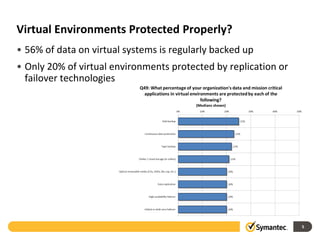
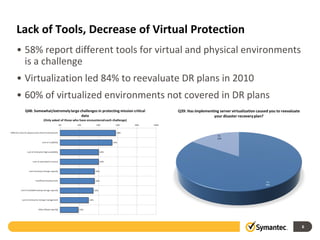
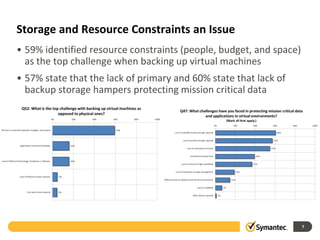
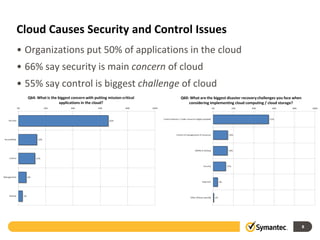
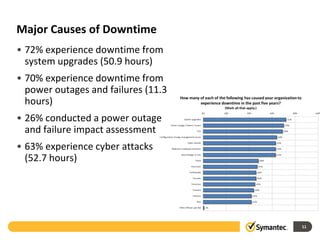
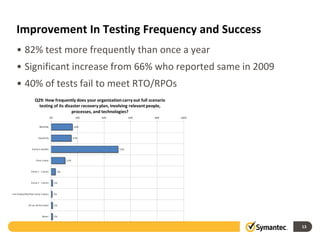
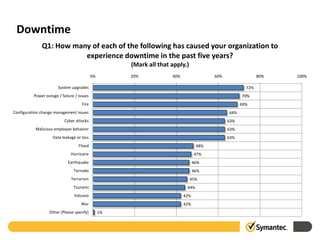
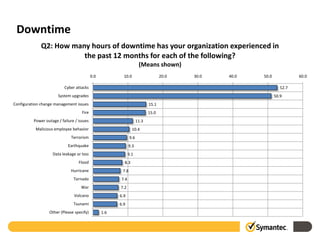
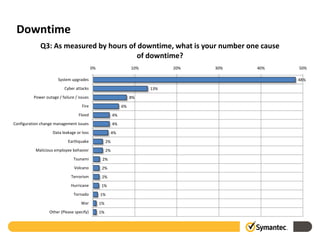
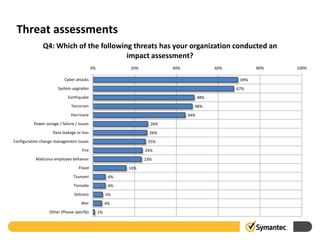
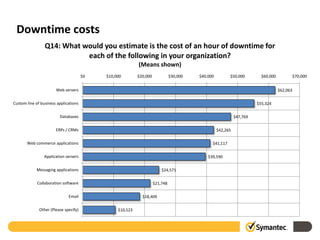
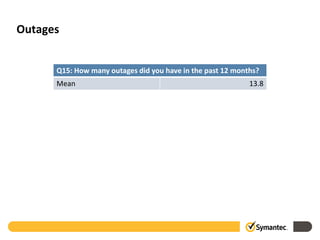
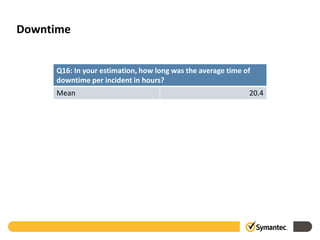
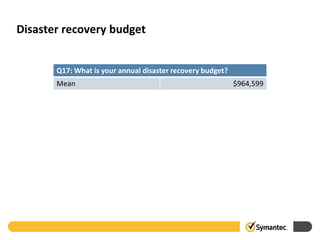
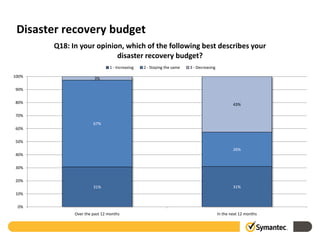
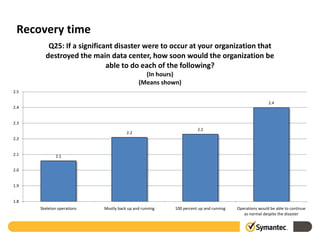
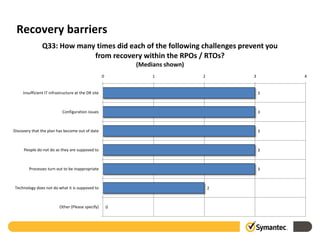
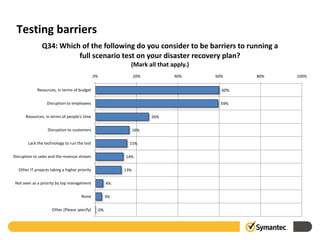
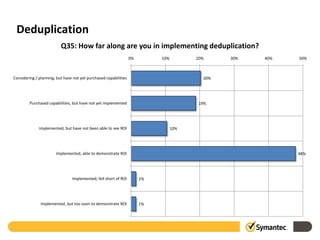
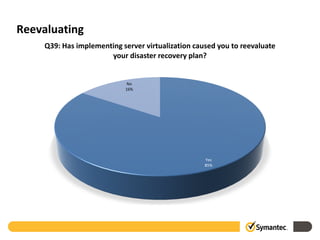
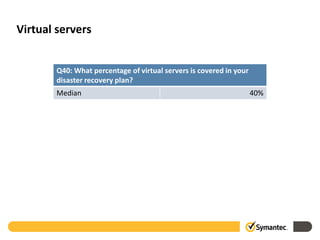
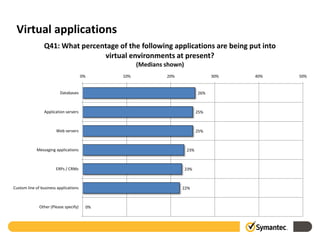
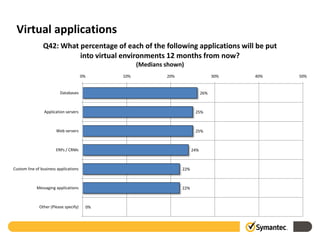
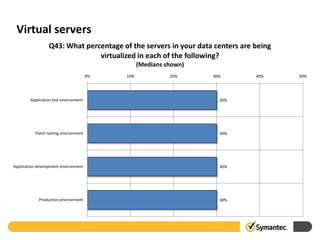
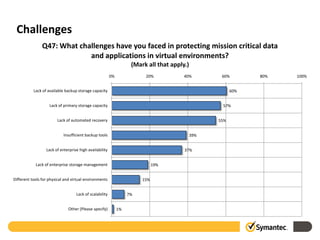
