Synchronous mac protocol study
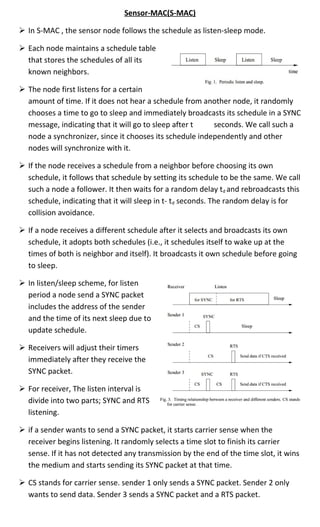
- 1. Sensor-MAC(S-MAC) In S-MAC , the sensor node follows the schedule as listen-sleep mode. Each node maintains a schedule table that stores the schedules of all its known neighbors. The node first listens for a certain amount of time. If it does not hear a schedule from another node, it randomly chooses a time to go to sleep and immediately broadcasts its schedule in a SYNC message, indicating that it will go to sleep after t seconds. We call such a node a synchronizer, since it chooses its schedule independently and other nodes will synchronize with it. If the node receives a schedule from a neighbor before choosing its own schedule, it follows that schedule by setting its schedule to be the same. We call such a node a follower. It then waits for a random delay td and rebroadcasts this schedule, indicating that it will sleep in t- td seconds. The random delay is for collision avoidance. If a node receives a different schedule after it selects and broadcasts its own schedule, it adopts both schedules (i.e., it schedules itself to wake up at the times of both is neighbor and itself). It broadcasts it own schedule before going to sleep. In listen/sleep scheme, for listen period a node send a SYNC packet includes the address of the sender and the time of its next sleep due to update schedule. Receivers will adjust their timers immediately after they receive the SYNC packet. For receiver, The listen interval is divide into two parts; SYNC and RTS listening. if a sender wants to send a SYNC packet, it starts carrier sense when the receiver begins listening. It randomly selects a time slot to finish its carrier sense. If it has not detected any transmission by the end of the time slot, it wins the medium and starts sending its SYNC packet at that time. CS stands for carrier sense. sender 1 only sends a SYNC packet. Sender 2 only wants to send data. Sender 3 sends a SYNC packet and a RTS packet.
- 2. Each node periodically broadcasts SYNC packets to its neighbors even if it has no followers. This allows new nodes to join an existing neighborhood. The new node follows the same procedure in the above subsection to choose its schedule. S-MAC Adaptive listening(2004) S-MAC proposes an important technique, called adaptive listen, to improve the latency caused by the periodic sleep of each node in a multihop network. The basic idea is to let the node who overhears its neighbor’s transmissions (ideally only RTS or CTS) wake up for a short period of time at the end of the transmission. In this way, if the node is the next-hop node, its neighbor is able to immediately pass the data to it instead of waiting for its scheduled listen time. If the node does not receive anything during the adaptive listening, it will go back to sleep until its next scheduled listen time. Synchronous channel polling(SCP-MAC)(2006) To send a packet, the sender adds a preamble before the packet. This preamble is effectively a wake-up signal, informing other nodes a data packet is about to be transmitted. The preamble must be at least as long as the channel polling period to ensure all receivers will detect it. The performance of LPL is sensitive to the channel polling period, since longer periods reduce receiver costs but increase sender costs.
- 3. unlike LPL, SCP-MAC synchronizes the polling times (schedules) of all neighboring nodes. a short wake-up tone is required for senders to guarantee rendezvous. A sends to node B. When B receives a packet during the first regular polling. it adds n high frequency poll in the same frame, immediately following its regular poll. (We define n below) If A has more packets to send, it sends them in these adaptive polling times. Spacing of adaptive slots is determined by the longest packet length that the physical layer supports. If B finds none of its additional polls useful (such as if A had no additional data to send) it transitions back to its regular, low-duty cycle polling period. If any of B’s additional slots were successfully used, B extends the adaptive polling with n slots, allowing A to continue transmission. It also automatically plans an additional n in the next frame. If the duration of the traffic burst is shorter than one regular polling period, such process repeats at each hop, and the whole data can be transferred over N hops using N polling periods. Disadvantage: Q-MAC(Query based network)(2006) In Q-MAC two types of sleep planning to suit query processing in a multi hop network. It follows a (1) static sleep schedule when there is no query and (2) dynamic sleep schedule when a query is transmitted. When there is no query, the nodes follow a static sleep schedule. The active time period of the nodes at different regions are synchronized such that the next hop node is made active before the current node’s active period is over.
