Embed presentation
Download to read offline
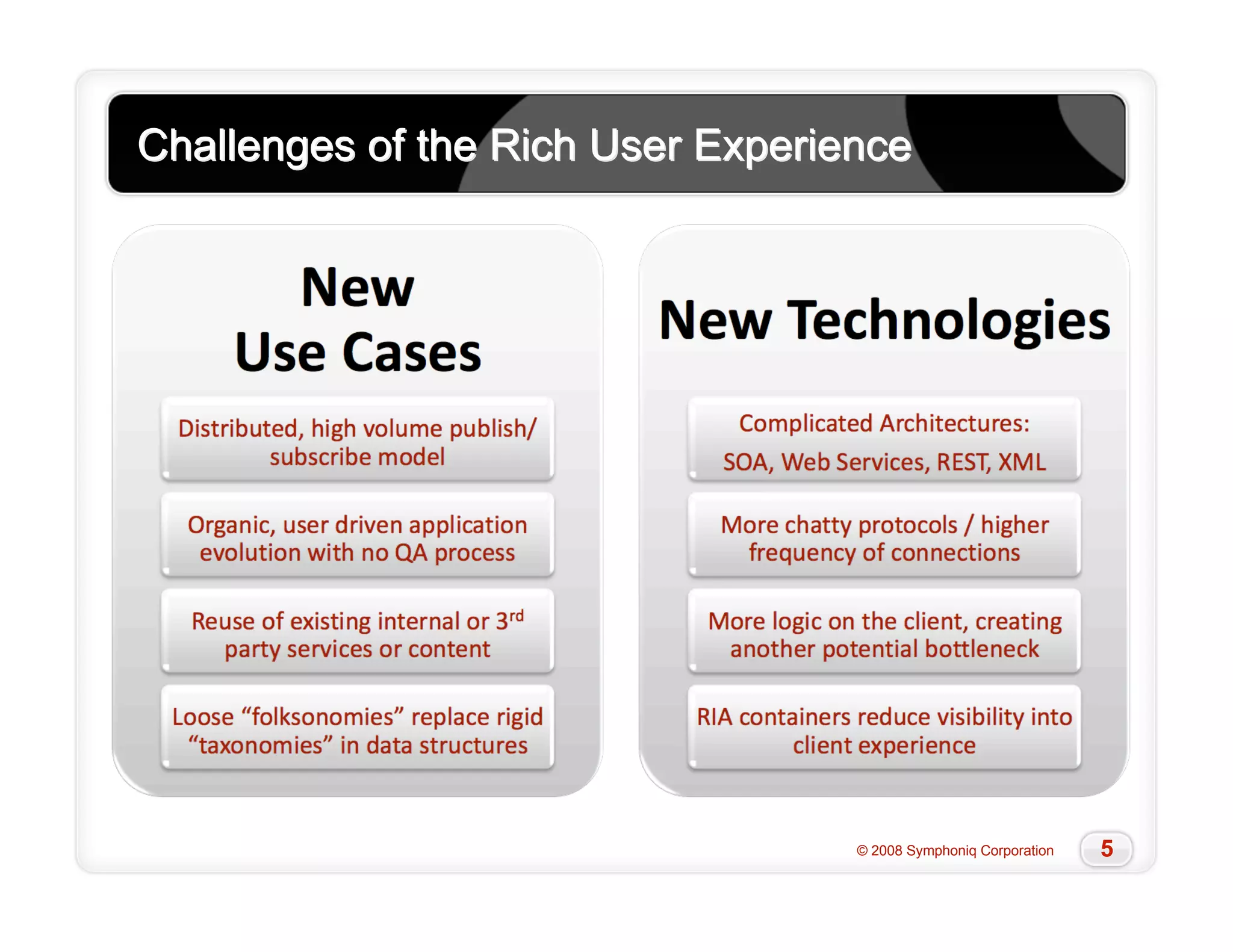
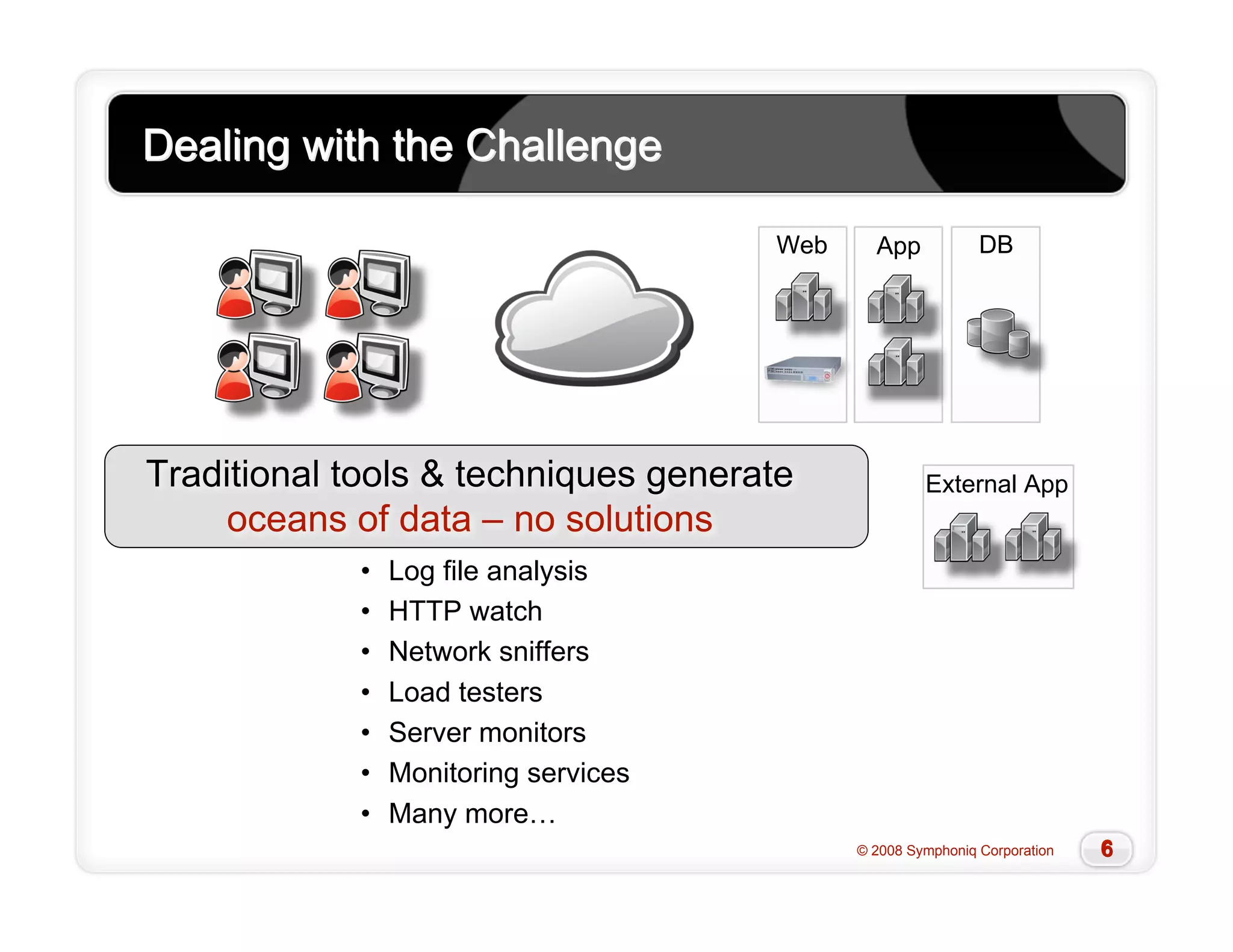
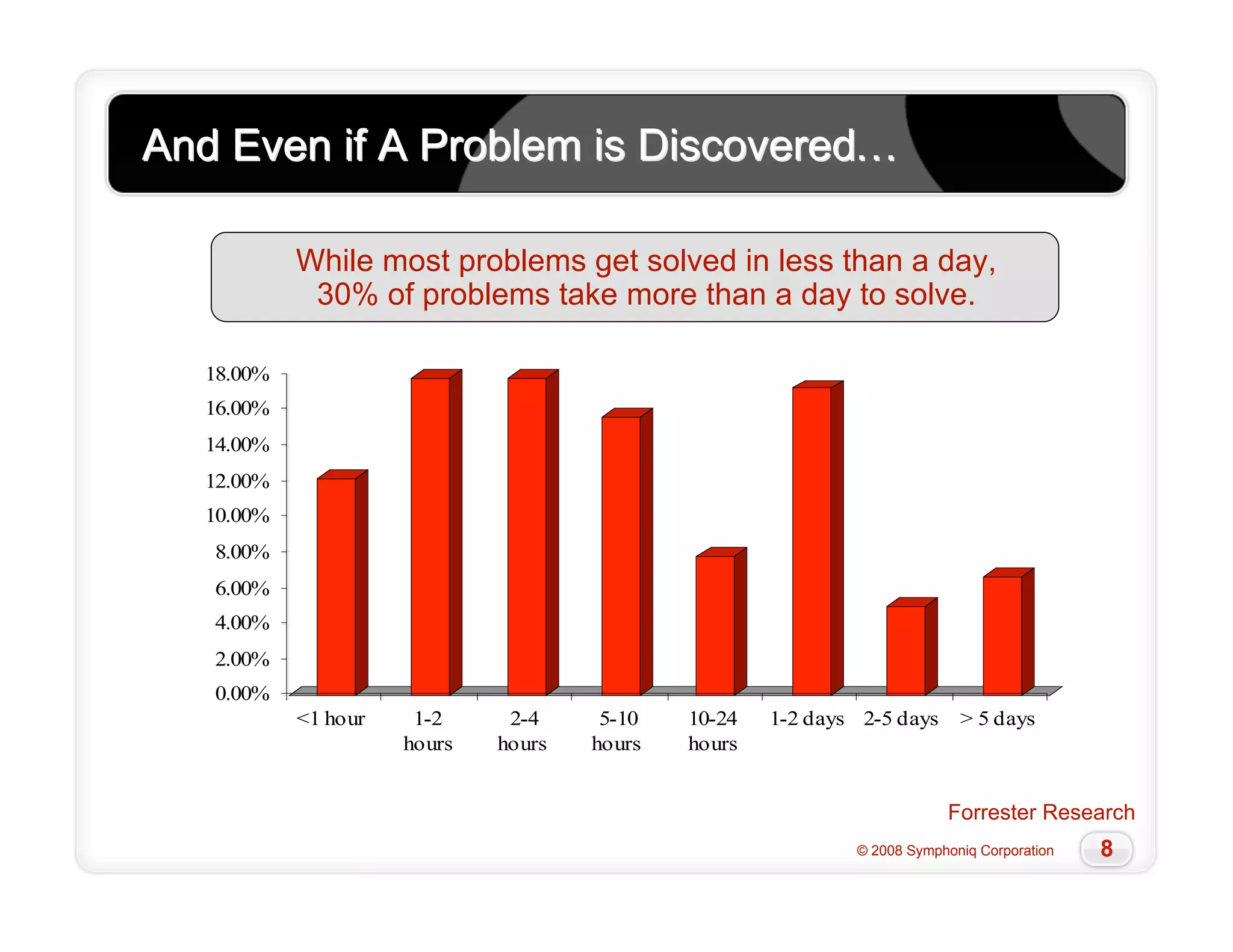
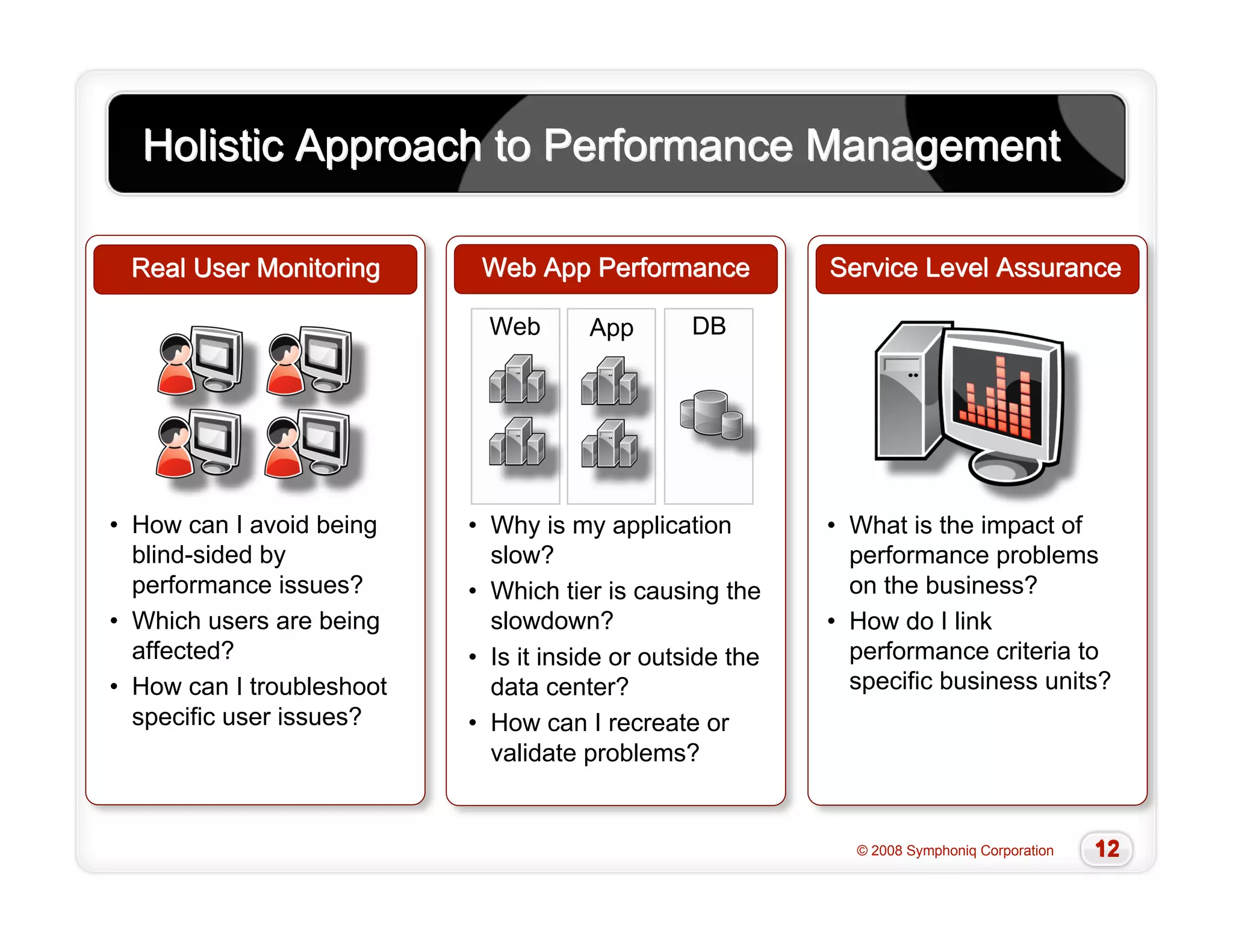
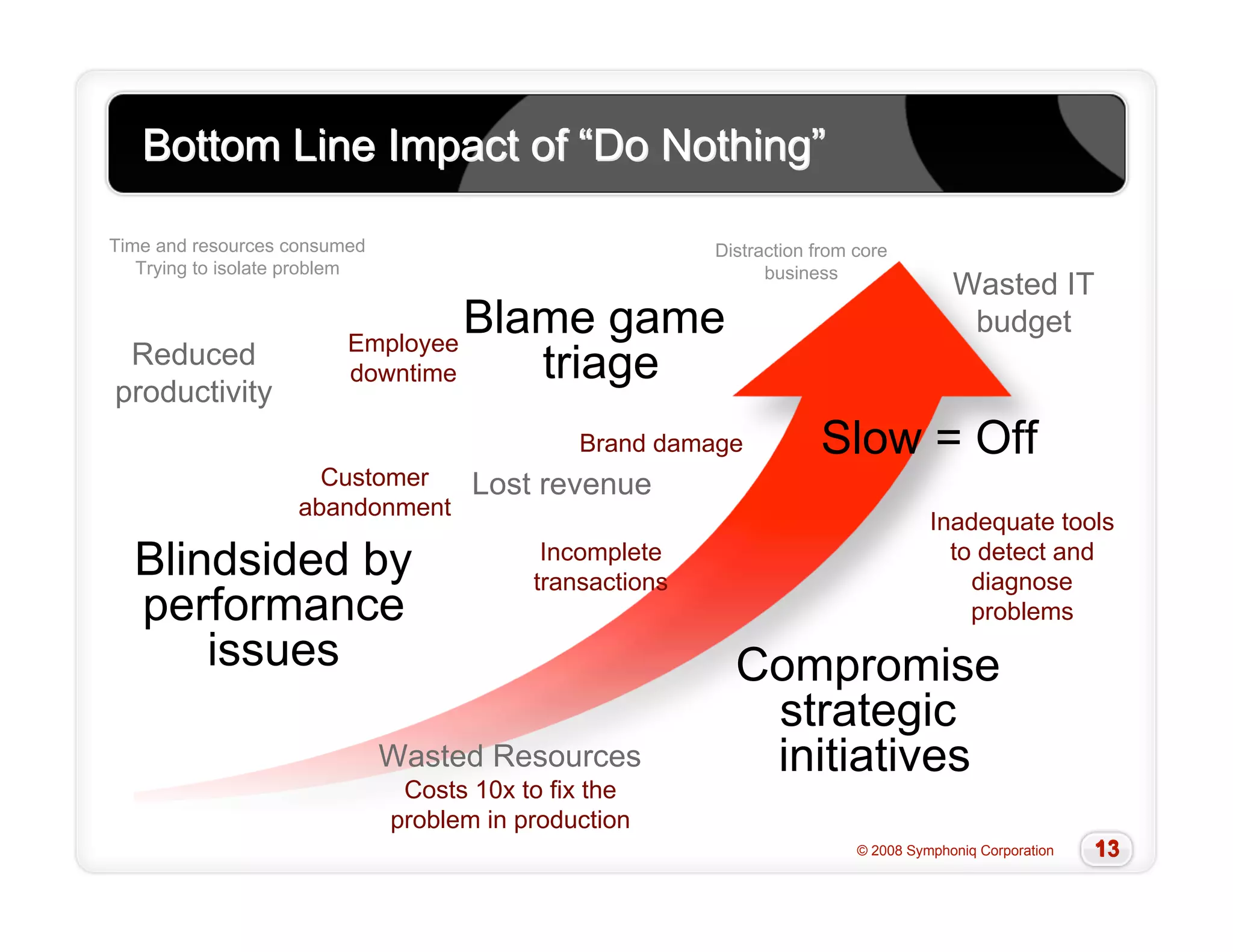
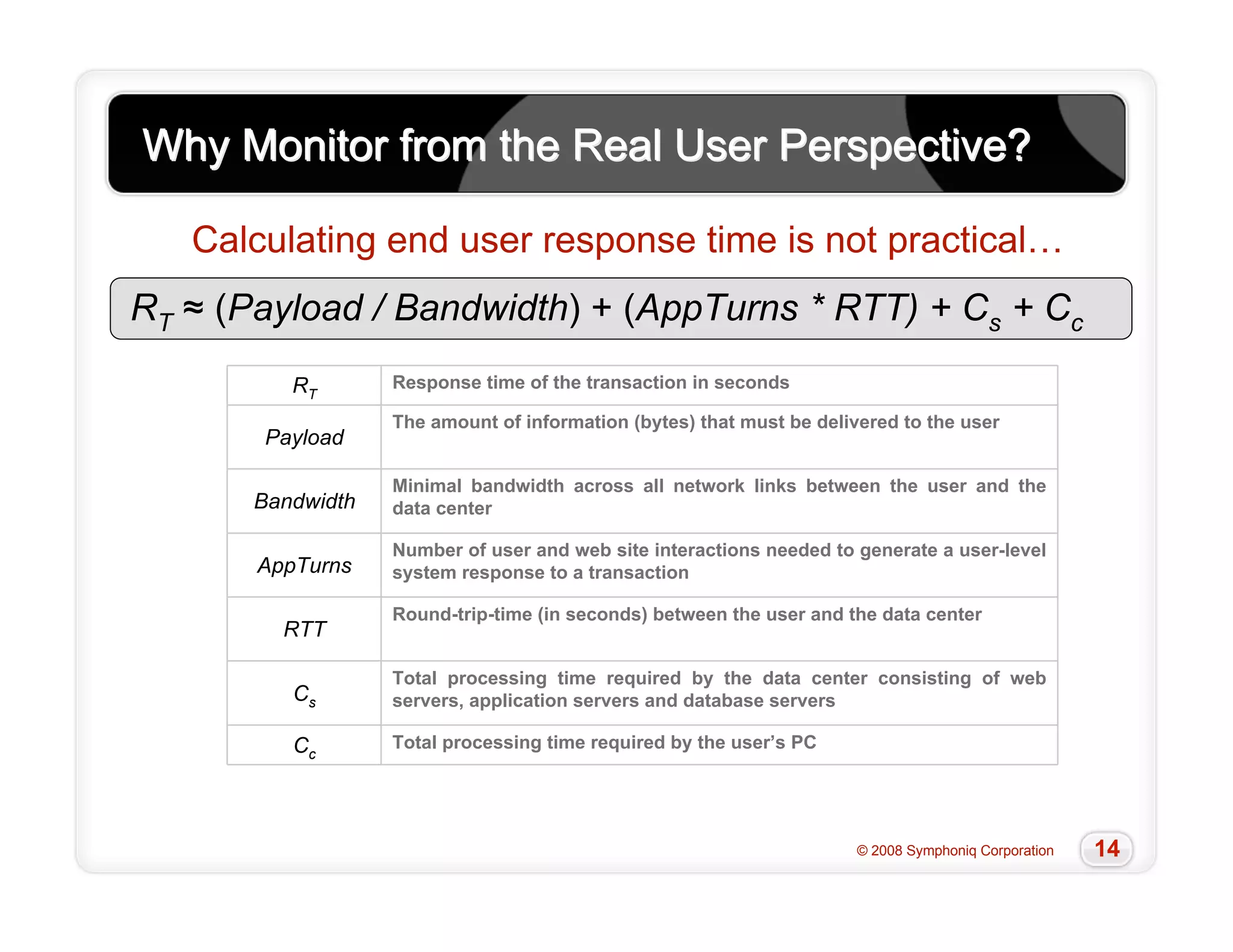
