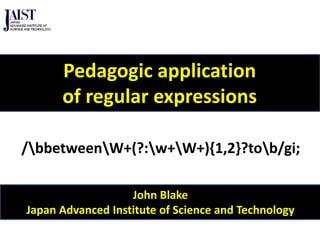
Pedagogic application of regular expressions
•Download as PPTX, PDF•
1 like•559 views
Using regular expressions in online langage learning tools to enable learners to identify particular features and provide feedback on the features as necessary, e.g. find errors and provide suggestions on how to rewrite them
Report
Share
Report
Share
Recommended
Regular expressions for JavaScript

This document discusses regular expressions (regex) for pattern matching in text. It covers introductory examples of using regex for tasks like error detection. It then explains probabilistic parsing, rule-based pattern matching, and regex in more detail. Examples are provided for using regex to match parts of speech, proofread text for grammatical errors, and annotate text for pronunciation.
Arabic spell checkers

This document outlines several papers on Arabic spell checking techniques. It discusses approaches that use morphological analysis, edit distance, and knowledge bases to detect and correct spelling errors in Arabic text. The techniques detect ill-formed words, semantically incorrect words, missing, incorrect, or extra letters. Evaluations show the approaches achieve over 80% recall and 90% precision on error detection and correction. Later papers propose full spell checking systems but do not report experimental results.
Total oop in c# dot net

The document discusses object-oriented programming concepts like classes, objects, methods, properties, inheritance, and polymorphism. It provides examples of different OOP concepts in C# like class definitions, object creation, method overloading, and inheritance hierarchies. The key topics covered include defining classes with data members and methods, creating objects from classes, using inheritance to extend classes, and implementing polymorphism through method overloading and overriding.
Arabic spell checking approaches

The document discusses several approaches to Arabic spell checking. It begins by outlining common Arabic spelling errors and then summarizes seven different approaches: 1) a stochastic approach focusing on space insertions and deletions, 2) a Prolog-based approach detecting errors and offering corrections, 3) an approach using n-gram scores and a matrix method, 4) generating an Arabic word list for error detection and language modeling, 5) a system with error detection and correction components using a dictionary and error model, 6) improving this system by enhancing the dictionary and candidate generation, and 7) concluding that the results are promising but there is still room for improvement.
oop Lecture 7

This document discusses object-oriented programming (OOP) and the need for OOP. It describes the limitations of procedural languages, including unrestricted access to global data and a poor model of real-world objects. OOP combines data and functions into objects, addressing these issues. Key characteristics of OOP include objects, classes, inheritance, and reusability. Classes can be derived from existing classes without modifying them, allowing code to be reused.
Java unit 2

This document discusses naming conventions and data types in Java. It provides guidelines for naming classes, methods, variables and packages using camel case and other conventions. It also describes the different primitive and non-primitive data types in Java like integer, floating point, character, boolean, and object reference types. Local, instance, and static variables are explained. The document also covers the different types of literals in Java including integer, floating point, character, string, and boolean literals.
SKILLWISE - OOPS CONCEPT

This document provides an overview of object-oriented programming (OOP) concepts including classes, objects, encapsulation, inheritance, polymorphism, and relationships between objects. It compares OOP to structured programming and outlines the benefits of OOP such as reusability, extensibility, and maintainability. Key OOP features like encapsulation, inheritance, polymorphism, and relationships are explained in detail. The document also introduces the Unified Modeling Language (UML) as a standard language for visualizing and modeling software systems using OOP concepts.
What is pattern recognition (lecture 3 of 6)

In this series I intend to simplify a beautiful branch of computer science that we as humans use it in everyday life without knowing. Pattern recognition is a sub-branch of the computer vision research and is tightly related to digital signal processing research as well as machine learning and artificial intelligence.
Recommended
Regular expressions for JavaScript

This document discusses regular expressions (regex) for pattern matching in text. It covers introductory examples of using regex for tasks like error detection. It then explains probabilistic parsing, rule-based pattern matching, and regex in more detail. Examples are provided for using regex to match parts of speech, proofread text for grammatical errors, and annotate text for pronunciation.
Arabic spell checkers

This document outlines several papers on Arabic spell checking techniques. It discusses approaches that use morphological analysis, edit distance, and knowledge bases to detect and correct spelling errors in Arabic text. The techniques detect ill-formed words, semantically incorrect words, missing, incorrect, or extra letters. Evaluations show the approaches achieve over 80% recall and 90% precision on error detection and correction. Later papers propose full spell checking systems but do not report experimental results.
Total oop in c# dot net

