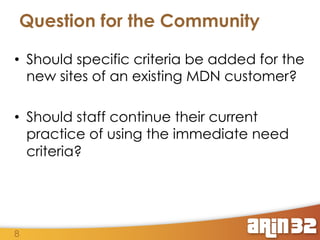
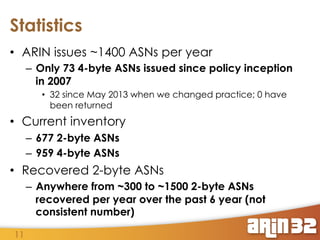
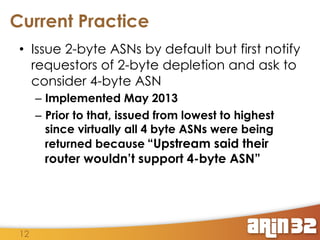
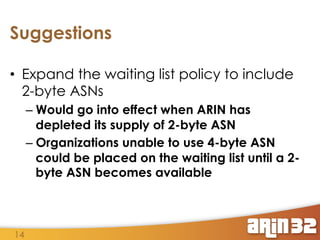
The document outlines recent policy implementations and reviews concerning IPv6 allocations and ASN assignments by ARIN. It discusses criteria for allocating additional Internet address registrations, identifies gaps in existing policies, and raises community questions regarding practices for new site qualifications and ASN allocations. The report also highlights the depletion of 2-byte ASNs and proposes changes for issuing ASNs to better align with other RIRs.