This presentation covers the application of the REST architectural style in designing web services, emphasizing the proper use of HTTP methods, status codes, and HATEOAS (Hypermedia as the Engine of Application State). It explains the principles of REST using the Atom Publishing Protocol and provides examples of various HTTP methods and their characteristics, as well as the significance of URIs and status codes in resource management. The document also discusses RESTful implementations and highlights the Google Calendar Data API as a practical application of these principles.

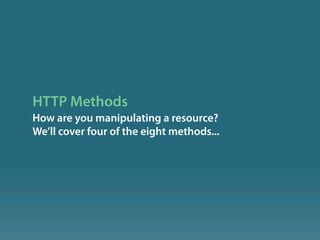
![HTTP
"Hypertext Transfer Protocol (HTTP) is an
application-level protocol for distributed,
collaborative, hypermedia information systems. Its
use for retrieving inter-linked resources led to the
establishment of the World Wide Web."[1]](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-3-320.jpg)

![Limited Vocabulary
There are only 8 methods: HEAD, GET, POST, PUT,
DELETE, TRACE, OPTIONS, CONNECT (we're only
going to talk about 4 of them); but you get to de ne
your own resources.[2]](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-7-320.jpg)
![What Makes a Service RESTful?
If the HTTP method doesn’t match the method
information, the service isn’t RESTful. If the scoping
information isn’t in the URI, the service isn’t
resource-oriented. These aren’t the only
requirements, but they’re good rules of thumb.
From RESTful Web Services[3]](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-9-320.jpg)
![More on Safety
A hit counter is generally "safe". Yes, it changes state
but the user is not held accountable for that state
transition.
Deleting something is not safe: you've held the user
accountable. For example, Google Web Accelerator
(cache pre-fetching) broke 37signals' Backpack web
application because they were using GET to delete
information[4].](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-12-320.jpg)
![HTTP Status Codes
What was the result of your request?
A few examples...[5]](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-16-320.jpg)








![418 I’m A Teapot
According to the Hyper Text Coffee Pot
Control Protocol (HTCPCP/1.0)[6]:
Any attempt to brew coffee with a teapot should result
in the error code "418 I'm a teapot". The resulting entity
body MAY be short and stout.
Clipped photo by revolution cycle / CC BY 2.0
http://www. ickr.com/photos/11795120@N06/3832234809/](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-28-320.jpg)



![Uniform Interface
• URI identi es the resource.
• HTTP method says how we're manipulating the
resource.
• Entity-header elds and entity-body[7] represent the
resource.
• Requests and responses are self-descriptive and
stateless.](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-32-320.jpg)
![Hypermedia As The Engine Of
Application State (HATEOAS)
From Chapter 5 of the Fielding Dissertation[8]:
In order to obtain a uniform interface, multiple architectural constraints are
needed to guide the behavior of components. REST is de ned by four interface
constraints: identi cation of resources; manipulation of resources through
representations; self-descriptive messages; and, hypermedia as the engine of
application state.](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-33-320.jpg)

![Google Calendar API
The Google Calendar Data API allows client
applications to view and update calendar events in
the form of Google Data API feeds.
Your client application can use the Calendar Data
API to create new events, edit or delete existing
events, and query for events that match particular
criteria.
From the Developer's Guide[9]](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-48-320.jpg)







![Credits
Author: Bradley Holt
Technical Review: Josh Sled
Layout & Design: Jason Pelletier
Photo: Revolution Cycle, Solar Powered Tea Pot, http://www. ickr.com/photos/11795120@N06/3832234809/
This presentation licensed under Creative Commons -- Attribution 3.0 United States License.
[1]: Hypertext Transfer Protocol. (2009, August 25). In Wikipedia, The Free Encyclopedia. Retrieved August 25, 2009, from
http://en.wikipedia.org/wiki/Hypertext_Transfer_Protocol
[2]: HTTP/1.1: Method De nitions. (n.d.). Retrieved August 26, 2009, from World Wide Web Consortium - Web Standards:
http://www.w3.org/Protocols/rfc2616/rfc2616-sec9.html
[3]: Richardson, L., & Ruby, S. (2007). RESTful Web Services. Sebastopol, CA: O’Reilly Media, Inc.
[4]: Google Web Accelerator: Hey, not so fast - an alert for web app designers. (2005, May 6). Retrieved September 8, 2009, from Signal
vs. Noise: http://37signals.com/svn/archives2/google_web_accelerator_hey_not_so_fast_an_alert_for_web_app_designers.php
[5]: HTTP/1.1: Status Code De nitions. (n.d.). Retrieved August 27, 2009, from World Wide Web Consortium - Web Standards:
http://www.w3.org/Protocols/rfc2616/rfc2616-sec10.html
[6]: Hyper Text Coffee Pot Control Protocol (HTCPCP/1.0) (1998, April 1). Retrieved August 31, 2009, from The Internet Engineering Task
Force (IETF): http://www.ietf.org/rfc/rfc2324.txt
[7]: HTTP/1.1: Entity (n.d.). Retrieved September 1, 2009, from World Wide Web Consortium - Web Standards: http://www.w3.org/
Protocols/rfc2616/rfc2616-sec7.html
[8]: Fielding Dissertation: CHAPTER 5: Representational State Transfer (REST) (2000). Retrieved September 1, 2009, from Architectural
Styles and the Design of Network-based Software Architectures: http://www.ics.uci.edu/~ elding/pubs/dissertation/
rest_arch_style.htm#sec_5_1_5
[9]: Developer's Guide - Google Calendar APIs and Tools (n.d.). Retrieved September 1, 2009, from Google Data APIs:
http://code.google.com/apis/calendar/docs/2.0/developers_guide.html](https://image.slidesharecdn.com/resource-orientedwebservices-090911152529-phpapp01/85/Resource-Oriented-Web-Services-60-320.jpg)