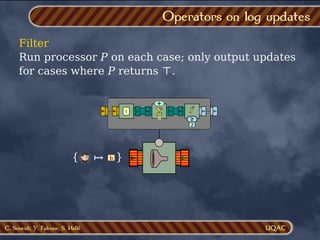
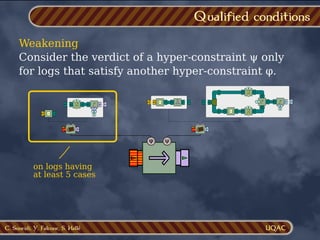
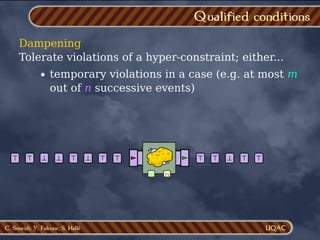
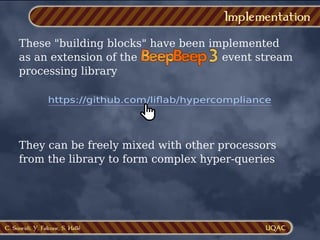
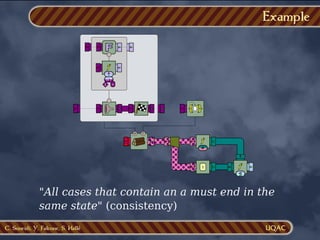
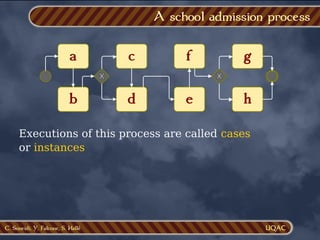
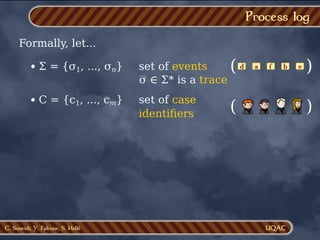
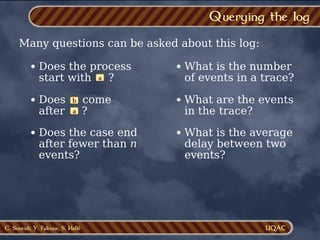
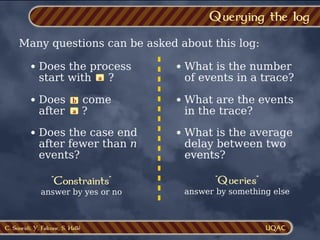
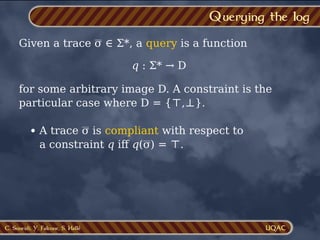
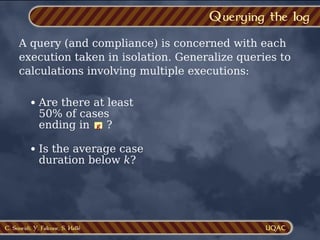
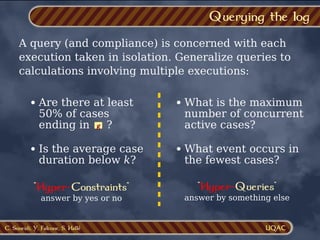
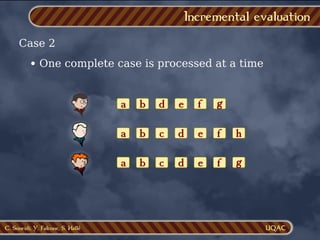
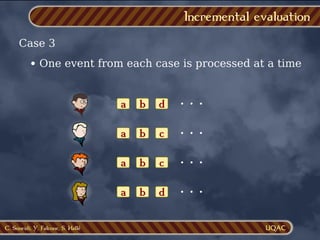
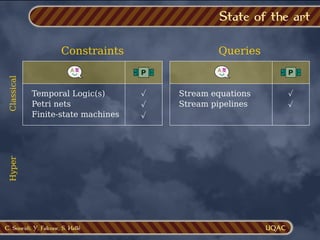
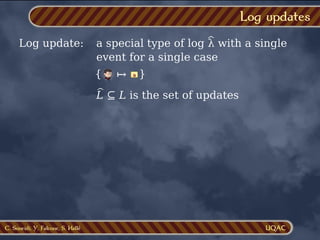
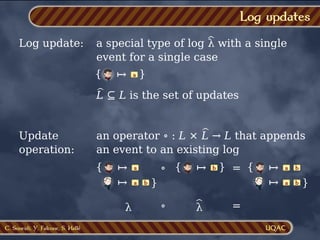
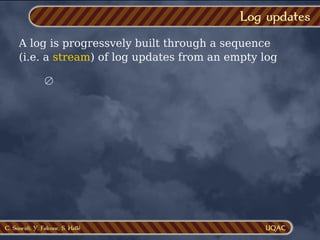
The document discusses stream processing and querying of process logs. It defines a process log as a mapping of case identifiers to traces, which are sequences of events. Queries can check properties of individual traces or perform aggregations across multiple traces. Hyper-queries generalize this to operate on the full log. Various methods of incrementally evaluating queries and hyper-queries are discussed as the log is produced, such as processing one case or event at a time. The state of the art in constraint and query languages is reviewed.













