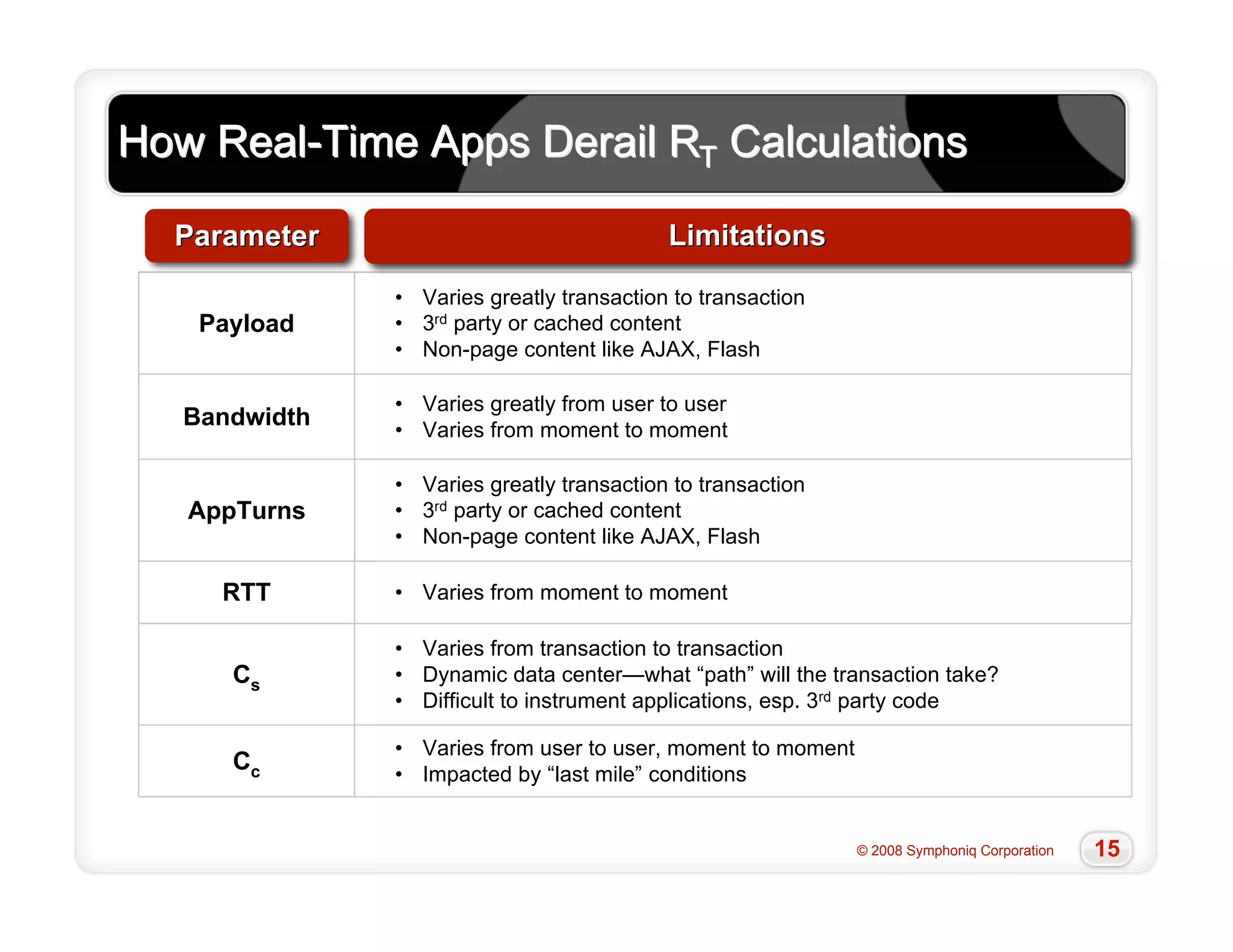
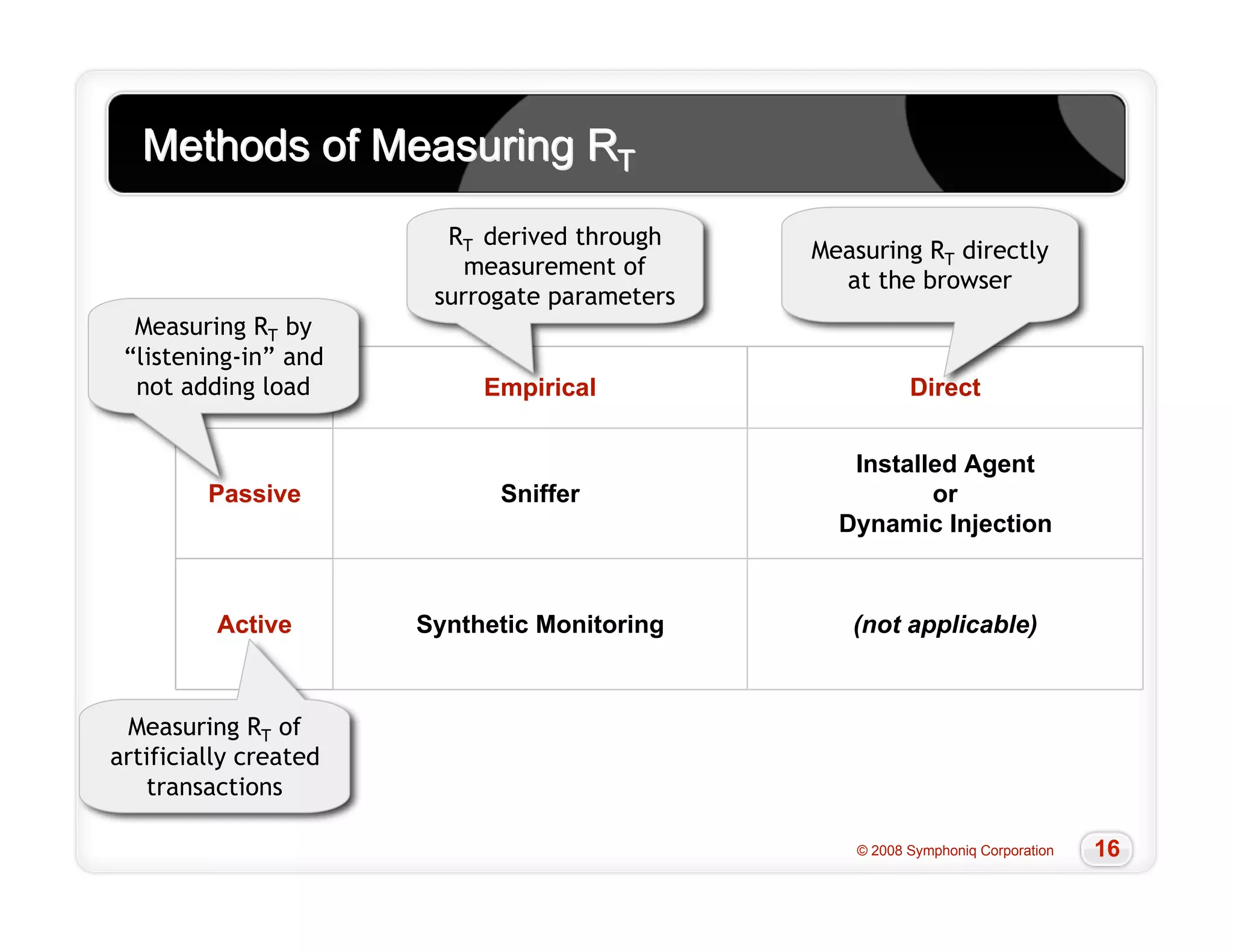
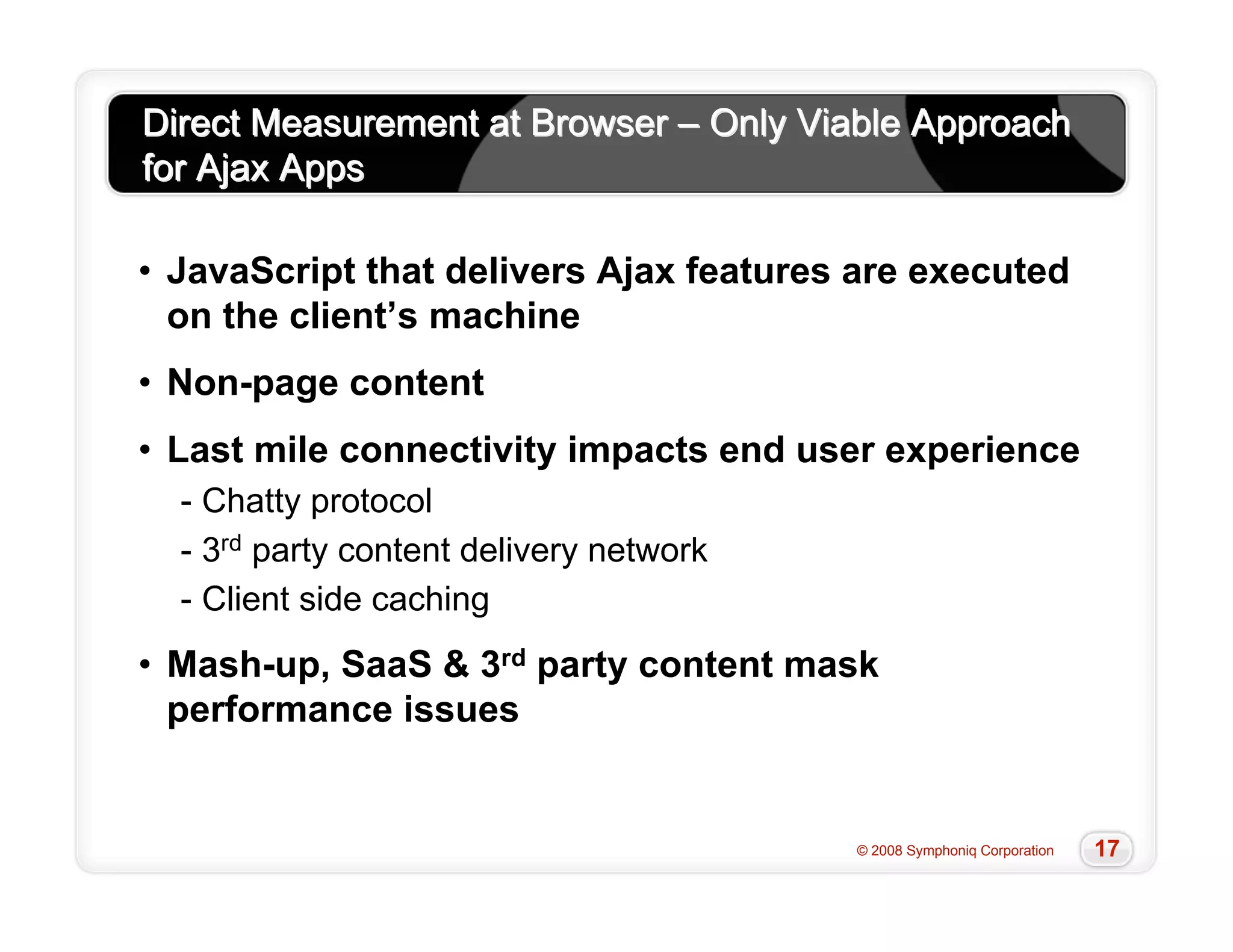
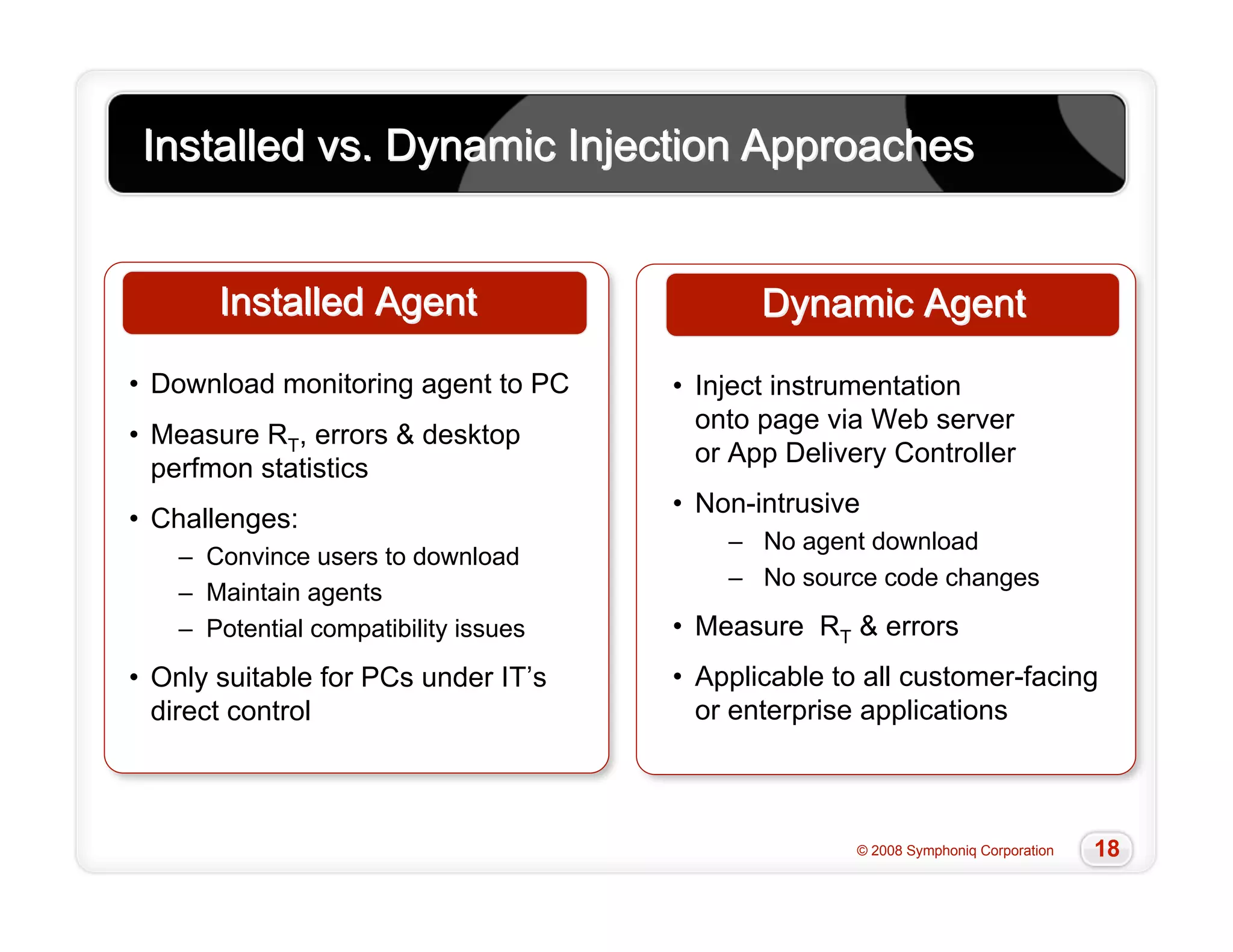
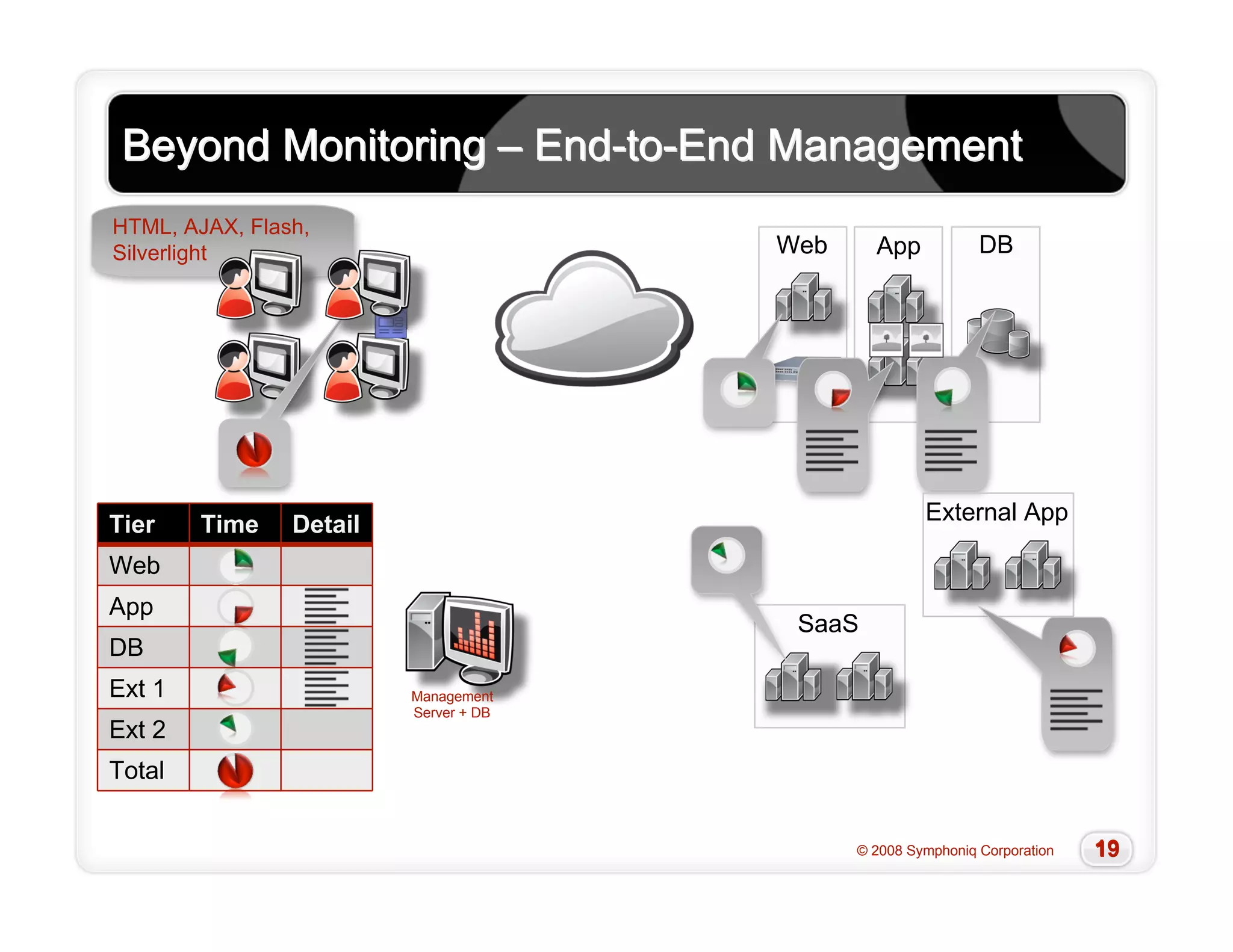
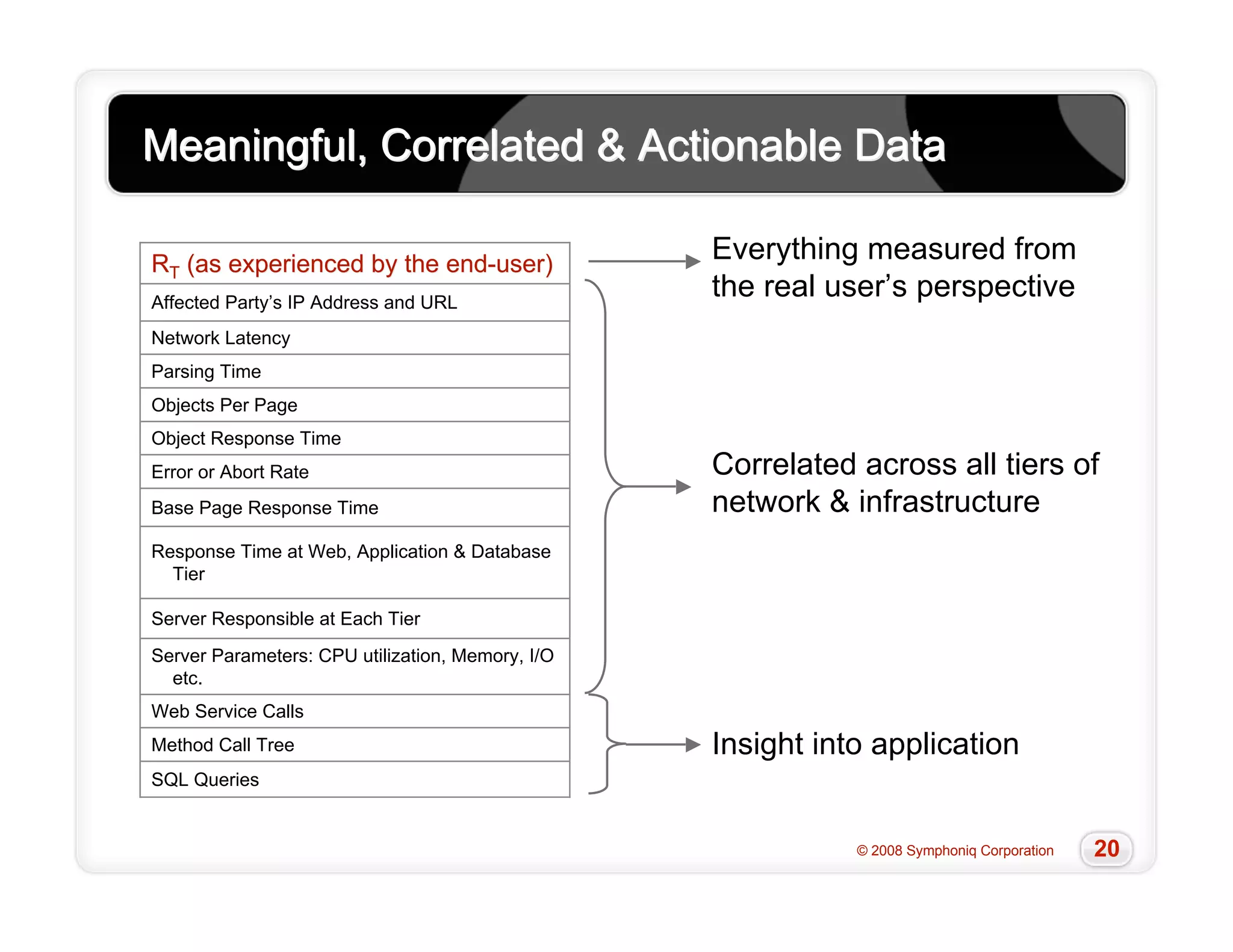
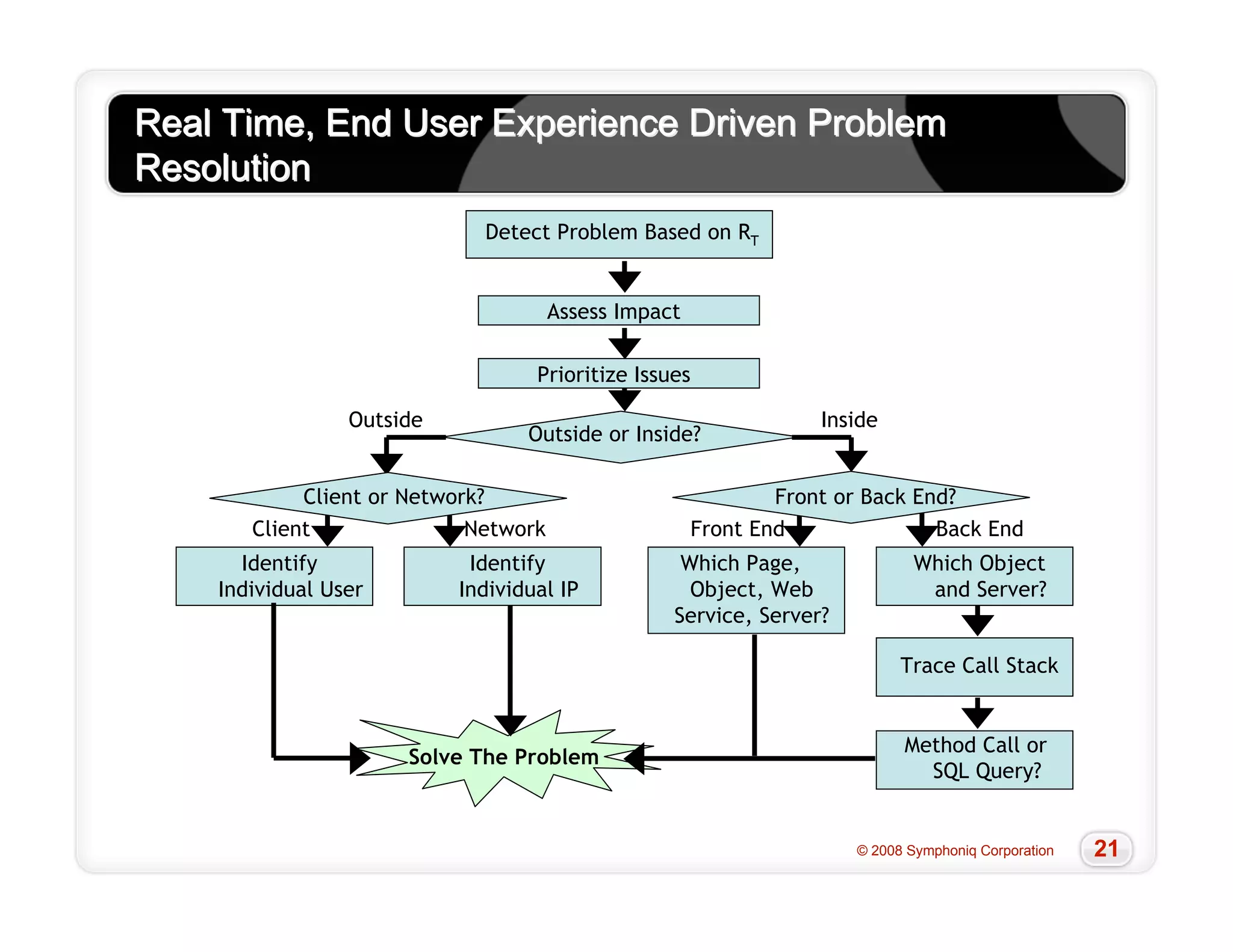
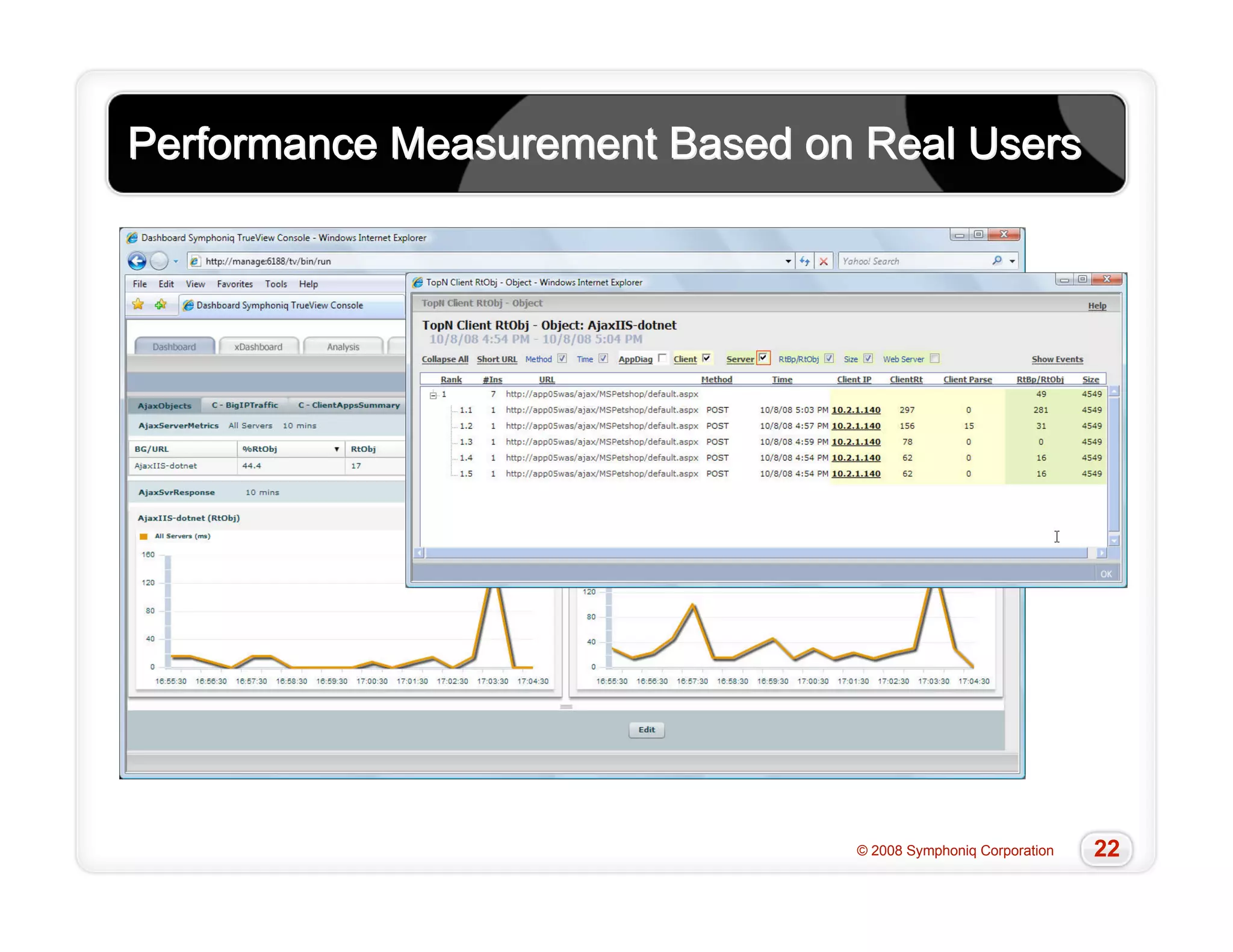
