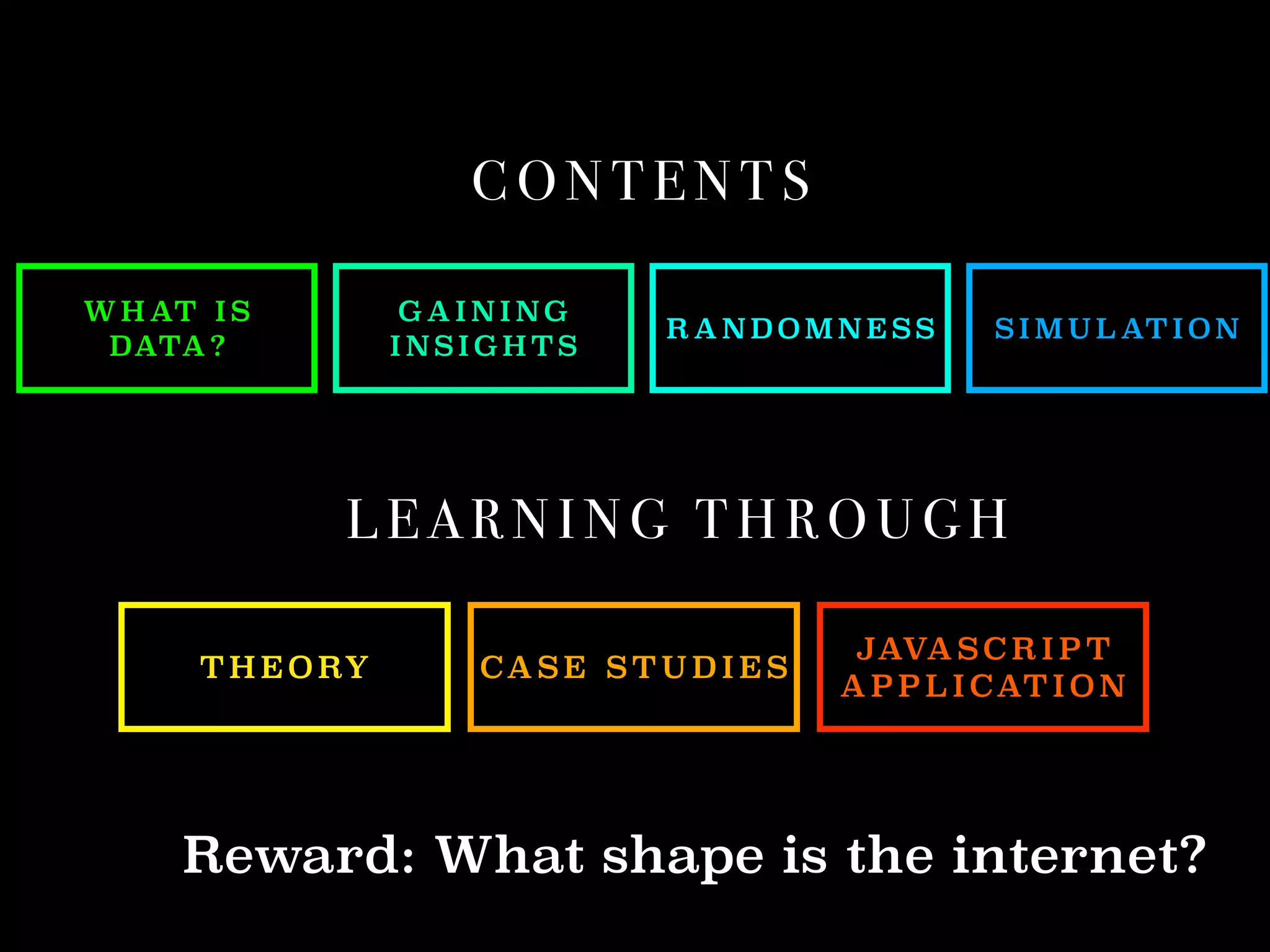
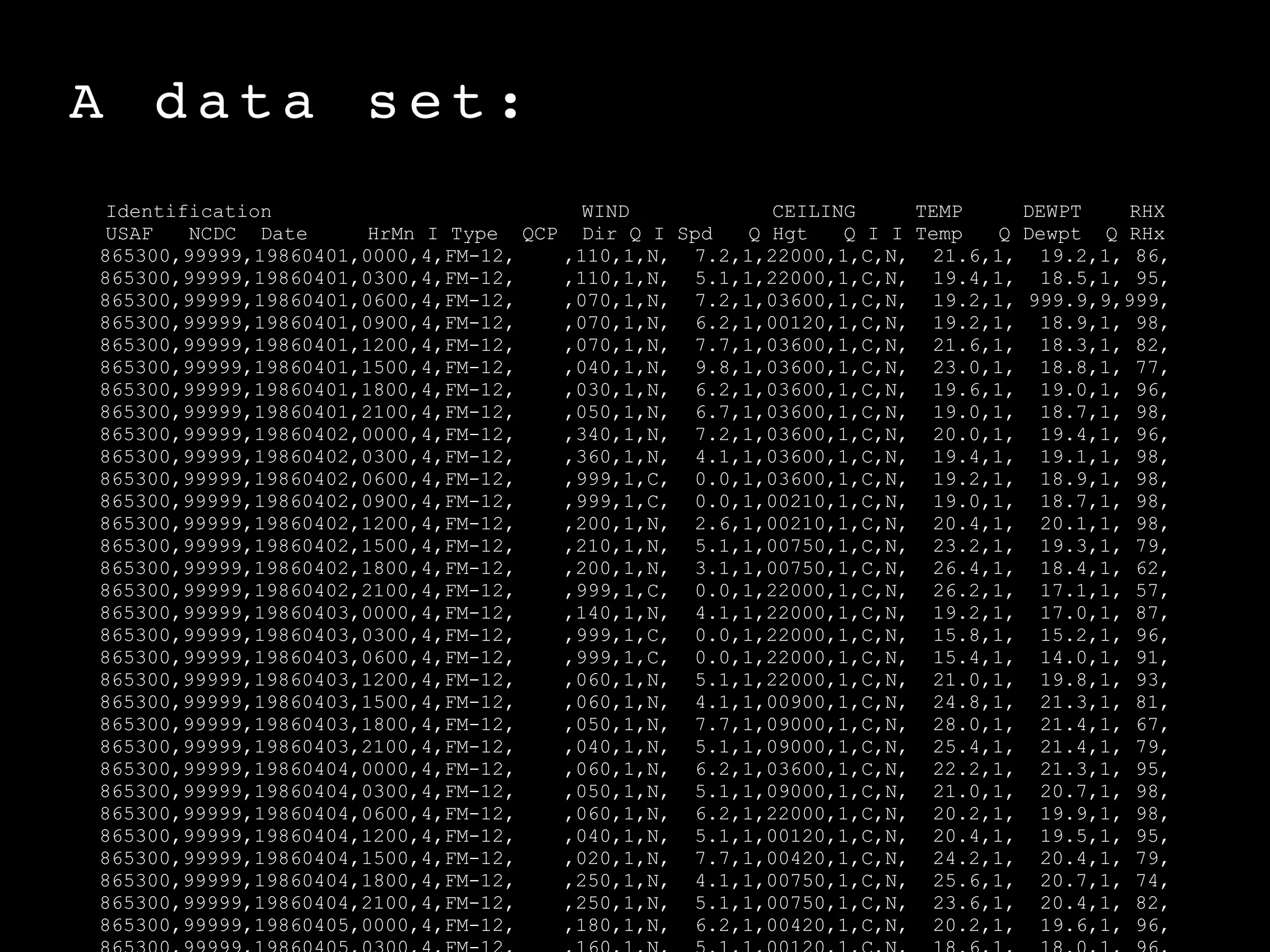
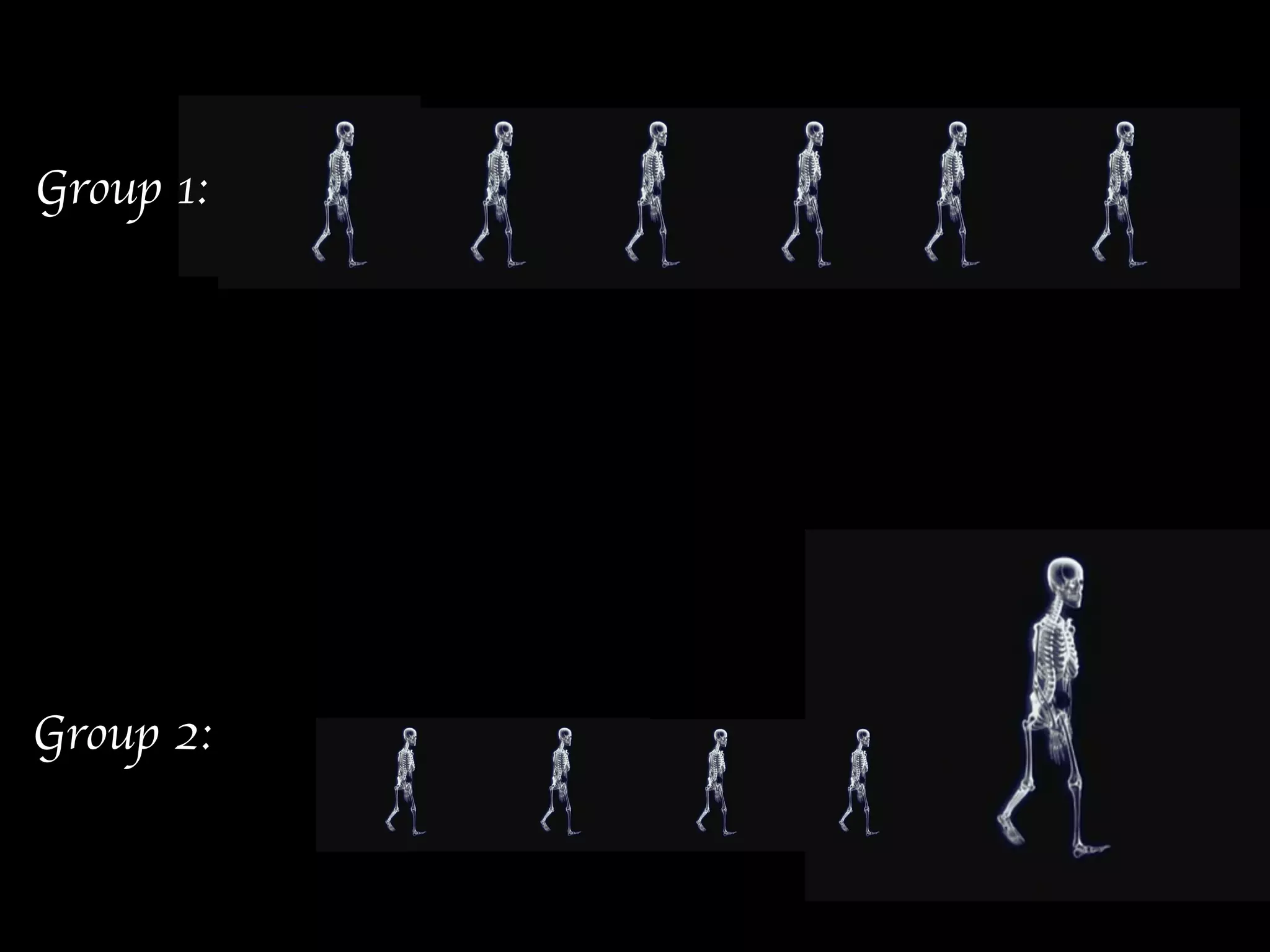
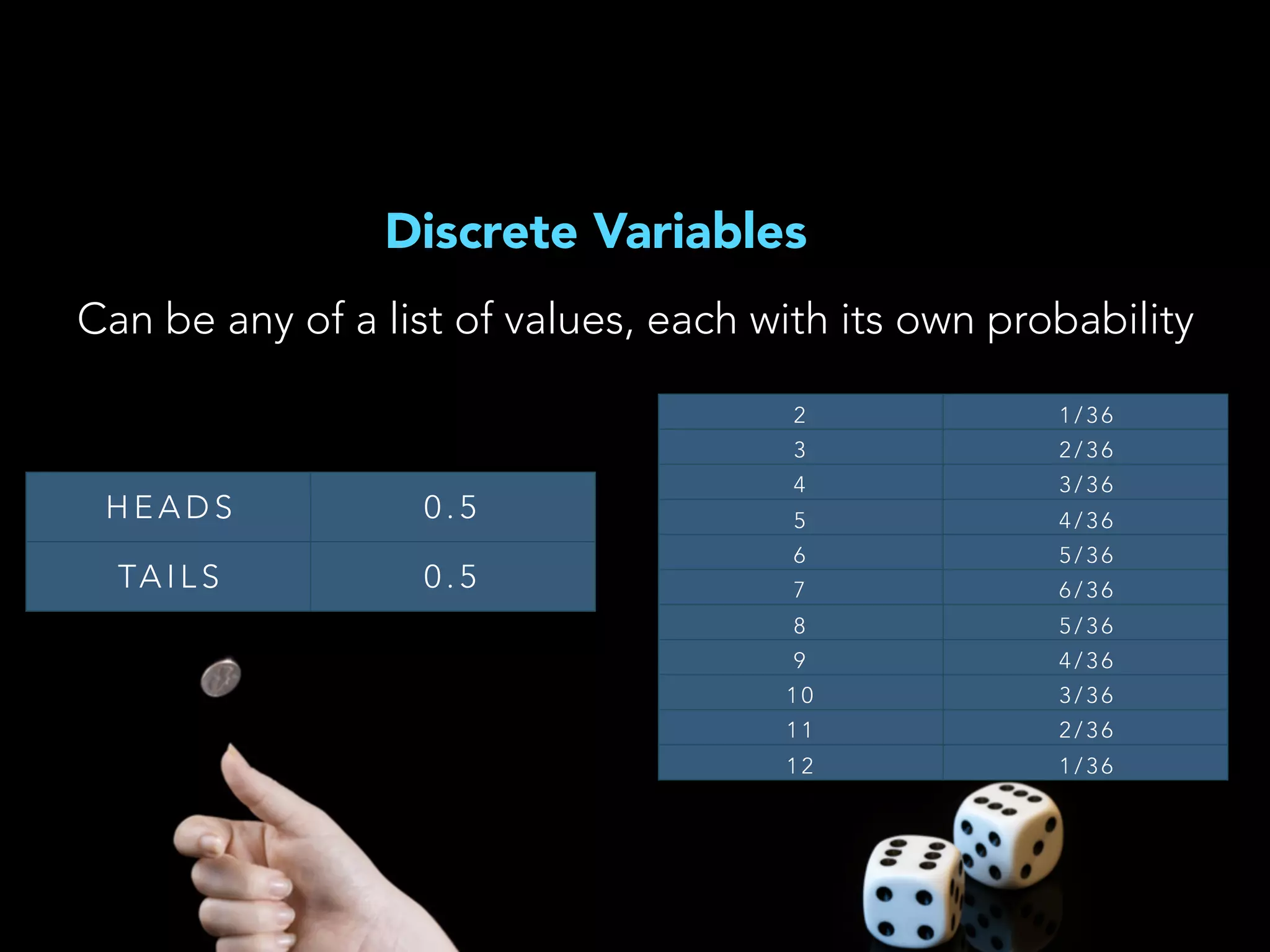
