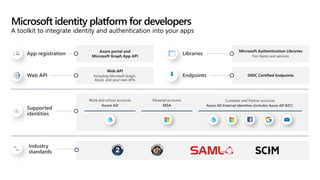
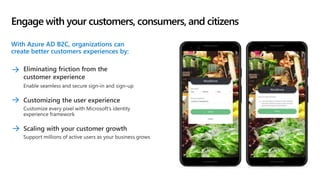
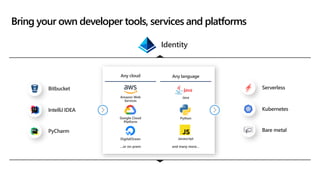
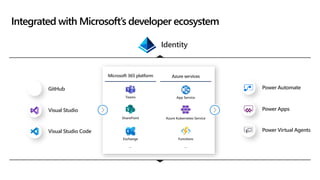
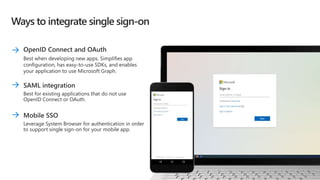
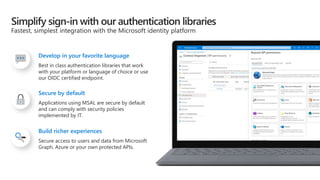
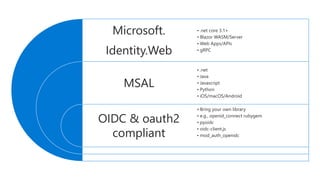
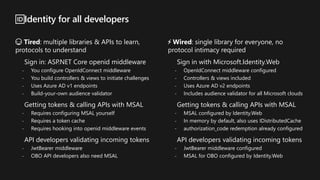
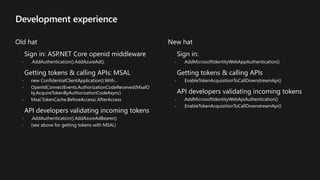
The document discusses the Microsoft Identity Platform aimed at helping developers integrate identity and access management into applications, emphasizing ease of use and security features. It highlights the benefits of using Microsoft services for authentication, including support for a variety of programming languages and developer tools, along with compliance and customization options. Additionally, the document outlines the transition from traditional authentication methods to a more streamlined approach using the Microsoft.Identity.Web library.