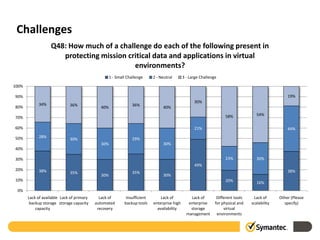
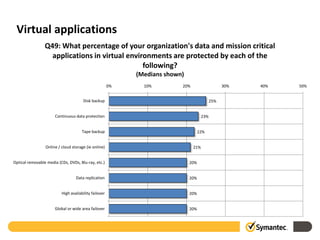
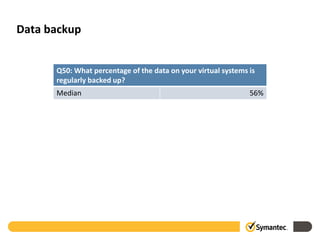
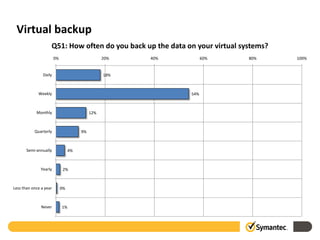
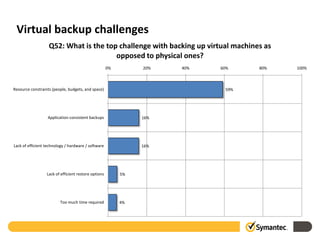
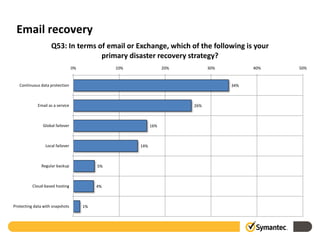
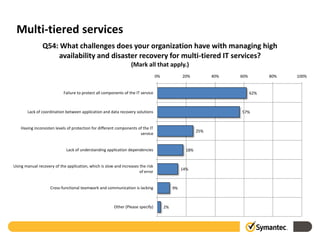
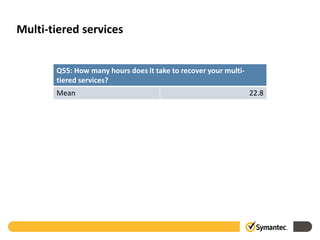
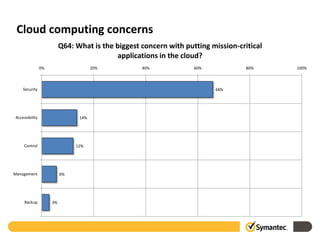
The 2010 Symantec Disaster Recovery Study surveyed 1,700 enterprises, revealing that virtualization and cloud adoption complicate disaster recovery (DR) planning, with only 20% of virtual environments protected adequately. Key challenges include resource constraints, a lack of proper testing, and heightened concerns about cloud security, as organizations struggle with downtime averaging 5 hours, exceeding the expected 2-hour recovery time. Recommendations emphasize treating mission-critical data uniformly across environments, employing integrated toolsets, and prioritizing low-impact backup solutions to minimize downtime.