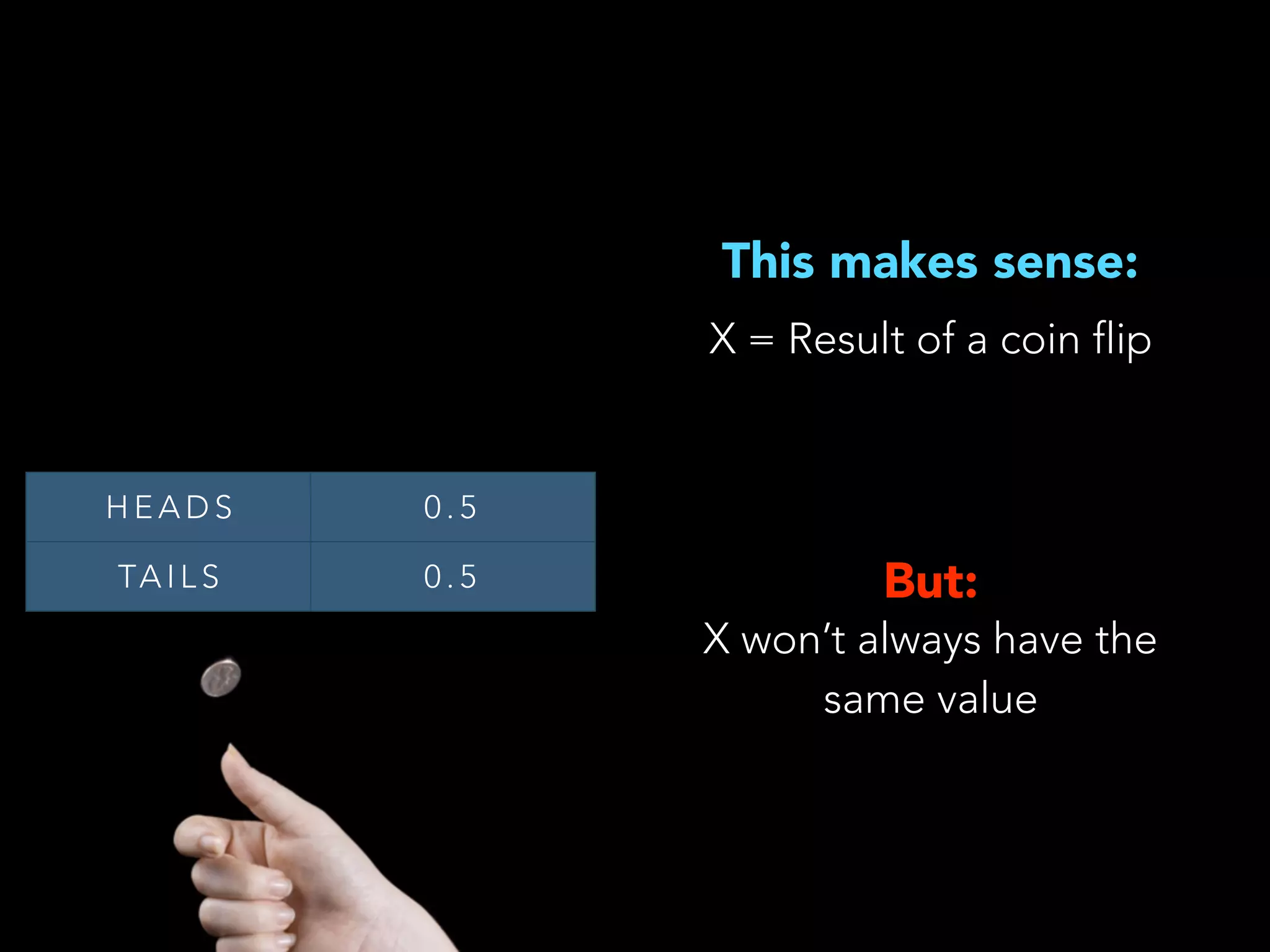
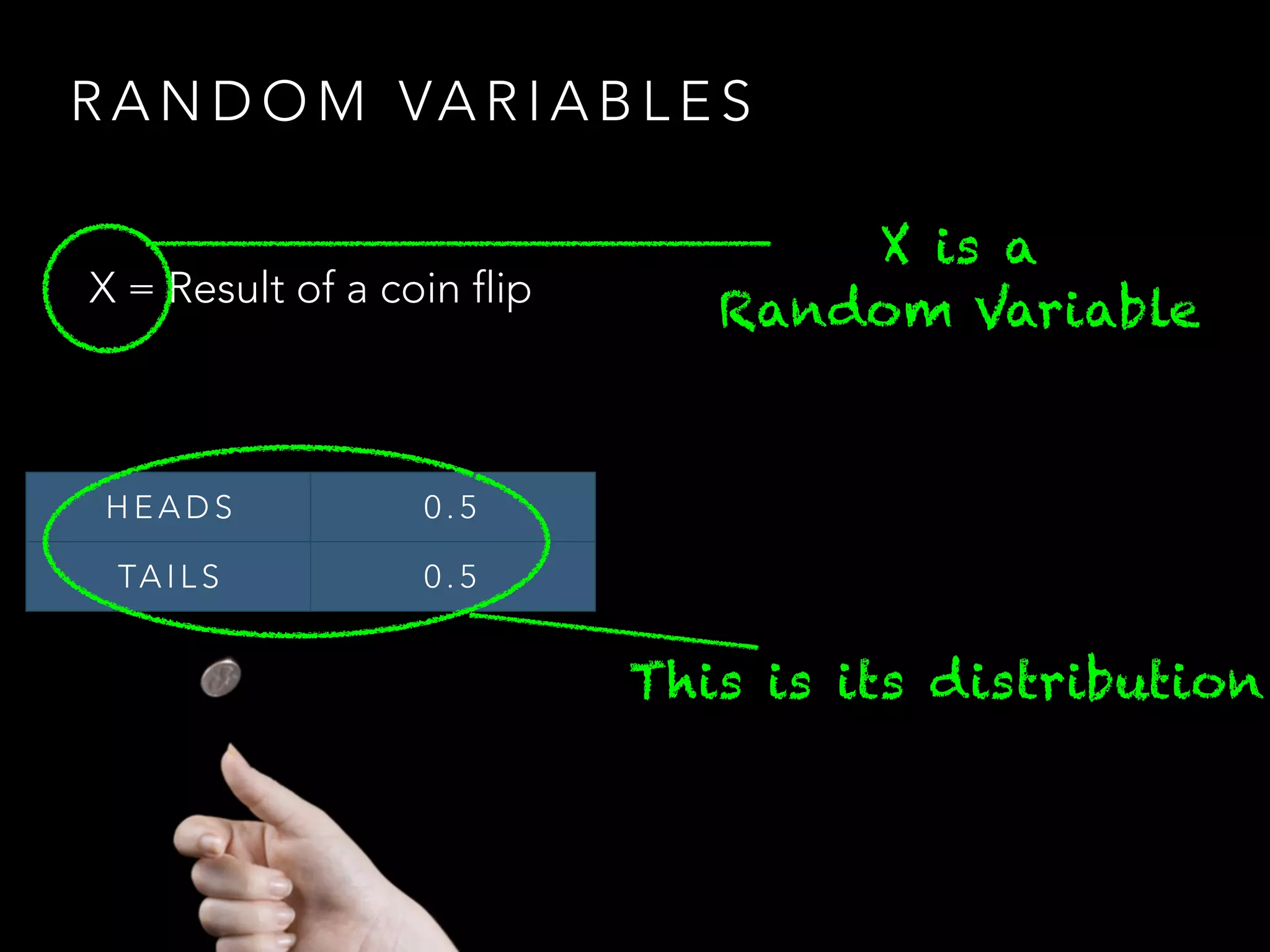
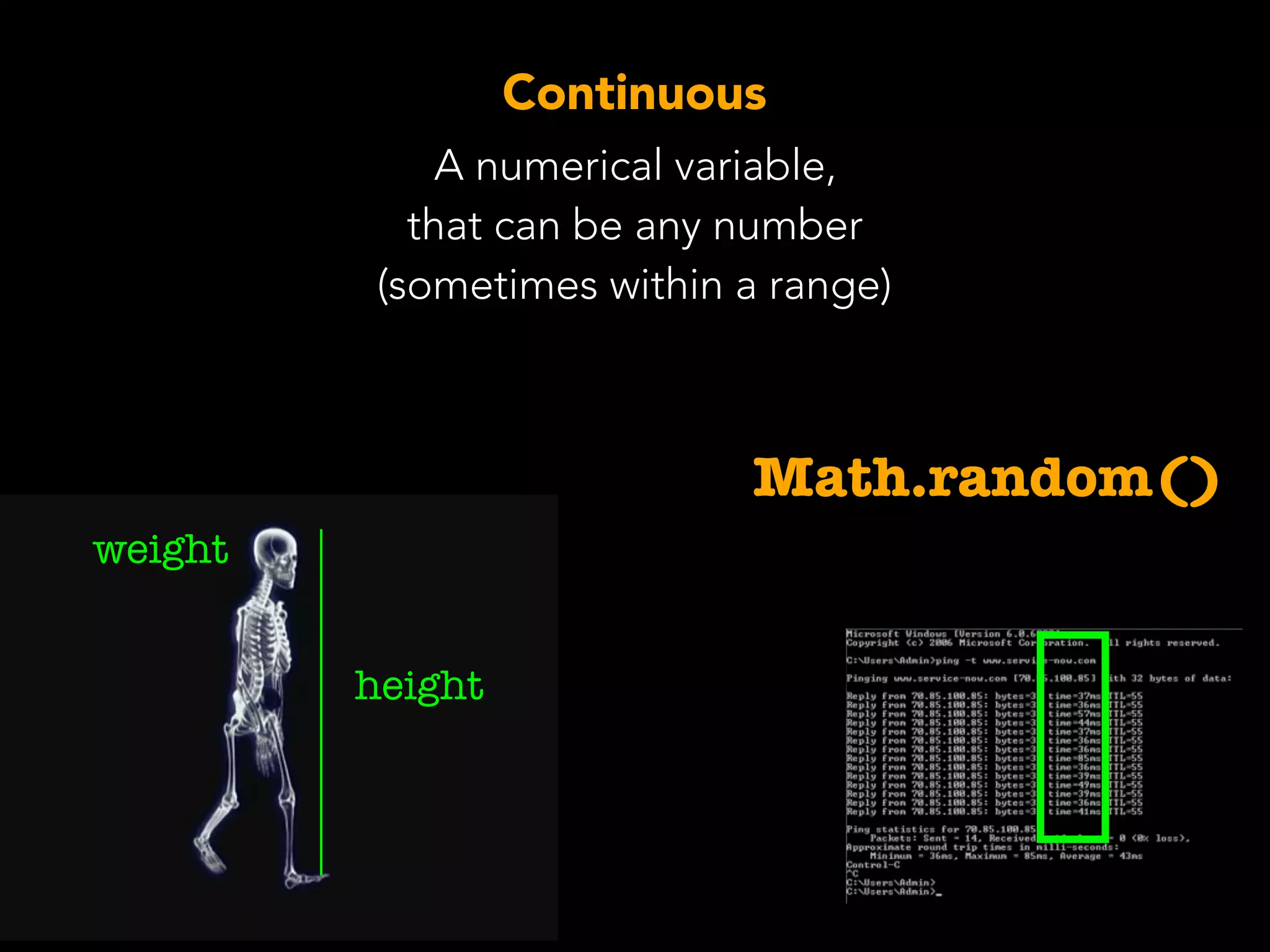
