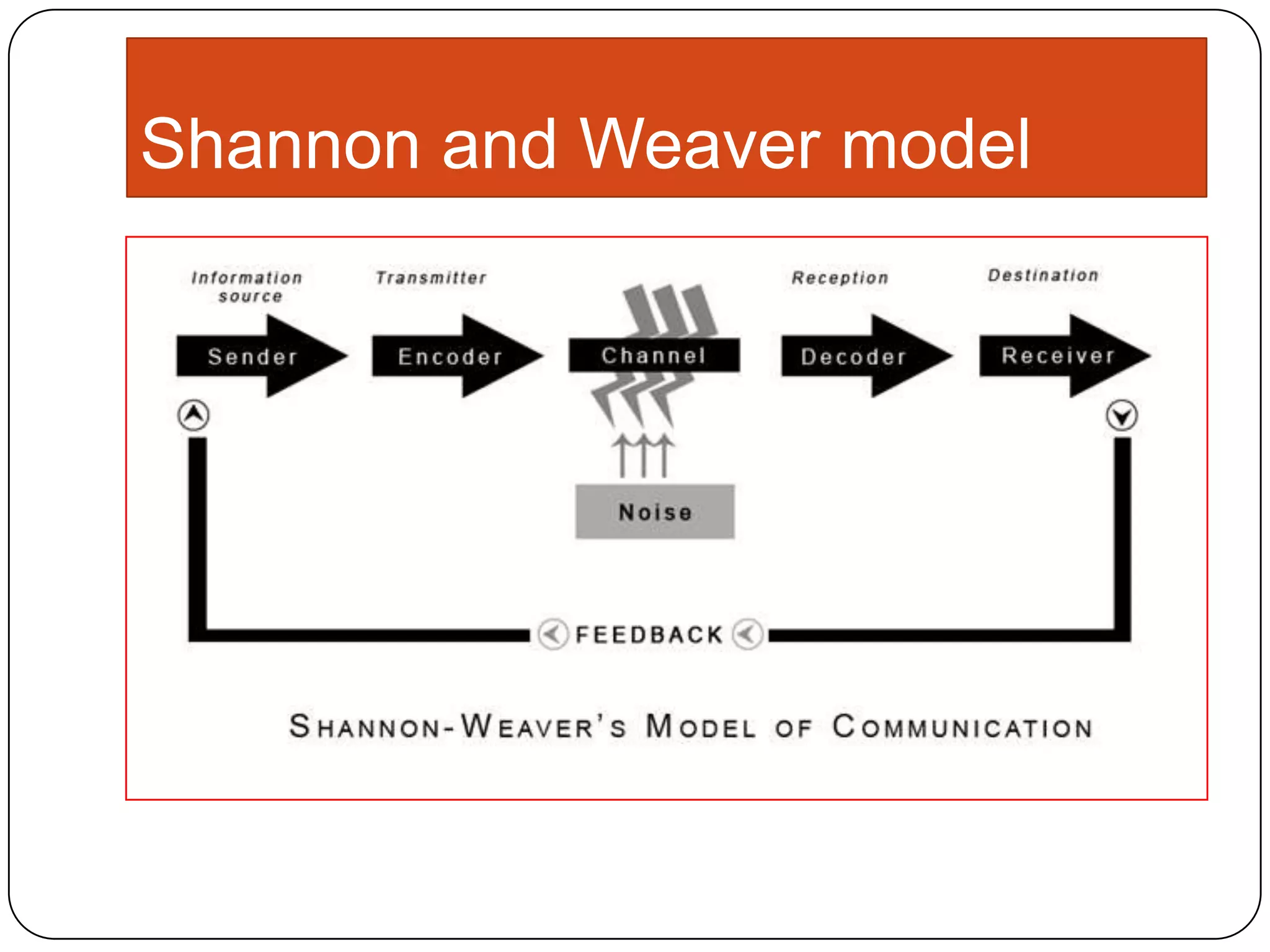
Claude Shannon and Warren Weaver were engineers at Bell Labs who developed a model of communication to maximize efficiency of telephone cables and radio waves. Their model included an information source, transmitter to encode a message, channel to transmit signals, receiver to decode the message, and destination to receive the message. Noise is a dysfunctional factor that can interfere with the message and reduce fidelity. The model helped establish a mathematical theory of communication and is considered foundational to the field.