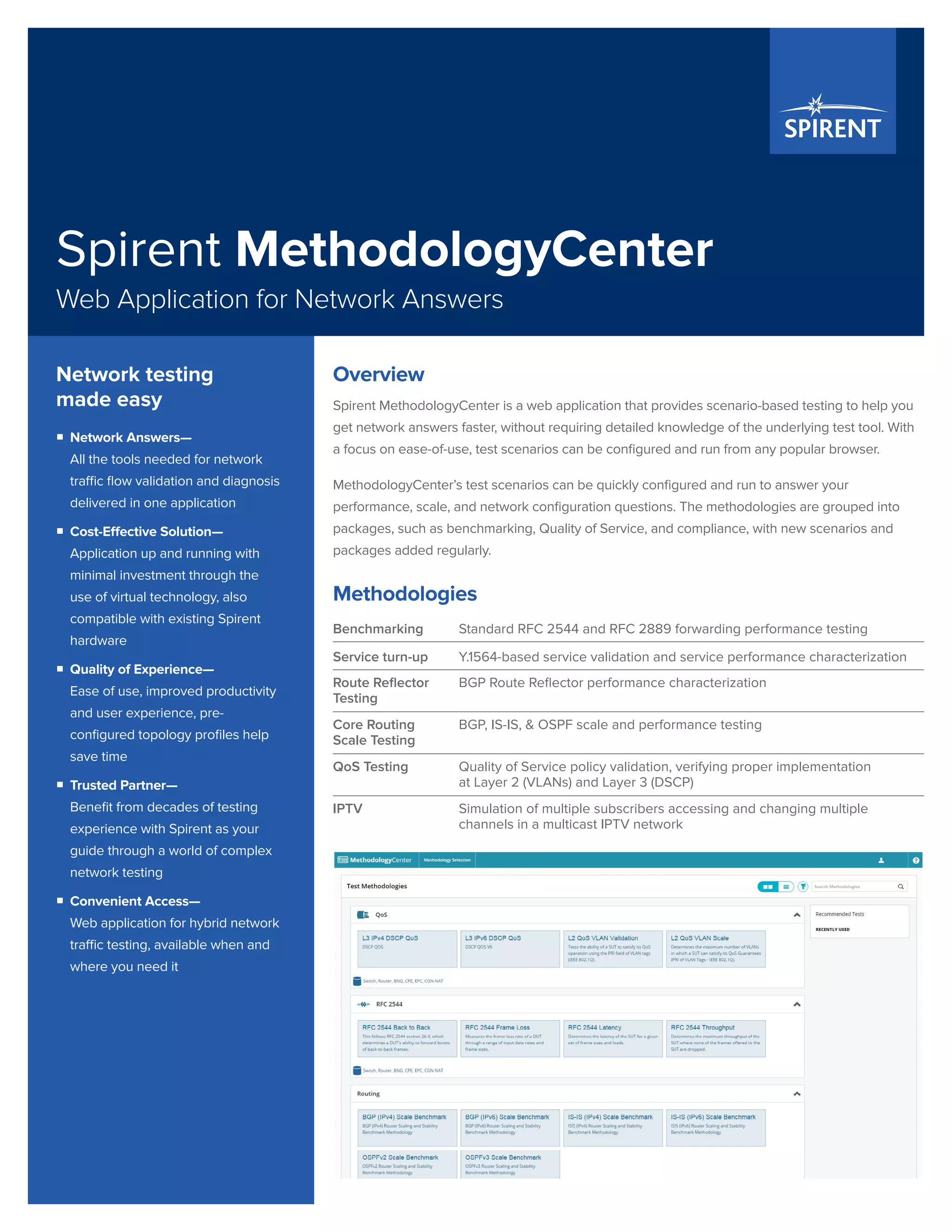
Spirent MethodologyCenter is a web application designed for scenario-based network testing, enabling users to quickly configure and run tests without deep tool knowledge. It offers a growing library of standardized test scenarios and aims to simplify network performance assessment. The application is cost-effective, user-friendly, and accessible from any popular browser, enhancing productivity and user experience.