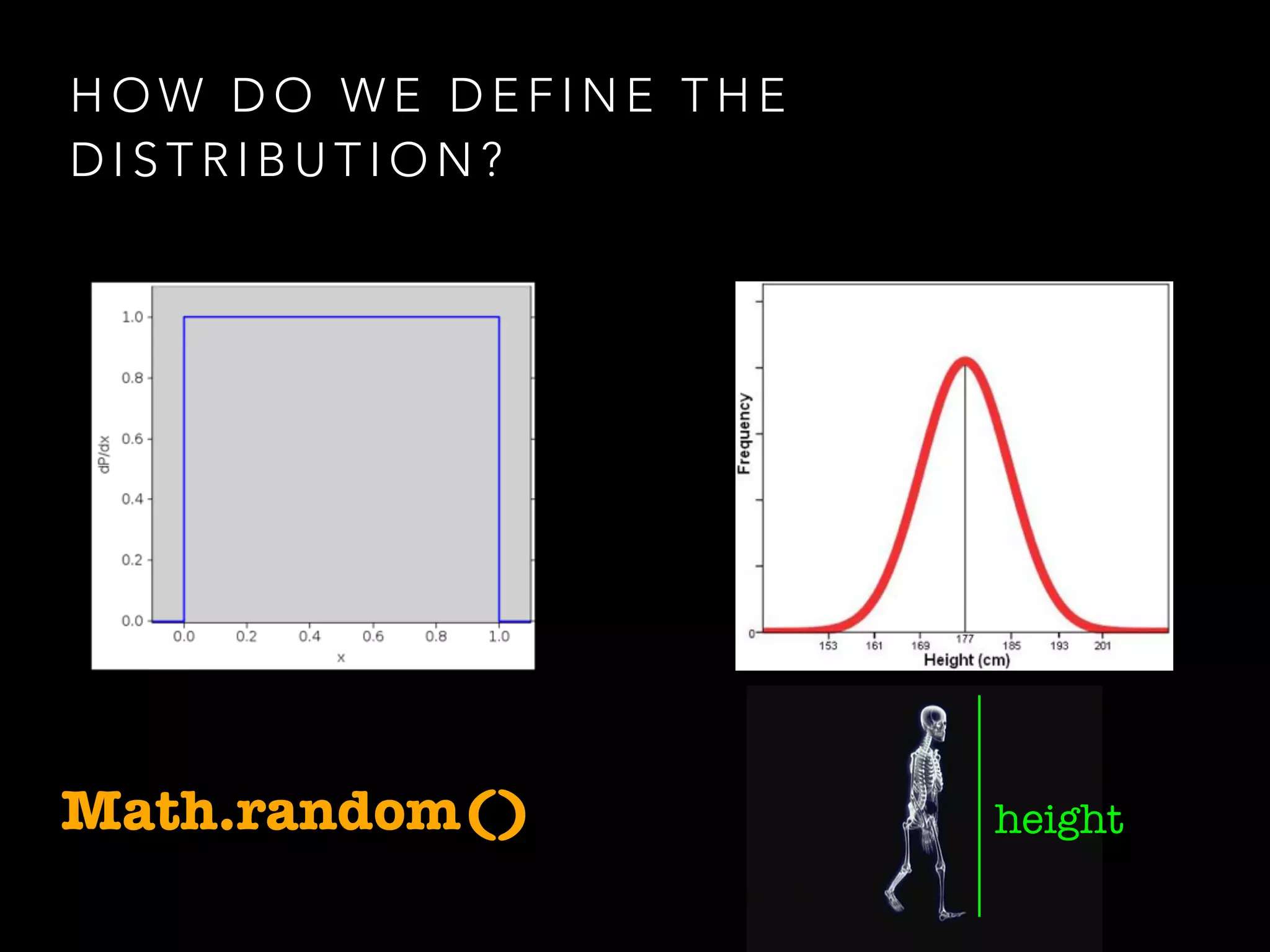
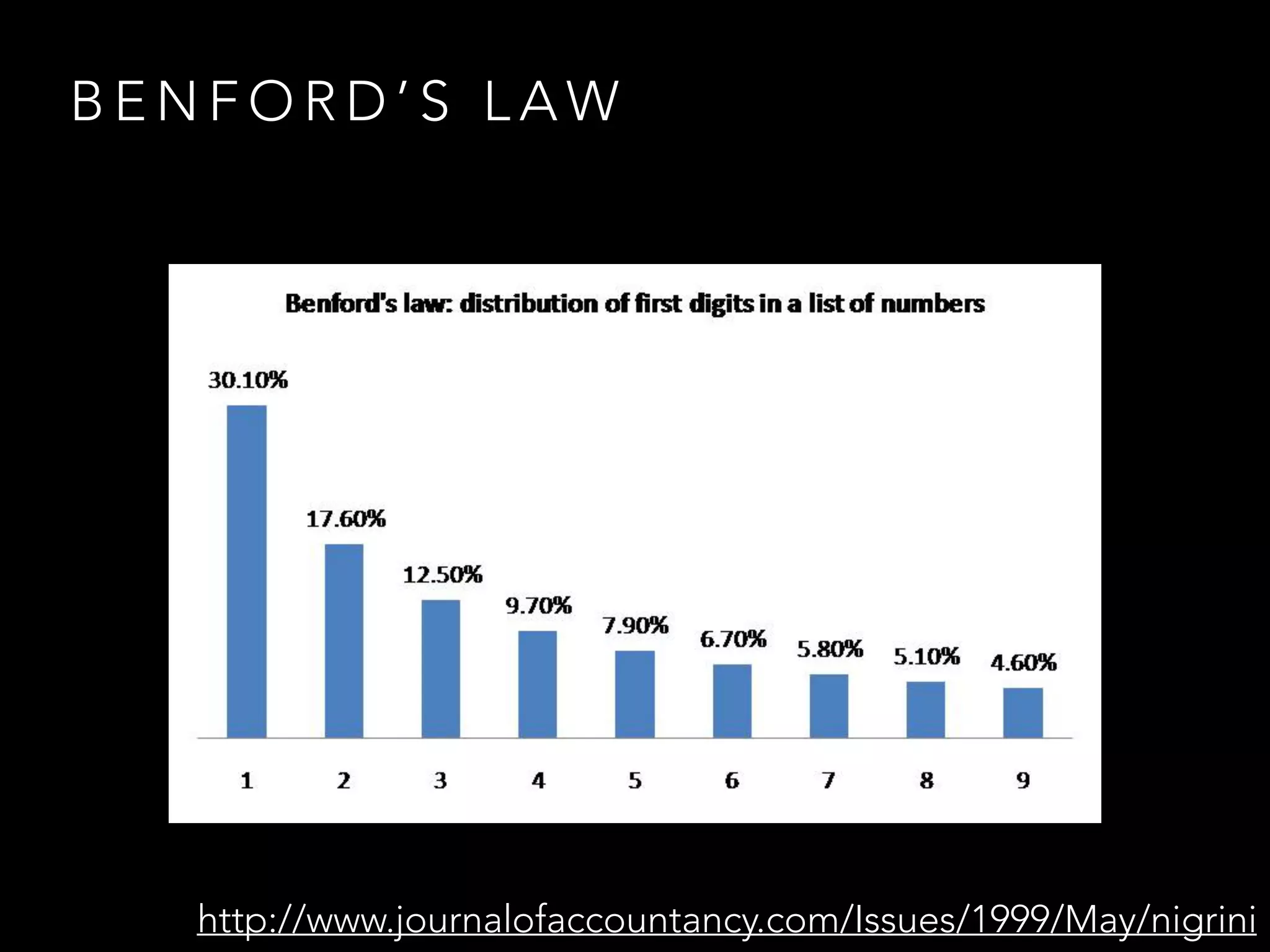
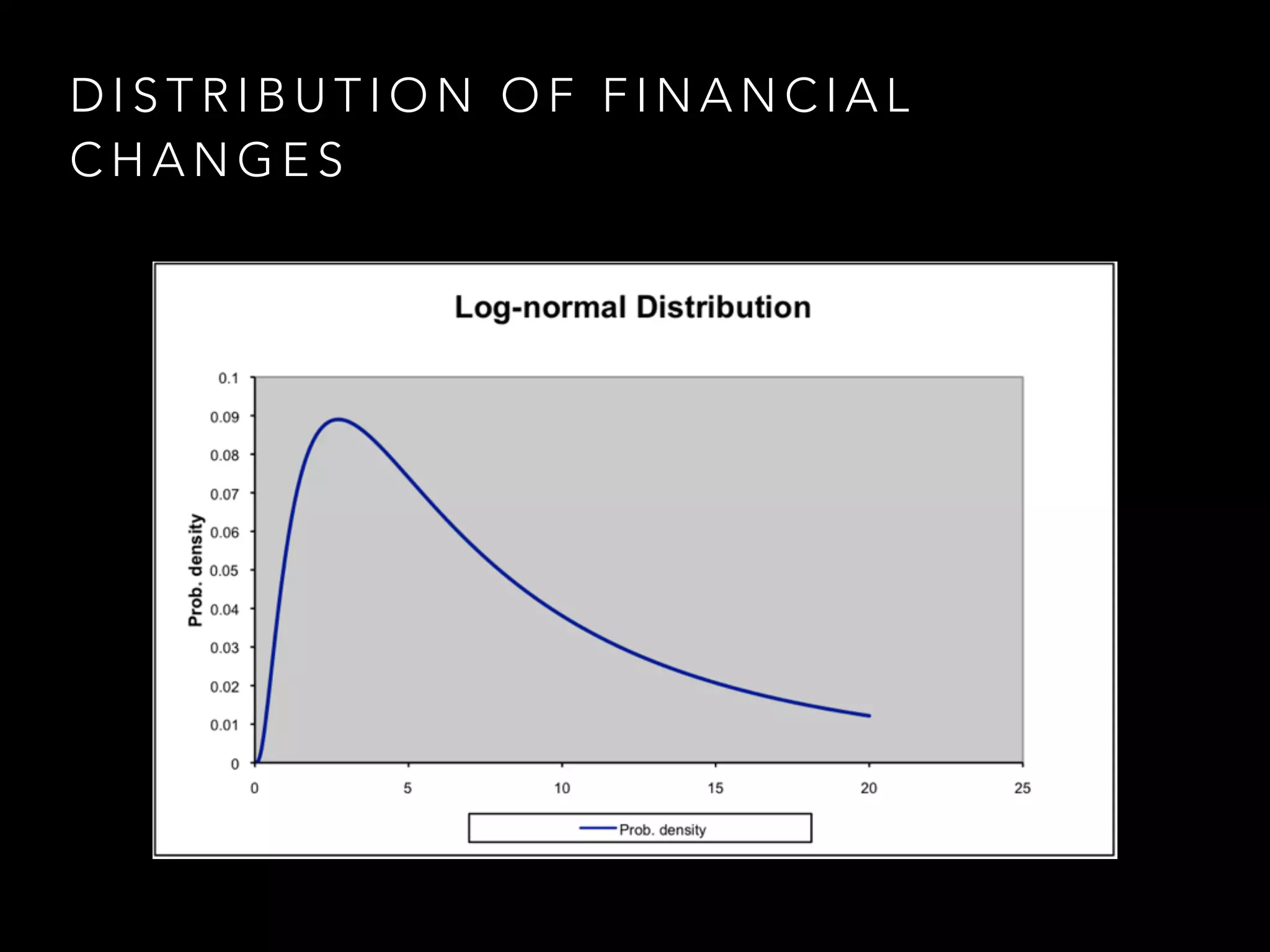
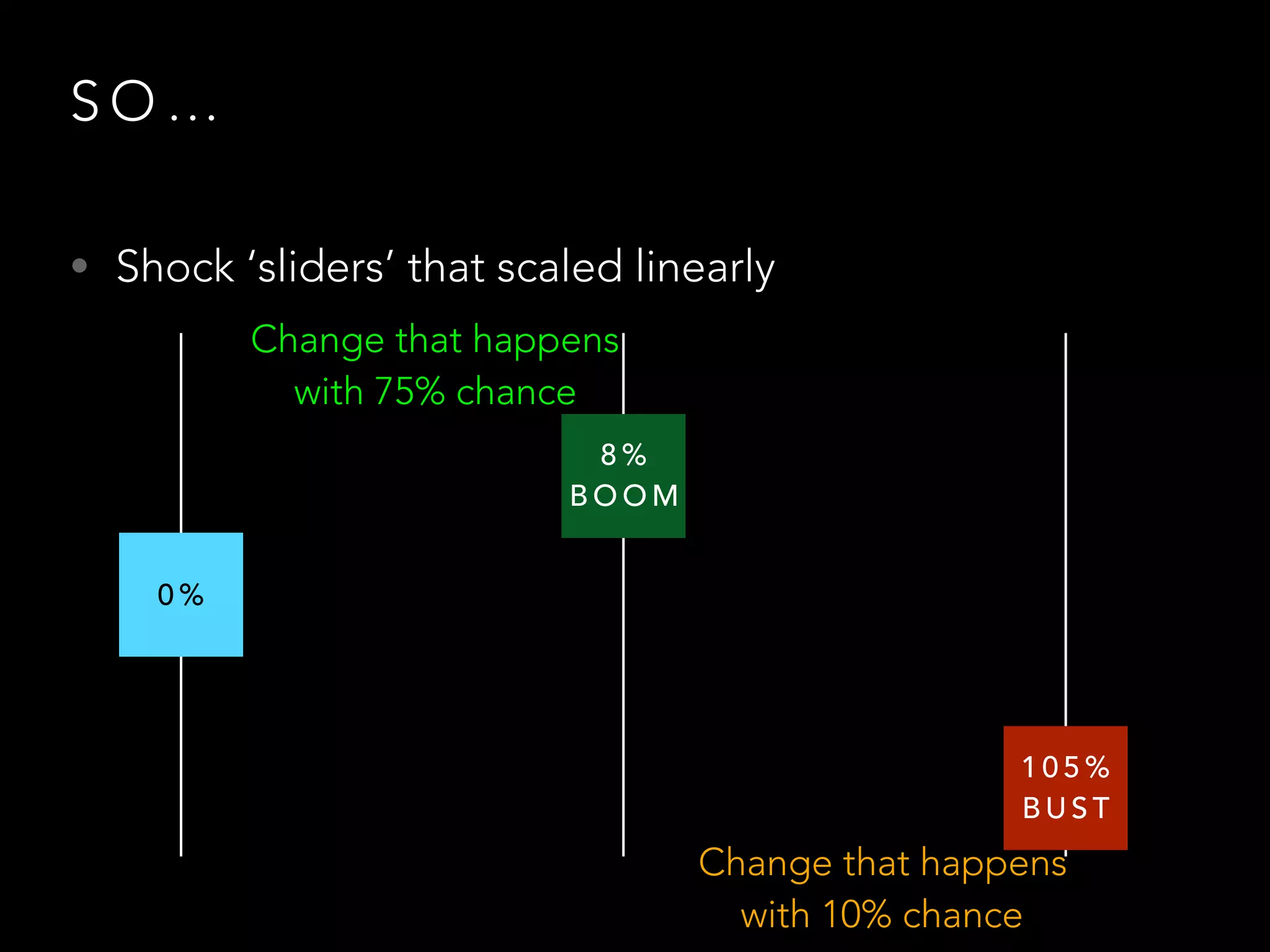
