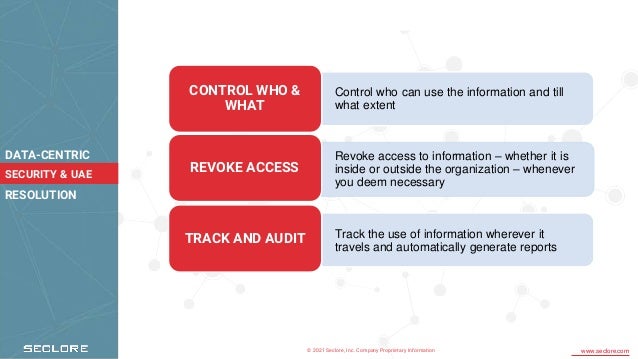
The document outlines Qatar's national cybersecurity strategy in preparation for the FIFA 2022 World Cup, emphasizing the importance of digital technologies and a collaborative approach to cybersecurity. Seclore's data-centric security solutions are presented as essential tools for organizations to comply with the FIFA cybersecurity framework and manage data securely. The solutions enable organizations to control data access, track usage, and protect information effectively both internally and externally.