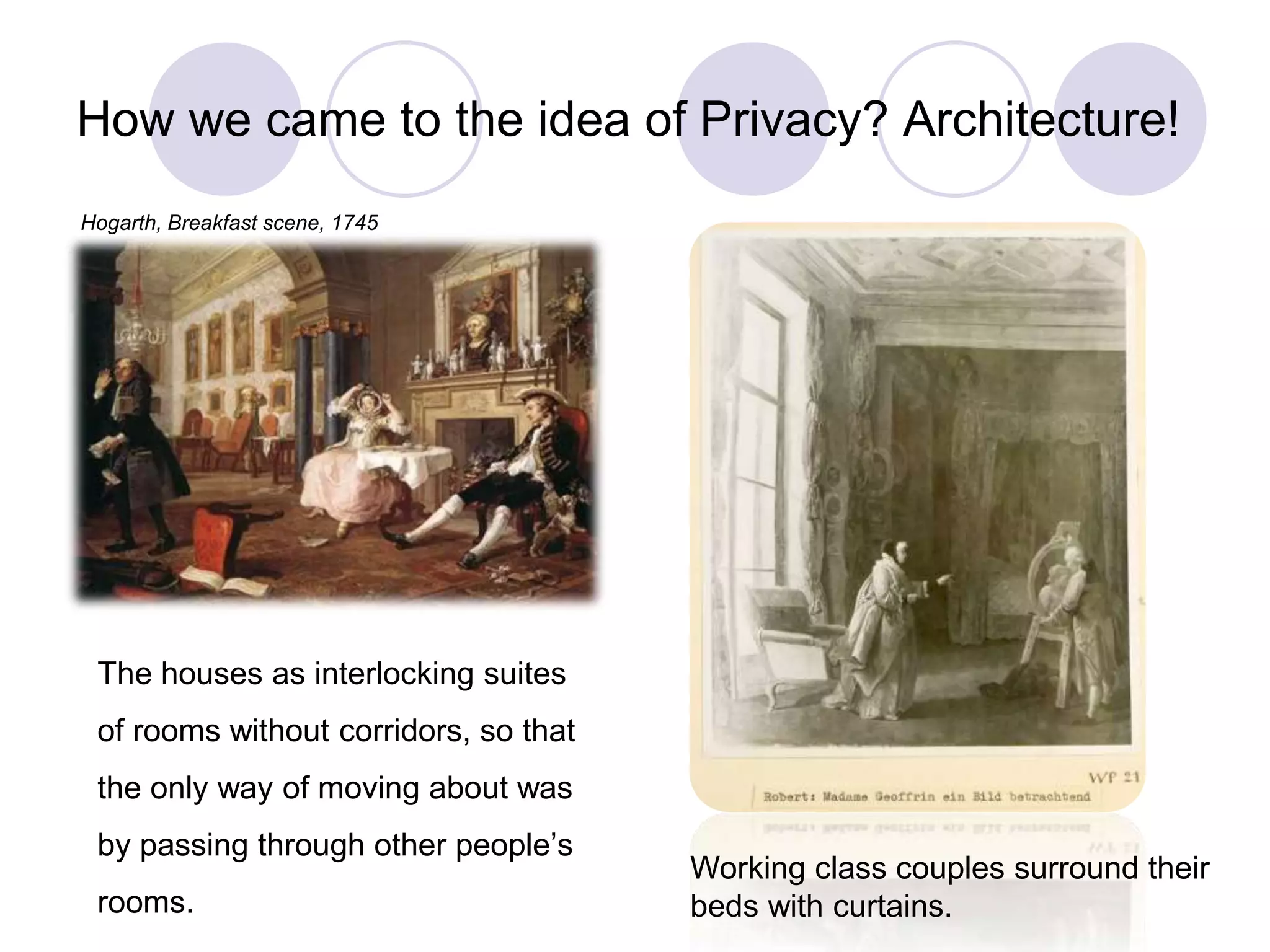
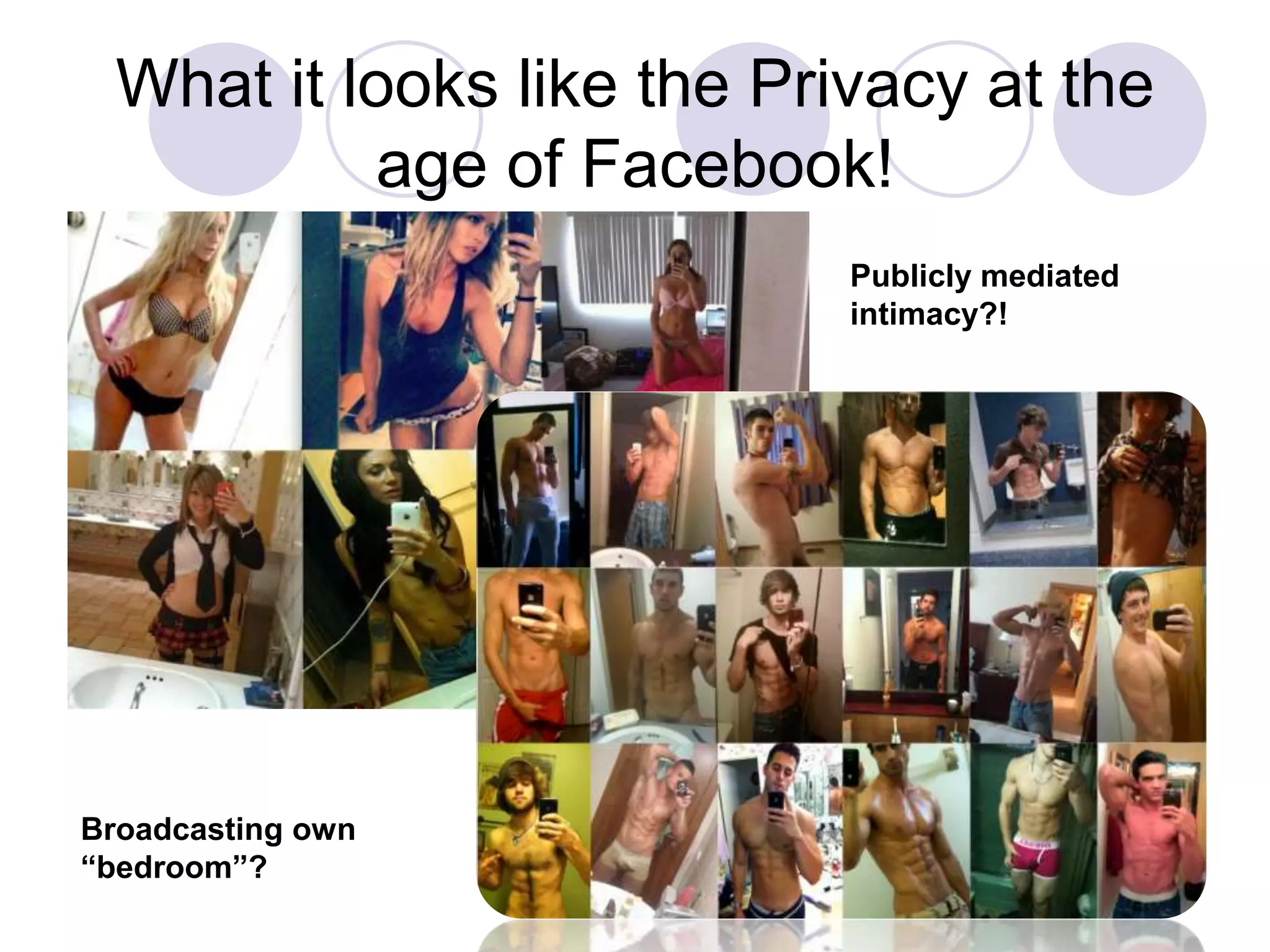
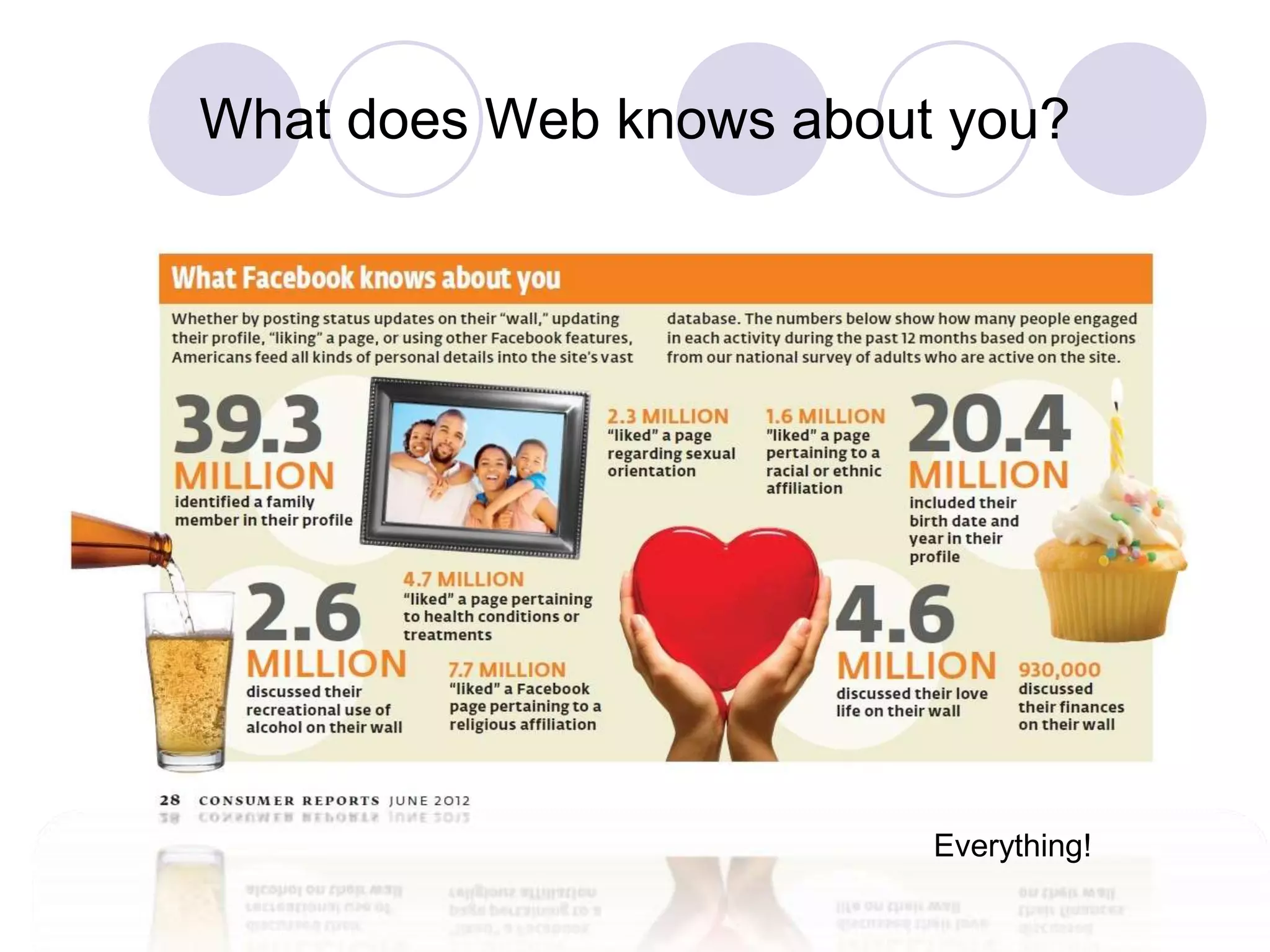
The document explores the concept of privacy as an essential aspect of individuality and personal control in social interactions. It discusses the evolution of privacy, its significance in contemporary society, especially in the context of social media, and the potential consequences of compromising privacy. The author encourages readers to reflect on their online self-presentation and the implications of their digital footprint.