![C. Soueidi, Y. Falcone, S. Hallé
Problem
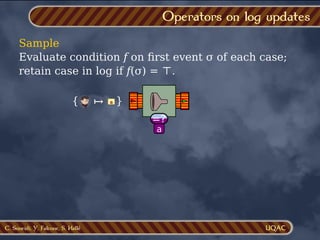
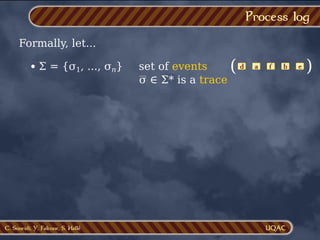
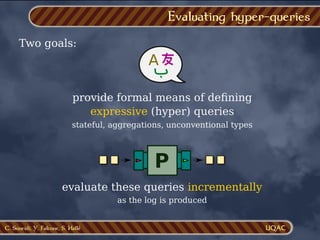
Problem Given a hyperquery q : L → D, define a
processor πq : L* → D* such that
πq(λ1 ⋅ ... ⋅ λn)[n] = q(λ1 ∘ ... ∘ λn)
Hyper-processors
πq](https://image.slidesharecdn.com/slides-231102181422-e73e8934/85/Monitoring-Business-Process-Compliance-Across-Multiple-Executions-with-Stream-Processing-66-320.jpg)
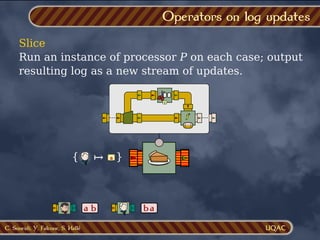
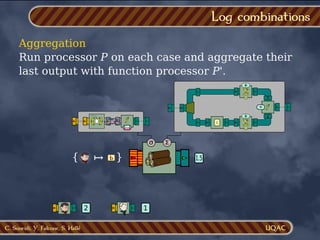
![C. Soueidi, Y. Falcone, S. Hallé
Problem
Problem Given a hyperquery q : L → D, define a
processor πq : L* → D* such that
πq(λ1 ⋅ ... ⋅ λn)[n] = q(λ1 ∘ ... ∘ λn)
Hyper-processors
q( )
{ }
a
↦ { }
a
↦
πq](https://image.slidesharecdn.com/slides-231102181422-e73e8934/85/Monitoring-Business-Process-Compliance-Across-Multiple-Executions-with-Stream-Processing-67-320.jpg)
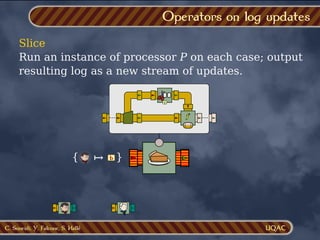
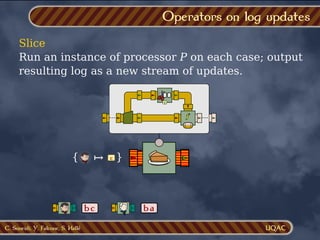
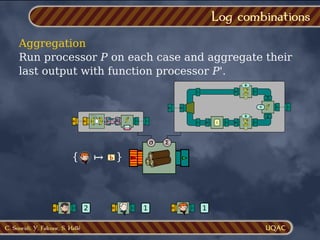
![C. Soueidi, Y. Falcone, S. Hallé
Problem
Problem Given a hyperquery q : L → D, define a
processor πq : L* → D* such that
πq(λ1 ⋅ ... ⋅ λn)[n] = q(λ1 ∘ ... ∘ λn)
Hyper-processors
πq](https://image.slidesharecdn.com/slides-231102181422-e73e8934/85/Monitoring-Business-Process-Compliance-Across-Multiple-Executions-with-Stream-Processing-68-320.jpg)
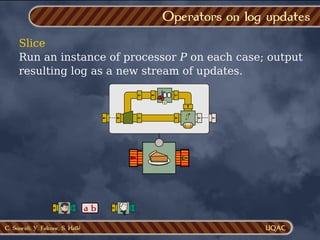
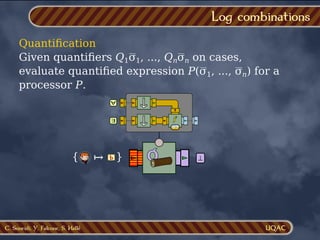
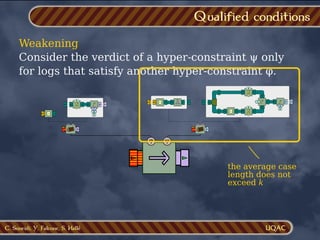
![C. Soueidi, Y. Falcone, S. Hallé
