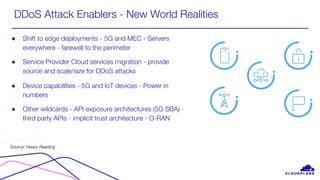
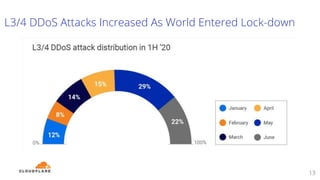
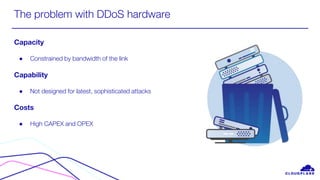
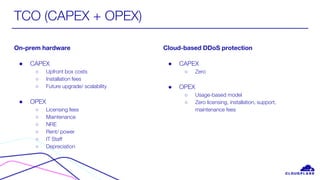
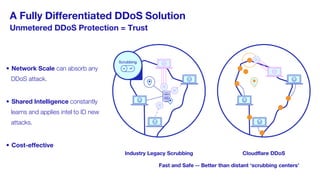
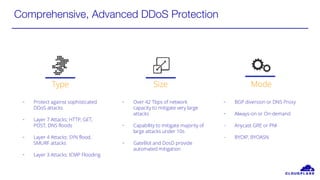
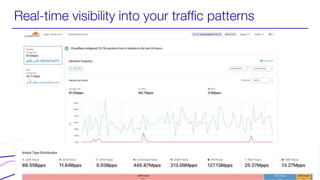
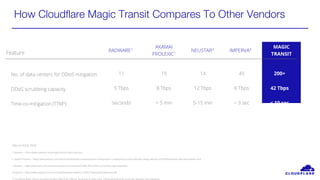
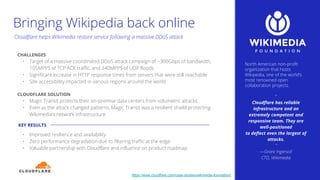
The webinar discusses the rising threats of DDoS attacks and explores strategies for service providers to implement DDoS mitigation as a service. Cloudflare, a leader in the field, highlights the benefits of their global network, which can absorb high-capacity attacks while offering cost-effective, cloud-based solutions with automated mitigation. Key topics include the growing complexity of attacks and the economic impacts on service providers from both direct and indirect attack methods.