The document discusses object-oriented programming concepts like classes, objects, methods, properties, inheritance, and polymorphism. It provides examples of different OOP concepts in C# like class definitions, object creation, method overloading, and inheritance hierarchies. The key topics covered include defining classes with data members and methods, creating objects from classes, using inheritance to extend classes, and implementing polymorphism through method overloading and overriding.
Arabic spell checking approaches

The document discusses several approaches to Arabic spell checking. It begins by outlining common Arabic spelling errors and then summarizes seven different approaches: 1) a stochastic approach focusing on space insertions and deletions, 2) a Prolog-based approach detecting errors and offering corrections, 3) an approach using n-gram scores and a matrix method, 4) generating an Arabic word list for error detection and language modeling, 5) a system with error detection and correction components using a dictionary and error model, 6) improving this system by enhancing the dictionary and candidate generation, and 7) concluding that the results are promising but there is still room for improvement.
oop Lecture 7

This document discusses object-oriented programming (OOP) and the need for OOP. It describes the limitations of procedural languages, including unrestricted access to global data and a poor model of real-world objects. OOP combines data and functions into objects, addressing these issues. Key characteristics of OOP include objects, classes, inheritance, and reusability. Classes can be derived from existing classes without modifying them, allowing code to be reused.
Java unit 2

This document discusses naming conventions and data types in Java. It provides guidelines for naming classes, methods, variables and packages using camel case and other conventions. It also describes the different primitive and non-primitive data types in Java like integer, floating point, character, boolean, and object reference types. Local, instance, and static variables are explained. The document also covers the different types of literals in Java including integer, floating point, character, string, and boolean literals.
SKILLWISE - OOPS CONCEPT

This document provides an overview of object-oriented programming (OOP) concepts including classes, objects, encapsulation, inheritance, polymorphism, and relationships between objects. It compares OOP to structured programming and outlines the benefits of OOP such as reusability, extensibility, and maintainability. Key OOP features like encapsulation, inheritance, polymorphism, and relationships are explained in detail. The document also introduces the Unified Modeling Language (UML) as a standard language for visualizing and modeling software systems using OOP concepts.
What is pattern recognition (lecture 3 of 6)

In this series I intend to simplify a beautiful branch of computer science that we as humans use it in everyday life without knowing. Pattern recognition is a sub-branch of the computer vision research and is tightly related to digital signal processing research as well as machine learning and artificial intelligence.
Top 5 Reasons European companies keep outsourcing IT services

Many politicians have fought the outsourcing of services and manufacturing. Furthermore, unemployment is high in the Western world, especially in Europe. Still IT services outsourcing and BPO represent a US$ 952 billion market. And it keeps growing. Why?
This 16-page document gives a (very) high-level overview of the top 5 reasons pushing companies especially in Europe to keep outsourcing.
What do you think - is it good, bad, just a natural consequence of globalization?
Feel free to react and share your thoughts.
Fundraising by facebook app

This document provides instructions for setting up a Money Bomb fundraising tool using three payment options: offline mode which is free, direct credit card/piggy bank purchase, or deducting the fee from funds raised. It outlines how to brand, preview, and activate the Money Bomb widget by agreeing to a $295 fee deduction. Admins can then copy the script to websites or install the Money Bomb app on their organization's Facebook page to begin fundraising.
Años 80´s

Los años 60 fueron la década dorada del rock and roll, con géneros como el rock británico y el soul estadounidense alcanzando gran popularidad. Grupos emblemáticos como The Beatles, The Rolling Stones y Motown Records revolucionaron la música y cultura de la época. El rock se expandió a nivel mundial a través de festivales musicales y nuevos subgéneros surgieron tanto en Europa como en América del Norte.
Primera guerra-mundial 

Este documento resume los antecedentes y desarrollo de la Primera Guerra Mundial, incluyendo las alianzas previas entre las potencias europeas, los frentes de batalla en el este y el oeste, el uso de submarinos por Alemania, la tregua de Navidad de 1914 entre soldados británicos y alemanes en las trincheras, y la Revolución Rusa de 1917 que sacó a Rusia de la guerra.
MediaWhiz POV: Conversion Optimization for Lead-gen Paths

MediaWhiz SVP Jeremy Leonard details conversion optimization for lead-gen paths. At a presentation given at Conversion Conference Oct. 9, 2012, in Fort Lauderdale, Fla., Leonard explains how digital and performance marketers can generate efficient and cost-effective conversions with an eye toward quality and sustainability.
Open project 2011

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise causes chemical changes in the brain that may help boost feelings of calmness, happiness and focus.
Materials design presentation 01 (2)