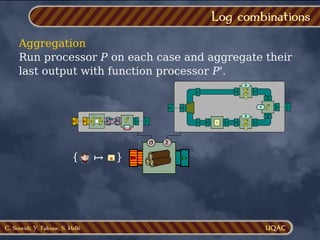
Problem
Problem Given a hyperquery q : L → D, define a
processor πq : L* → D* such that
πq(λ1 ⋅ ... ⋅ λn)[n] = q(λ1 ∘ ... ∘ λn)
Hyper-processors
πq
πq
{ }
a
↦
}
a
↦
{ a
↦
q(](https://image.slidesharecdn.com/slides-231102181422-e73e8934/85/Monitoring-Business-Process-Compliance-Across-Multiple-Executions-with-Stream-Processing-69-320.jpg)
![C. Soueidi, Y. Falcone, S. Hallé
Problem
Problem Given a hyperquery q : L → D, define a
processor πq : L* → D* such that
πq(λ1 ⋅ ... ⋅ λn)[n] = q(λ1 ∘ ... ∘ λn)
Hyper-processors
πq](https://image.slidesharecdn.com/slides-231102181422-e73e8934/85/Monitoring-Business-Process-Compliance-Across-Multiple-Executions-with-Stream-Processing-70-320.jpg)
![C. Soueidi, Y. Falcone, S. Hallé
Problem
Problem Given a hyperquery q : L → D, define a
processor πq : L* → D* such that
πq(λ1 ⋅ ... ⋅ λn)[n] = q(λ1 ∘ ... ∘ λn)
Hyper-processors
πq
πq
}
a
↦
{ a
↦
q(
)
{ }
b
↦ b](https://image.slidesharecdn.com/slides-231102181422-e73e8934/85/Monitoring-Business-Process-Compliance-Across-Multiple-Executions-with-Stream-Processing-71-320.jpg)
![C. Soueidi, Y. Falcone, S. Hallé
Problem
Problem Given a hyperquery q : L → D, define a
processor πq : L* → D* such that
πq(λ1 ⋅ ... ⋅ λn)[n] = q(λ1 ∘ ... ∘ λn)
Hyper-processors
πq
πq
}
a
↦
{ a
↦
q(
)
{ }
b
↦ b
In other words, πq incrementally evaluates q on
each update
Avoid re-evaluating q from scratch every time!](https://image.slidesharecdn.com/slides-231102181422-e73e8934/85/Monitoring-Business-Process-Compliance-Across-Multiple-Executions-with-Stream-Processing-72-320.jpg)