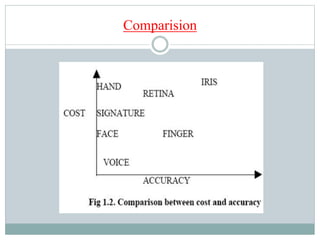
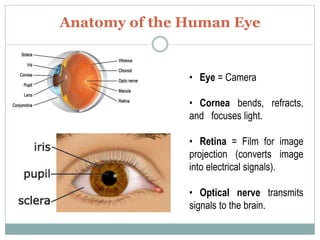
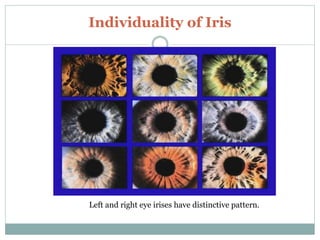
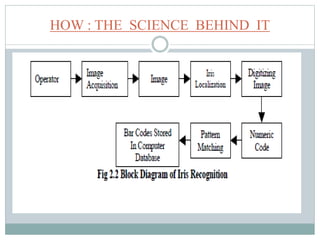
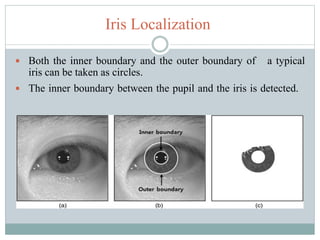
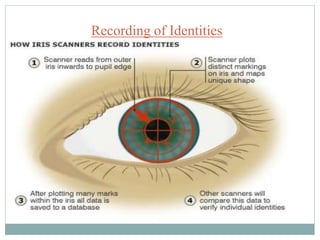
This document discusses iris recognition as a biometric authentication method. It begins by explaining the need for biometrics due to technology advances and globalization. It then describes the anatomy of the human eye and characteristics of the iris that make it suitable for identification, such as its complex texture and stability over time. The document outlines how iris recognition works by locating the iris and recording its unique patterns. It discusses the benefits of iris recognition for security and applications like border control, ATMs, and forensics. In conclusion, iris recognition is presented as an accurate biometric technique that will likely see increased future usage.