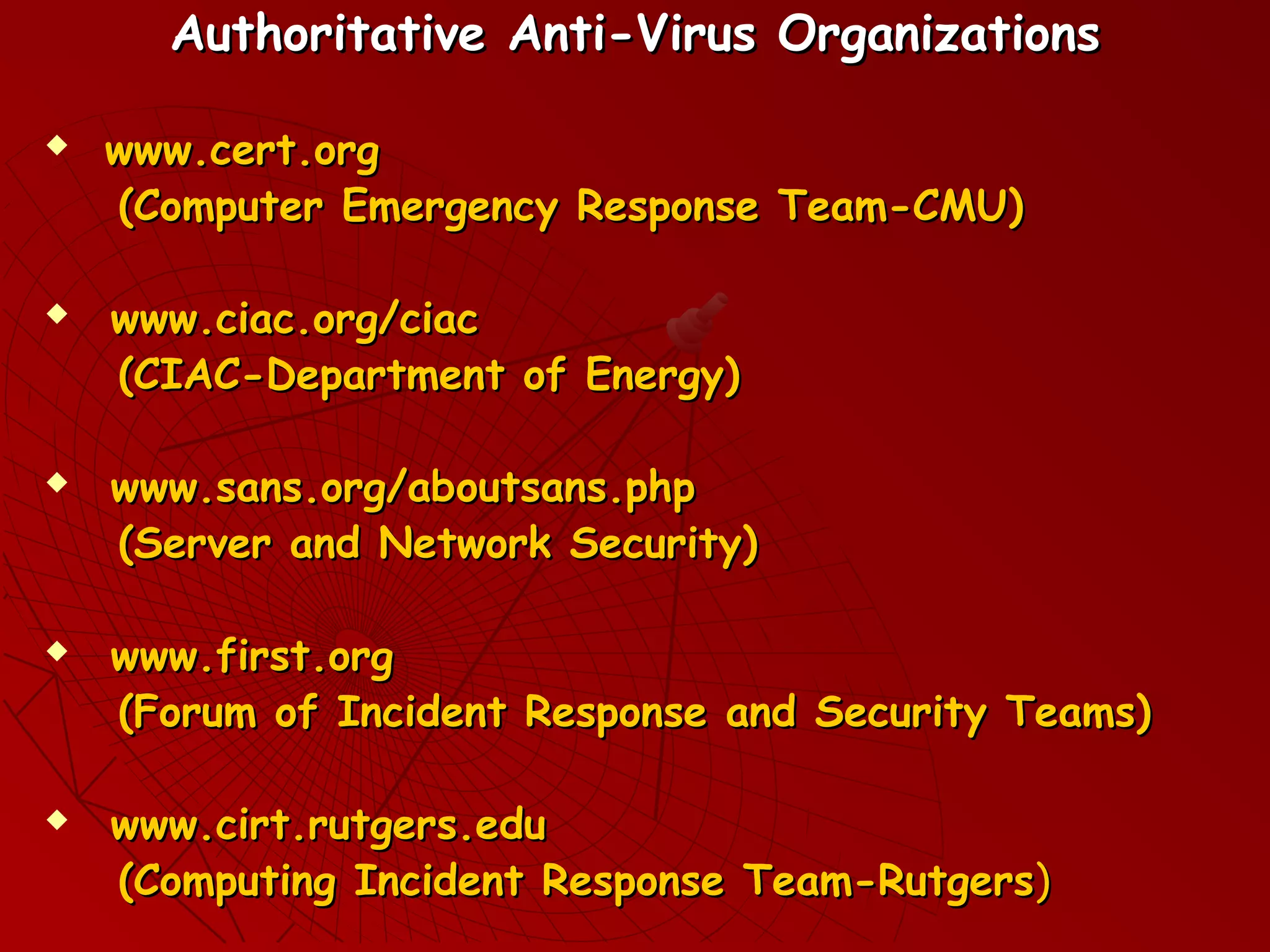
This document discusses various cybersecurity threats such as computer viruses, network worms, Trojan horses, and hoaxes. It defines these threats and describes how they spread and the typical symptoms they cause. It also discusses reasons for software vulnerabilities, hacker motivations, and fallacies about cybersecurity. The document provides best practices for organizations and individuals, such as maintaining updated antivirus software, backing up data, and verifying security information from authoritative sources only.