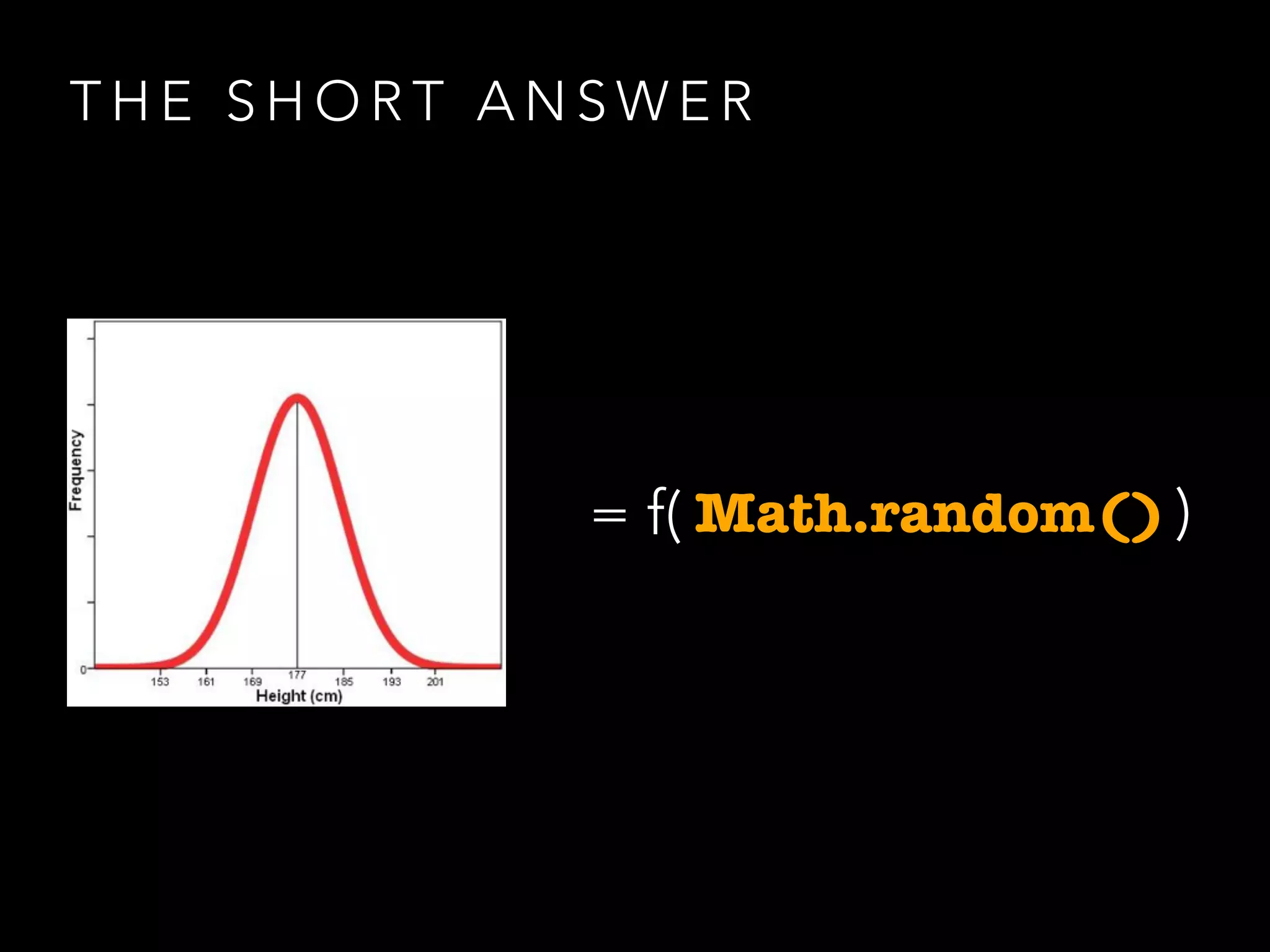
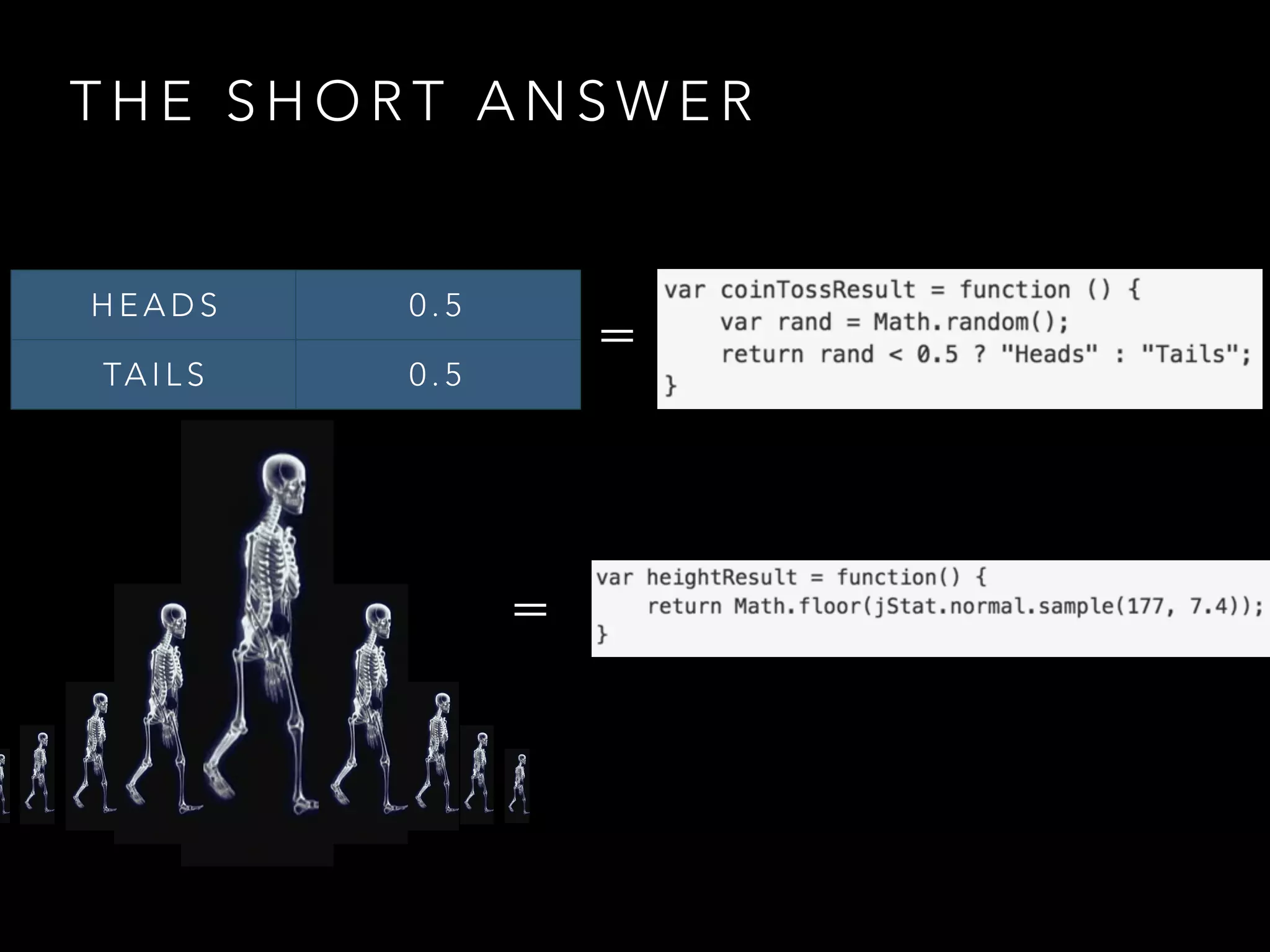
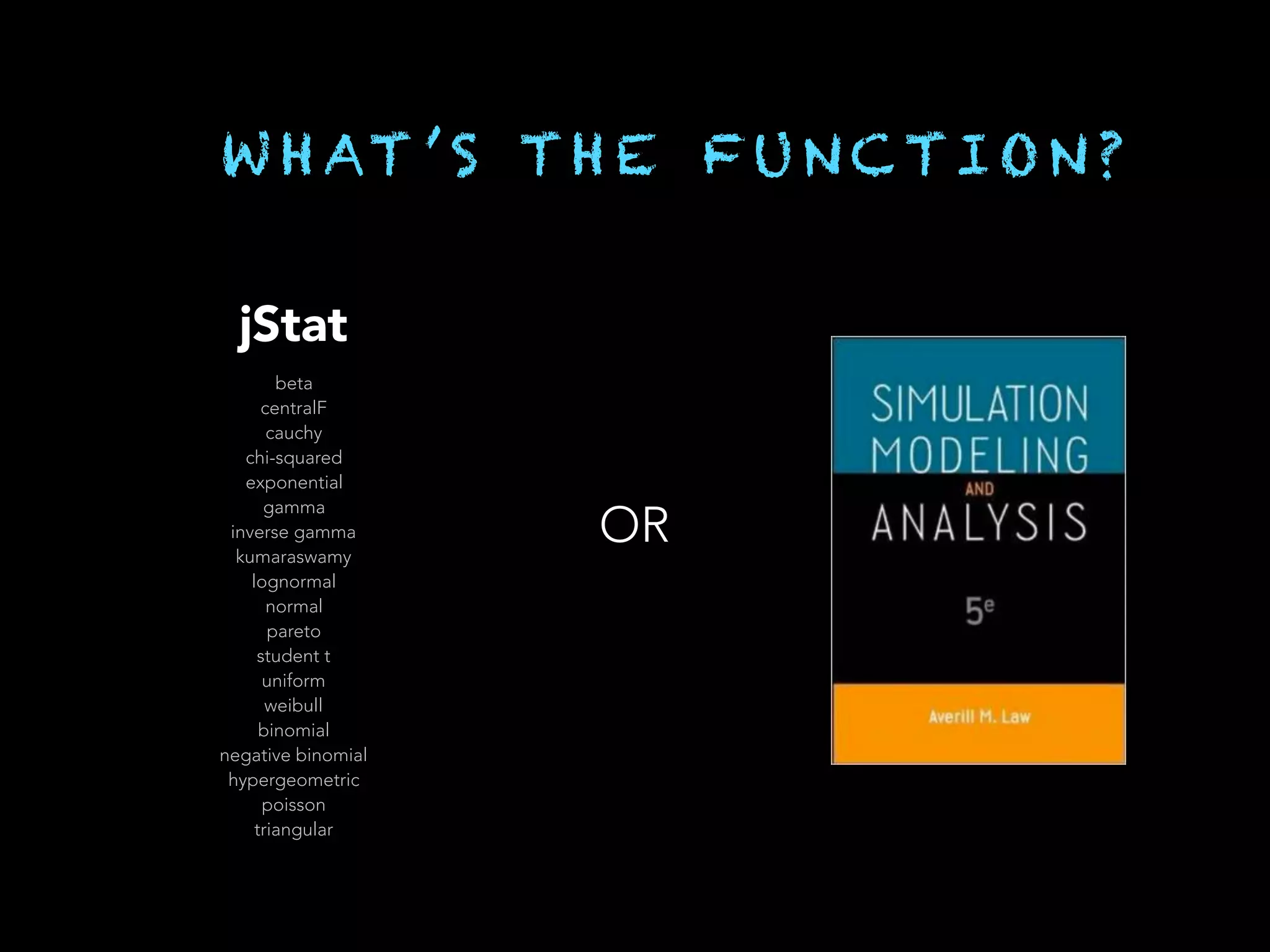
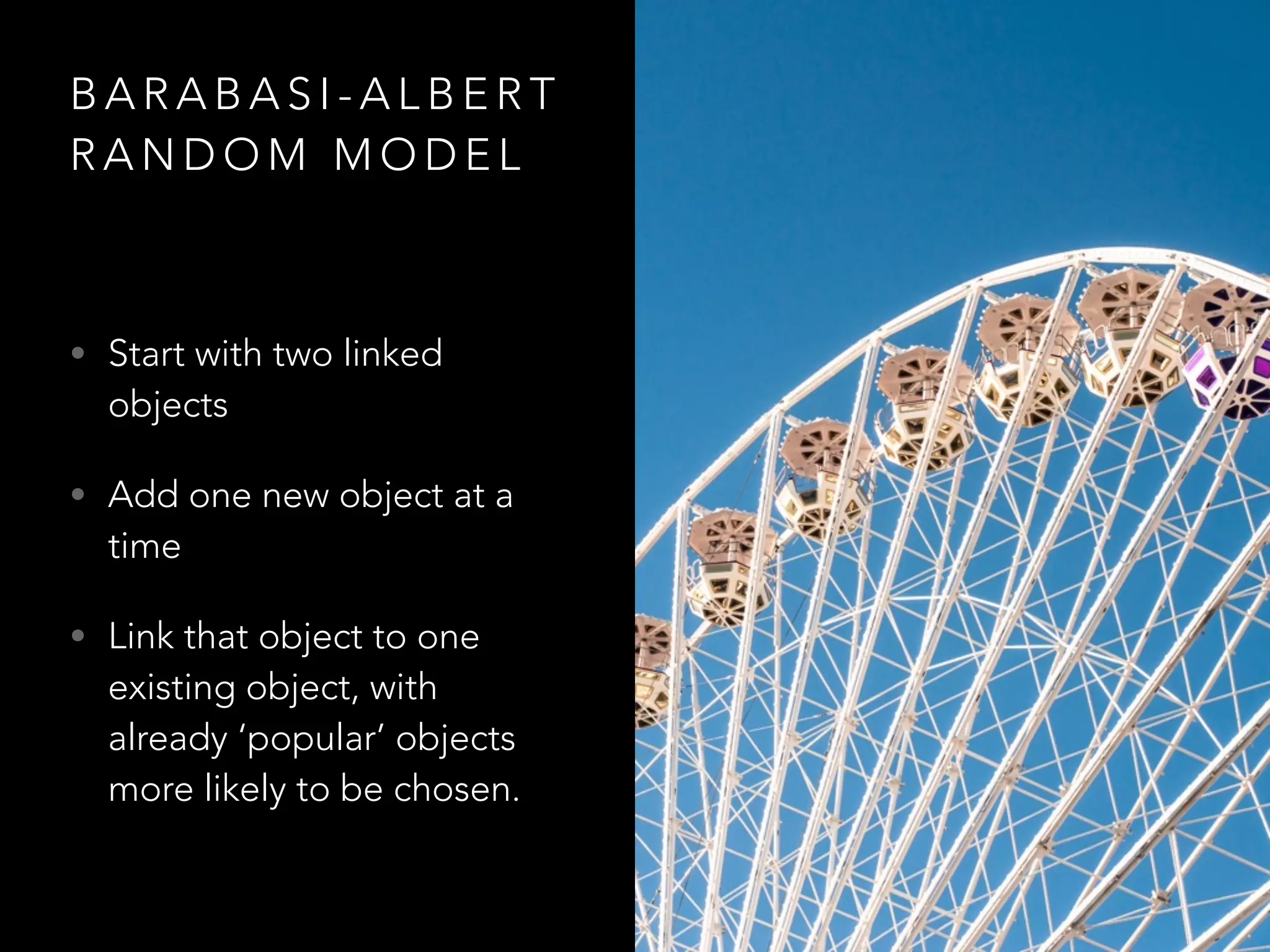