- 4. When the destination is unknown to the sink, but it may know the appropriate region (e.g. temperature of a node in north).In this case, the sink can send the query to the cluster head and the cluster head can send it to the destination. The node which forwards the query packet will change the sleep schedule as fully ‘on’ (sink)till it gets the data packet. When the destination node E sends the data packet, the intermediate nodes will change their radio to their usual schedule, after forwarding the data packet. This dynamic schedule avoids the delay in transmission. If the destination is known (i.e. how many hops away from a node), the schedule can be changed dynamically based on the arrival time of the data. The intermediate nodes calculate the time at which they have to forward the data using the following details: The time at which the query packet is forwarded, The distance of the destination node, Time taken to transmit the data packet for one hop distance. The accurate wake up time is hard to estimate and each node is activated at the reserved time and is kept active for a timeout period. If the packet is not received within the timeout period, the node will switch off the radio. The sleep schedule if data should be collected from multiple destinations. In this case, a multicast query is sent to the destination sensor nodes.
- 5. There may be many number of packets to the sink for a single query, since many nodes send the sensed information. The radio of the intermediate nodes is made on, after a particular period of time. After all the data packets are transmitted, a control packet is sent towards the sink, so that the intermediate nodes switch off the radio. The radio remains on until a control packet is received. The cluster head or a special node is responsible to send this control packet. Disadvantage: DW-MAC(demand wakeup mac)(2008) DW-MAC assumes that a separate protocol used to synchronize the clocks in sensor nodes during the Sync period with required precision. The basic concept of DW- MAC is to wake up nodes on demand during the Sleep period of a cycle in order to transmit or receive a packet. In DW-MAC, medium access control and scheduling are fully integrated. DW-MAC sets up a one-to-one mapping between a Data period and the following Sleep period. An SCH carries no timing information, and the transmission of an SCH simply replaces RTS/CTS for medium access control thus minimize schedule overhead. Node A first contends for channel access and transmits an SCH during the Data period. Transmission of the SCH starts T1time units after the beginning of the Data period. Based on T1 and the duration of the SCH transmission,T3, nodes A and B will both schedule their wakeup time toT2 from the beginning of the following Sleep period, and will agree on a maximum wakeup duration of T4, based on the ratio between TData and TSleep. T2=T1*Tsleep/Tdata where T2 defines after how much time from the beginning of the sleep the
- 6. sender and receiver will wake up. Disadvantage: • In DW-MAC, Data period and Sleep period are fixed, which results in that the • system cannot dynamically adapt to different traffic loads. • At the beginning of the sleep period , the initial data transmission takes too long time to transmit . • the interval between the two nodes data transmission may long interval to transmit. AS-MAC(Adaptive scheduling-MAC)(2010) AS-MAC is the enhance and modified format of DW-MAC scheme. In DW-MAC the durations of the Data period and Sleep period are static, but AS-MAC designs a flexible Reserved Active Time (RAT) within the fixed Adaptive Scheduling (AS) period, so that nodes can change the length of the RAT in each operational cycle and be adaptive to the variable traffic load. A timer is employed to decide moment the nodes should sleep. The timer expires when there is no transmission of SCH frames or transmission/collision in its neighborhood for a period of time,T0 T0 indicates maximum continuing amount of idle listening in the AS period. .In 1st operation cycle(average traffic load case): after AS-Period starts, two events occur. After the 2nd event, there is no new event within timeout T0 period. Thus node enters Sleep period after two events plus T0 time, thus early enter to Sleep period. For this case,T0<RAT<preset AS-Period. In 2nd operation cycle (high traffic load case): node keeps sensing five events in succession, and the interval of any two events in succession is shorter than the timeout T0 period. Thus node keeps Active mode till its full AS-Period. For this case, RAT = pre-set AS-Period.
