SI Sheet (notes)
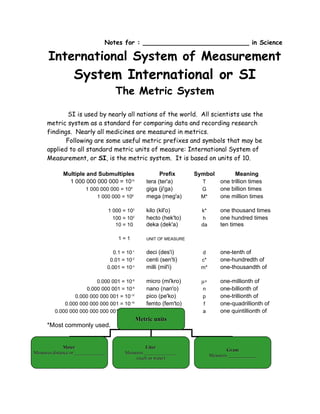
- 1. Notes for : ___________________________ in Science International System of Measurement System International or SI The Metric System SI is used by nearly all nations of the world. All scientists use the metric system as a standard for comparing data and recording research findings. Nearly all medicines are measured in metrics. Following are some useful metric prefixes and symbols that may be applied to all standard metric units of measure: International System of Measurement, or SI, is the metric system. It is based on units of 10. Multiple and Submultiples Prefix Symbol Meaning 1 000 000 000 000 = 1012 tera (ter'a) T one trillion times 1 000 000 000 = 109 giga (ji'ga) G one billion times 1 000 000 = 106 mega (meg'a) M* one million times 1 000 = 103 kilo (kil'o) k* one thousand times 100 = 102 hecto (hek'to) h one hundred times 10 = 10 deka (dek'a) da ten times 1=1 UNIT OF MEASURE 0.1 = 10-1 deci (des'i) d one-tenth of 0.01 = 10-2 centi (sen'ti) c* one-hundredth of 0.001 = 10-3 milli (mil'i) m* one-thousandth of 0.000 001 = 10-6 micro (mi'kro) µ∗ one-millionth of 0.000 000 001 = 10-9 nano (nan'o) n one-billionth of 0.000 000 000 001 = 10-12 pico (pe'ko) p one-trillionth of 0.000 000 000 000 001 = 10-15 femto (fem'to) f one-quadrillionth of 0.000 000 000 000 000 001 = 10-18 atto (at'to) a one quintillionth of Metric units *Most commonly used. Meter Liter Gram Measures distance or _____________ Measures ______________ Measures ____________ (such as water)
- 2. 1. There are no ___________in the metric system. 2. There are no ___________ in the metric system. 3. When the liter symbol is hand written, it must be a __________ letter so that is not confused with a _______. When it is with another symbol, lower case can be used. Ex: L stands for _______, and ml or mL both mean __________. 4. Metric temperature is __________. Celsius is a more common form of SI temperature, because it is derived directly from the Kelvin scale. On the Celsius scale, water freezes at ___oC and boils at _____o C. Sentence to help you remember: ________________________________ Prefix scale 3 scale m L g Identify the position of the decimal. If there is no decimal, it is at the end of the number. 1. Identify the location of prefix that you _____ (and notice if it is a meter, liter or gram) on the metric scale. Put your pencil there. 2. Identify the ________ position (where the new prefix is located—or what you want to find out). 3. Determine whether you need to move right or ________ . 4. Determine how many ________ you need to move to get there. 5. Move the _______ the same number times and in the same direction. • 3.4m = ______ cm • Notice where the decimal is (.) • Put your pencil on (units) where m would be. • Move your pencil right 2 times to cm on the chart. • Move the decimal right 2 times for the answer.
- 3. • 500mg = _____ g • Notice where where the decimal should be and your pencil on the mg box. • Move your finger 3 times left then move the decimal 3 times left. • .2kL = _____ L • Notice the decimal and pencil on the chart. • Count 3 right then move the decimal 3 right. • Practice just a few then check your answers with a friend. • 3.5cm=____mm • 500mg=____g • 2L=____mL • .25km=____m • Metric units of volume can be converted to cubic centimeters, cc, or centimeters cubed, cm3, very easily. • Step one… convert to millileters (mL). • Step two…milliliters are _________to cubic centimeters and to centimeters cubed. • So… _____ = _____ = _____ • 23mL = _____cc • 55cc = _____cm3 • .7L = _____cc • First convert to mL • .7L = _____mL • You get _______mL • Then _______mL = ________cc • Now that wasn’t so tough was it?