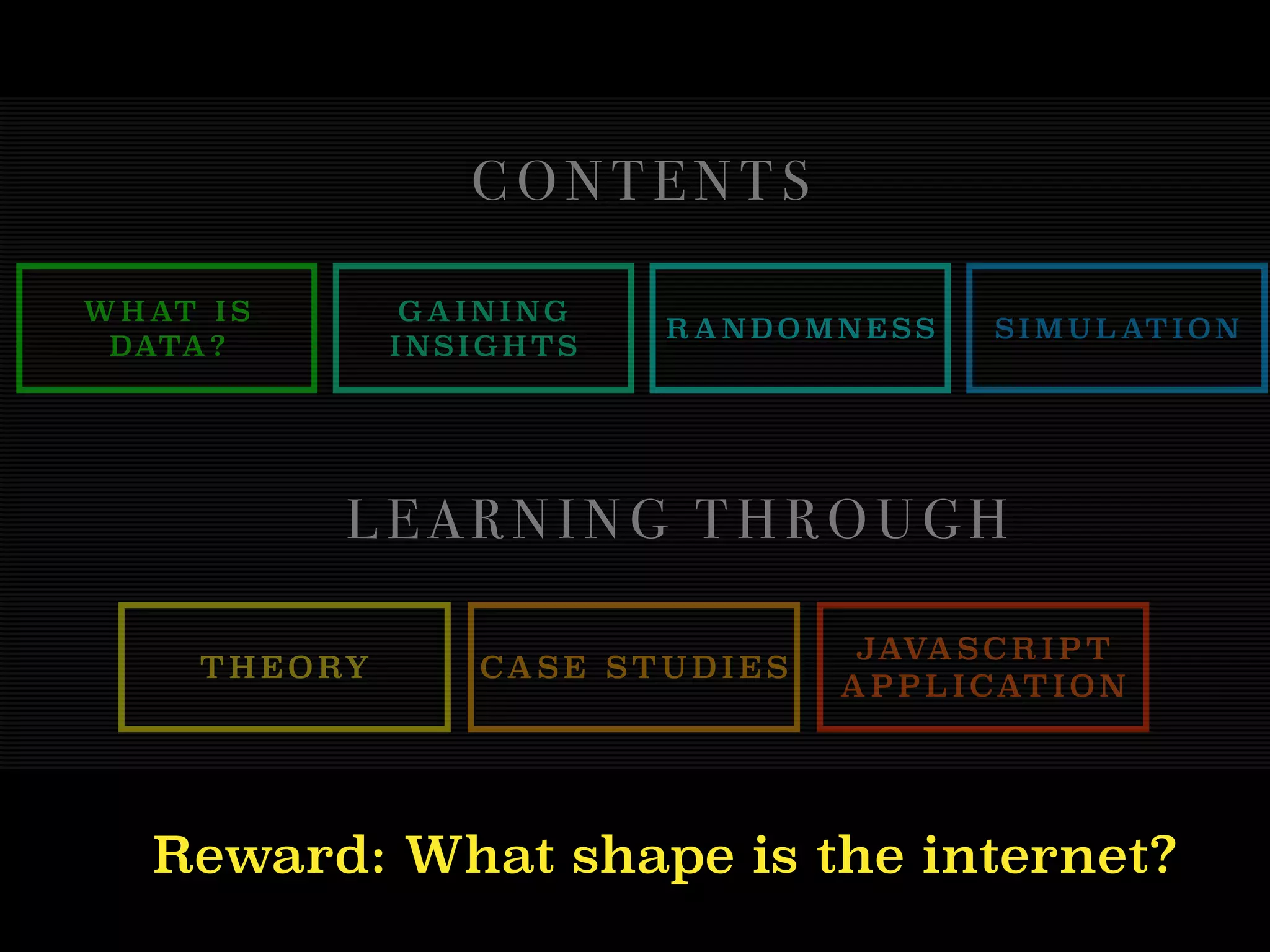
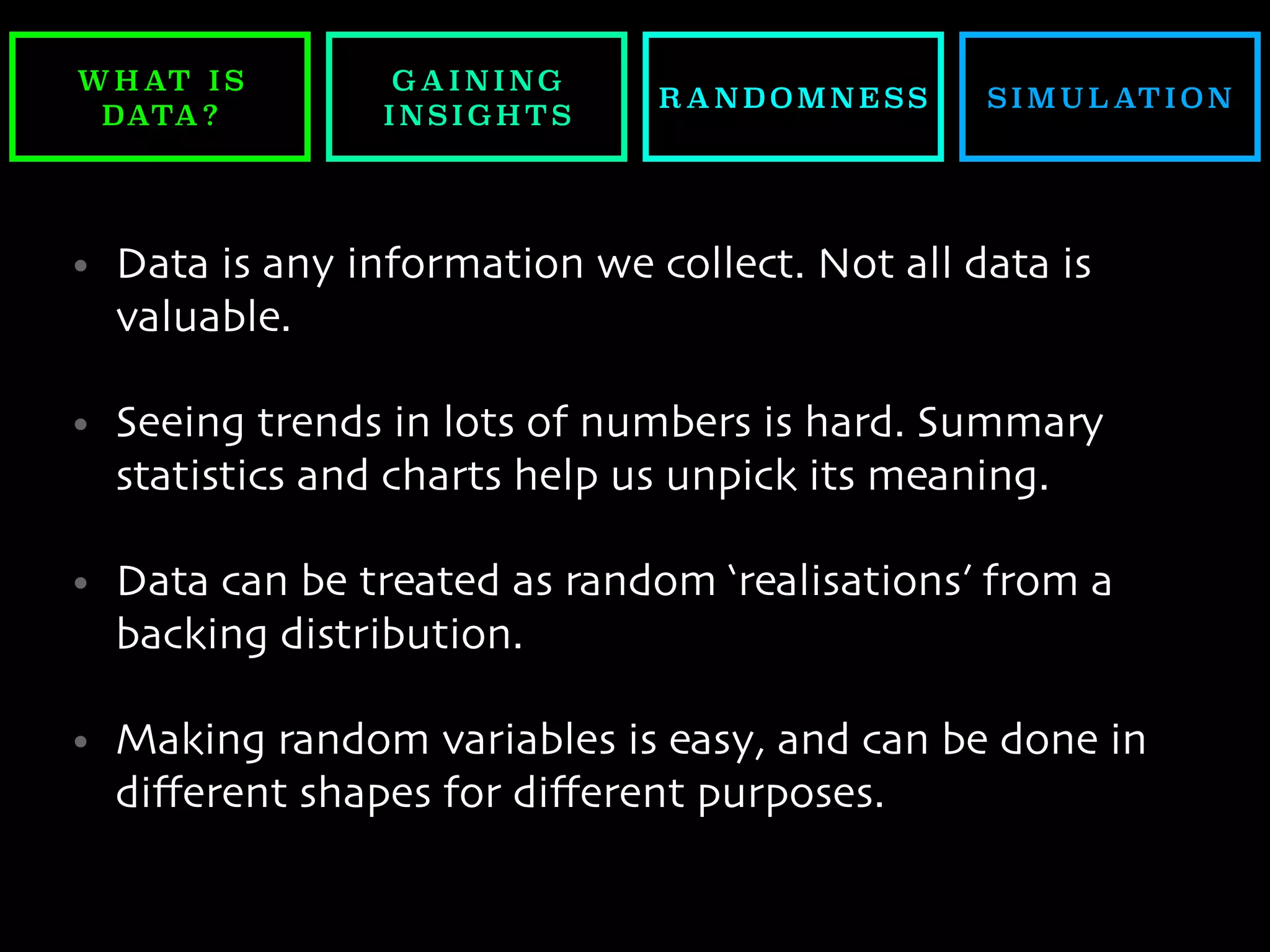
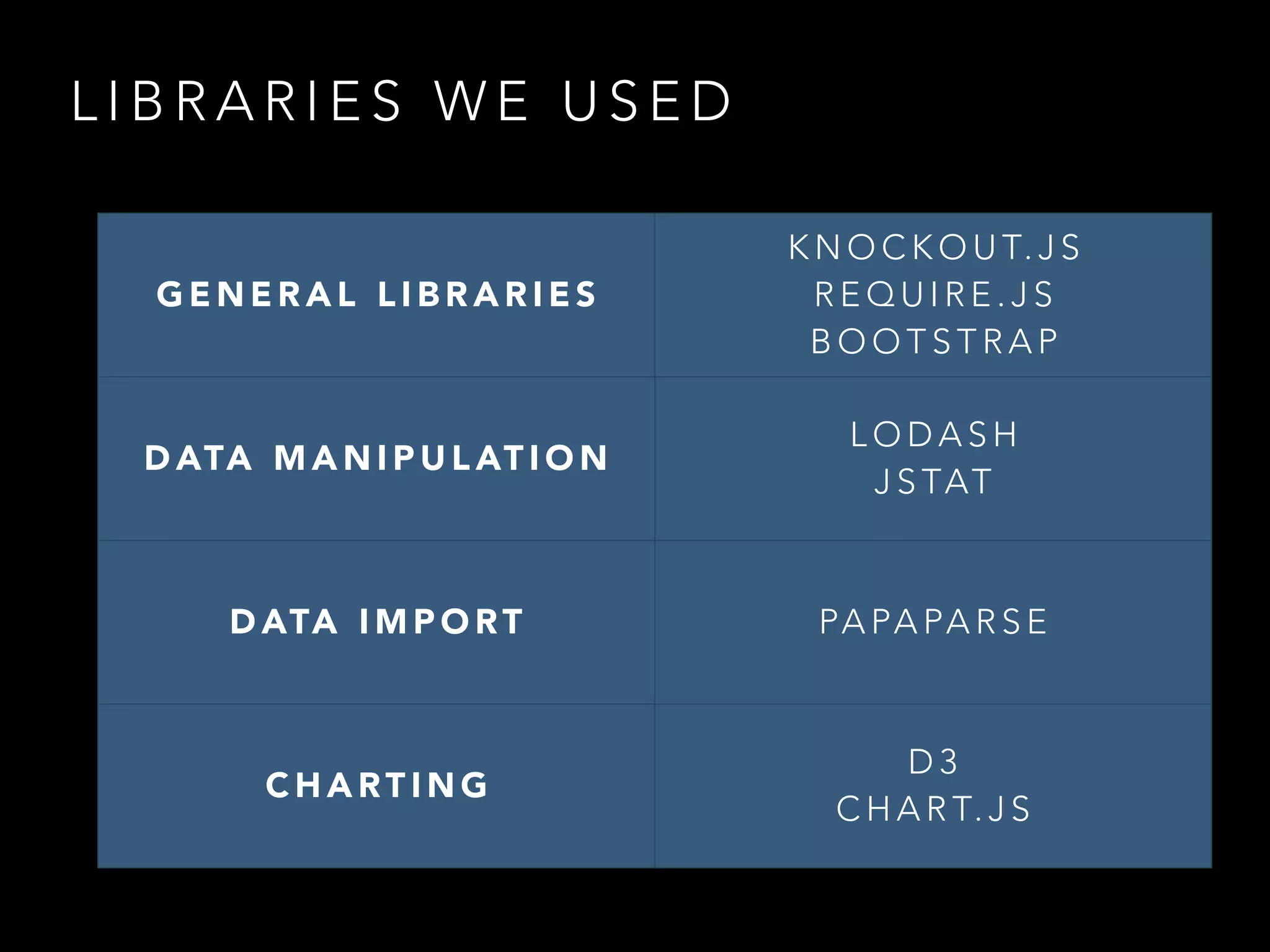
The document discusses statistical programming in JavaScript and introduces the concepts of data, insights, and random variables. It highlights the importance of understanding different types of data and various statistical measures, as well as the implications of randomness in programming and data analysis. The content includes practical applications, such as data collection methods and simulations, aimed at improving data interpretation and decision-making.