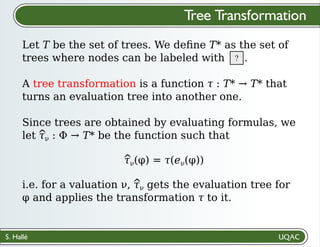
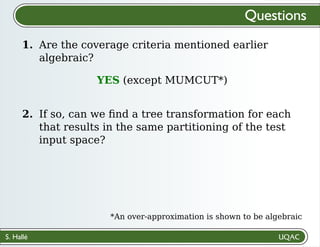
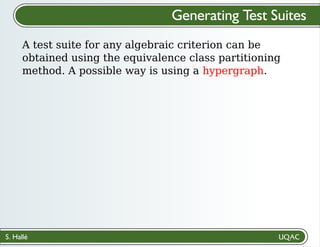
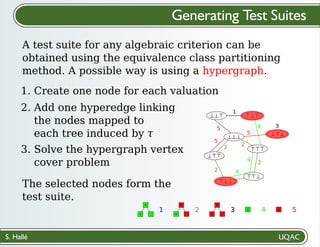
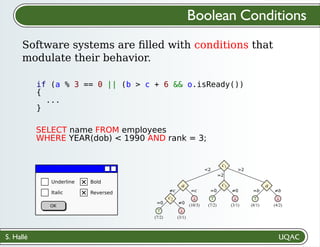
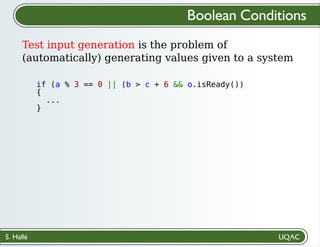
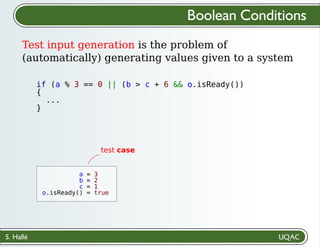
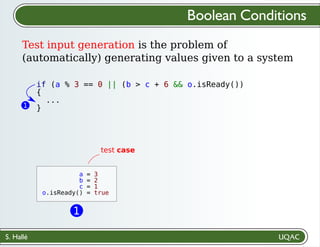
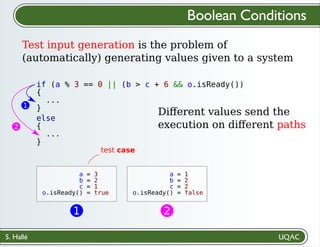
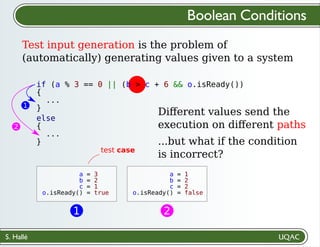
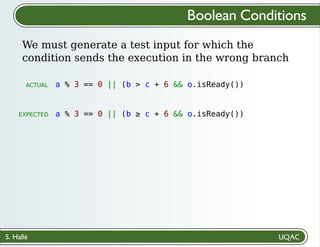
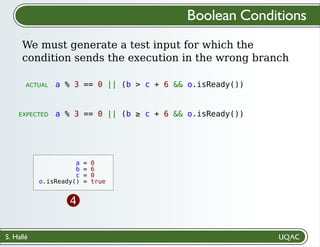
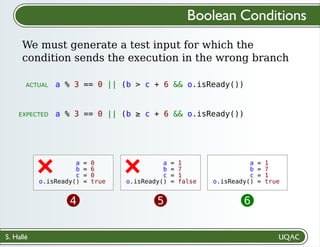
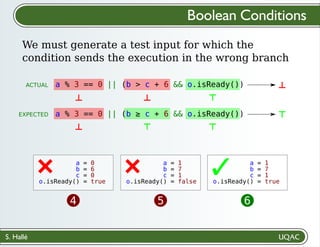
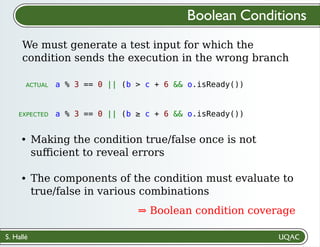
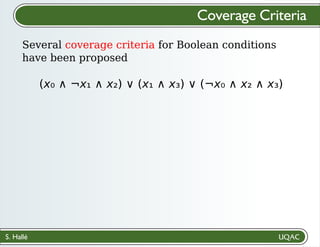
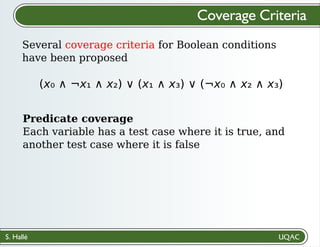
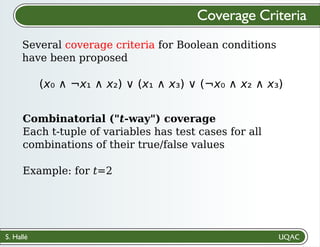
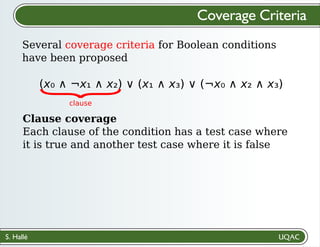
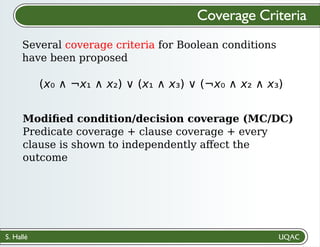
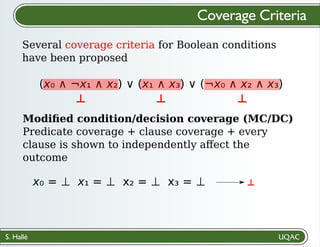
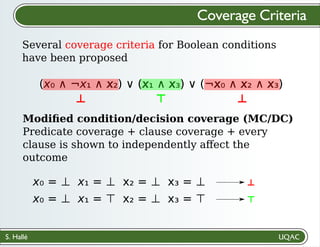
