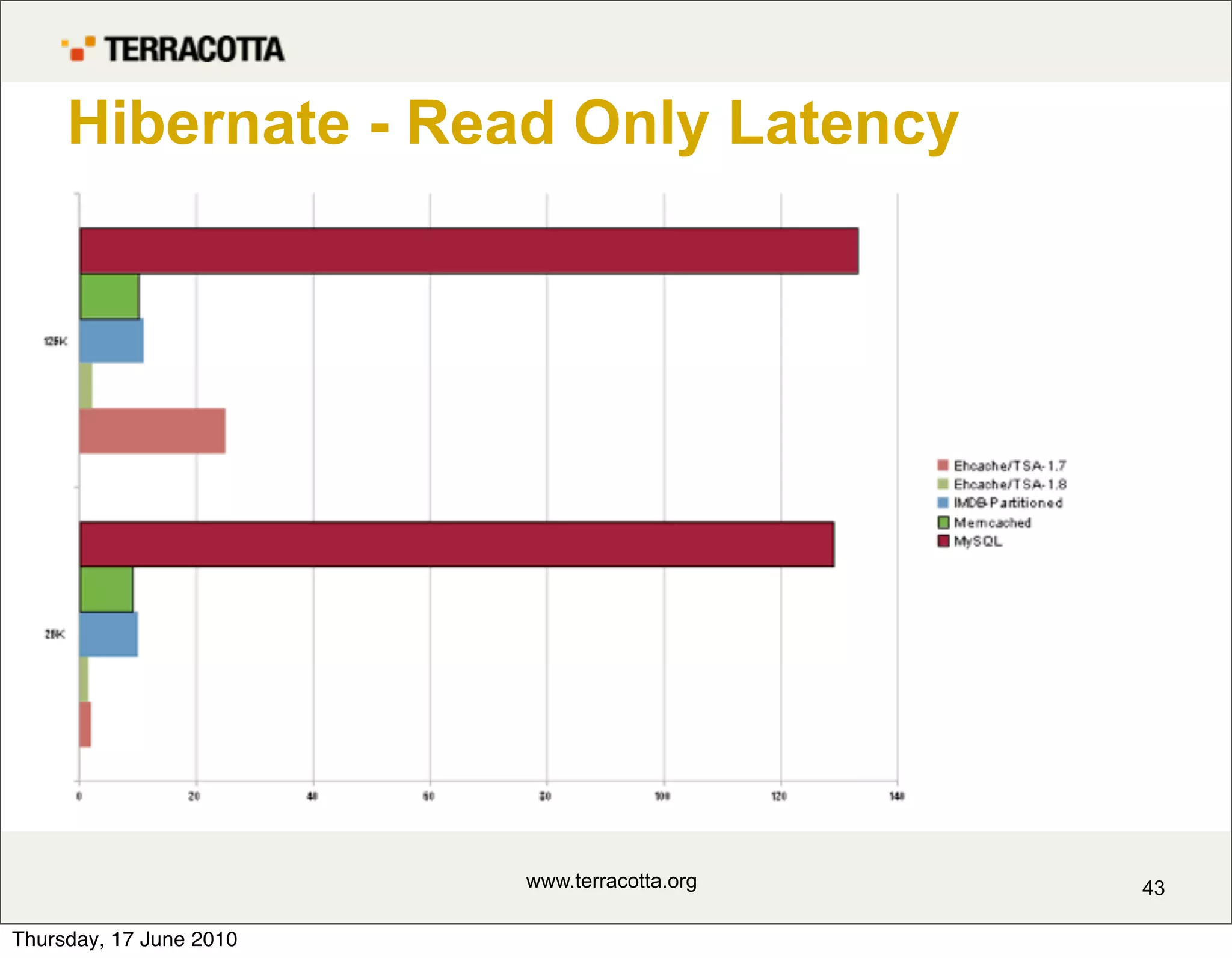
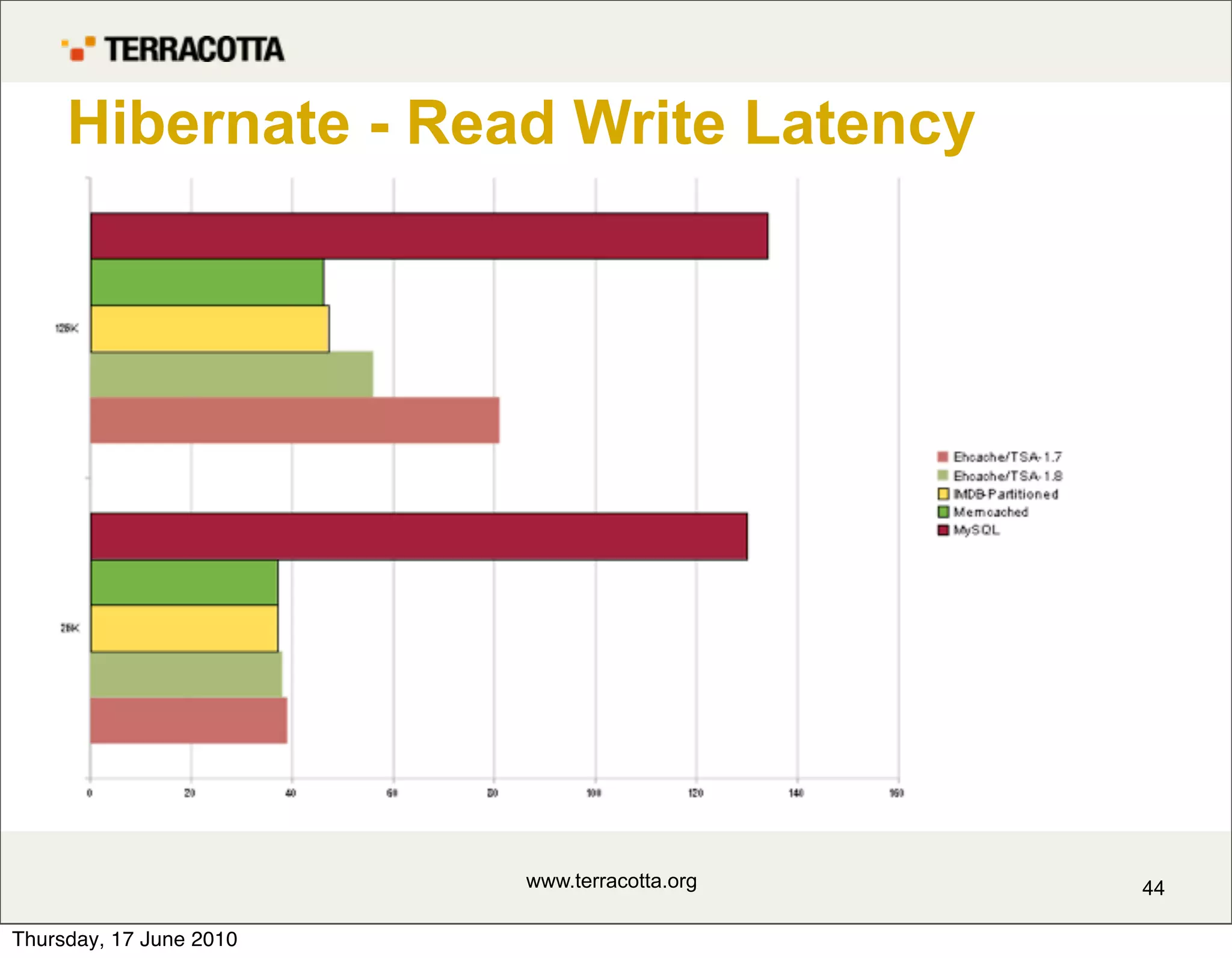
The document discusses caching and new features in Ehcache 2 and Hibernate caching. It describes reasons for caching like offloading resources, improving performance, and enabling scalability. It discusses how caching works by leveraging principles of locality of reference and Pareto distributions. It also covers challenges like data size, staleness, and maintaining coherency in a clustered environment.