This document outlines a materials design for a political science reading comprehension course. It discusses selecting a text about the origins and evolution of democracy from MIT open courseware. The text is elaborated to make it clearer and more explicit. Pre-reading, while-reading, and post-reading activities are proposed to help students build background knowledge, understand the macrostructure and microstructure, and continue discussion. The materials aim to tap into students' knowledge, lead to discussion, and foster curiosity to read more.
51 ways to reduce your out-of-class marking

John Blake from the Japan Advanced Institute of Science and Technology presented 51 strategies for reducing time spent on marking student assignments. The strategies are divided into operational, quality control, feedback, and avoidance categories. Some examples include having students submit assignments in pairs or groups, using strict word limits, providing assignment templates and models, checking work in class, using technology like track changes and comment functions, investing time upfront to create reusable feedback materials, and attempting to avoid marking assignments whenever possible. The overall goal is to streamline the marking process and provide feedback to students in a more efficient manner.
Pune OpenCoffee Club, an Introduction (2014)

Since 2008, the Pune OpenCoffee Club has been bringing startup founders together through events and community. Here's a short introduction to our activities and an invitation to get involved.
Winning - I am not designed to finish 2nd or 3rd

How to achieve your goals and objectives. Look at the year as 12 sections and approach every one with the same amount of enthusiasm and effort to achieve your sales targets and goals
Guia 02....

El documento proporciona instrucciones en 4 pasos para personalizar la barra de tareas en Windows: 1) agregar 5 accesos directos fijos, 2) cambiar la configuración de hora y fecha, 3) abrir 10 documentos de Word para ver el agrupamiento, y 4) ampliar el tamaño de los iconos.
On Target eCommerce

My presentation deck for On Target eCommerce. Originally created for my presentation at APOE in Wuhu, China on August, 2012.
Waterloo some modern lessons

This blog post discusses the importance of having a clear strategy and plan, as exemplified by the Battle of Waterloo. It notes that both Wellington and Napoleon had strategies for the battle, but Napoleon lost because he stayed behind the lines and was not aware of how the battle was unfolding, unlike Wellington who remained with his soldiers. The post stresses that for businesses to succeed, they need an appropriate plan or strategy to guide the team's actions, just as Wellington knew each soldier's role in achieving the overall strategy through his plan. It concludes by drawing a parallel to instruction manuals, emphasizing the importance of having a plan and revising it regularly to achieve goals.
Corporate social responsibility 

Corporate social responsibility (CSR) involves self-regulation by businesses to integrate social and environmental concerns into their operations and interactions with stakeholders. CSR participants include owners, shareholders, and local governments. CSR aims to balance economic, ecological, and social impacts as a way to profit businesses, compensate for state inefficiencies, and remedy violations of natural rights through continuous reputation-building activities. Businesses take different approaches to organizing CSR such as independent programs, own funds, or solutions developed through collaboration.
Minimal Introduction to C++ - Part II

This document provides an introduction to object-oriented programming concepts in C++ including classes, attributes, methods, constructors, destructors, operators, and access modifiers. It also lists some example problems solved in C++ using these concepts like classes for messages, circles, and machine epsilon. Exercises proposed include creating classes for spheres and counting triangles from random point data.
Determining The Barriers Faced By Novice Programmers

Most of the novice programmers find glitches at various phases while trying to complete a program in their Computer Science programming course. These phases can be while constructing the code, finding errors in the code at the time of compilation of the program, debugging these errors while executing the program. Novice programmers are unable to understand some of the concepts in programming. Computer Science programming course instructors are experiencing difficulty in finding these barriers faced by the students. These barriers are forcing students to drop programming course from their degree plan and becoming a concern to the professors teaching programming course. In this research ActivePresenter software is used. This software recorded the full motion video with crystal clear quality and helped in capturing screen shots automatically with a click of a mouse or pressing any key in the keyboard of the students who are trying to complete a programming assignment. By analyzing all the recordings collected from different students, these barriers are determined.
FLOSS Pilot Studies

This document describes a pilot study conducted to involve software engineering students in free and open source software (F/OSS) projects. The study implemented a F/OSS teaching and learning framework where students tested F/OSS projects over 12 weeks. Students found and reported bugs, and presented their testing activities. Student participation was evaluated using statistical analysis of testing data and online surveys. The framework provided students with practical software testing experience but had some challenges around specialization, collaboration, and evaluation. Lessons learned include benefits of flexible schedules and learning opportunities, as well as difficulties with communication and project management.
More Related Content
Viewers also liked
Top 5 Reasons European companies keep outsourcing IT services

