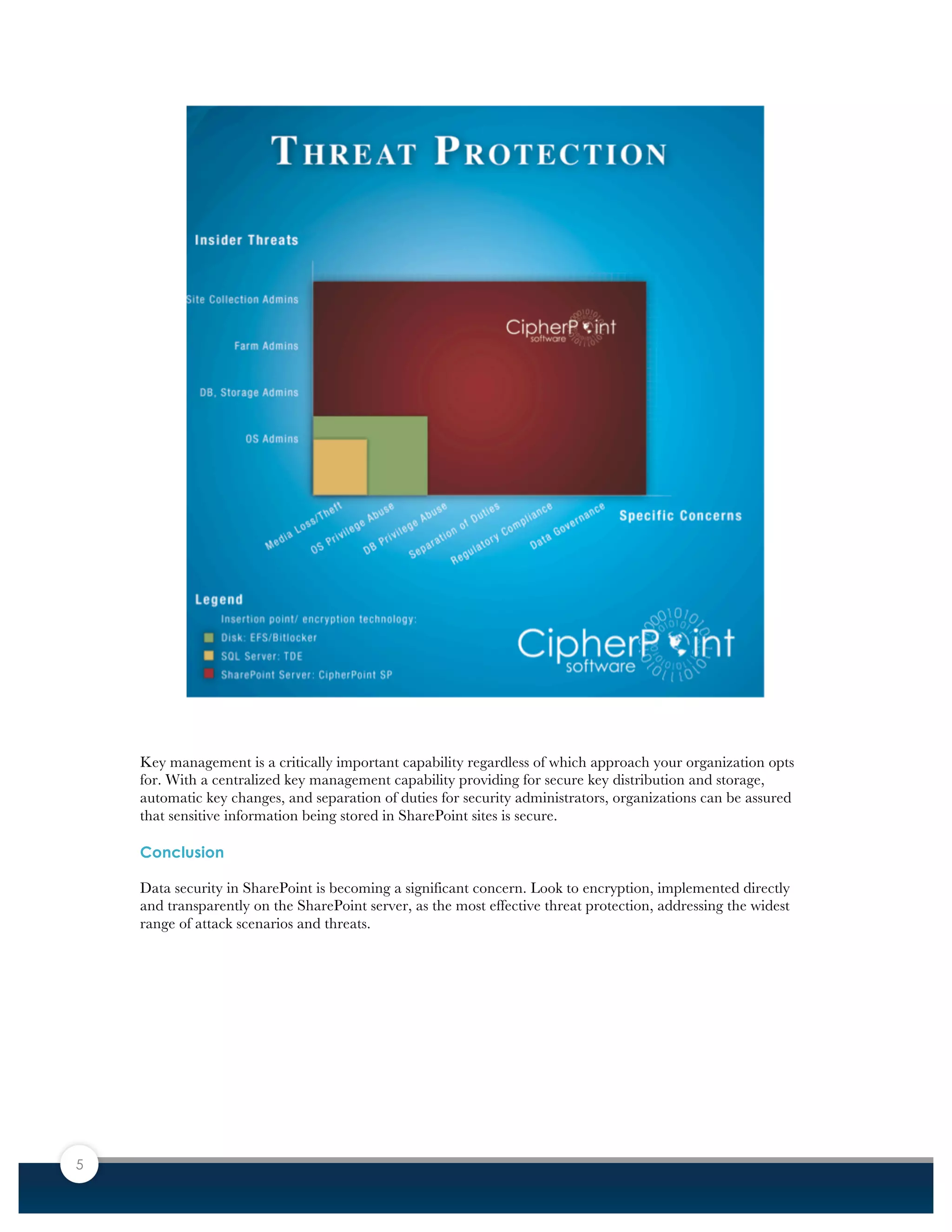
Popular collaboration platforms like SharePoint are increasingly used to store private information, raising data security concerns. While encryption at the disk or database levels provide some protection, they do not prevent access by privileged users like administrators. Transparent encryption at the application level protects against both external and insider threats by encrypting data and restricting access based on need-to-know. This provides the most comprehensive security for sensitive information stored in SharePoint.