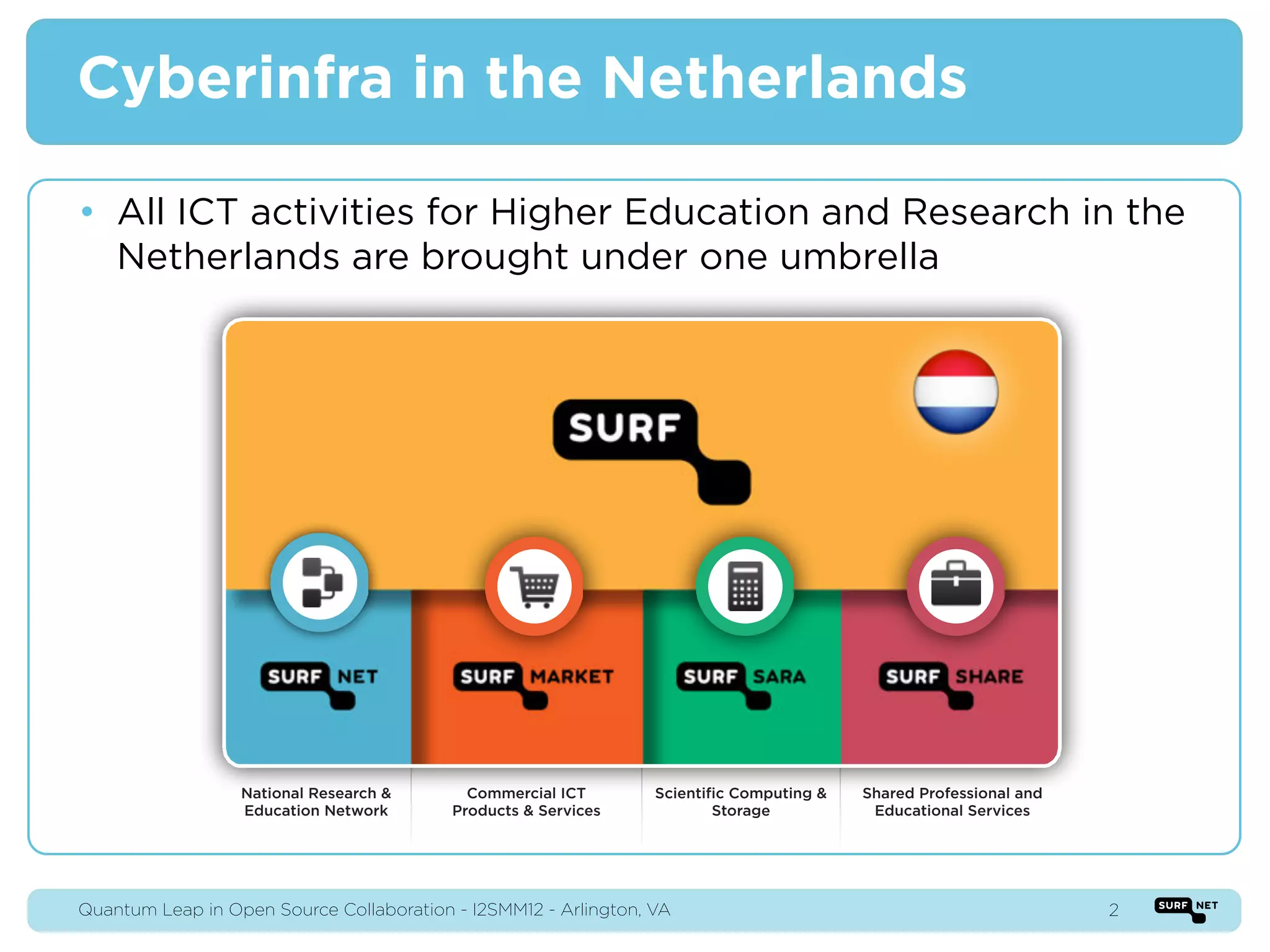
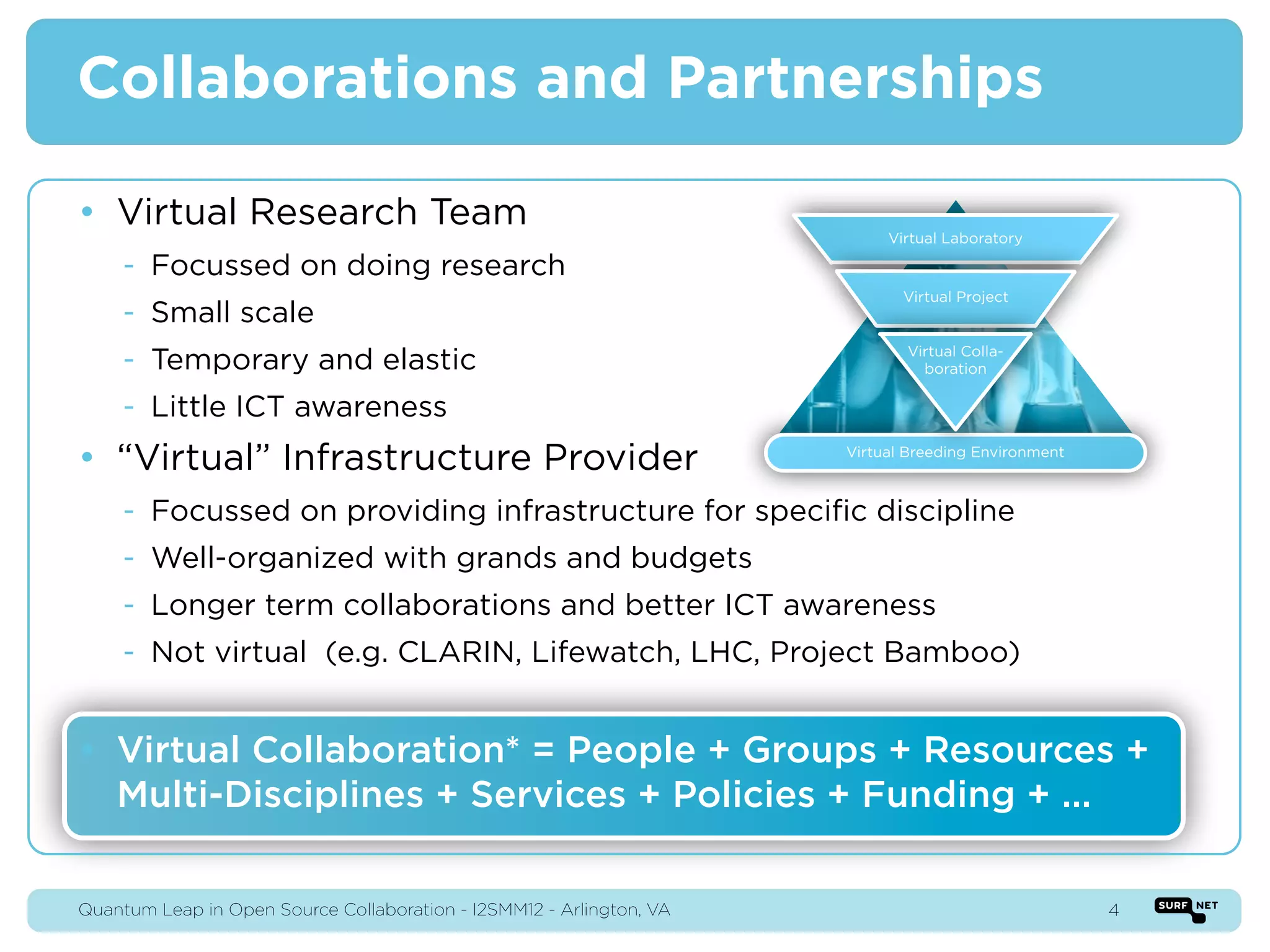
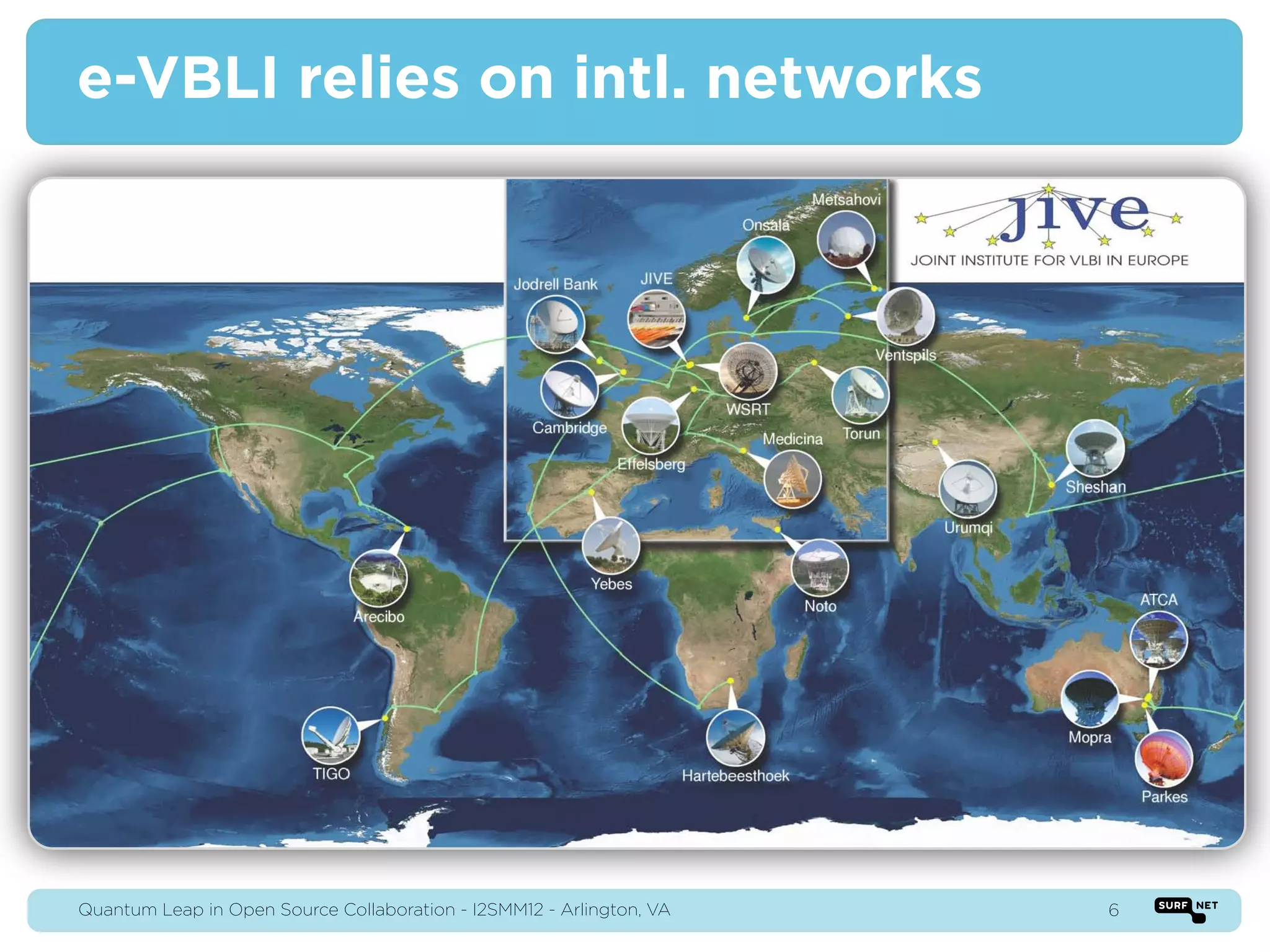
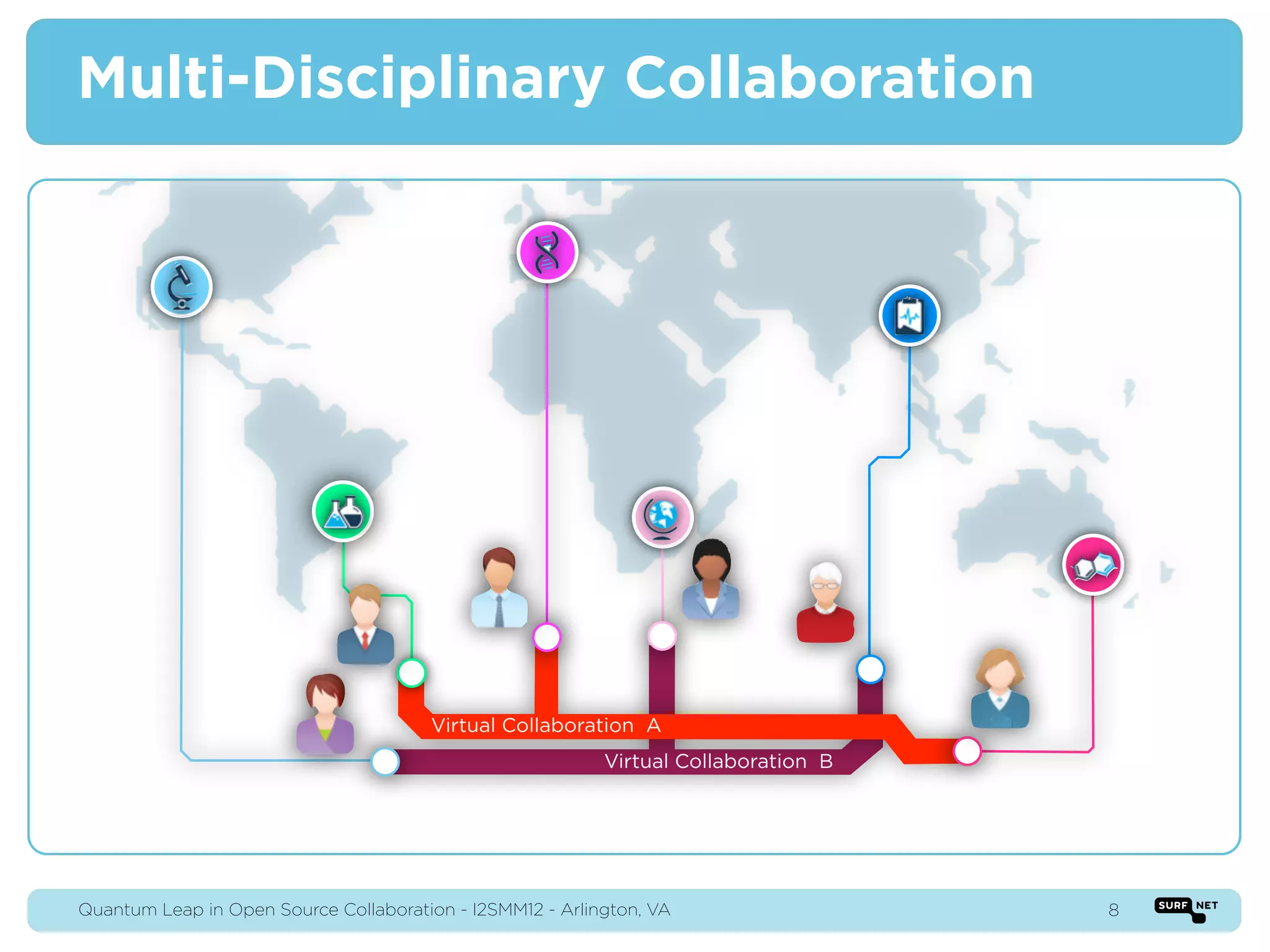
