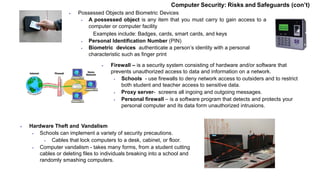
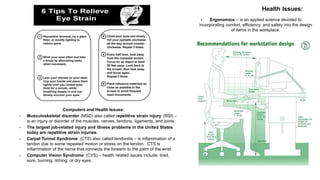
This document discusses various computer security risks, including viruses, malware, hacking and unauthorized access. It also covers ethics around issues like privacy, monitoring, copyright and dealing with objectionable online content. Effective computer security requires antivirus software, passwords, firewalls and backing up data. Users must be educated on responsible and ethical computer use.