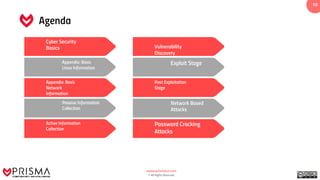
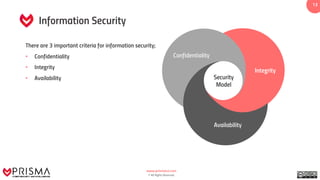
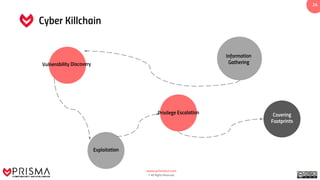
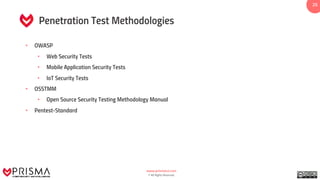
This document provides an overview of PRISMA, a cyber security consultancy firm. It discusses PRISMA's penetration testing and training services. It also covers topics related to penetration testing like methodologies, career paths in cyber security, and certifications. The document is intended to introduce PRISMA's services and activities to potential clients or training participants.