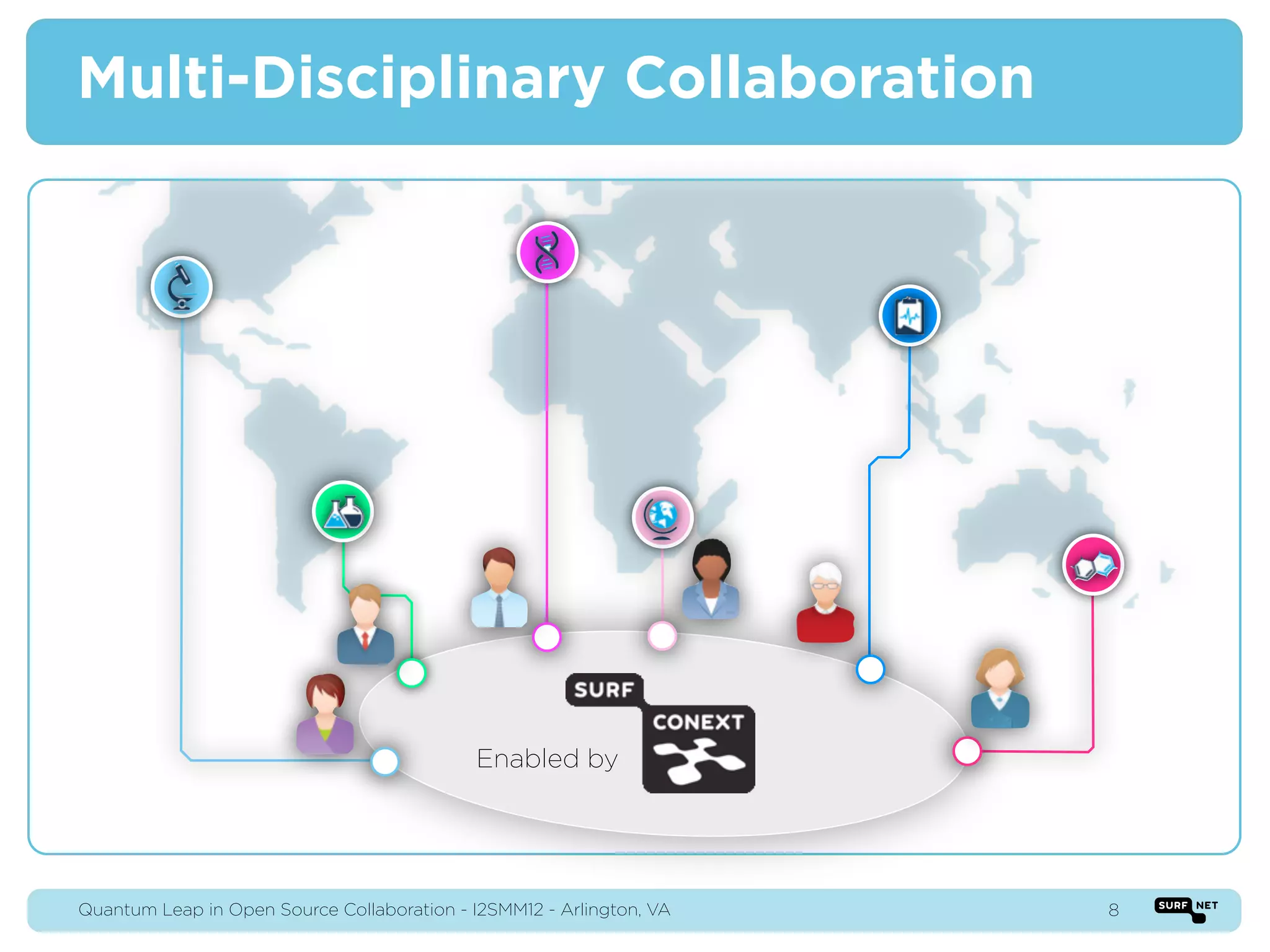
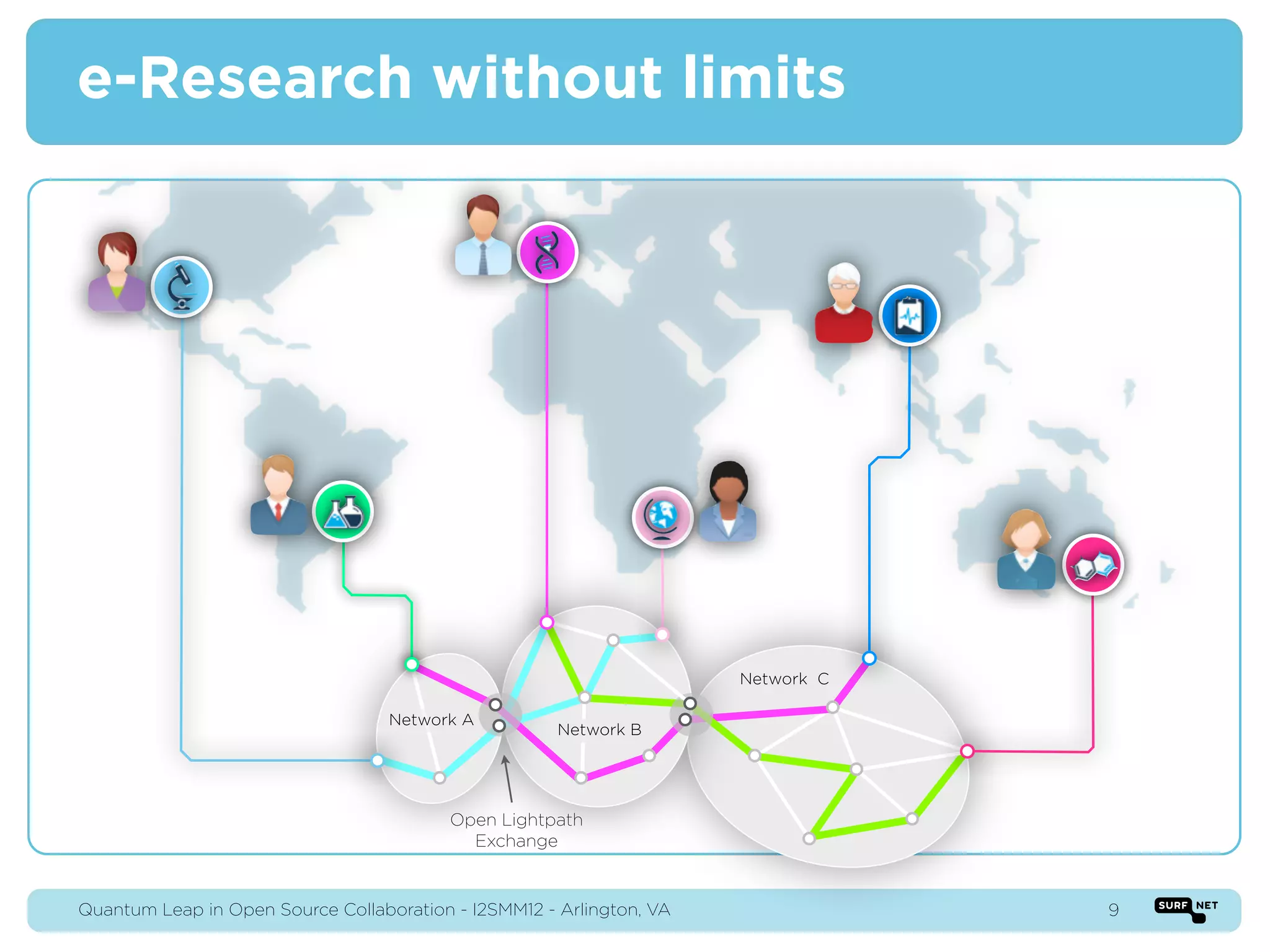
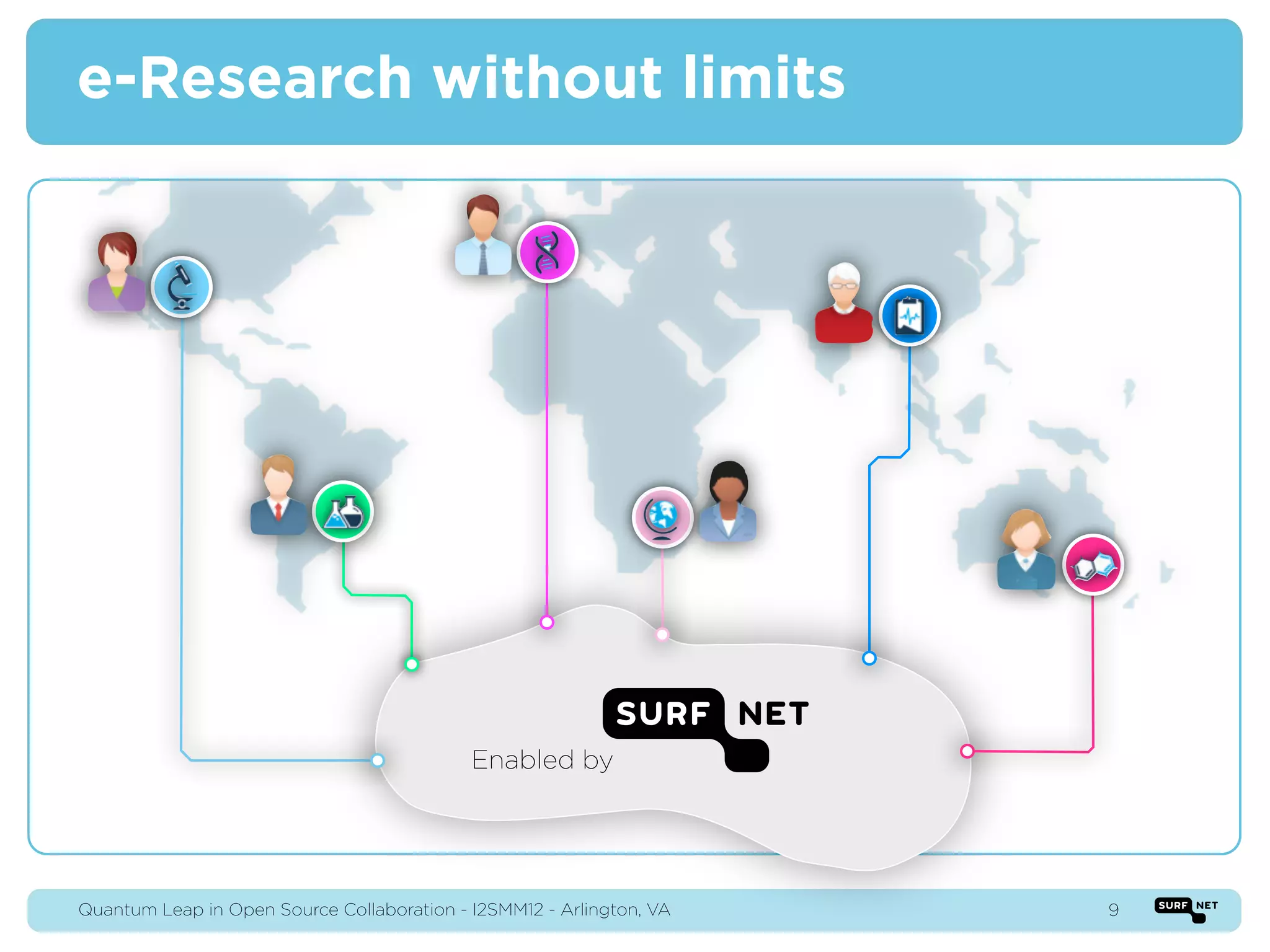
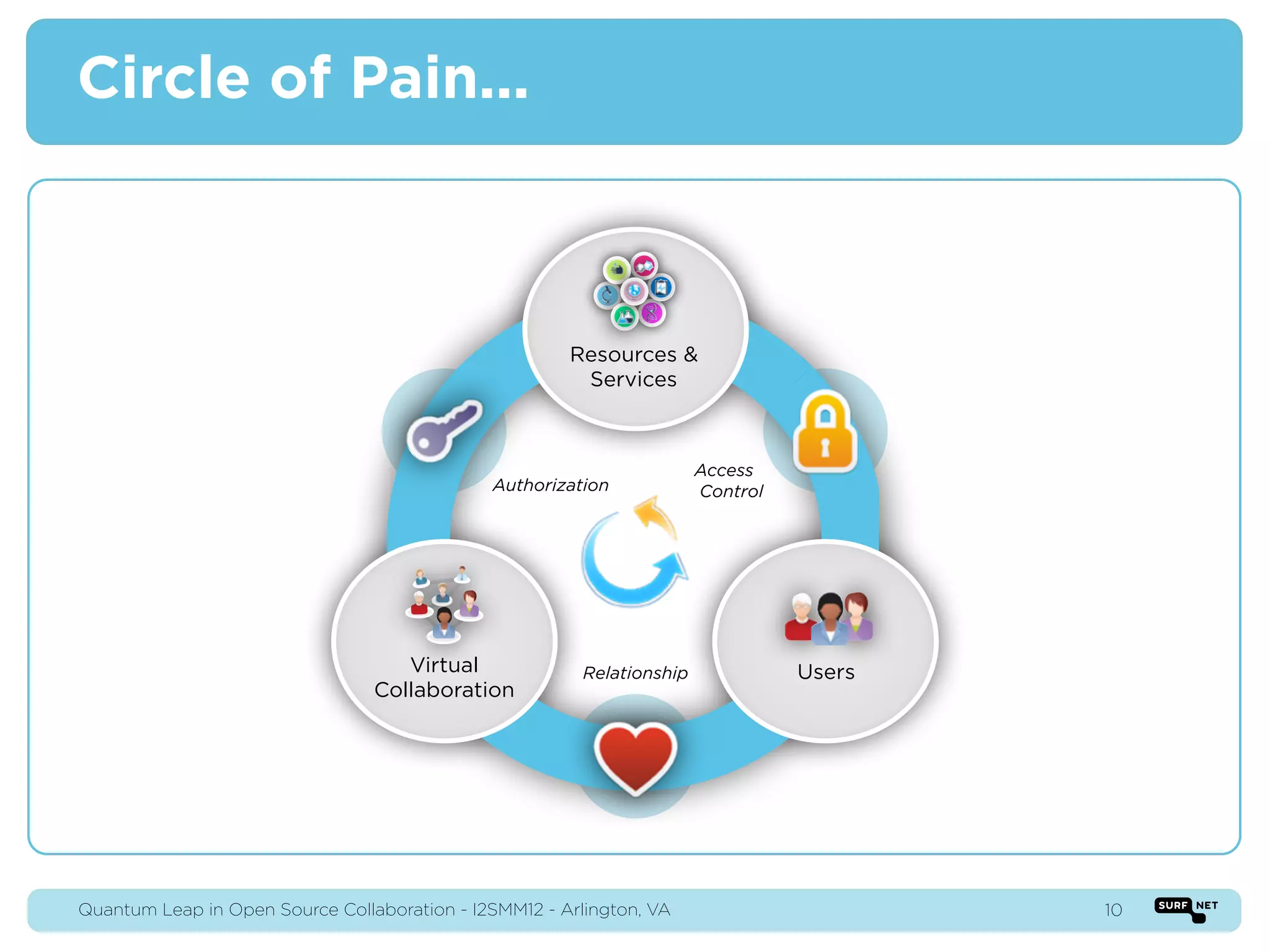