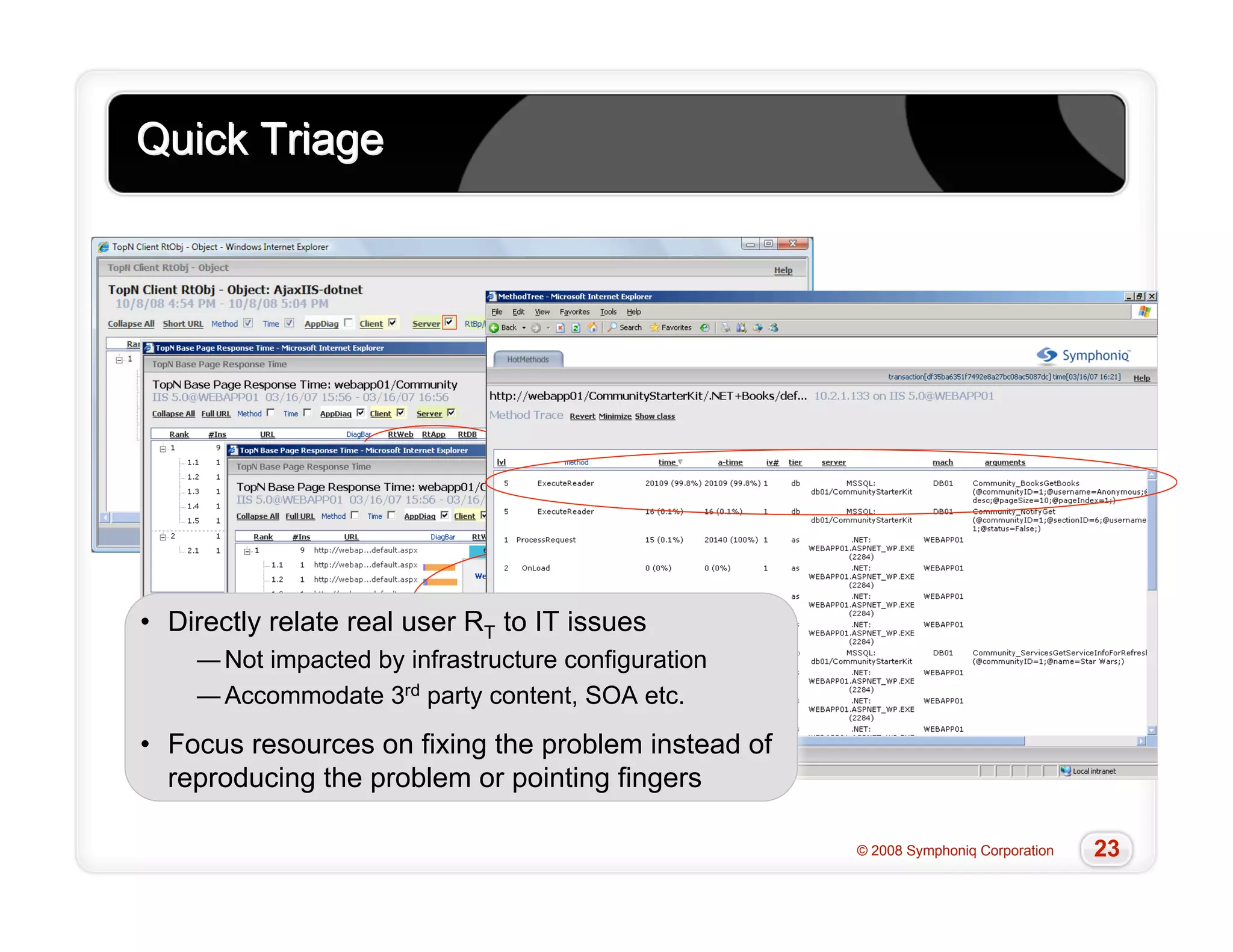
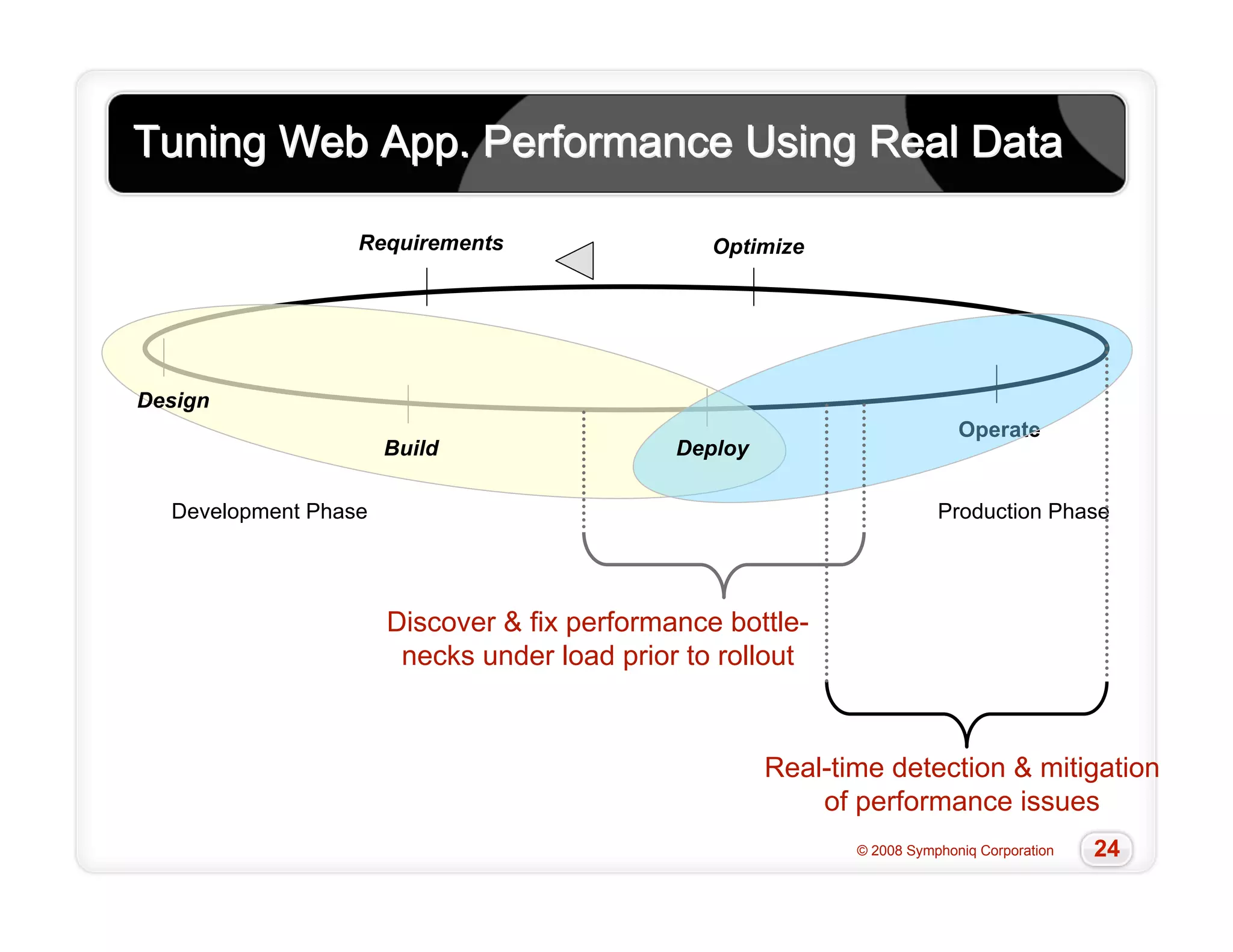
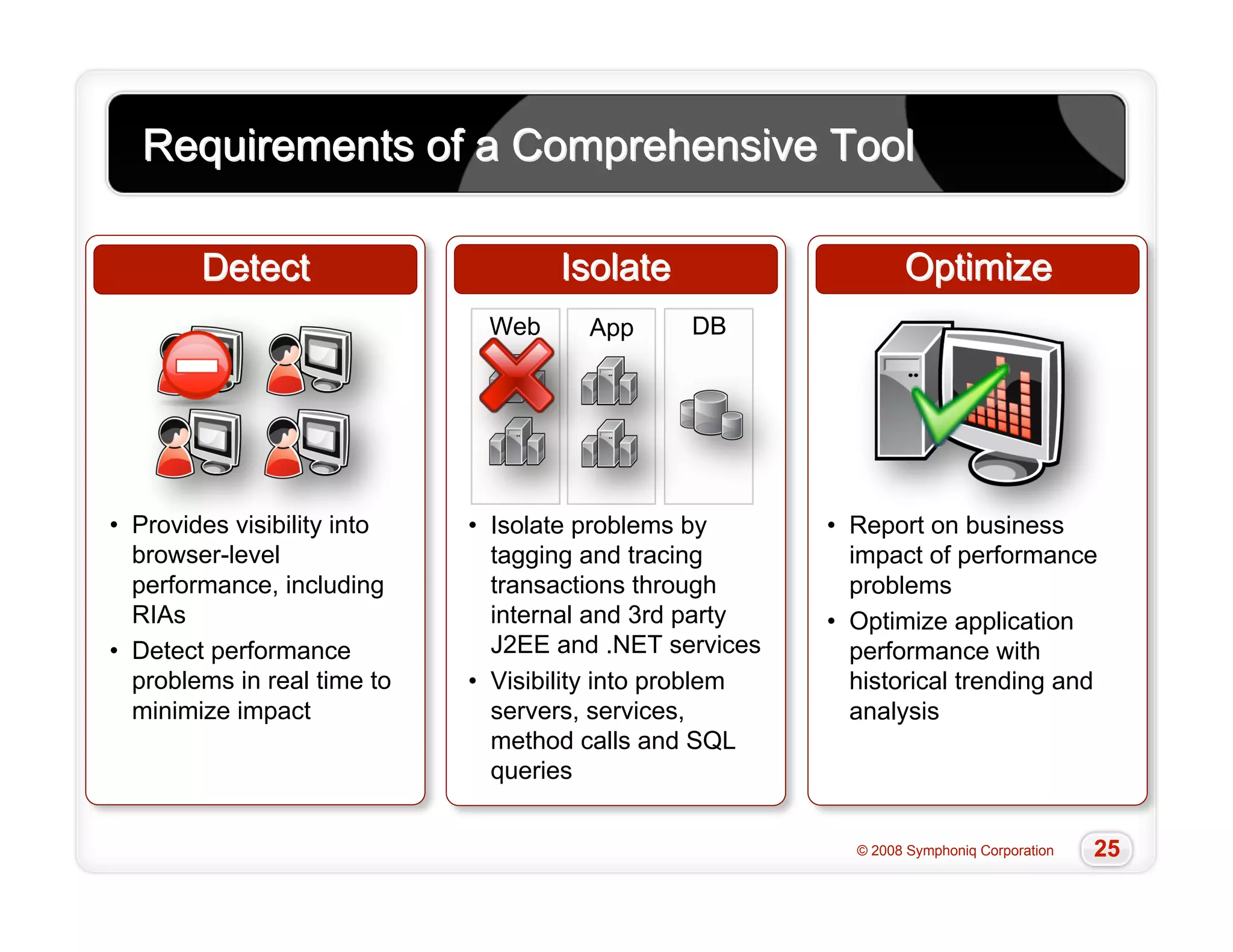
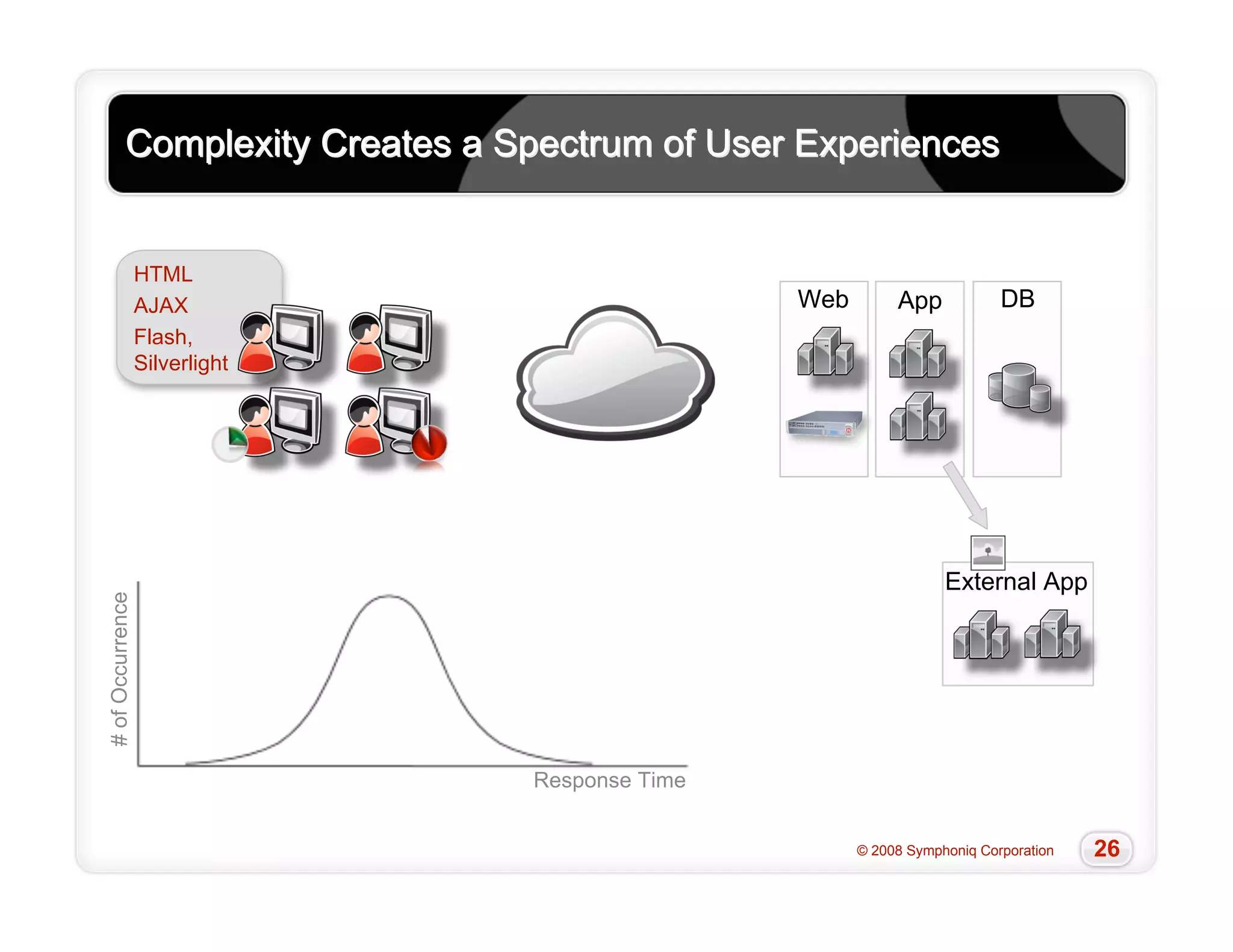
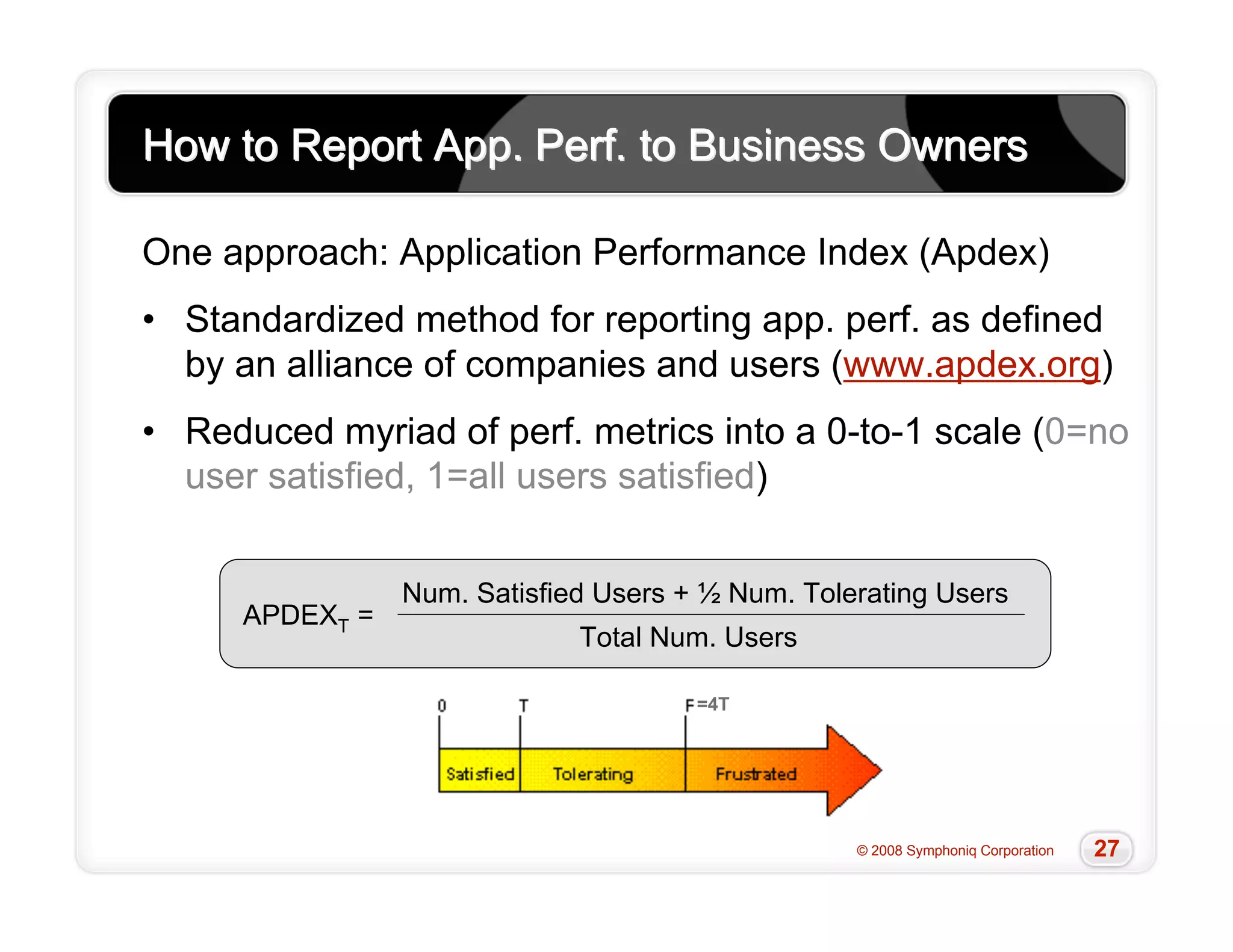
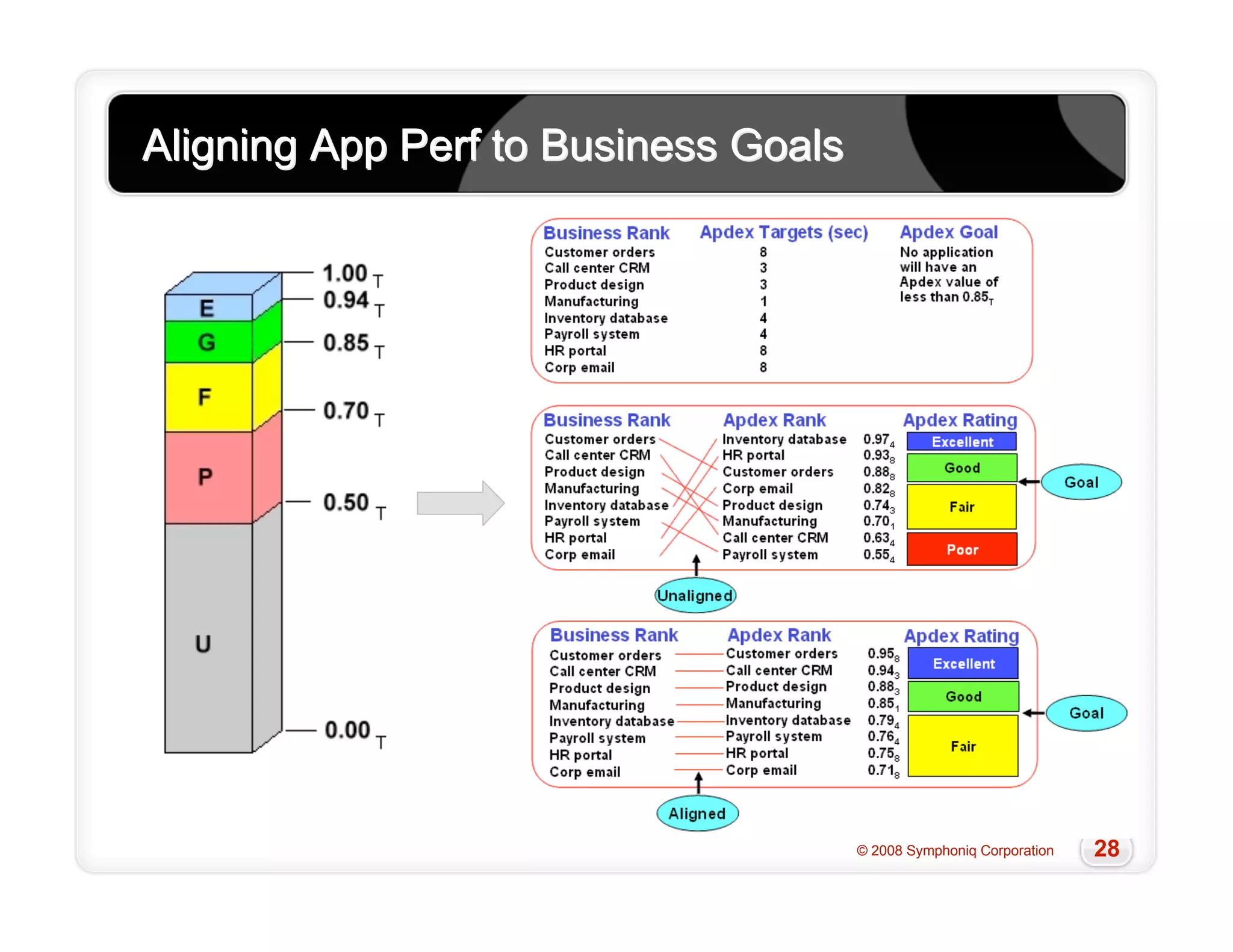
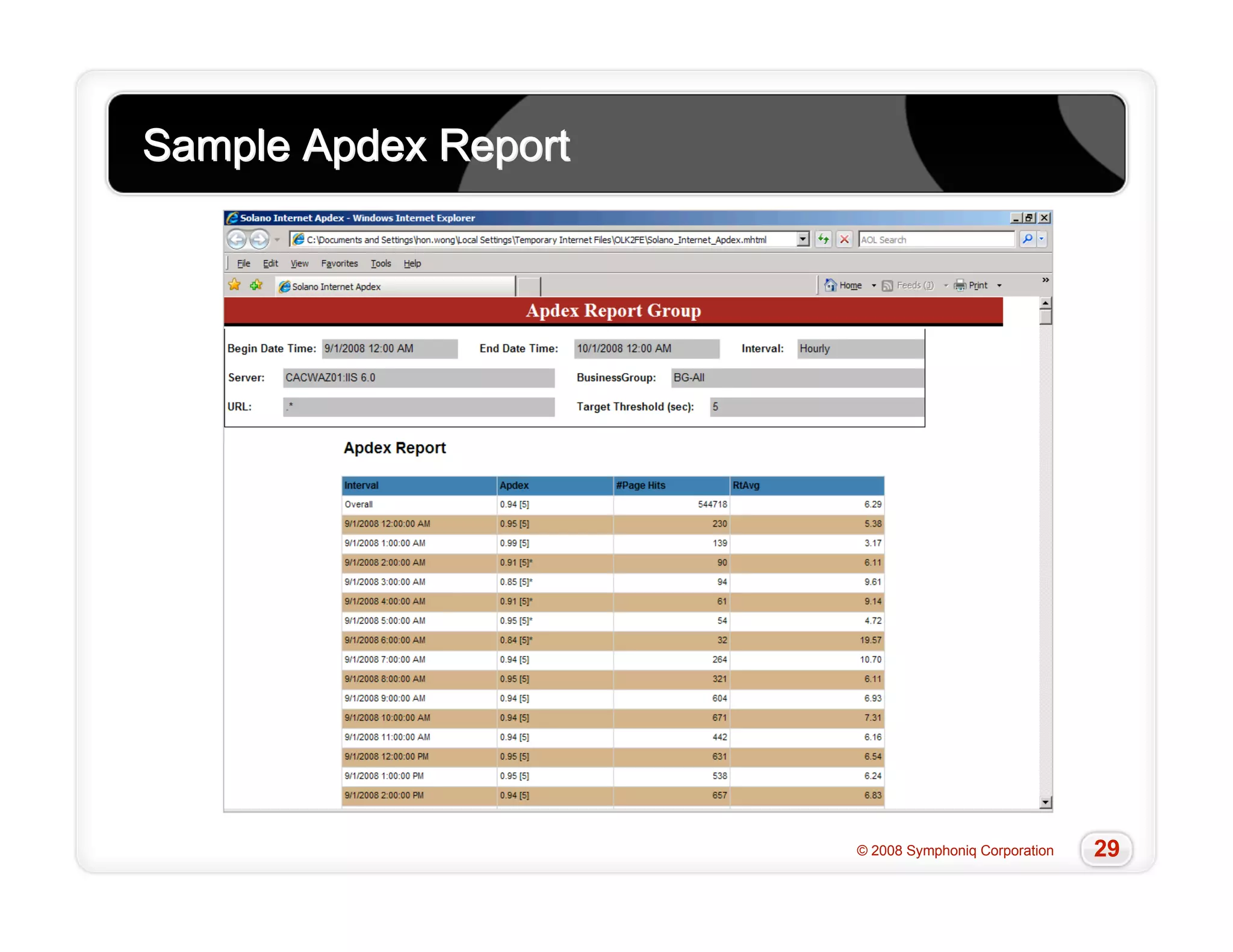

