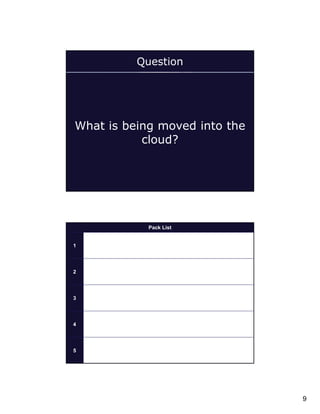
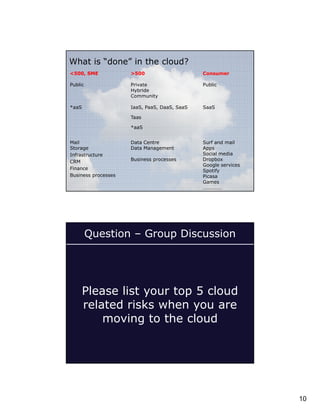
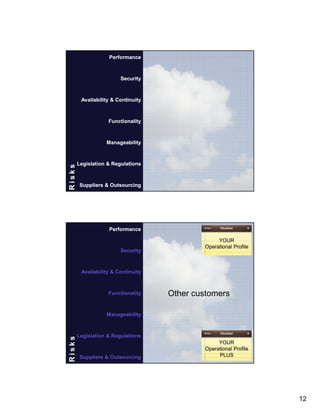
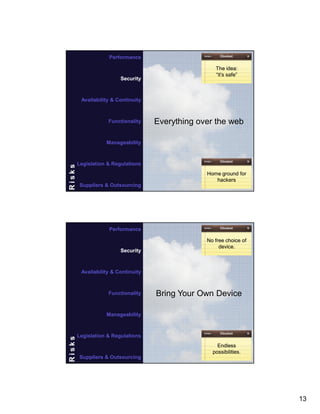
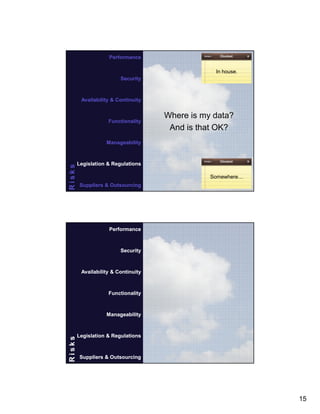
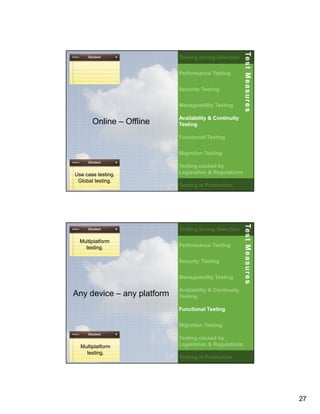
The document is a comprehensive overview of test management specifically for cloud-based applications, presented by Ruud Teunissen from Polteq Test Services. It covers essential characteristics of cloud services, reasons for transitioning to the cloud, associated risks, and key testing measures to be applied during selection and production. Furthermore, it provides a discussion on criteria for cloud service evaluation, including performance, security, and compliance with legal regulations.