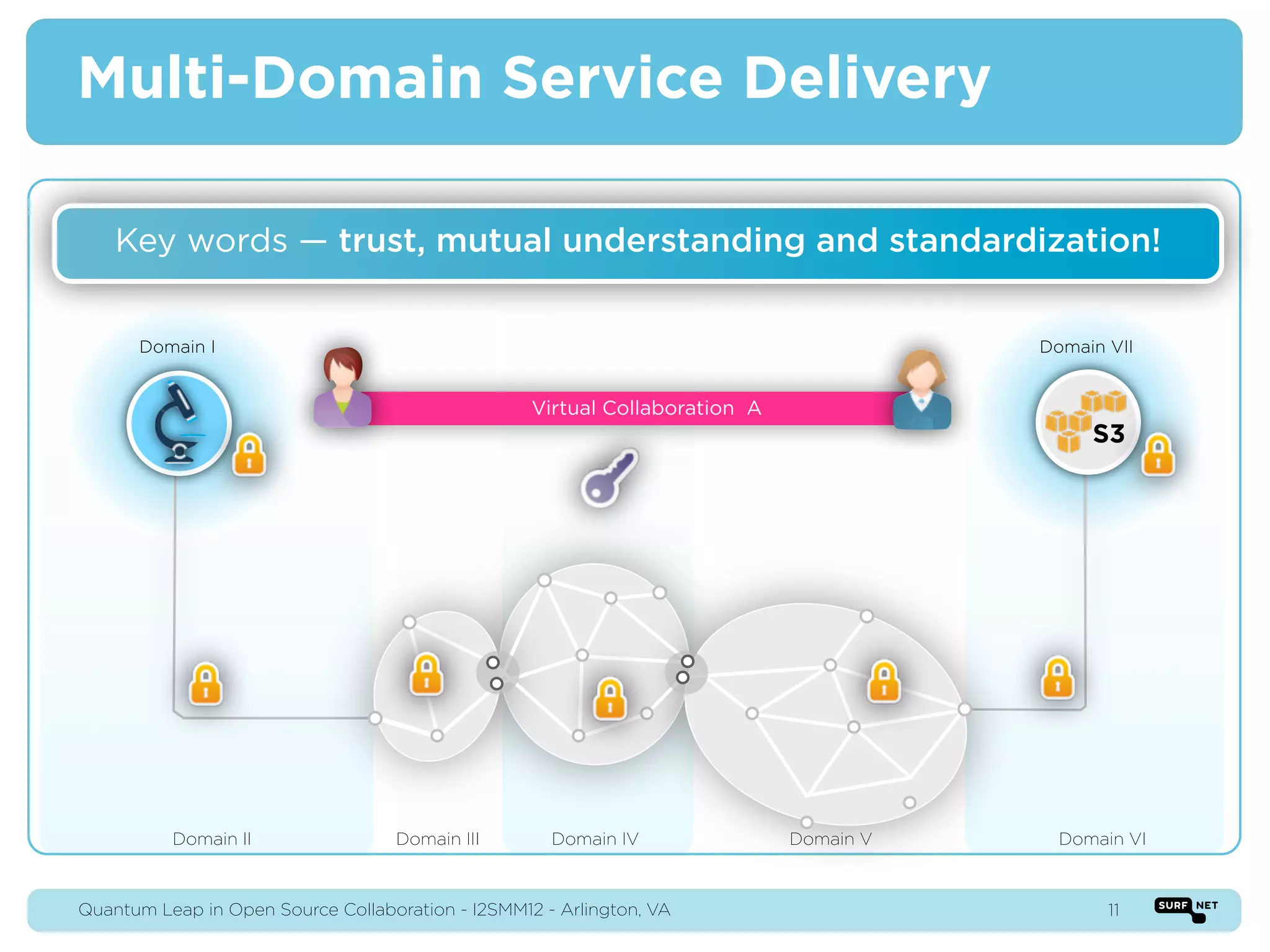
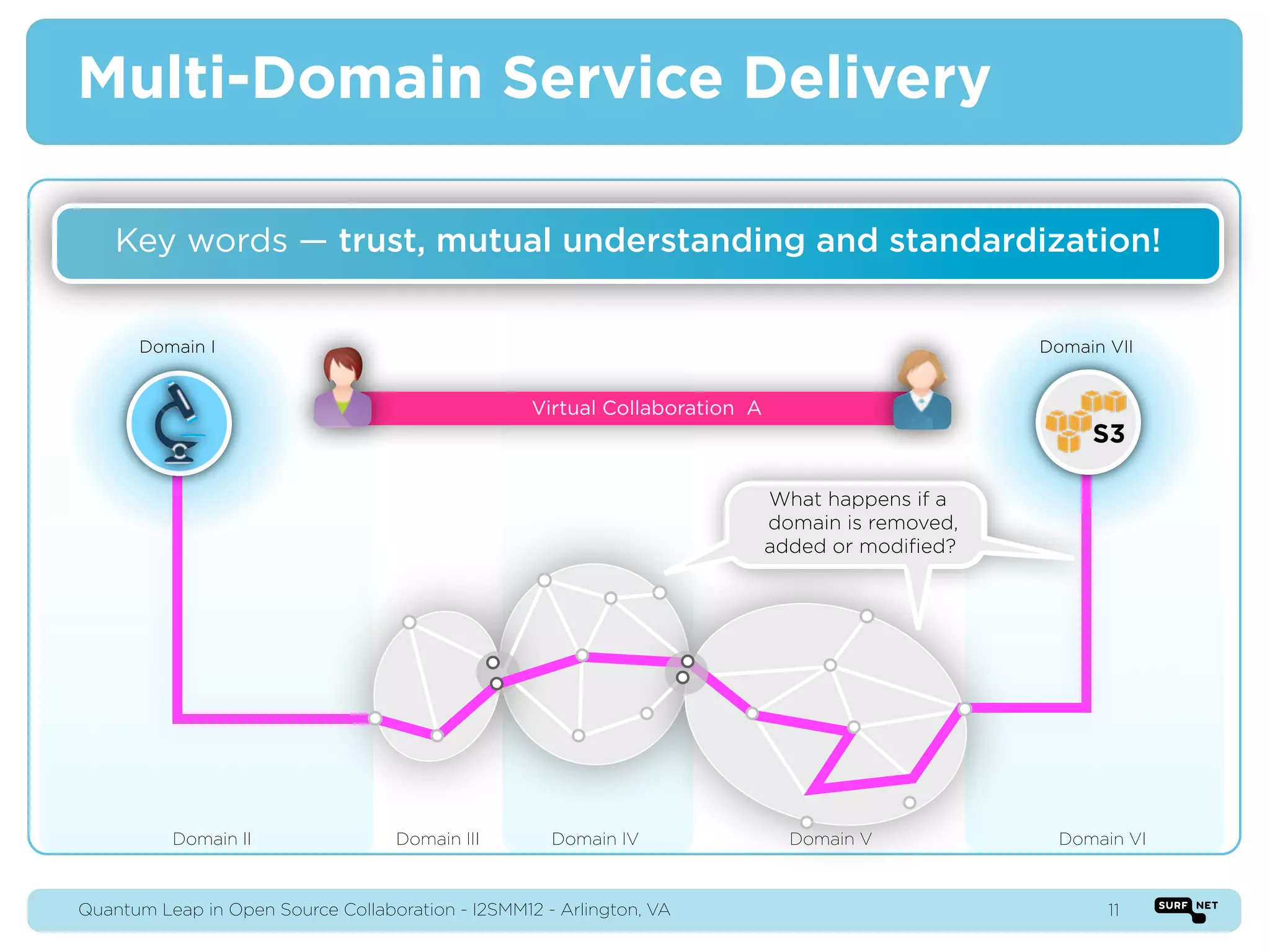
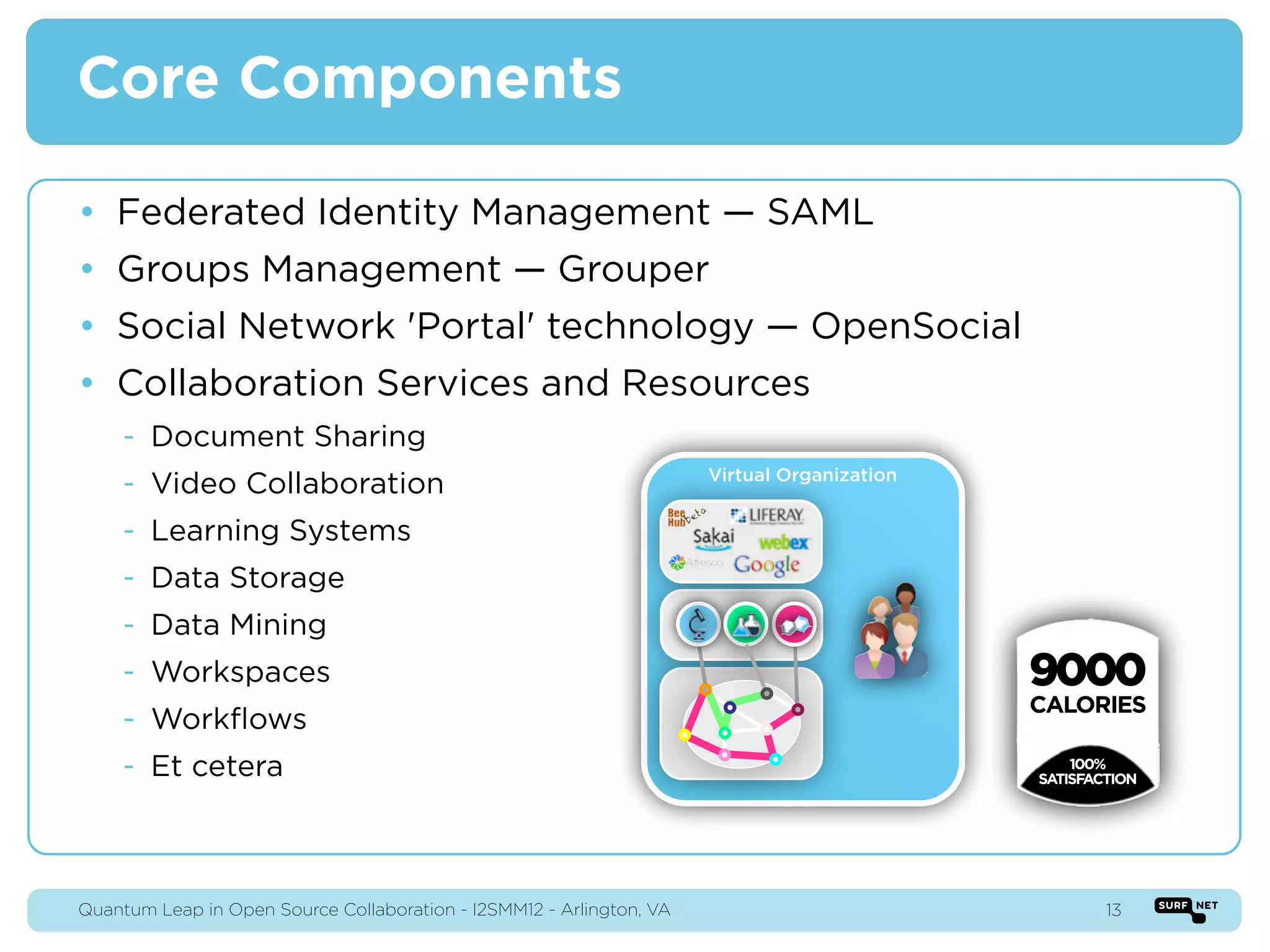
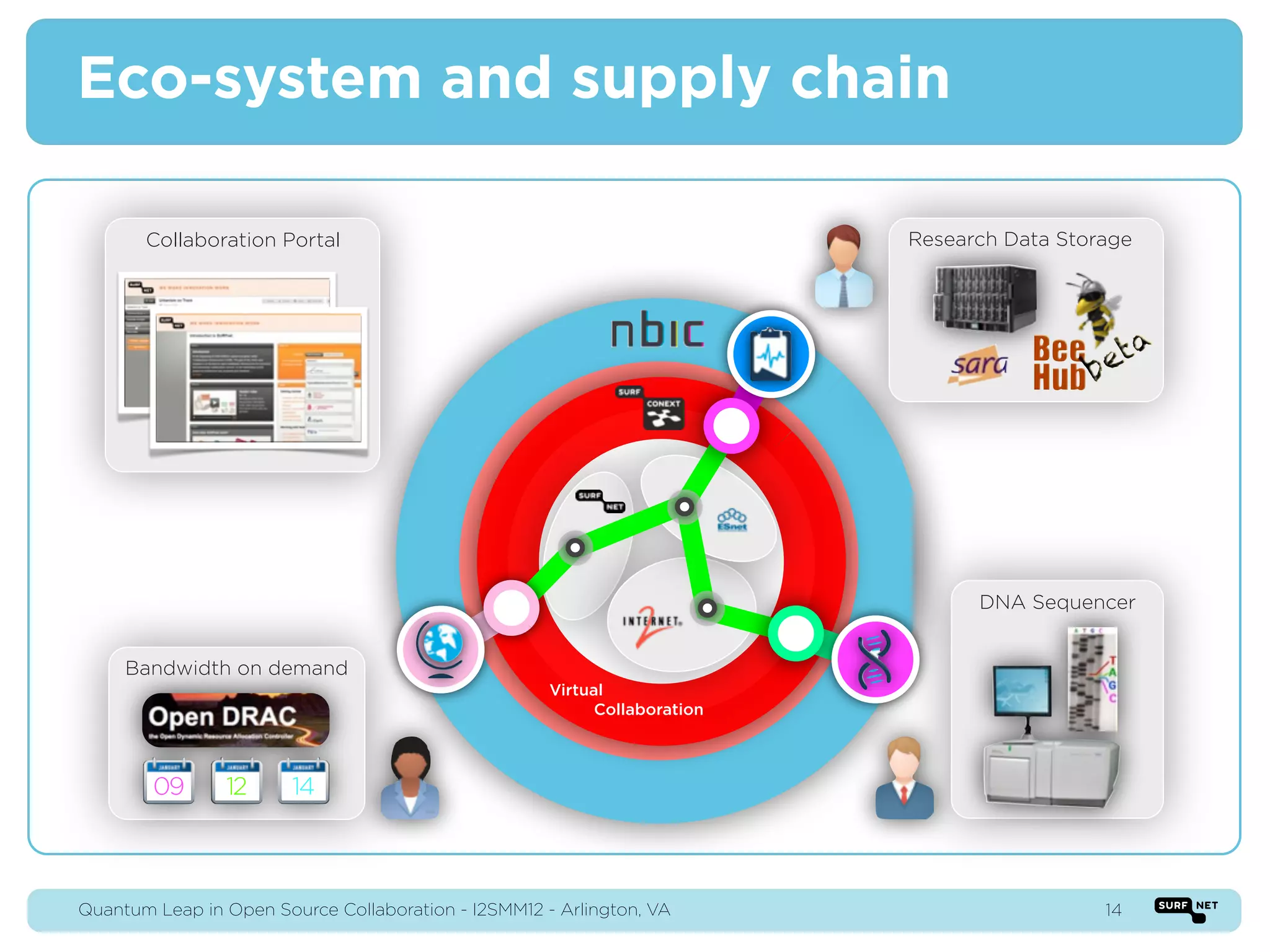