- 7. In 3rd operation cycle (low traffic load case): after AS-Period starts, there is no single event. Thus after timeoutT0 period, node immediately enters Sleep mode. For this case, RAT=T0 if the node has not sensed event happened inT0, it will go to sleep, staying awake only for the period of TSYNC +T0 ,Since T0<<TDATA In AS-MAC, The SCH frame also have added two parameters in the header of the SCH compare to DW-MAC SCH. The SCH also preserve the number of times the SCH has been sent as RTS or/and CTS. The two parameters are RTS_RetryNo and CTS_RetryNo. The purpose to introduce the two parameters, RTS_RetryNo and CTS_RetryNo, is to avoid duplicate data transmission, thus reducing latency and energy consumption. Assume A needs to send a data packet to D through B and C as shown in fig. A sends an SCH (RTS) successfully to B and sets a timer to wait for SCH (CTS) from B. Upon receiving the SCH (RTS) from A, B sends an SCH (CTS) to A which at the same time serves as SCH (RTS) to C. However, A might lost the SCH (CTS) from B before the SCH (CTS) timer timeout and interprets that its SCH (RTS) transmission failed. A sends another SCH (RTS) to B. In the mean time, after receiving the SCH (RTS) from B, C will continue the forwarding to D. If the 2nd SCH (RTS) succeeds and A also receives SCH (CTS) from B, the DW- MAC uses the 2nd time SCH (RTS) to schedule the data transmission. The advantages of SCH frame with tracked retry numbers are in three-folds: o end-to-end delivery latency will be reduced as the 1st successful RTS is used for mapping the data transmission. o energy consumption can be reduced due to the avoidance of unnecessary SCH frames transmission and o improvement of the delivery latency and energy conservation will not introduce perceivable overhead.
- 8. Disadvantage: Though the receiver don't know the data size when variable length data can be transmit by sender then how it can calculate the wakeup time in sleep period. R-MAC(Routing Enhancement MAC protocol)(2007) An operational cycle of a sensor node in RMAC can be divided into three stages: SYNC, DATA, and SLEEP. SYNC period, synchronizes the clocks on sensor nodes with the required precision. When a data packet is to be sent to a destination node that is multiple hops away, a control frame PION is sent during the DATA period to initiate the communication with the downstream nodes. The dual function of a single PION frame is to confirm receipt of a PION from its upstream node and to simultaneously request communication from a downstream node. Node S first picks a random period from the contention window and waits for the medium to be quiet for that period and an additional DIFS period (as in IEEE 802.11) before sending a PION to the next-hop node A. A gets the next-hop address for this destination from its own network layer. A then waits a SIFS period before transmitting its own PION. The PION contains three addresses, apart from the final destination address: its own address, the previous-hop address (S), and the new next-hop address(e.g B) This PION from A serves both as a CTS to S and as an RTS to B. when S receives A’s PION, S does not send its data frame immediately but waits for the start of the SLEEP period to transmit the data frame.
- 9. Node A stays awake to receive the data frame at the start of the SLEEP period, and after node A receives the data frame, it sends an ACK frame to S. After receiving the ACK, node S goes to sleep mode. If node A earlier received the confirmation PION from its next hop B in the DATA period, A immediately relays the data frame to B. This data frame relaying process continues at each hop until the final destination is reached. Disadvantage: • In SYNC period how the sensor node synchronize themselves that are not clearly explained.
- 10. Node A stays awake to receive the data frame at the start of the SLEEP period, and after node A receives the data frame, it sends an ACK frame to S. After receiving the ACK, node S goes to sleep mode. If node A earlier received the confirmation PION from its next hop B in the DATA period, A immediately relays the data frame to B. This data frame relaying process continues at each hop until the final destination is reached. Disadvantage: • In SYNC period how the sensor node synchronize themselves that are not clearly explained.