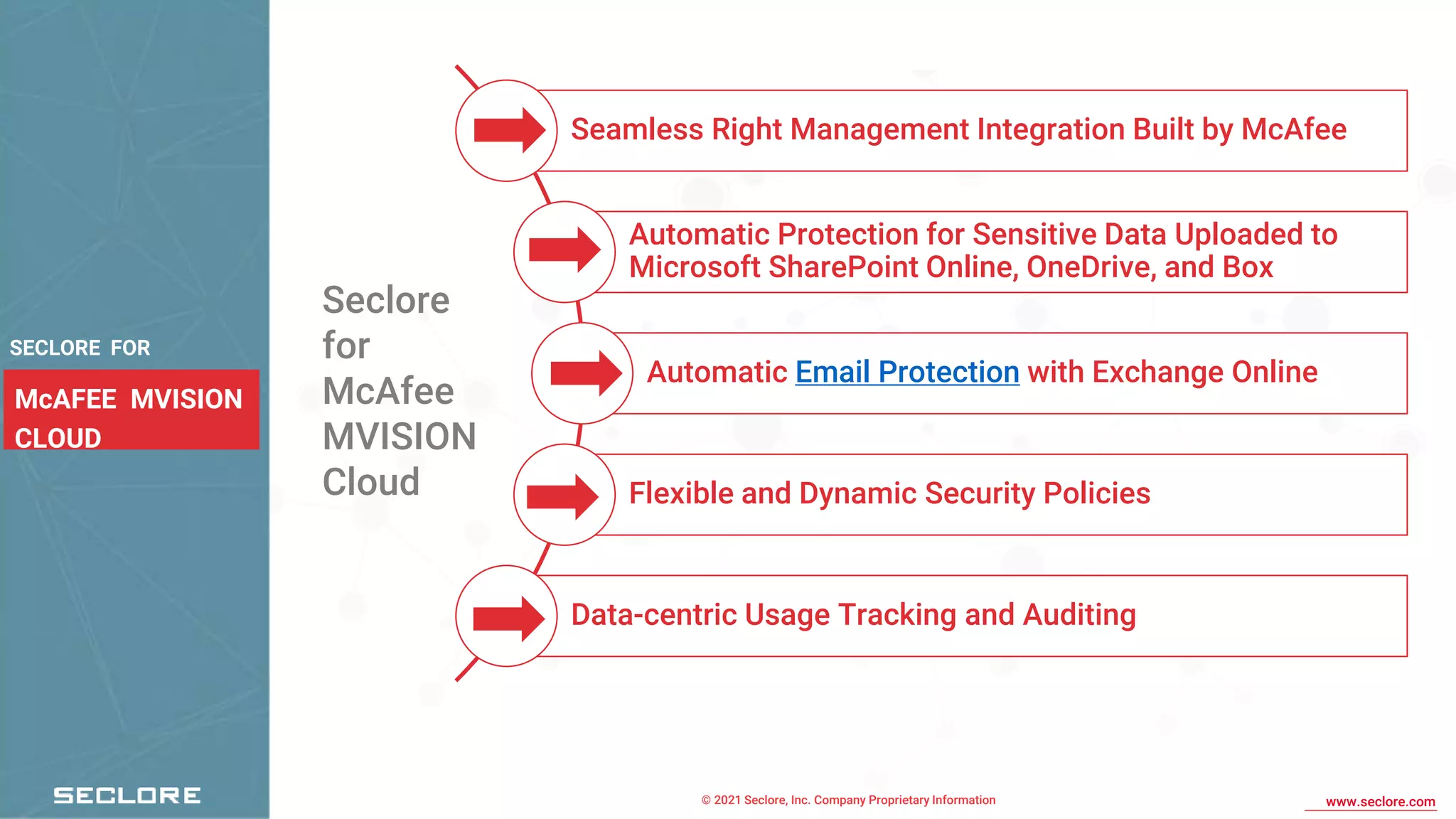
Seclore provides a data-centric security platform that enhances productivity by allowing organizations to securely collaborate with sensitive data without blocking or monitoring it. The integration with McAfee MVISION Cloud implements persistent usage controls for emails and documents, ensuring continuous security once data is shared. Seclore's solution helps over 2000 companies across 29 countries achieve their data security and compliance goals with minimal friction.