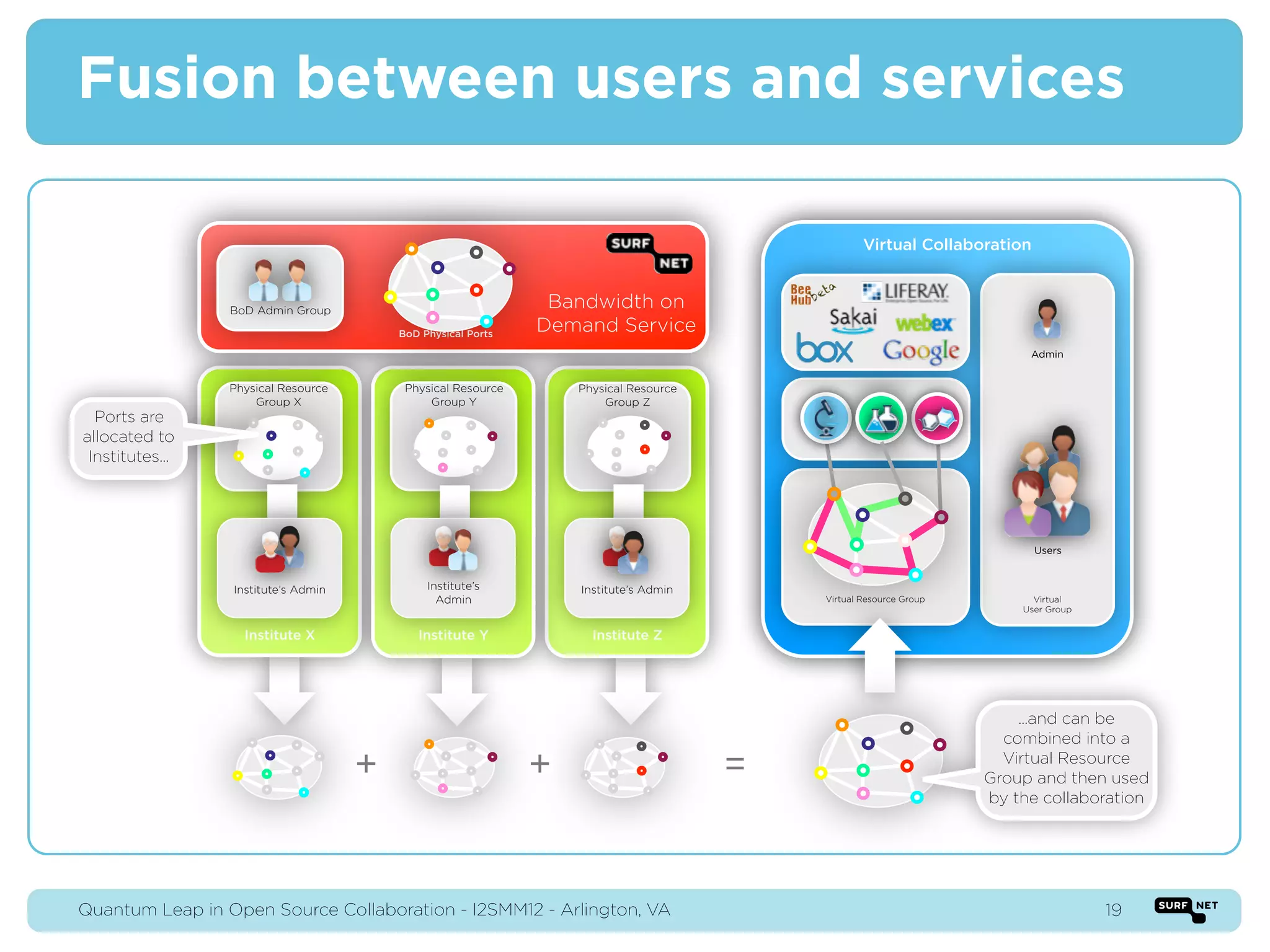
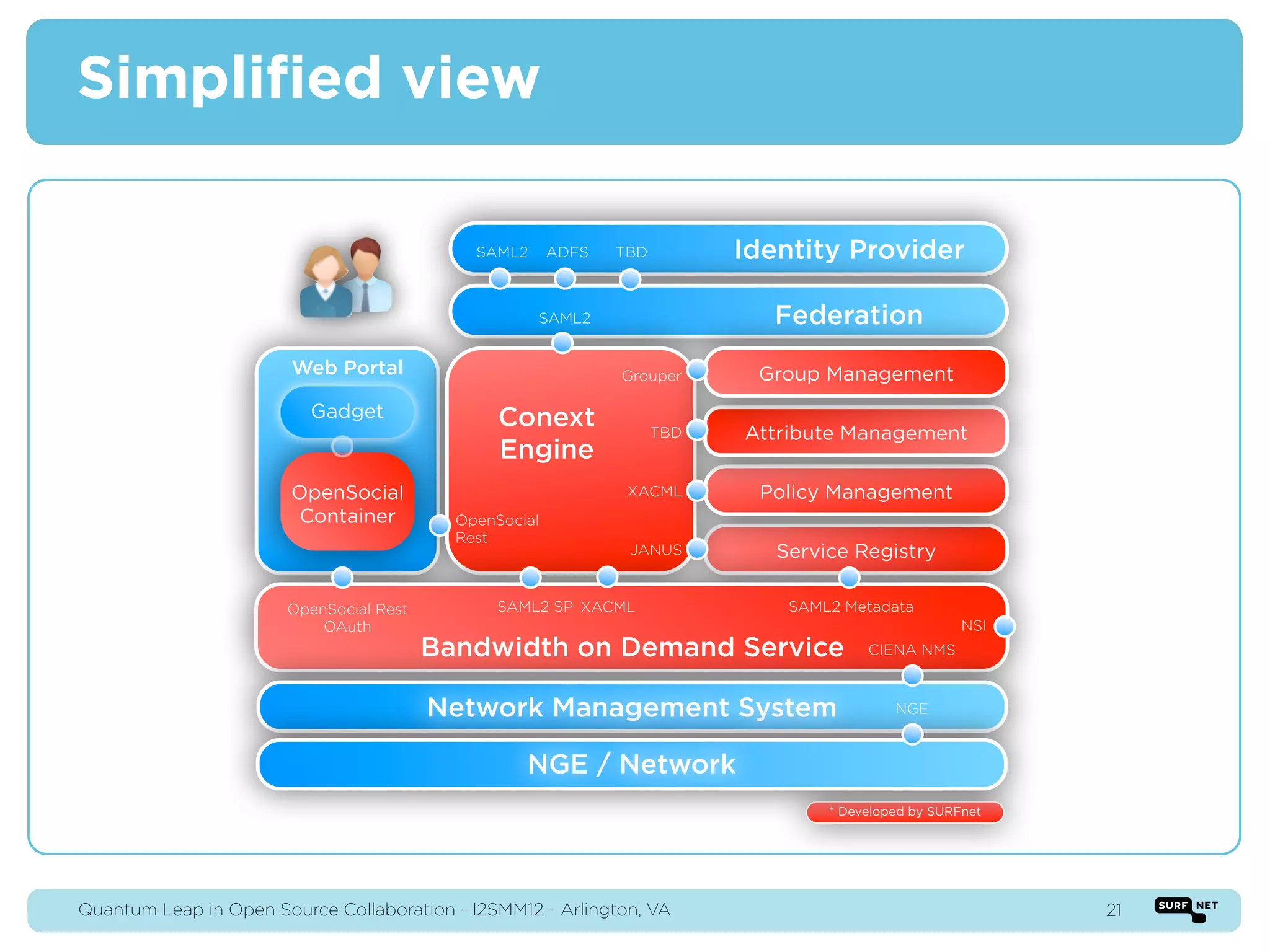
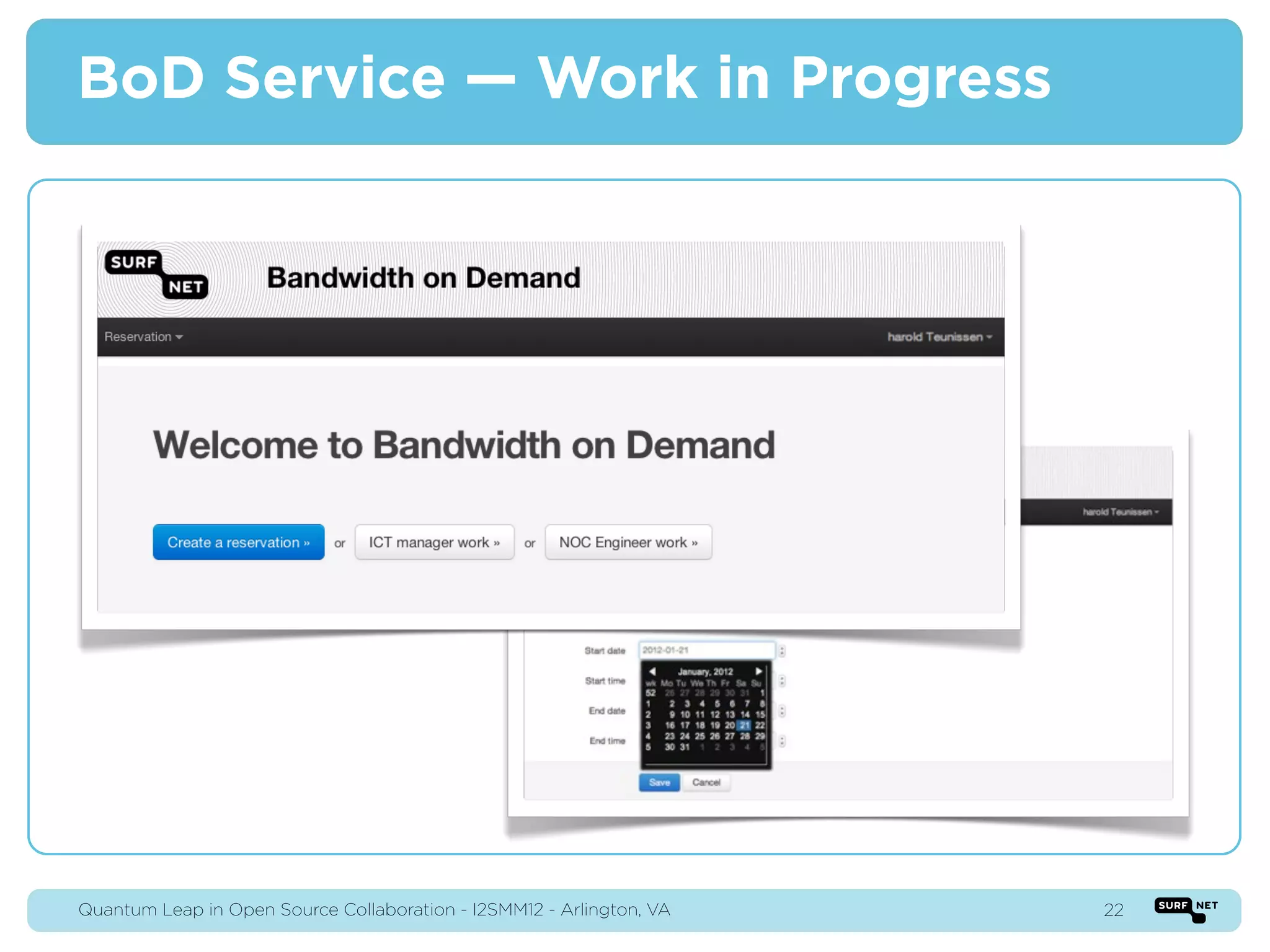
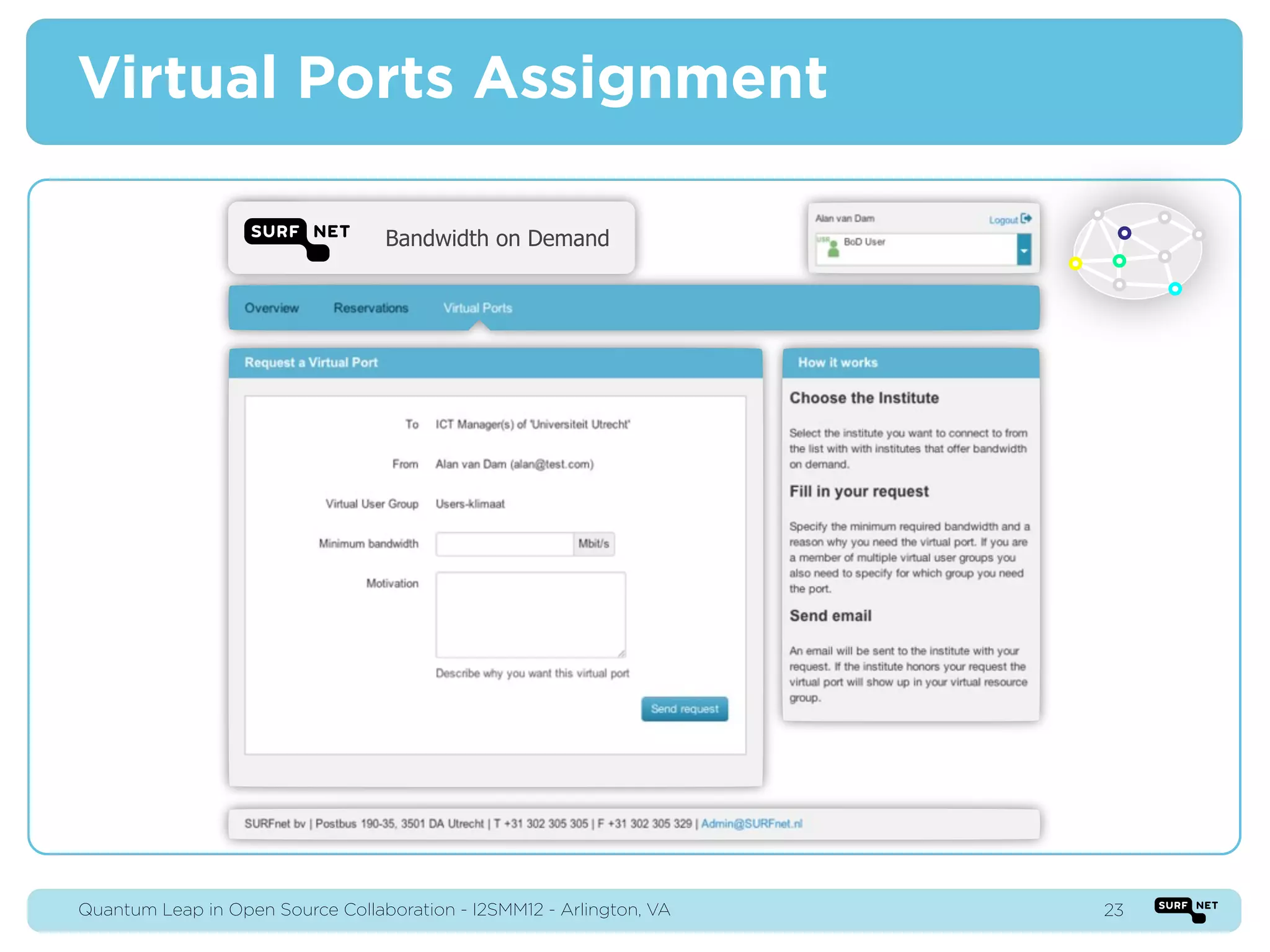