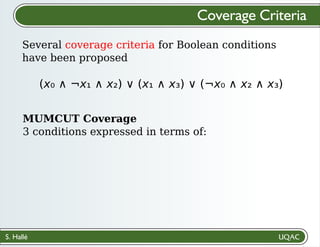
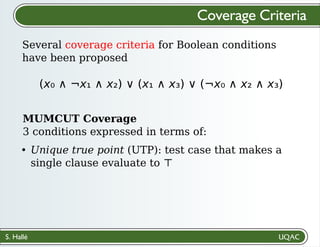
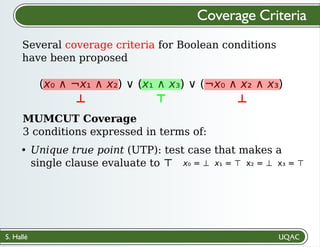
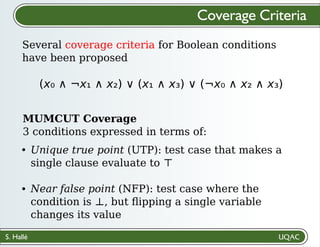
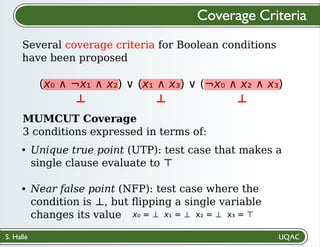
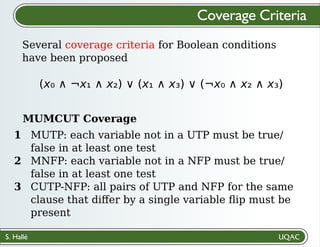
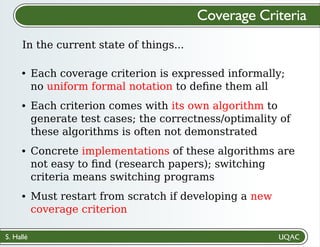
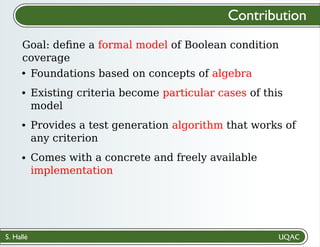
The document discusses the generation of test inputs for boolean conditions in software systems, emphasizing the need to ensure that conditions are evaluated correctly to avoid incorrect execution paths. It presents multiple coverage criteria for evaluating test input generation, including predicate coverage, combinatorial coverage, and modified condition/decision coverage. The author proposes an algebraic framework to formalize these criteria and provides an algorithm for generating test cases that comply with any selected coverage criterion.
