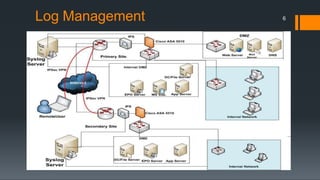
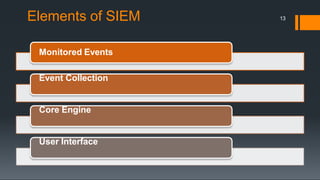
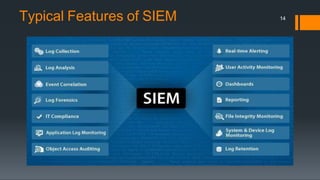
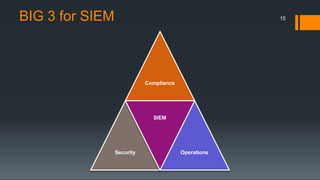
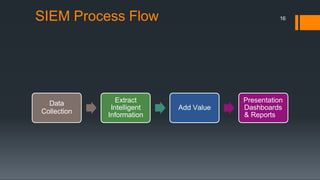
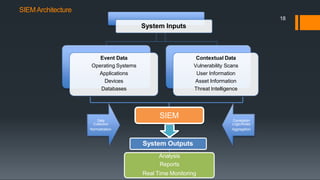
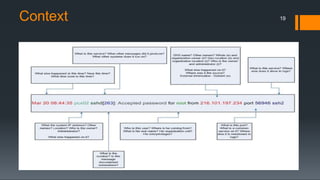
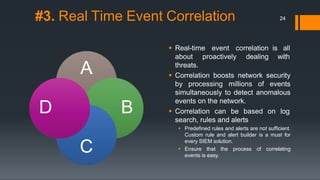
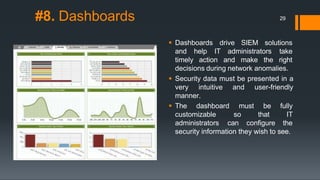
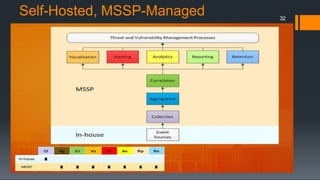
This document discusses log management and security information and event management (SIEM). It defines log management as collecting, aggregating, retaining, analyzing, searching, and reporting large volumes of computer-generated log messages. SIEM is described as combining security information management and security event management to identify threats, collect audit logs for security and compliance, and conduct investigations. The document outlines typical SIEM features and provides details on SIEM deployment options.