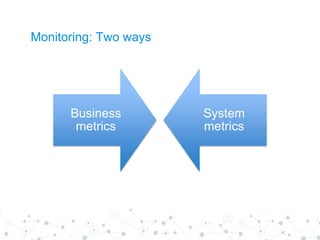
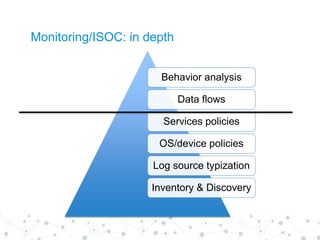
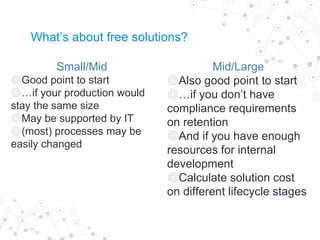
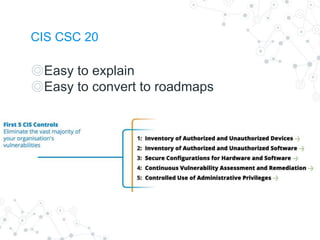
This document provides an overview of security operations (SOC) for companies of all sizes. It discusses the basic questions companies should ask regarding their security needs, how to approach monitoring both business and system metrics, and an in-depth look at monitoring and establishing an internal SOC. It then discusses solutions for security operations, both free and enterprise options, and things to consider if solutions are not working as expected or fail. The document concludes with embedding security into IT operations, discussing overlapping processes, compliance standards, typical incident response plans, and automating security processes. It also covers different approaches to security testing programs.