![S. Hallé
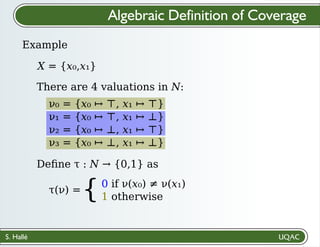
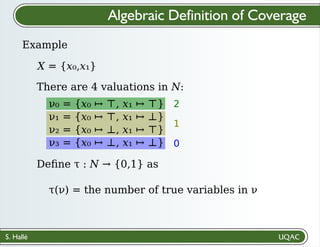
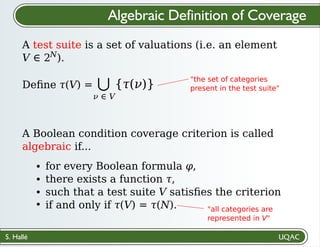
Algebraic Definition of Coverage
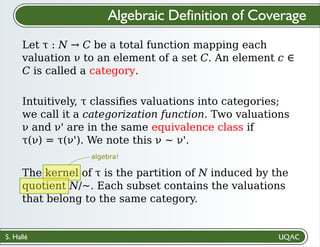
Let X be a set of arbitrary symbols (variables). A
valuation is a total function ν : X → {⊤,⊥}. We
define as N the set of all valuations.
We denote by φ[ν] the result of evaluating φ by
setting its variables to the values defined by ν.
Let Φ be the set of Boolean formulas with variables
in X. A valuation ν ∈ N is a specific way of
evaluating a condition φ ∈ Φ.
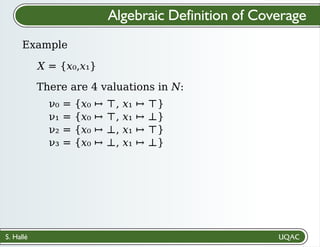
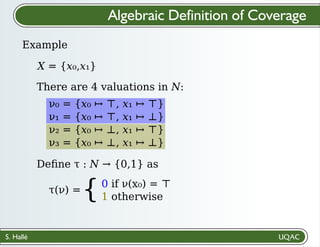
Example: X = {x₀,x₁}
ν(x₀) = ⊤, ν(x₁) = ⊥
φ = x₀ ∧ ¬x₁
φ[ν] = ⊤](https://image.slidesharecdn.com/slides-220518132747-38bedf5e/85/Test-Suite-Generation-for-Boolean-Conditions-with-Equivalence-Class-Partitioning-31-320.jpg)
![S. Hallé
𝜌(V) ∈ [0,1], and full coverage means 𝜌(V) = 1.
Algebraic Definition of Coverage
If a test suite V achieves partial coverage, it can
easily be quantified:
𝜌(V) =
𝜏(V)
𝜏(N)
coverage ratio of V fraction of all
categories that are
present in V
Note that we did not need to specify what specific
criterion we are talking about!](https://image.slidesharecdn.com/slides-220518132747-38bedf5e/85/Test-Suite-Generation-for-Boolean-Conditions-with-Equivalence-Class-Partitioning-43-320.jpg)
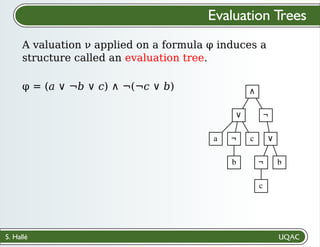
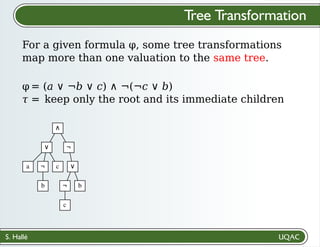
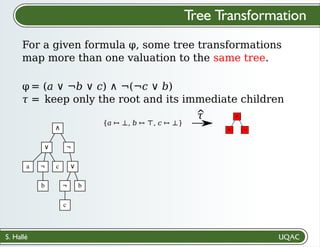
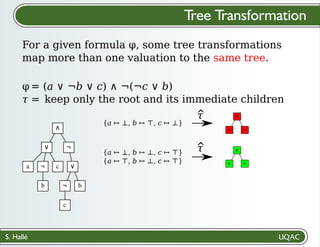
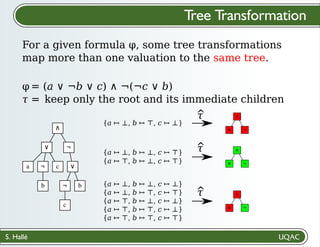
![S. Hallé
ν = {a ↦ ⊤, b ↦ ⊥, c ↦ ⊤}
Each valuation "colors" the
structure differently
Each combination of ν and φ
produces a unique tree
Define as eν(φ) the function that produces
the evaluation tree of φ[ν].
Evaluation Trees
∧
∨ ¬
a ¬ c
b
∨
¬ b
c
φ = (a ∨ ¬b ∨ c) ∧ ¬(¬c ∨ b)
A valuation ν applied on a formula φ induces a
structure called an evaluation tree.](https://image.slidesharecdn.com/slides-220518132747-38bedf5e/85/Test-Suite-Generation-for-Boolean-Conditions-with-Equivalence-Class-Partitioning-45-320.jpg)