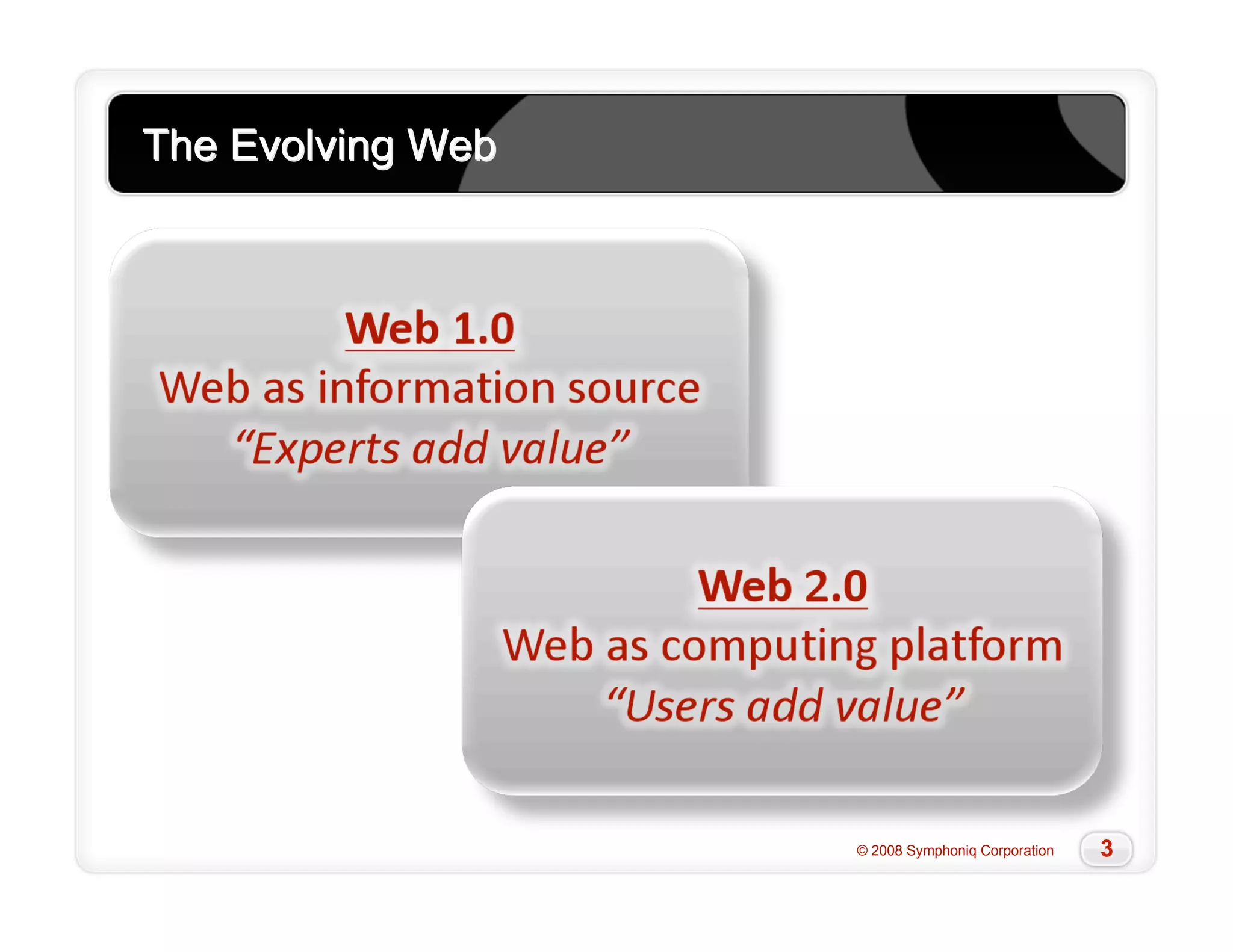
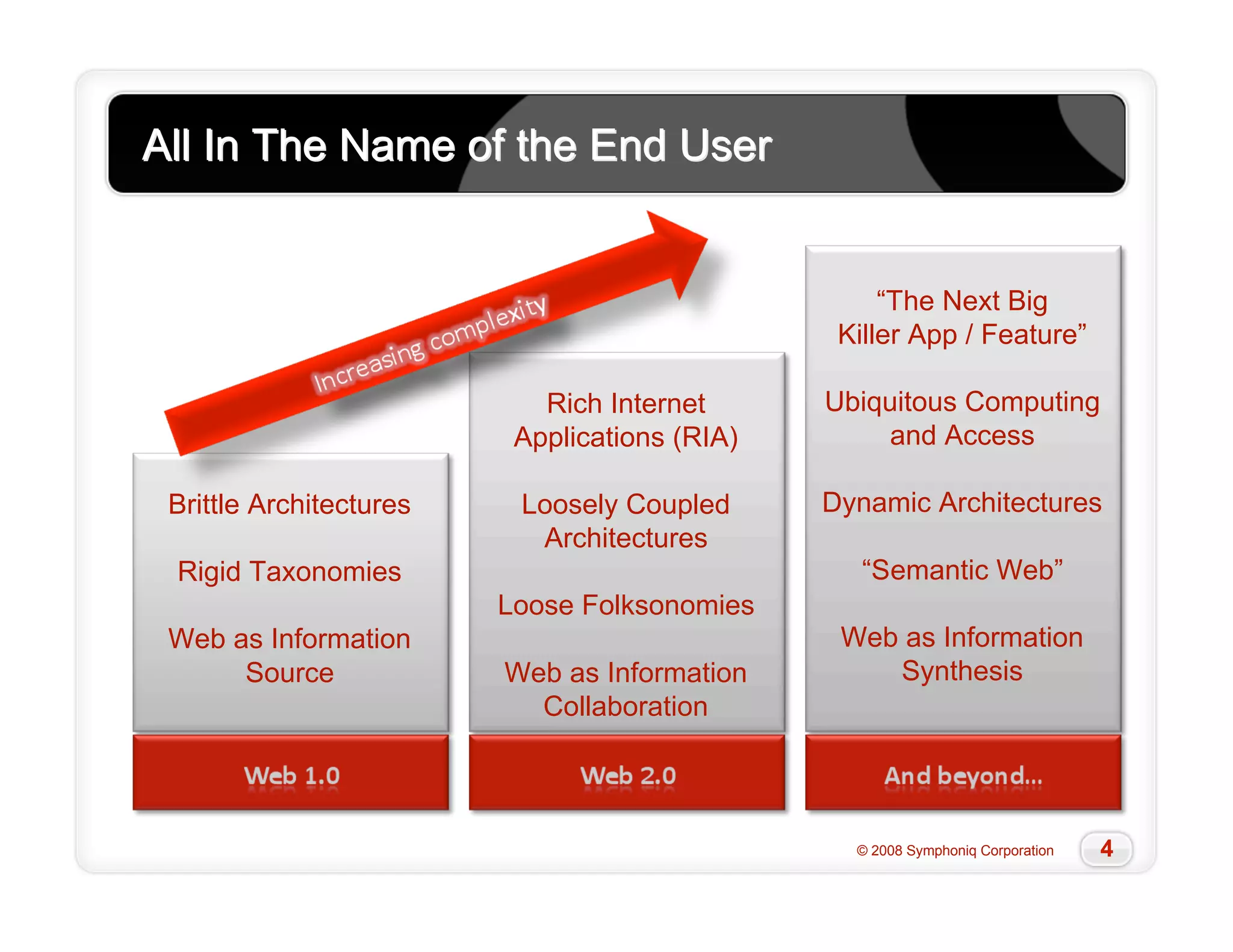
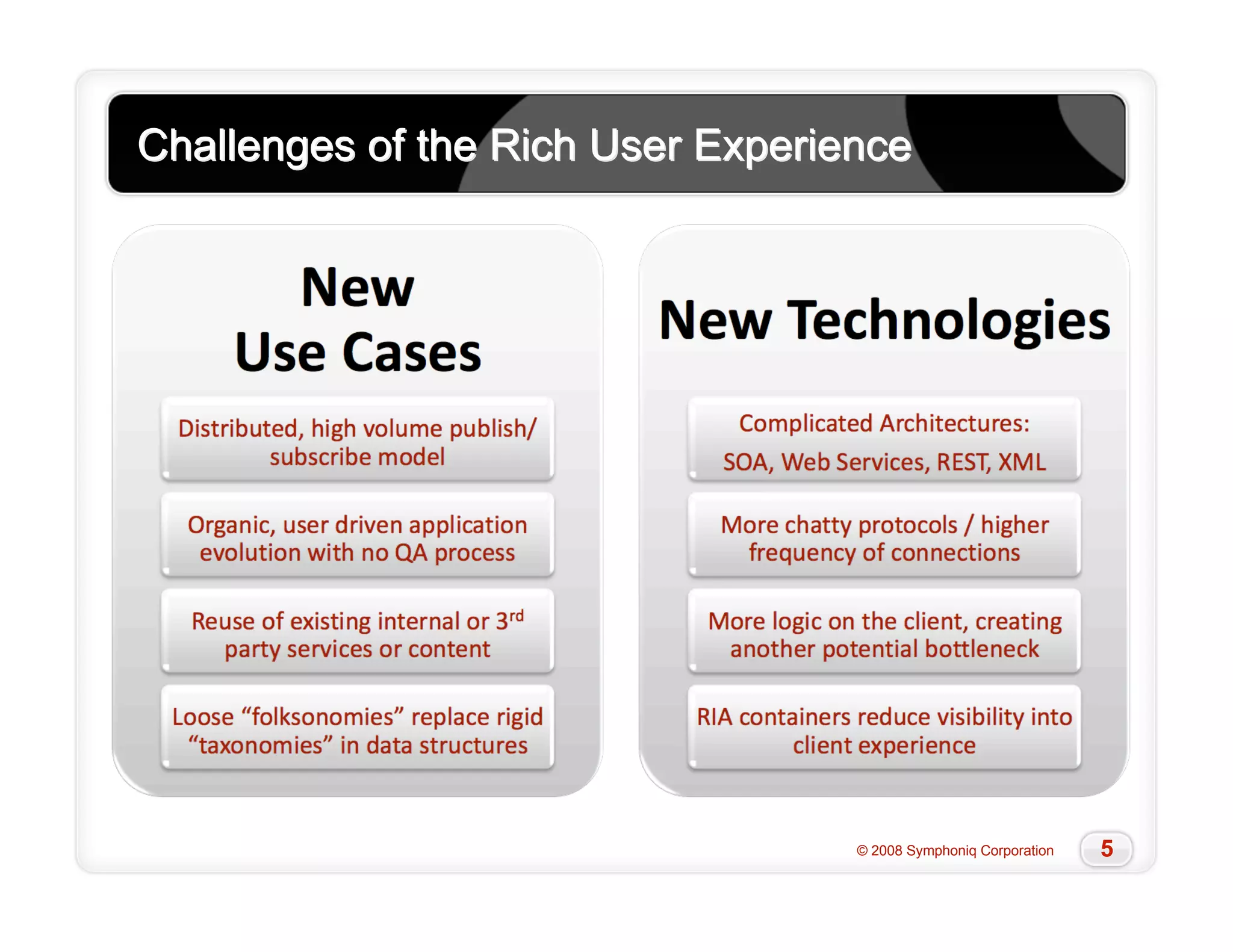
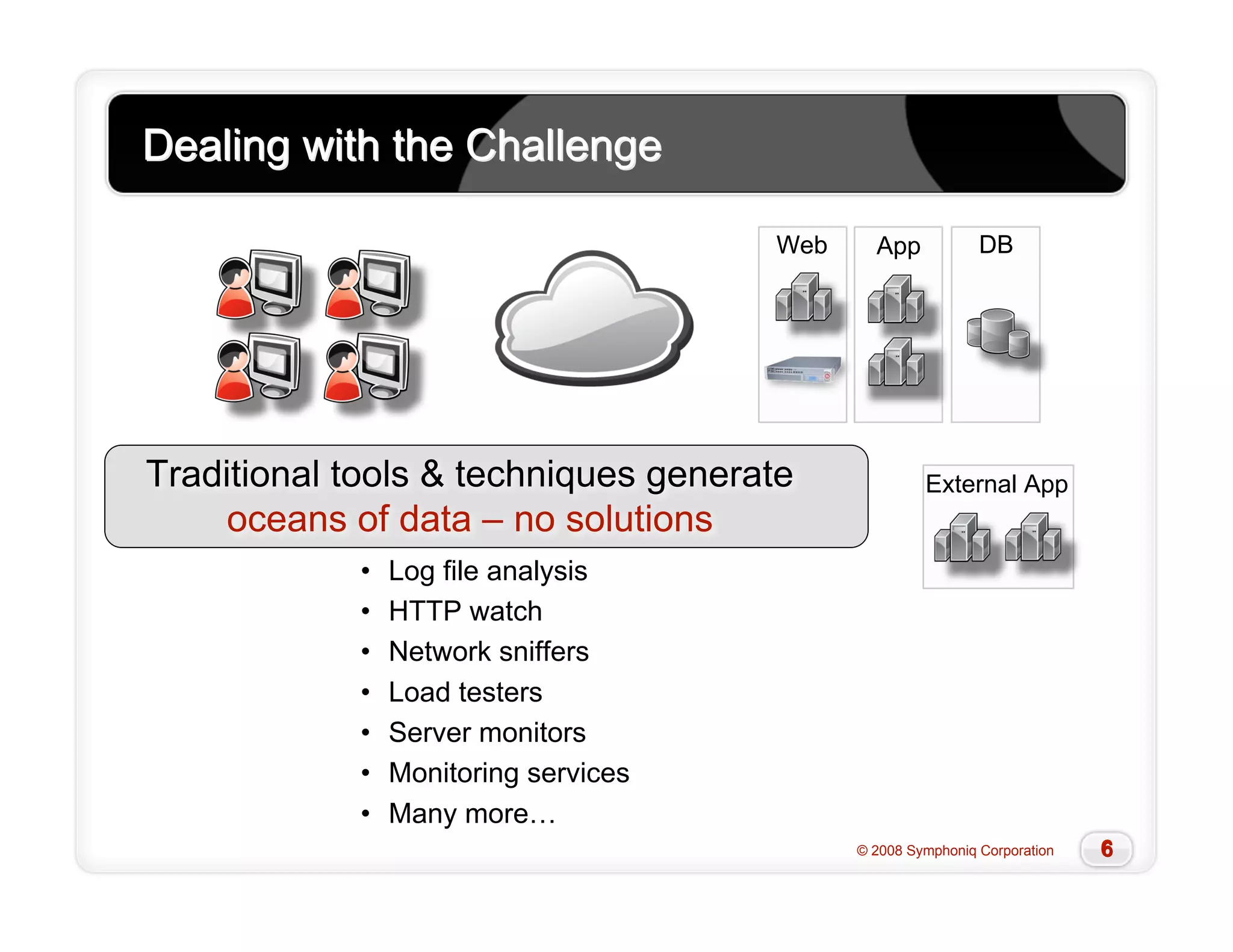
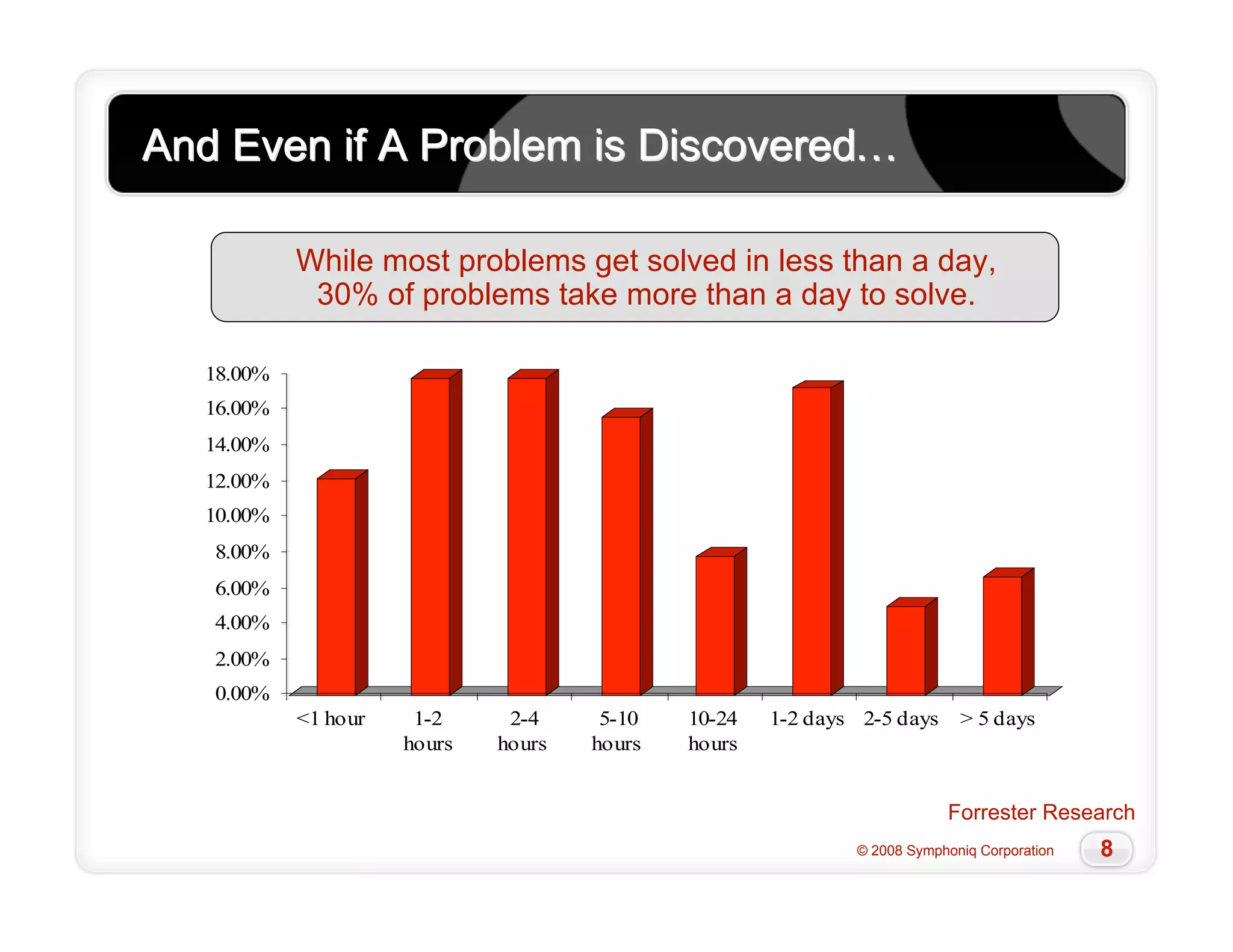
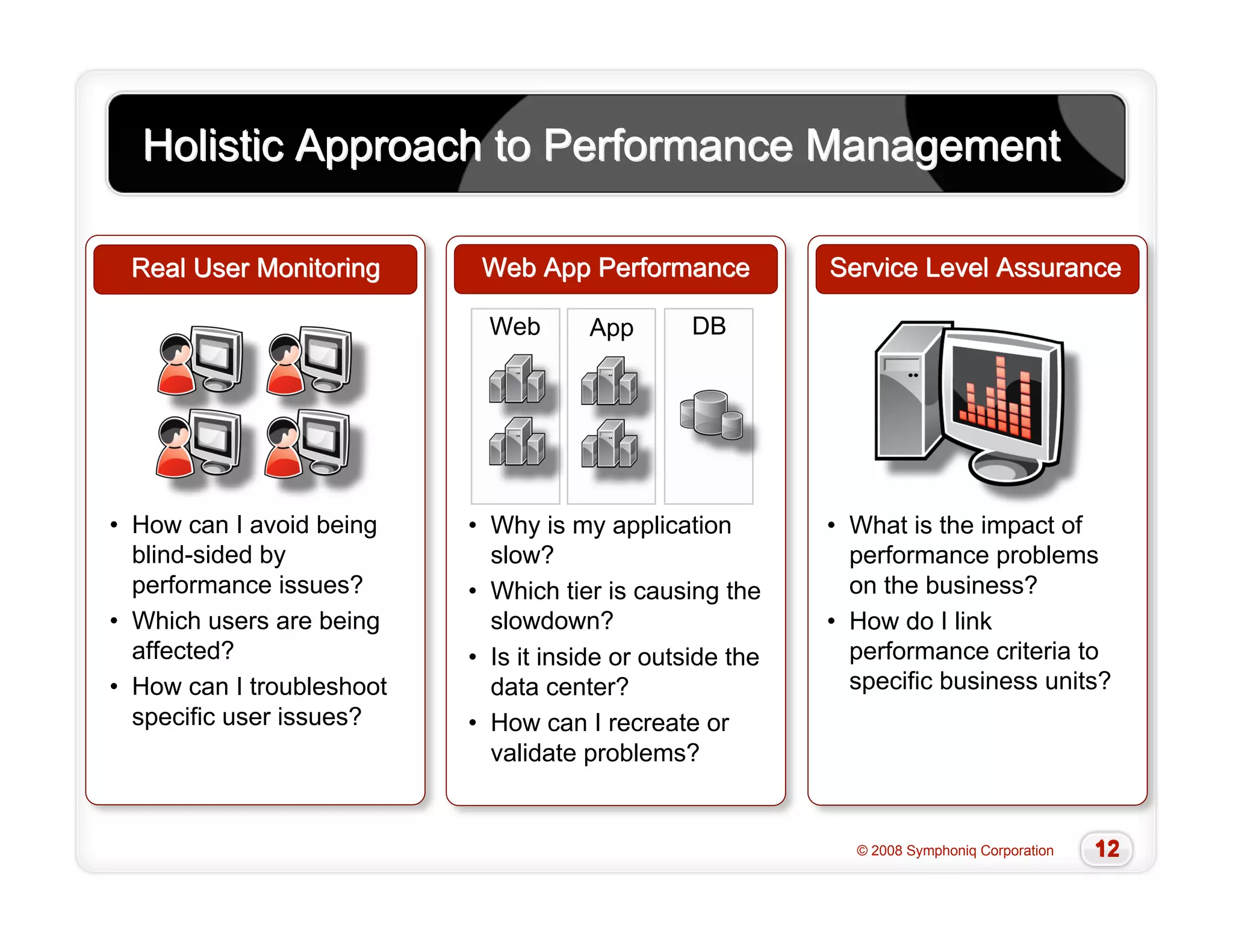
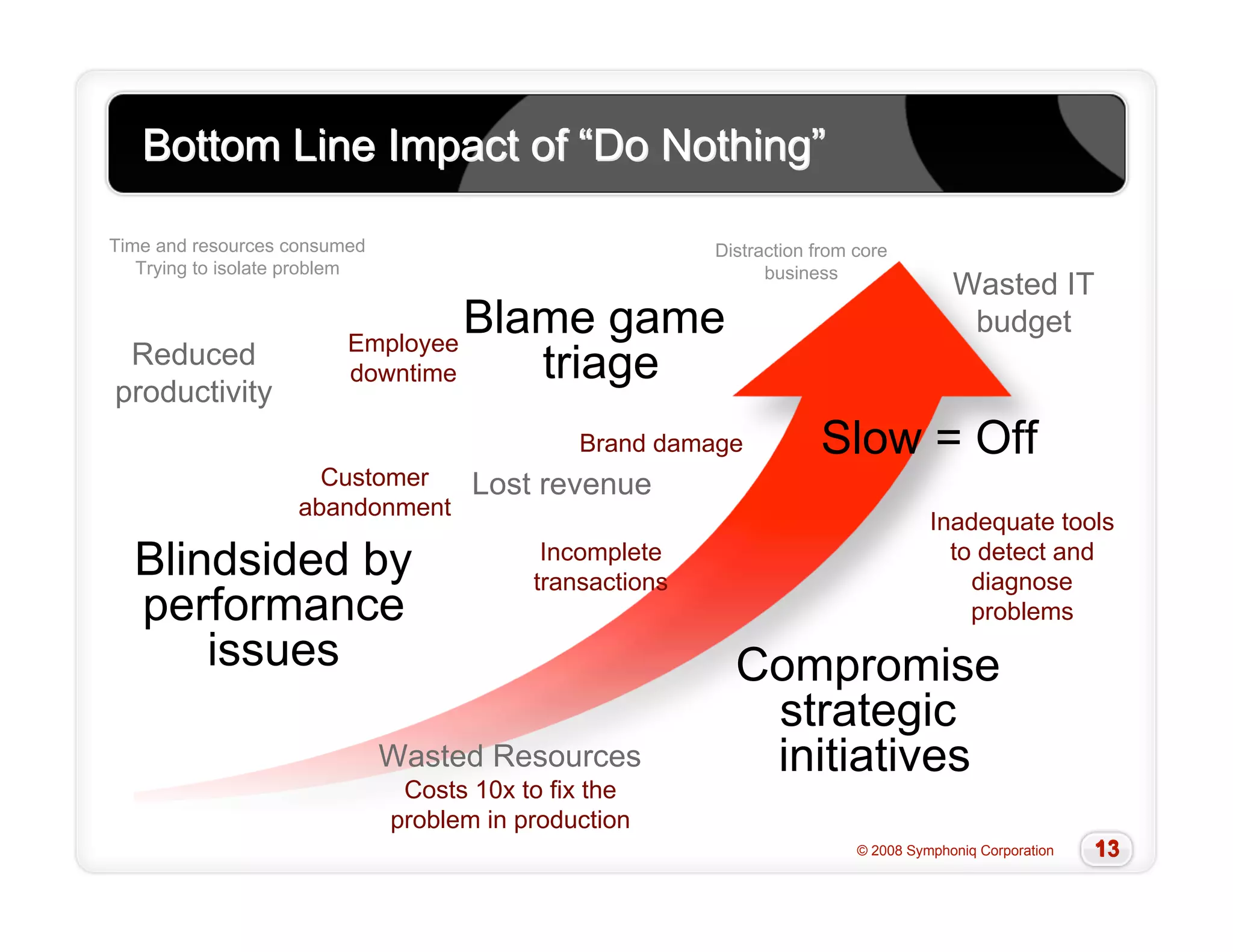
