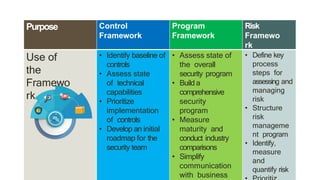
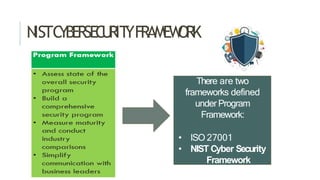
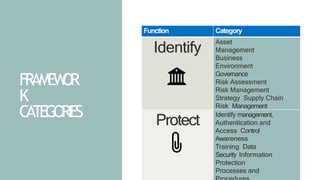
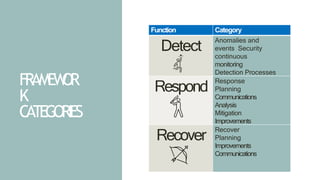
The document discusses cybersecurity frameworks, including their purpose of reducing risk and identifying vulnerabilities. It specifically describes the NIST Cybersecurity Framework, which defines a common language for managing risk across five functions: Identify, Protect, Detect, Respond, and Recover. The Framework includes categories within each function to help organizations assess their current security posture and develop a roadmap for improvement.