Embed presentation









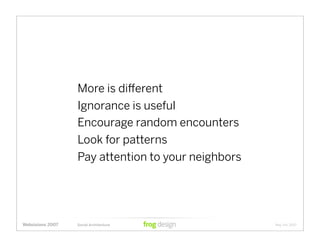








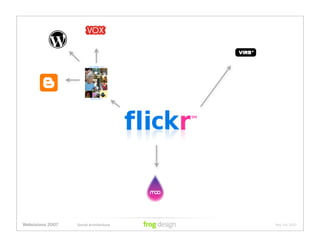
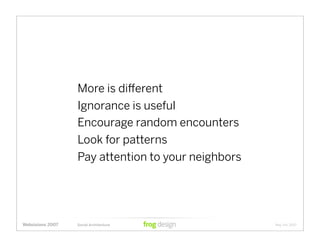
Sean Madden gave a presentation at Webvisions 2007 about modeling the next generation of social architecture. He discussed several concepts for improving social networks, including tagging, voting, customization, and purposeful self-organization. Madden argued that social networks should leverage ubiquitous computing and emergent organization to reduce cognitive load on users and organize information without inhibiting creation or consumption.