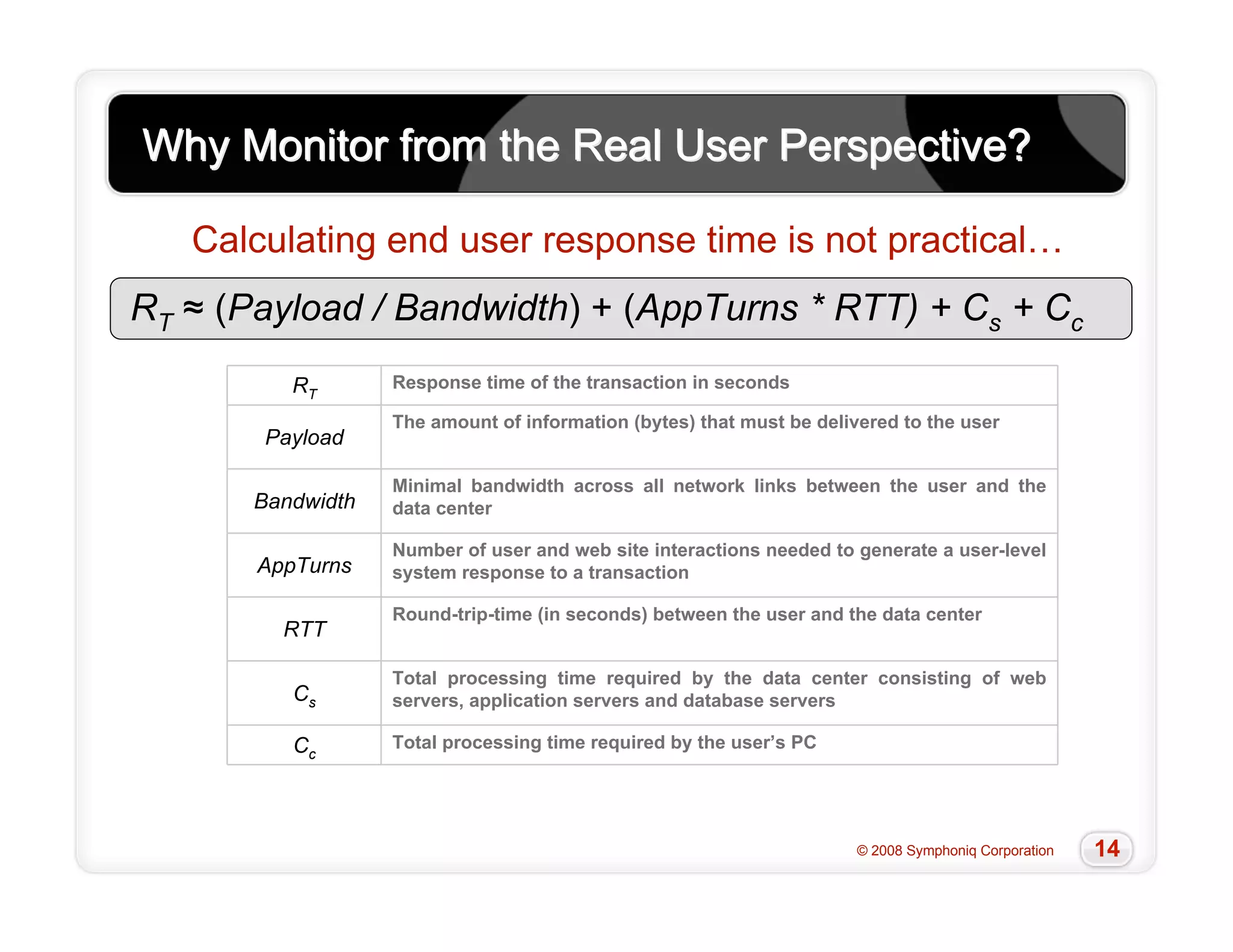
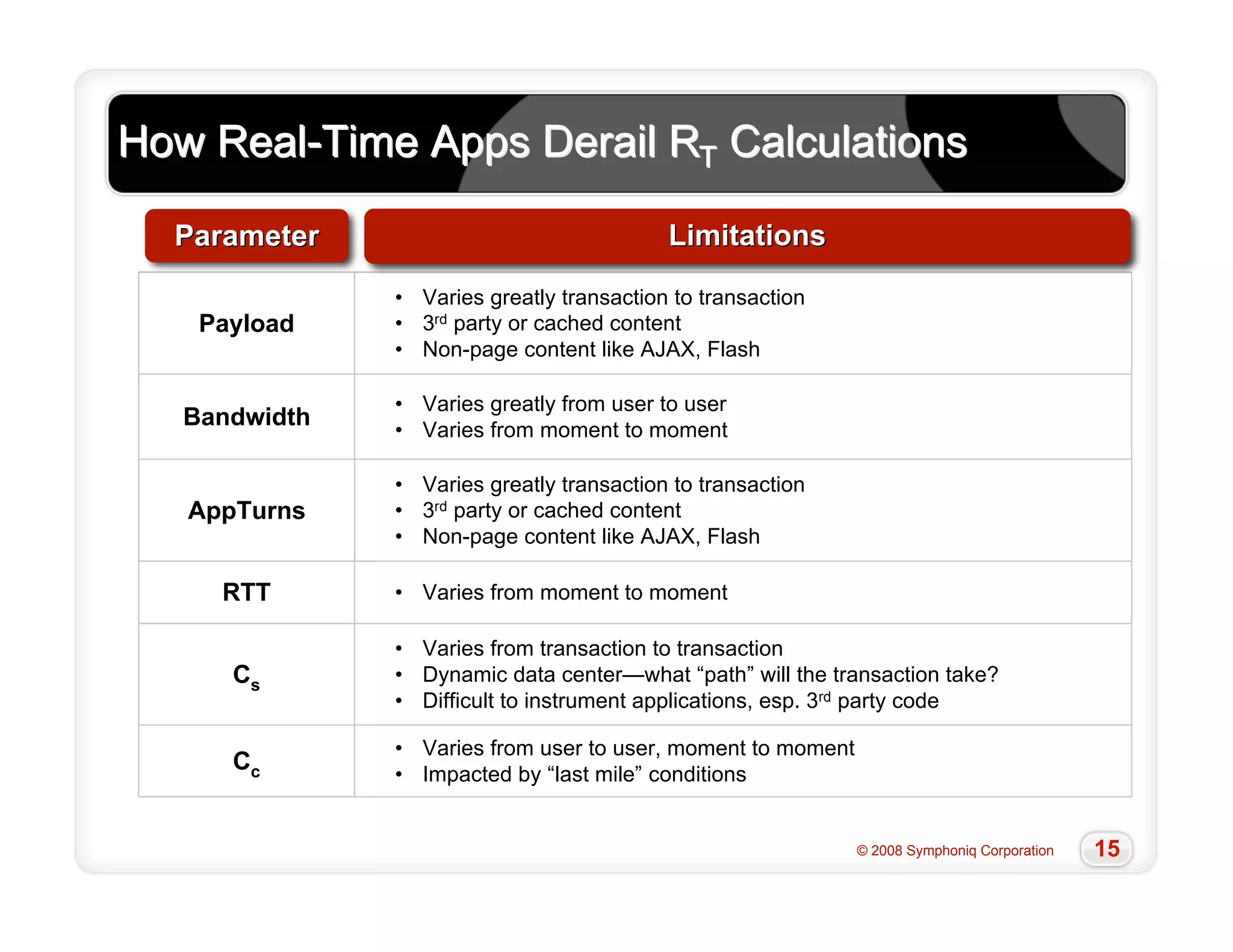
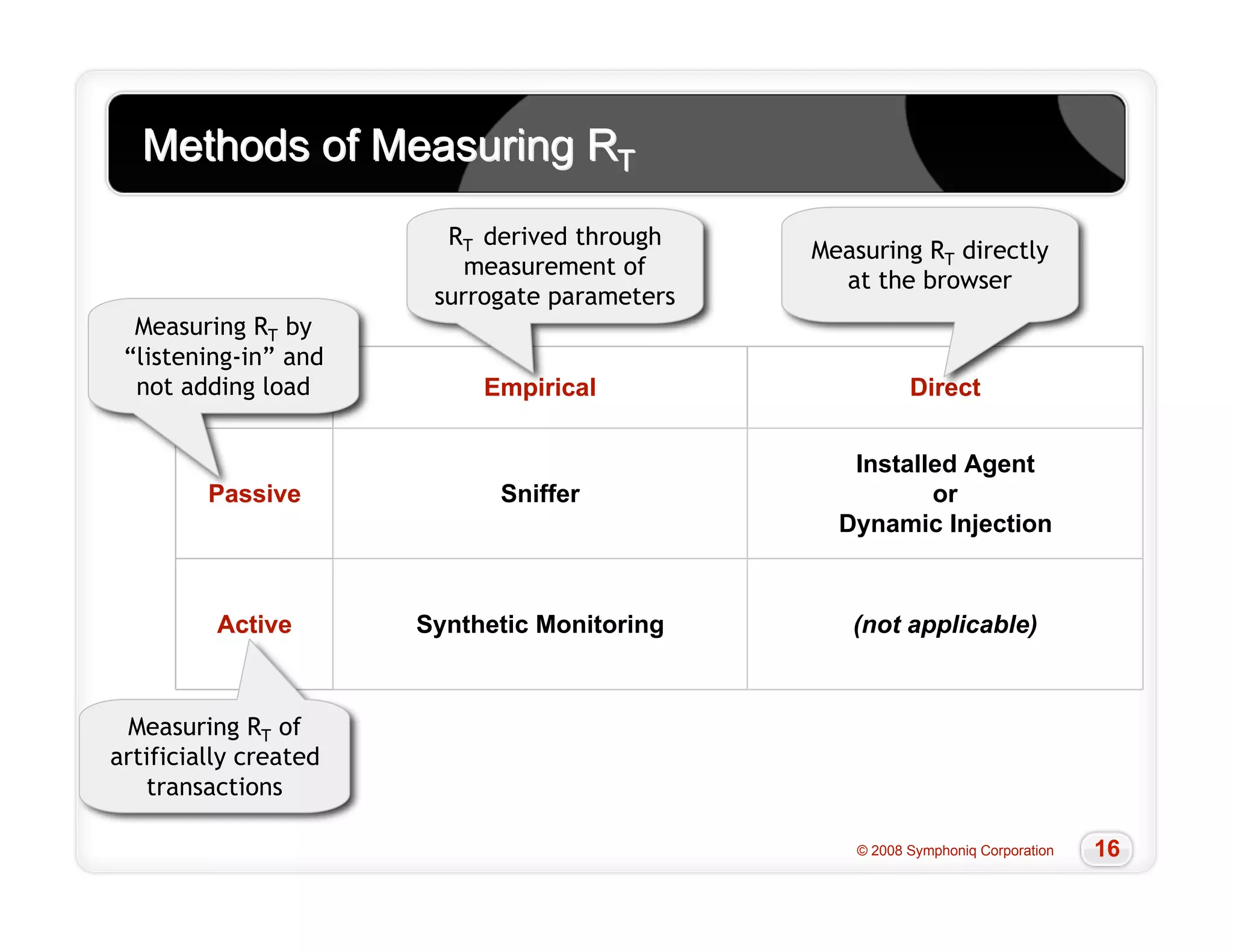
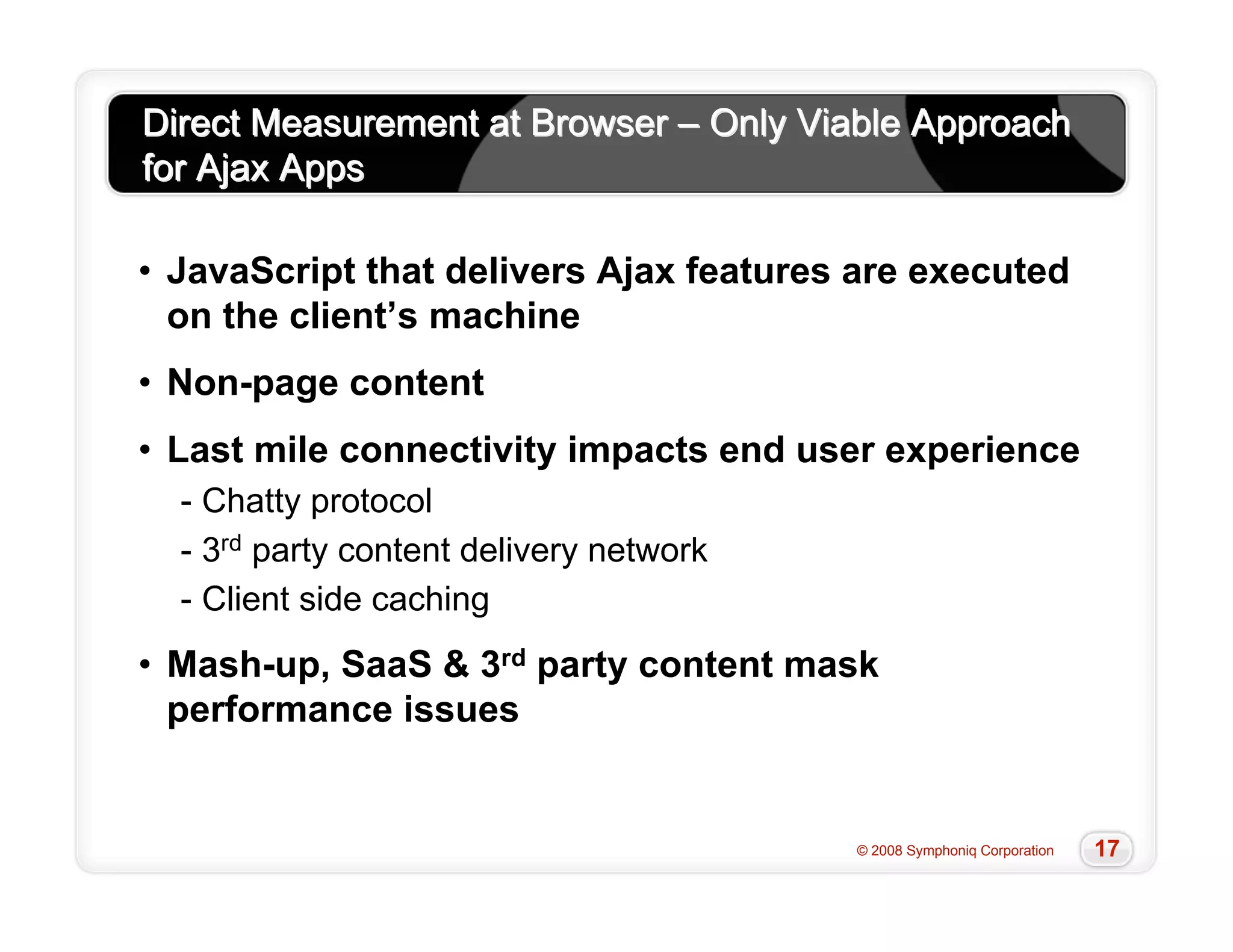
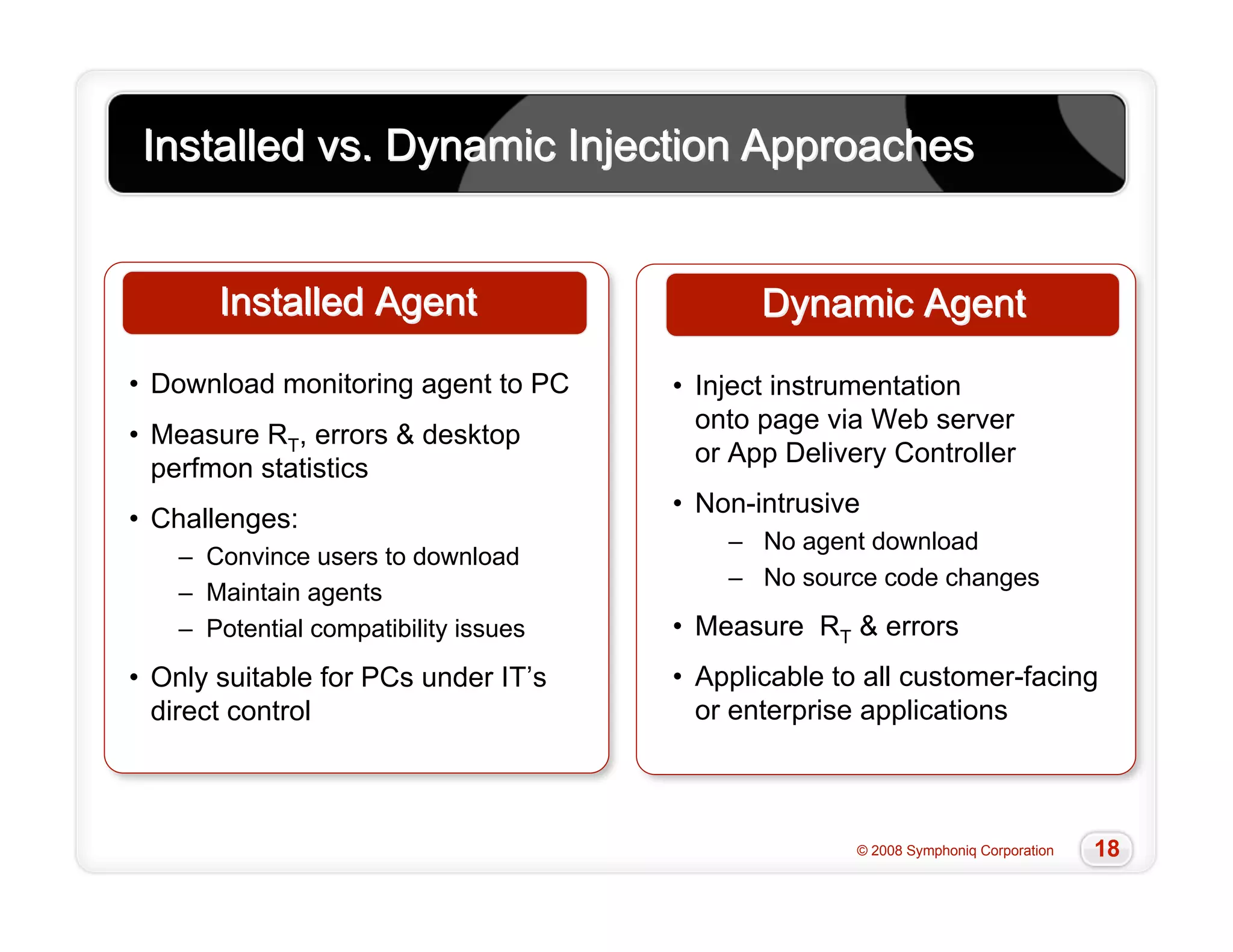
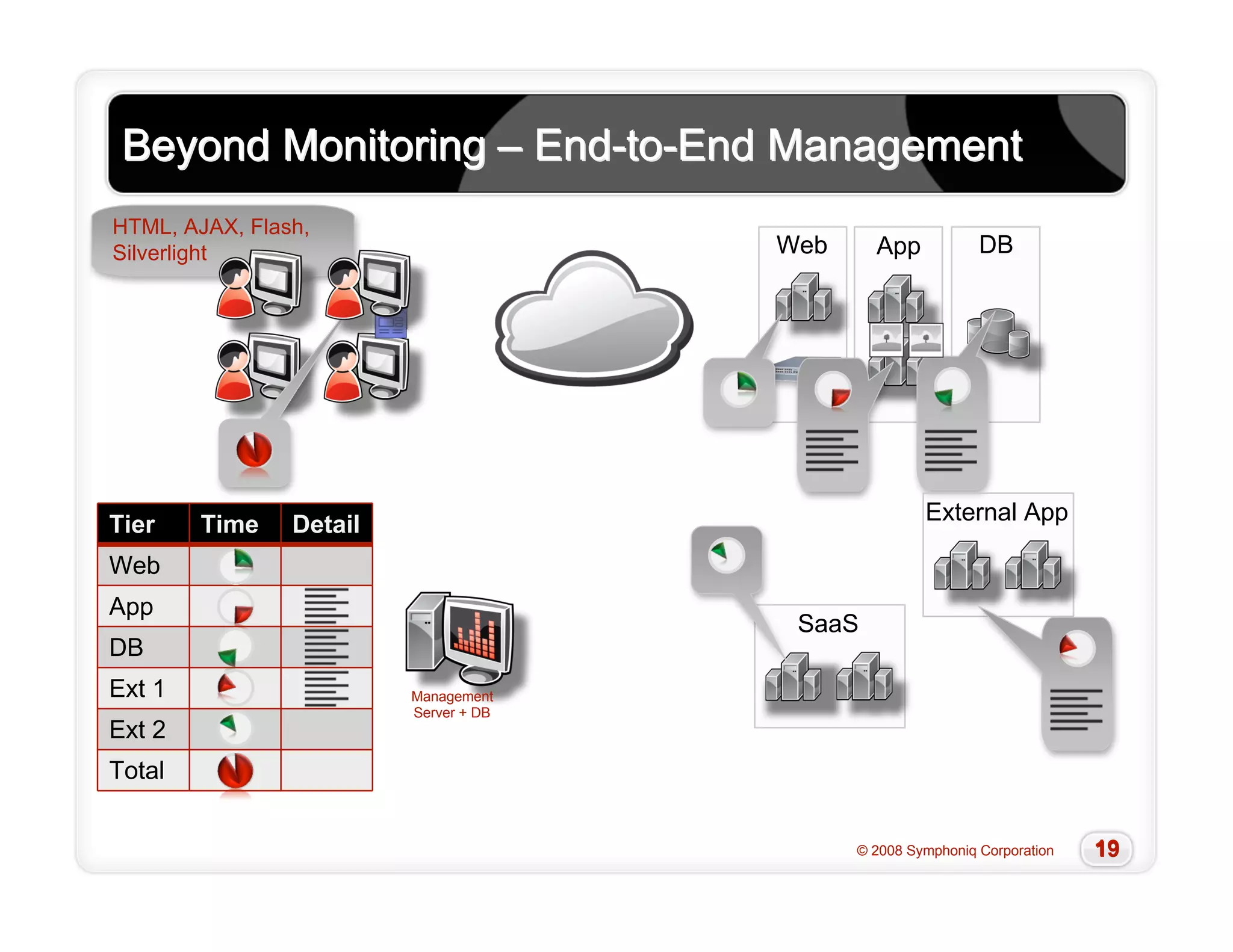
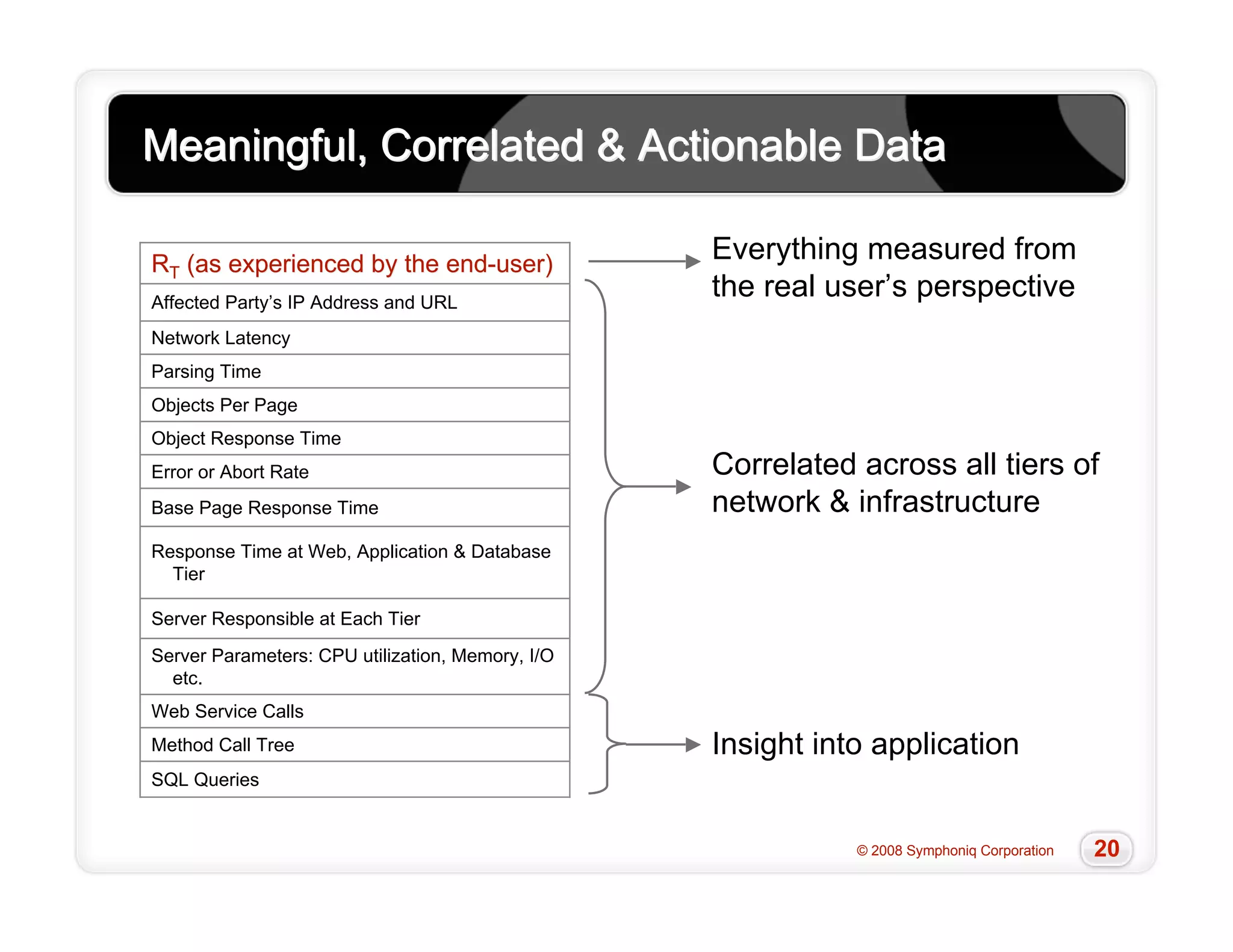
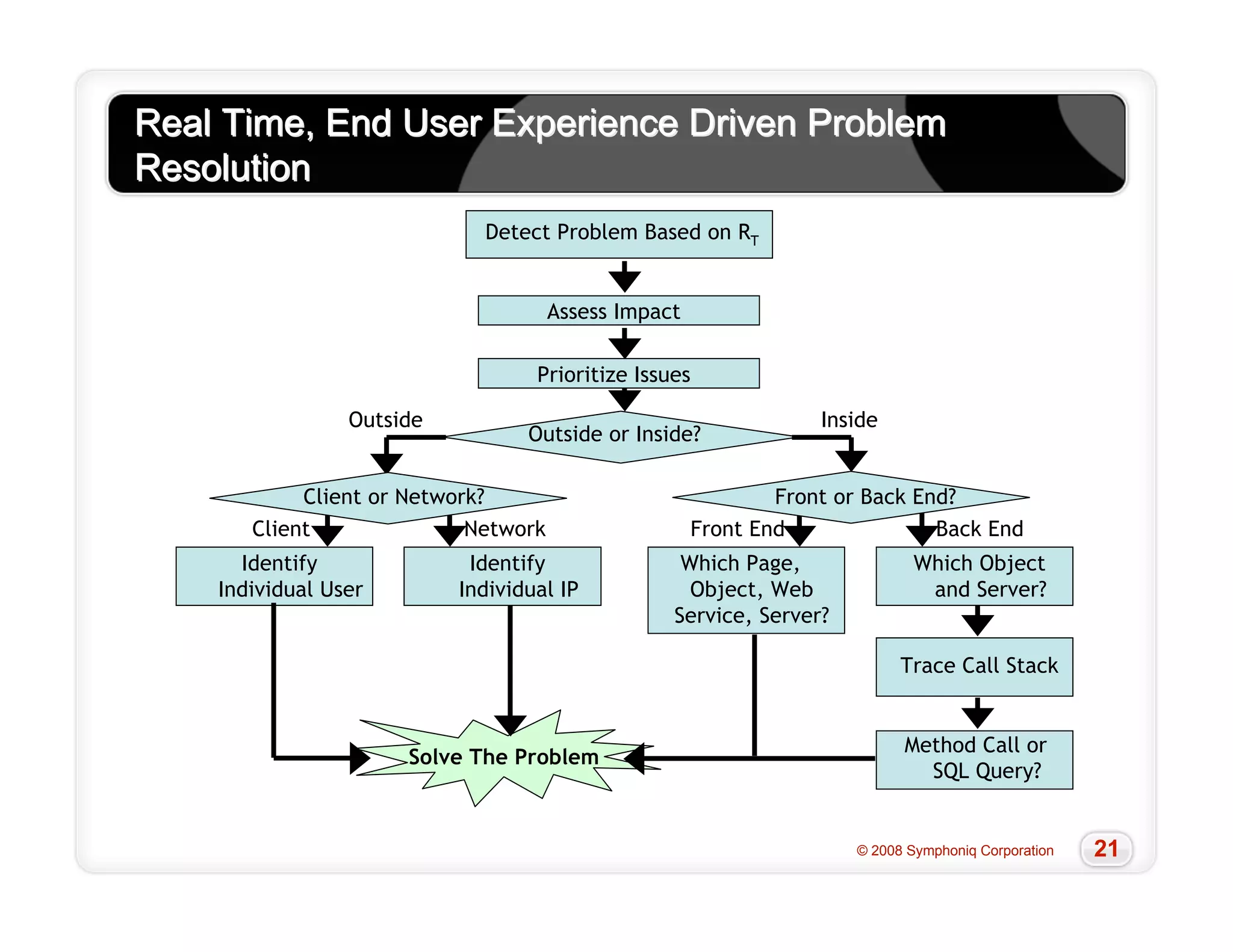
