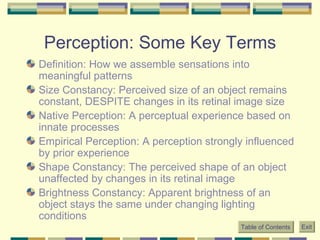
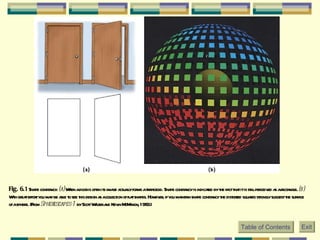
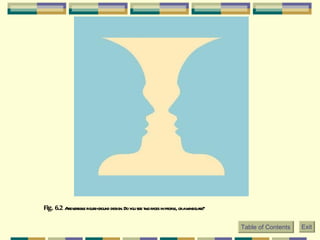
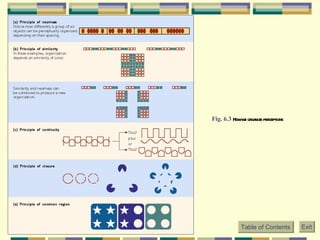
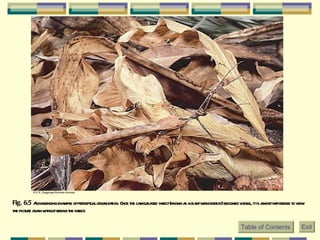
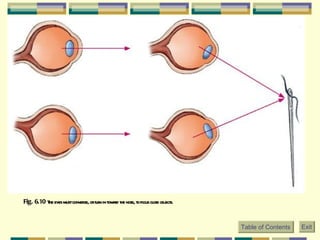
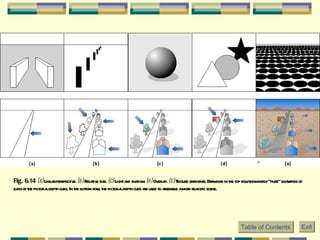
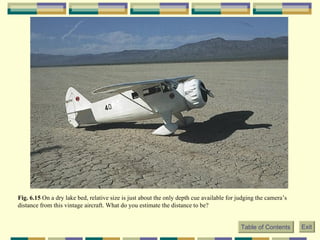
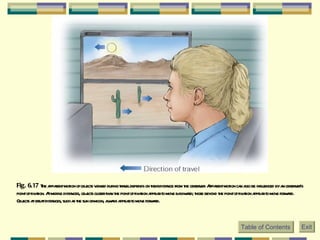
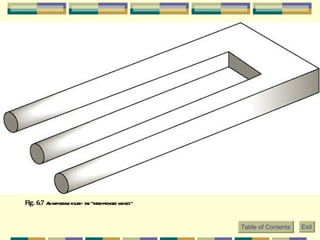
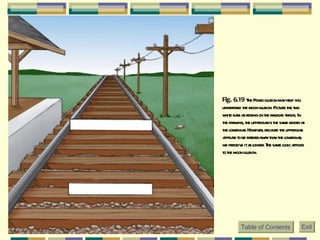
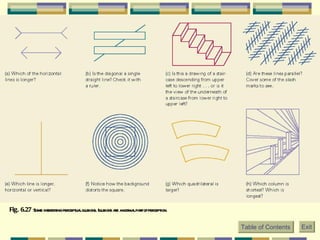
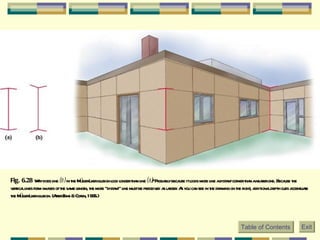
The document discusses key concepts in perception including size constancy, shape constancy, brightness constancy, and figure-ground organization. It also covers Gestalt principles of perceptual organization such as similarity, continuity, and closure. Depth perception is discussed including monocular and binocular cues like linear perspective, overlap, and motion parallax. Common illusions are also described such as the moon illusion and Muller-Lyer illusion.