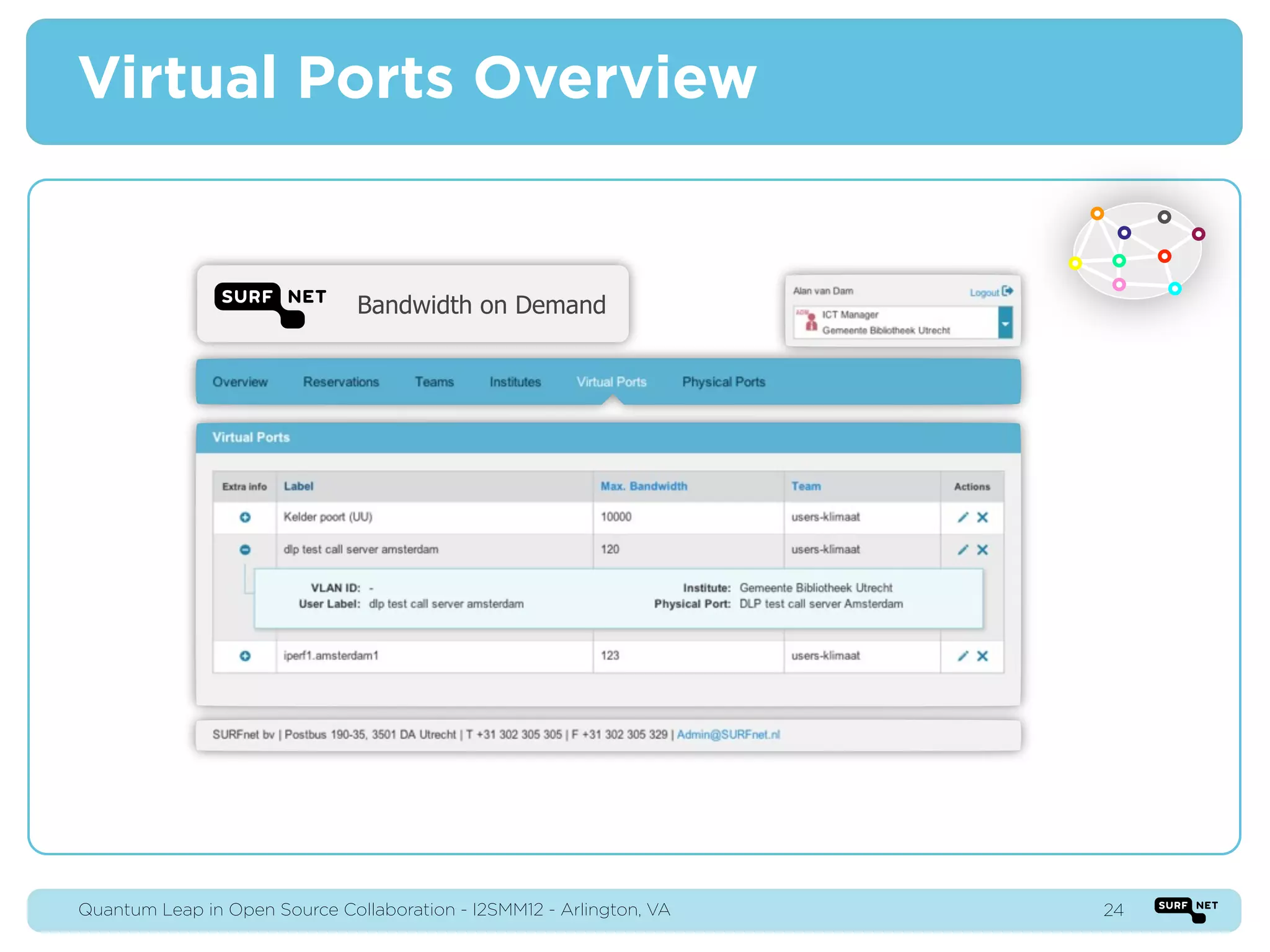
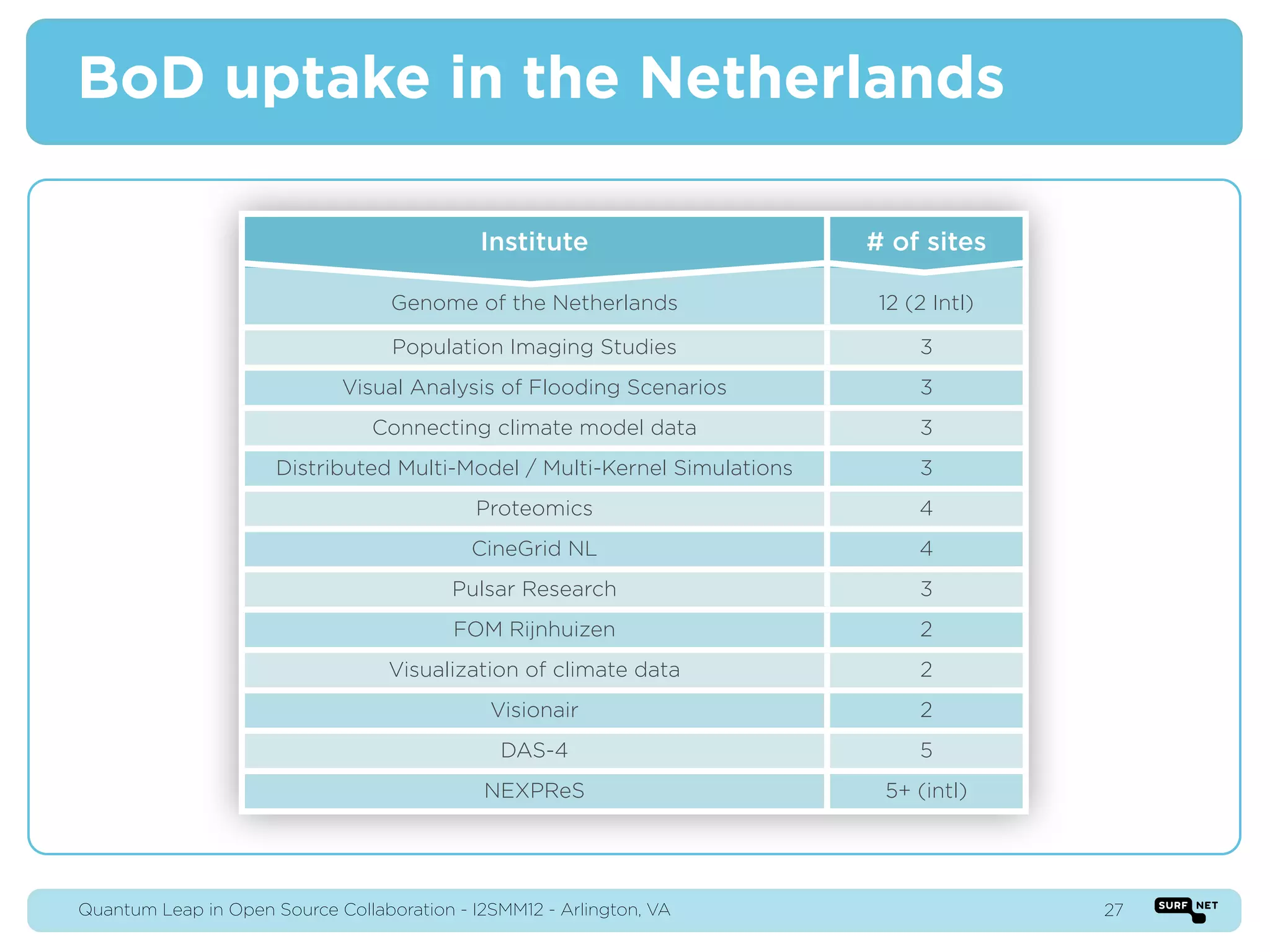
This document discusses open source collaboration and quantum leaps in research infrastructure. It describes how a national research and education network in the Netherlands brings together campus infrastructures to support large-scale, collaborative research projects requiring high-bandwidth networks and shared resources. Examples of multi-disciplinary projects are provided, and it outlines how open source tools can provide identity management, groups management, and other services to enable virtual collaboration across domains.