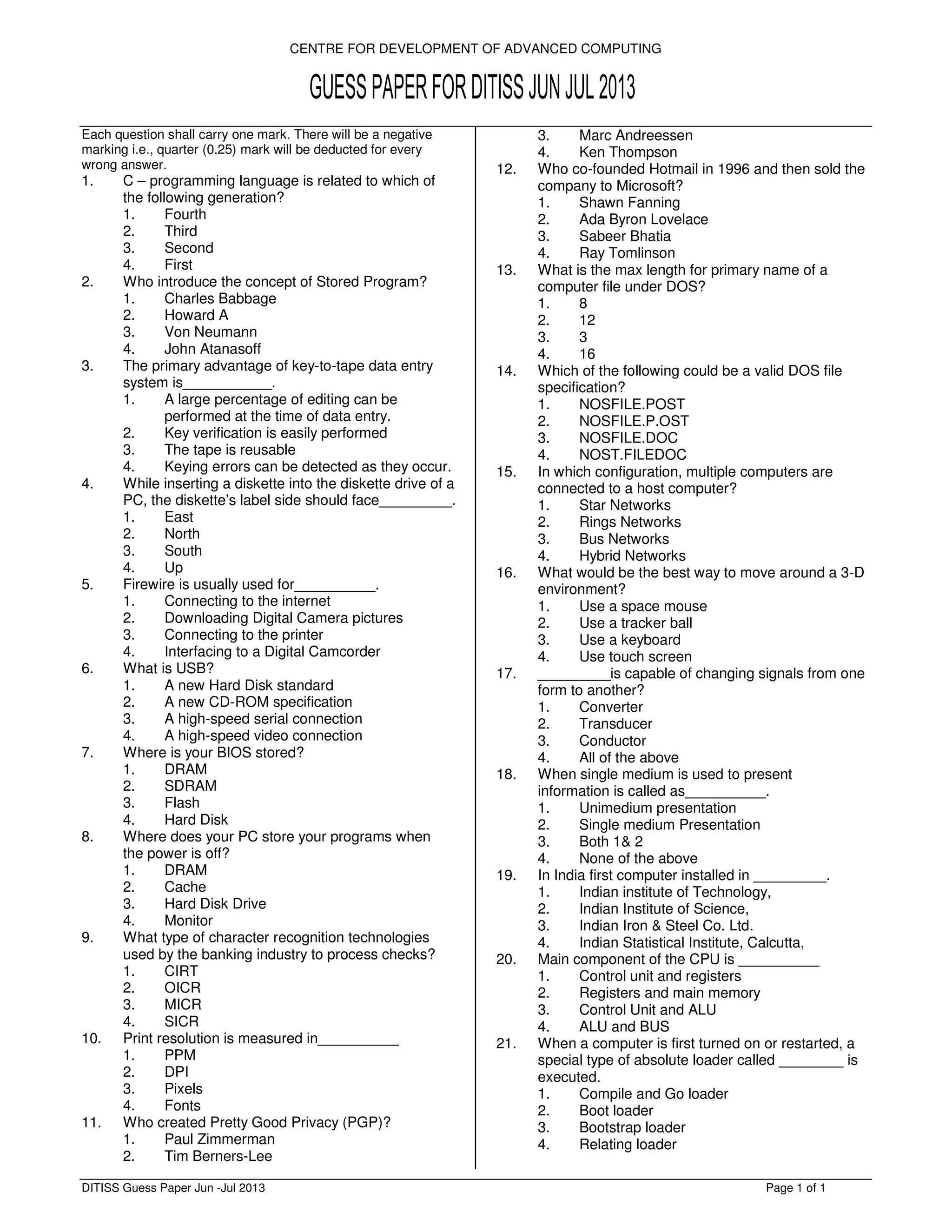
The document presents a collection of technical questions related to computer science, programming, operating systems, and networking, structured in a quiz format. Each question is multiple-choice with four options provided and covers topics ranging from programming languages, data entry systems, to protocols and memory management. It is designed as a guess paper for assessors in a computer technology examination conducted by the Centre for Development of Advanced Computing.