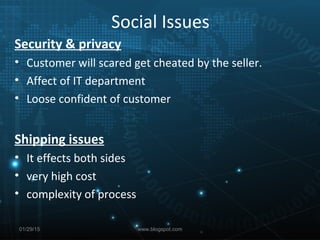
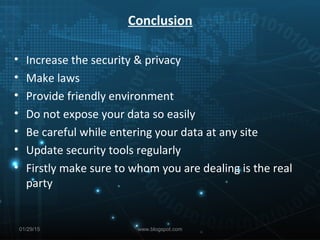
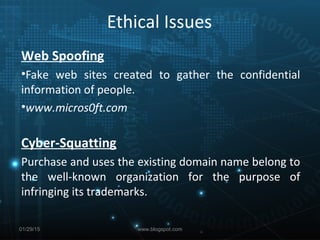
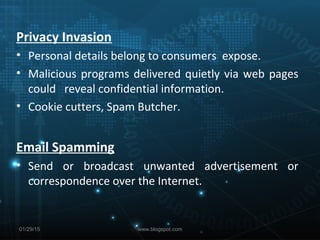
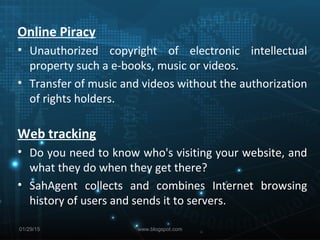
This document discusses several social and ethical issues in e-commerce, including web spoofing, cyber-squatting, privacy invasion, email spamming, online piracy, web tracking, and copyright infringement. It also addresses the threats posed to e-commerce servers, such as financial loss, and social issues like security, privacy, and shipping problems. The conclusion recommends increasing security and privacy protections, enacting new laws, providing a friendly online environment, being careful about sharing personal data, and regularly updating security tools.
![Copyright
• The copyright laws protect Intellectual property in its
various forms, and cannot be used freely.
• The distribution rights are with the copyright holder.
The Threats Posed to E-Commerce Servers
• The server can be viewed as the central repository for
your “E-Commerce Place of Business” [which consists
of the actual website which displays your products and
services, the customer database, and the payment
mechanism].
• Financial loss
01/29/15 www.blogspot.com](https://image.slidesharecdn.com/socialandethicalissuesincommerce-150129015452-conversion-gate01/85/Social-and-ethical-issues-in-commerce-6-320.jpg)