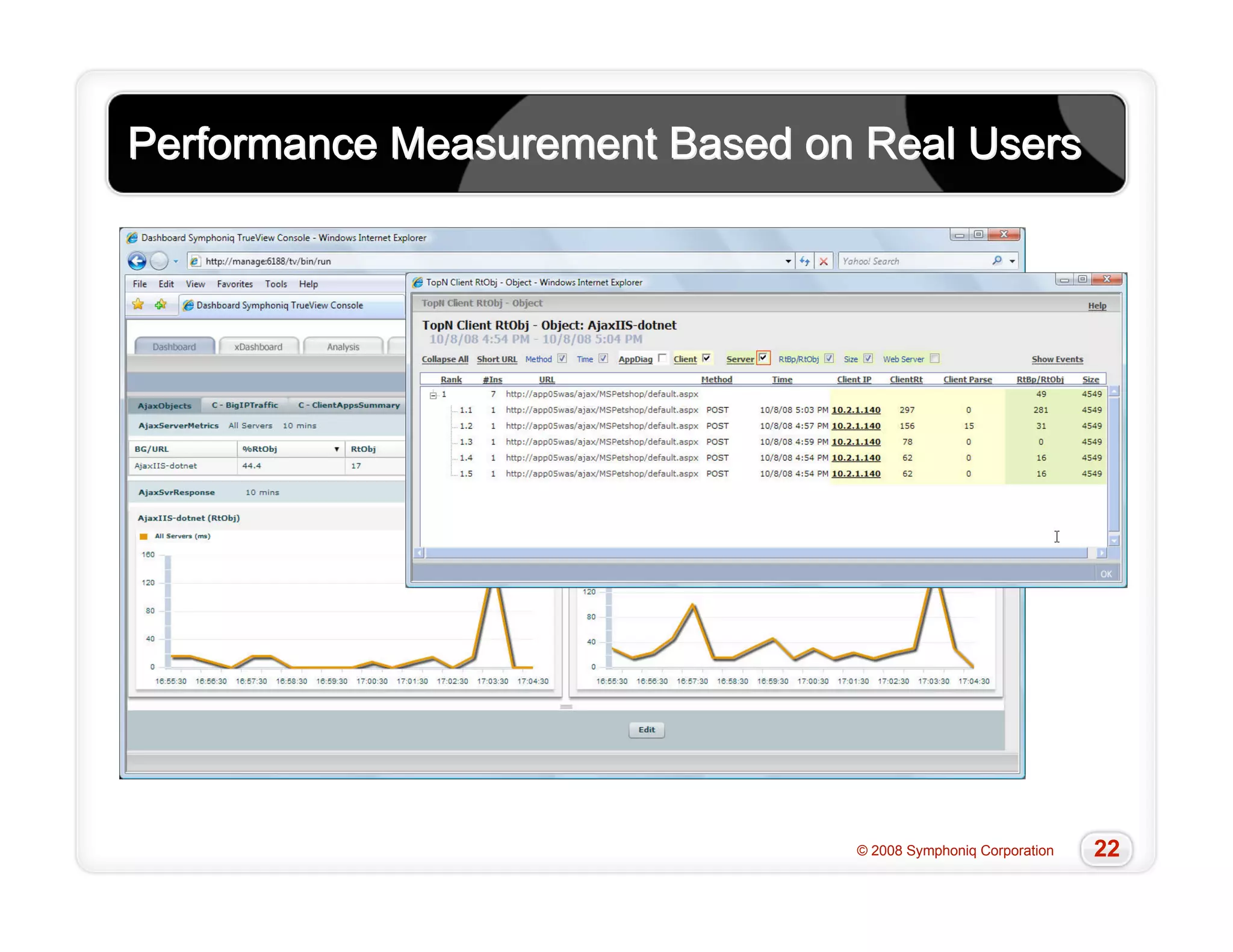
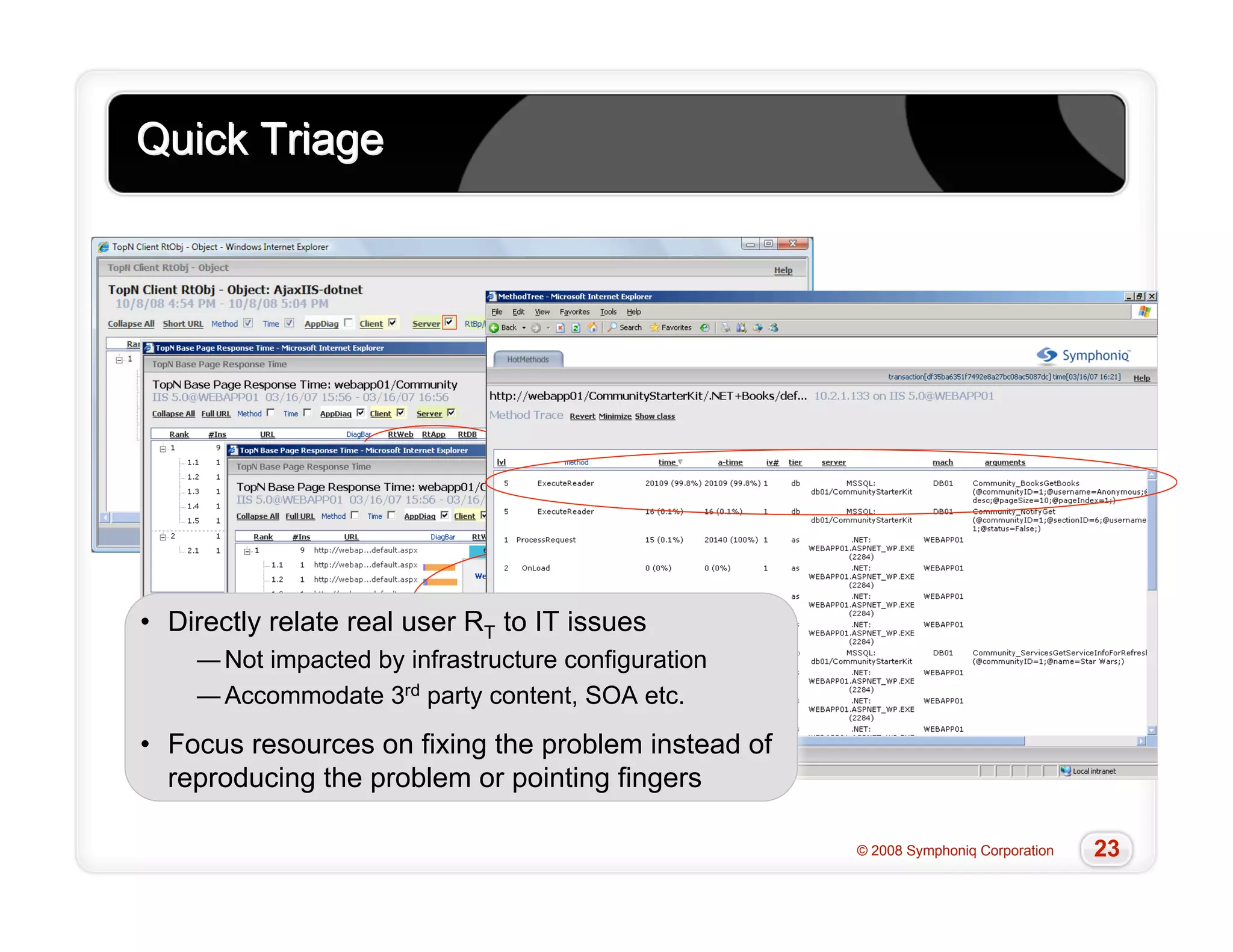
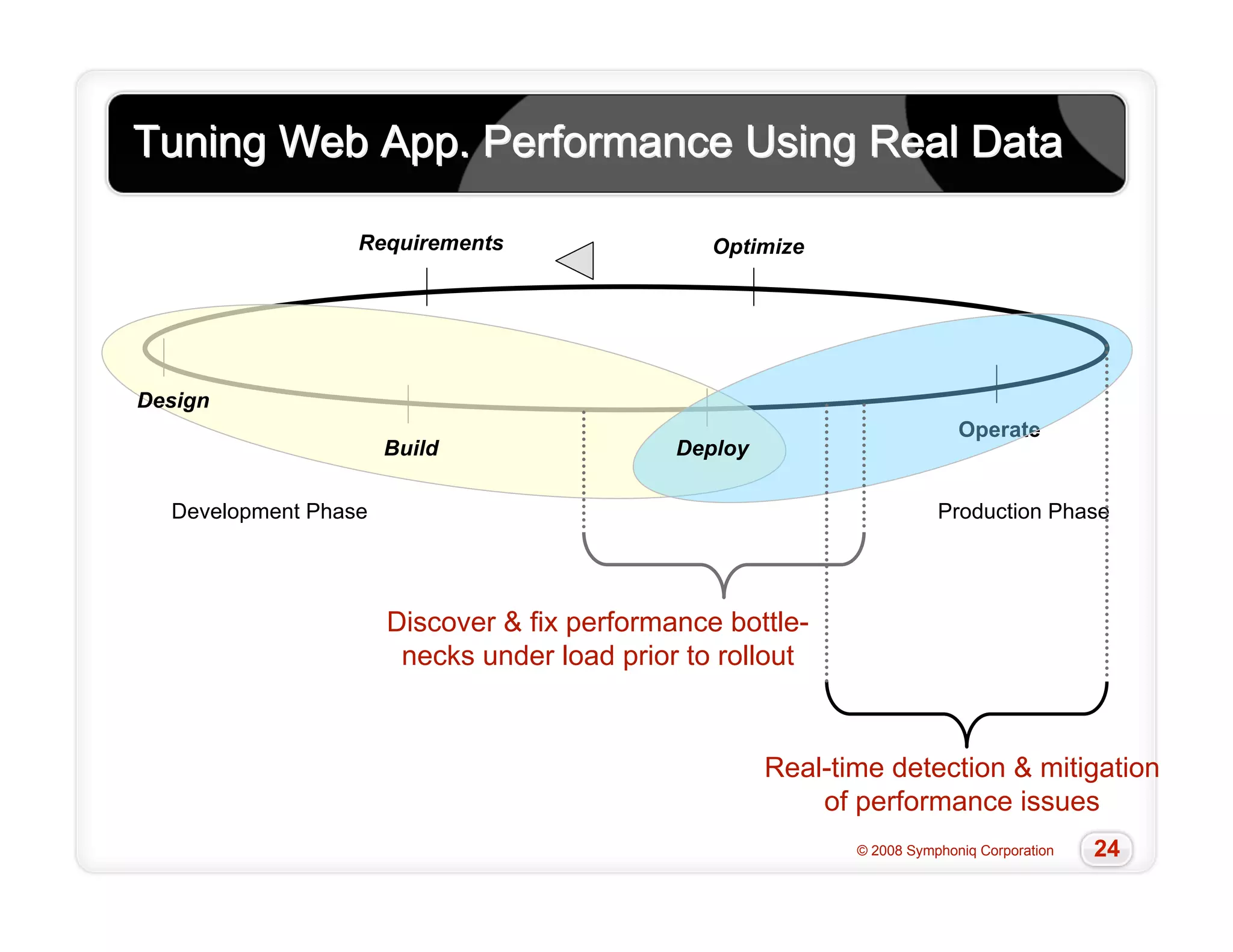
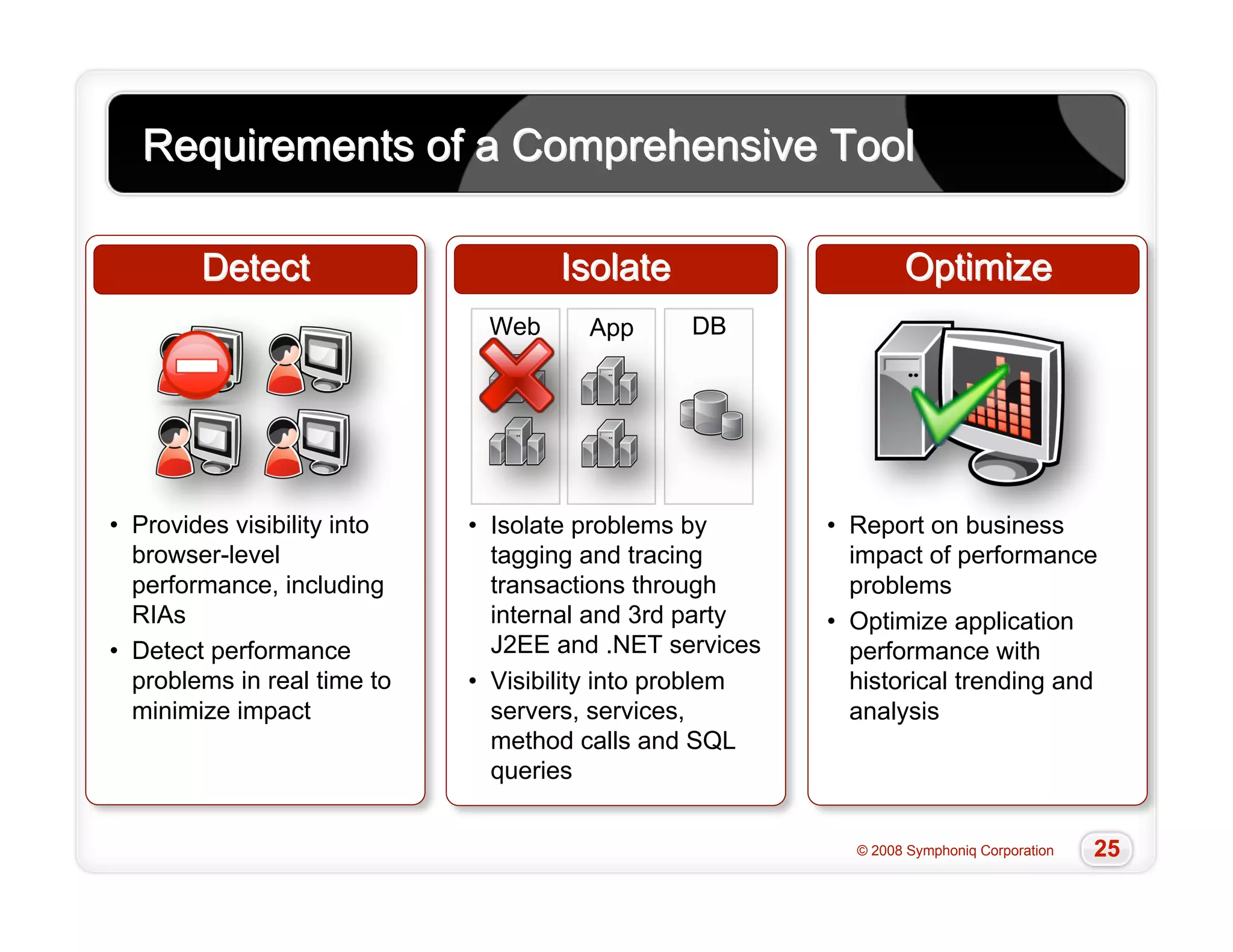
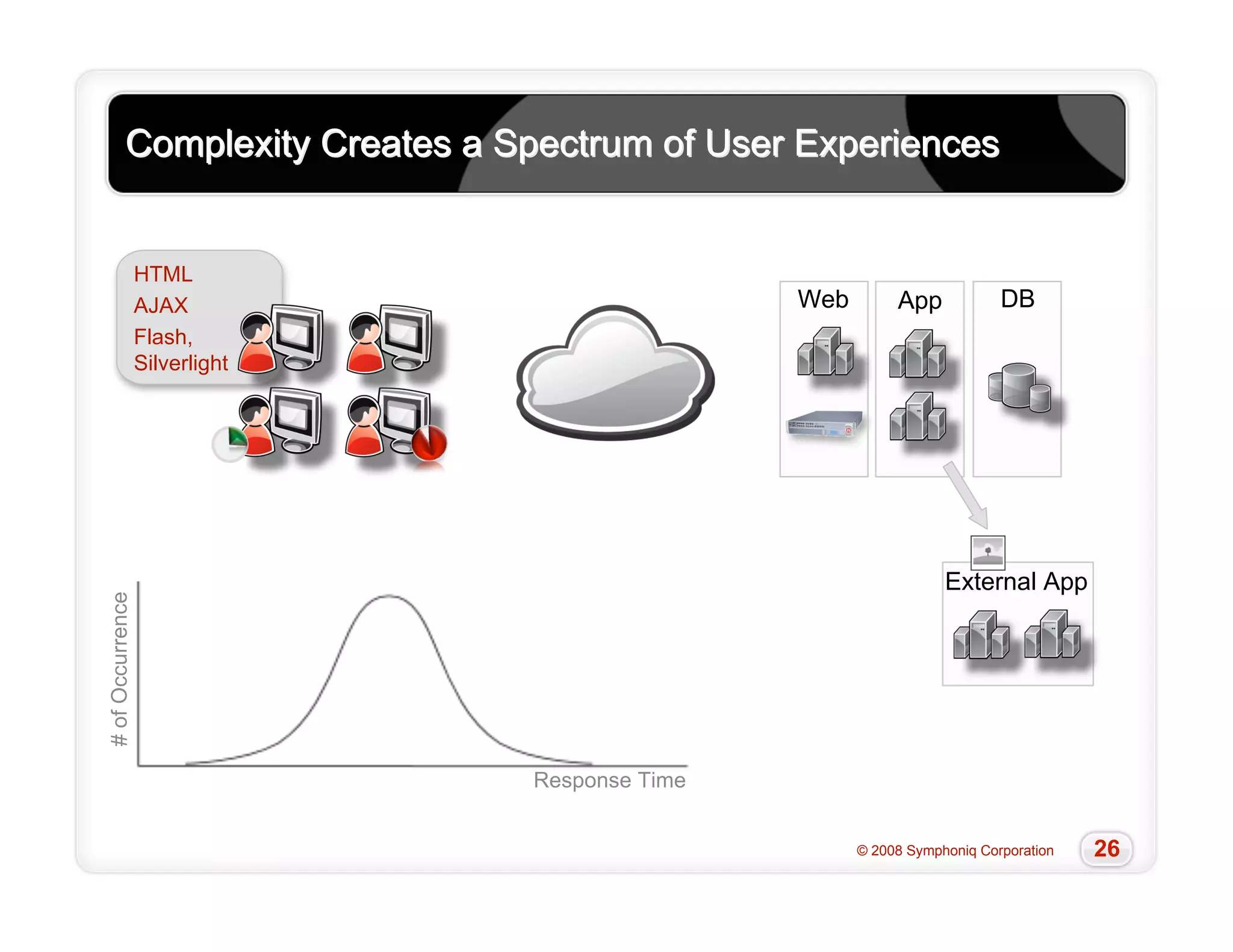
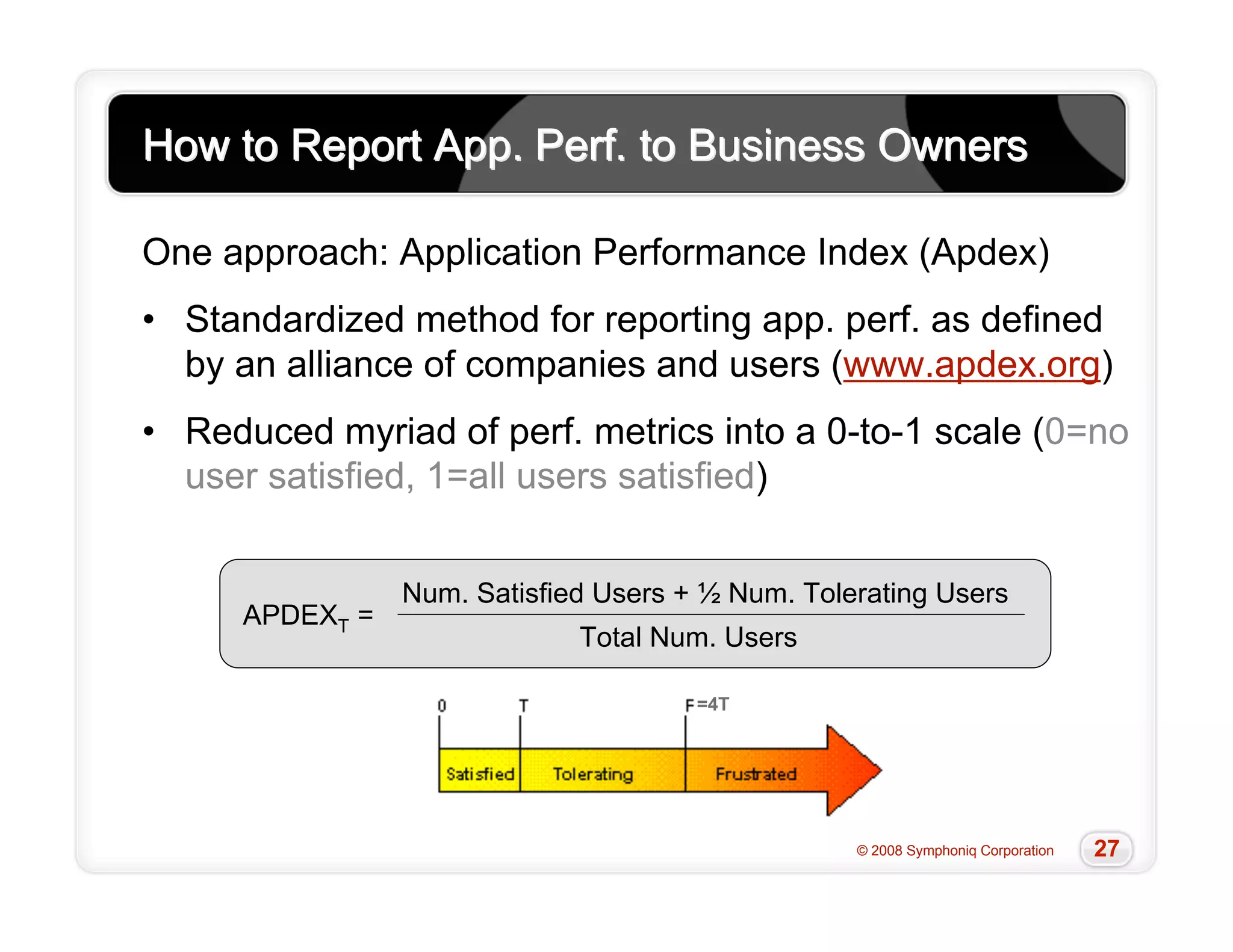
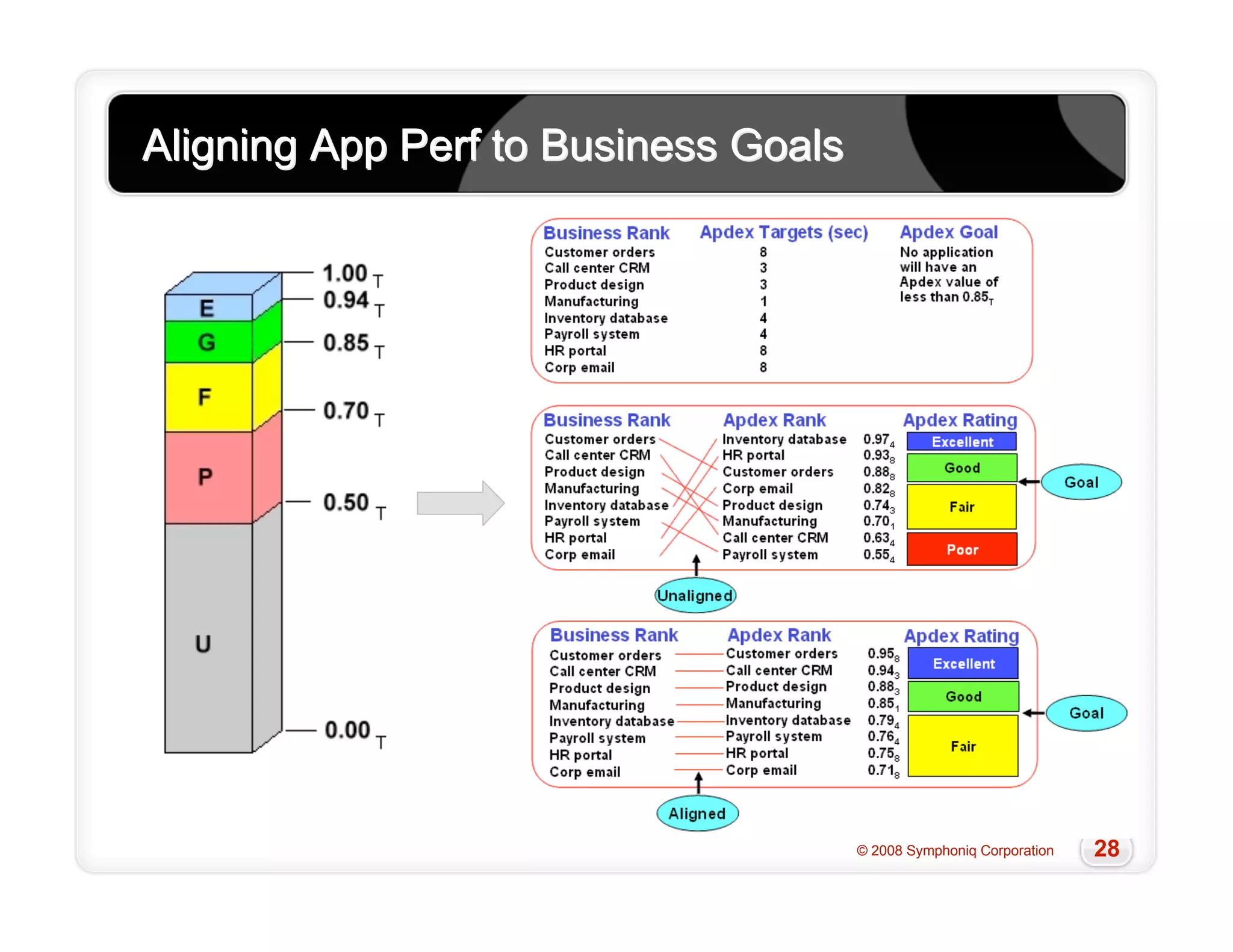
