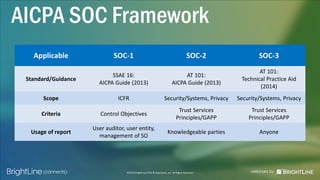
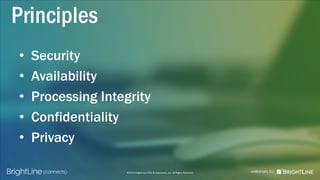
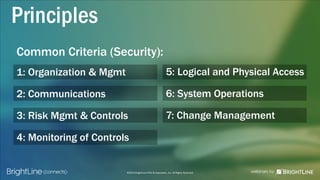
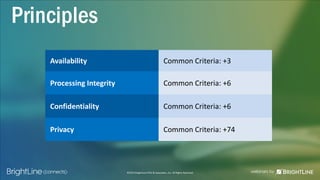
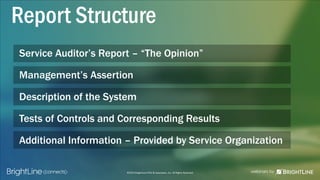
The document provides an overview of SOC 2 reports, emphasizing their importance for building trust and compliance with regulatory requirements. It outlines the AICPA framework, key principles, report types, and considerations for service organizations and user entities. Additionally, it includes mapping of SOC 2 to other standards and the necessity of third-party assessments in vendor management programs.