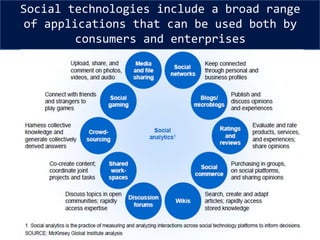
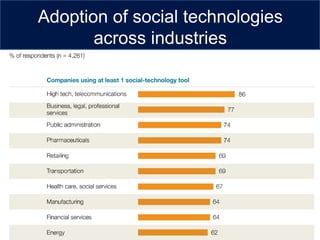
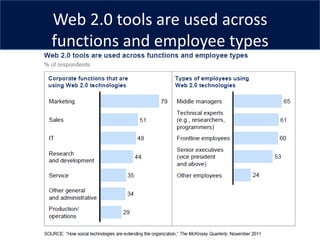
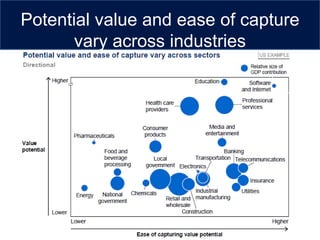
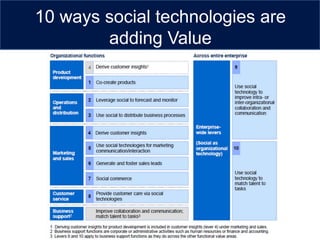
This document discusses the rise of social technologies and their value and impact. It notes that social technologies have become ubiquitous, changing how billions of people live and work. Companies are increasingly using social technologies to engage customers, improve performance and advance their missions. The document outlines 10 ways that social technologies are creating value for businesses, including through co-creating products, demand forecasting, distributing business processes, and improving communication and collaboration. Fully embracing social technologies may require transformational organizational changes to develop knowledge-sharing cultures that can best capture potential value.













![For me.
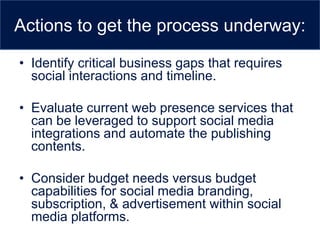
• In many instances, this is just another cost versus benefit exercise. Most of
the Small/Medium business IT are internal resource limited and it is
prudent to outsource certain support services, such as developing a web
strategy for website development [design/hosting, Search engine
optimization (SEO), Information architecture (IA), User experience
engineering(UXE), content development]. On the other hand, those
Business/IT/marketing teams with established network support groups
and comprehensive management capabilities may elect to do the job
themselves in Enterprise business environment. There is no one right or
wrong answer, it depends on specific environments.
• Conversely, if outsourcing is a viable option, there are scores of vendors
interested in obtaining small, medium and enterprise business. Social
media integration services is a growing market within website
development industry and the list of vendors includes
small companies in just matter of click in Google search providing service
offerings such as Website hosting, development, content management,
outsourced marketing, help-desk, technical support, etc.](https://image.slidesharecdn.com/socialtechnologies-121110024103-phpapp01/85/Social-technologies-37-320.jpg)