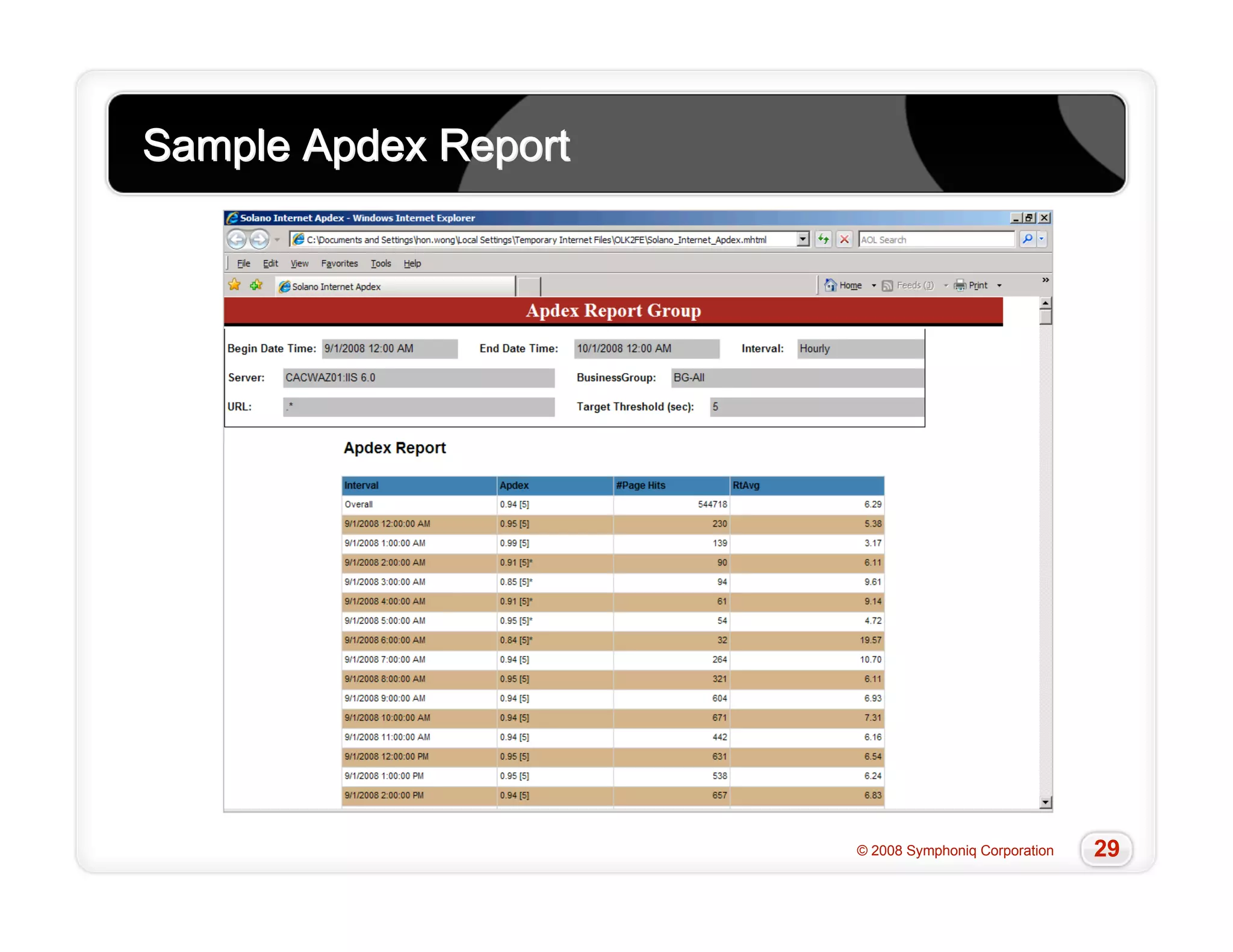
The document discusses the challenges of managing performance for modern web applications. It notes that traditional monitoring tools are inadequate as they do not measure from the user's perspective and cannot account for factors like third-party content and dynamic architectures. The document advocates for a new approach that directly measures response time at the browser level to provide accurate, correlated data across tiers. This real user monitoring allows teams to quickly triage issues, understand business impact, and optimize performance.