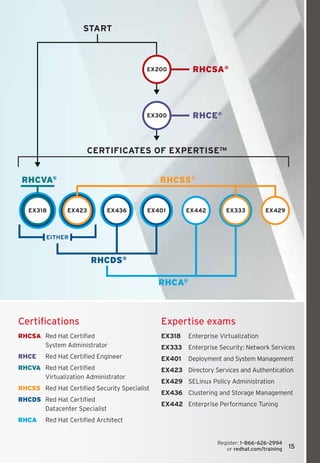
Here are the key certifications from Red Hat:
- RHCSA (Red Hat Certified System Administrator) - Certifies core Linux system administration skills
- RHCE (Red Hat Certified Engineer) - Certifies advanced Linux system administration skills for senior system administrators
- RHCVA (Red Hat Certified Virtualization Administrator) - Certifies skills to deploy and manage virtual hosts using Red Hat Enterprise Virtualization
Red Hat certifications validate hands-on skills through performance-based exams, ensuring certified professionals can effectively manage Red Hat solutions.