Many politicians have fought the outsourcing of services and manufacturing. Furthermore, unemployment is high in the Western world, especially in Europe. Still IT services outsourcing and BPO represent a US$ 952 billion market. And it keeps growing. Why?
This 16-page document gives a (very) high-level overview of the top 5 reasons pushing companies especially in Europe to keep outsourcing.
What do you think - is it good, bad, just a natural consequence of globalization?
Feel free to react and share your thoughts.
Fundraising by facebook app

This document provides instructions for setting up a Money Bomb fundraising tool using three payment options: offline mode which is free, direct credit card/piggy bank purchase, or deducting the fee from funds raised. It outlines how to brand, preview, and activate the Money Bomb widget by agreeing to a $295 fee deduction. Admins can then copy the script to websites or install the Money Bomb app on their organization's Facebook page to begin fundraising.
Años 80´s

Los años 60 fueron la década dorada del rock and roll, con géneros como el rock británico y el soul estadounidense alcanzando gran popularidad. Grupos emblemáticos como The Beatles, The Rolling Stones y Motown Records revolucionaron la música y cultura de la época. El rock se expandió a nivel mundial a través de festivales musicales y nuevos subgéneros surgieron tanto en Europa como en América del Norte.
Primera guerra-mundial 

Este documento resume los antecedentes y desarrollo de la Primera Guerra Mundial, incluyendo las alianzas previas entre las potencias europeas, los frentes de batalla en el este y el oeste, el uso de submarinos por Alemania, la tregua de Navidad de 1914 entre soldados británicos y alemanes en las trincheras, y la Revolución Rusa de 1917 que sacó a Rusia de la guerra.
MediaWhiz POV: Conversion Optimization for Lead-gen Paths

MediaWhiz SVP Jeremy Leonard details conversion optimization for lead-gen paths. At a presentation given at Conversion Conference Oct. 9, 2012, in Fort Lauderdale, Fla., Leonard explains how digital and performance marketers can generate efficient and cost-effective conversions with an eye toward quality and sustainability.
Open project 2011

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise causes chemical changes in the brain that may help boost feelings of calmness, happiness and focus.
Materials design presentation 01 (2)

This document outlines a materials design for a political science reading comprehension course. It discusses selecting a text about the origins and evolution of democracy from MIT open courseware. The text is elaborated to make it clearer and more explicit. Pre-reading, while-reading, and post-reading activities are proposed to help students build background knowledge, understand the macrostructure and microstructure, and continue discussion. The materials aim to tap into students' knowledge, lead to discussion, and foster curiosity to read more.
51 ways to reduce your out-of-class marking

John Blake from the Japan Advanced Institute of Science and Technology presented 51 strategies for reducing time spent on marking student assignments. The strategies are divided into operational, quality control, feedback, and avoidance categories. Some examples include having students submit assignments in pairs or groups, using strict word limits, providing assignment templates and models, checking work in class, using technology like track changes and comment functions, investing time upfront to create reusable feedback materials, and attempting to avoid marking assignments whenever possible. The overall goal is to streamline the marking process and provide feedback to students in a more efficient manner.
Pune OpenCoffee Club, an Introduction (2014)

Since 2008, the Pune OpenCoffee Club has been bringing startup founders together through events and community. Here's a short introduction to our activities and an invitation to get involved.
Winning - I am not designed to finish 2nd or 3rd

How to achieve your goals and objectives. Look at the year as 12 sections and approach every one with the same amount of enthusiasm and effort to achieve your sales targets and goals
Guia 02....

El documento proporciona instrucciones en 4 pasos para personalizar la barra de tareas en Windows: 1) agregar 5 accesos directos fijos, 2) cambiar la configuración de hora y fecha, 3) abrir 10 documentos de Word para ver el agrupamiento, y 4) ampliar el tamaño de los iconos.
On Target eCommerce

My presentation deck for On Target eCommerce. Originally created for my presentation at APOE in Wuhu, China on August, 2012.
Waterloo some modern lessons

This blog post discusses the importance of having a clear strategy and plan, as exemplified by the Battle of Waterloo. It notes that both Wellington and Napoleon had strategies for the battle, but Napoleon lost because he stayed behind the lines and was not aware of how the battle was unfolding, unlike Wellington who remained with his soldiers. The post stresses that for businesses to succeed, they need an appropriate plan or strategy to guide the team's actions, just as Wellington knew each soldier's role in achieving the overall strategy through his plan. It concludes by drawing a parallel to instruction manuals, emphasizing the importance of having a plan and revising it regularly to achieve goals.
Corporate social responsibility 

Corporate social responsibility (CSR) involves self-regulation by businesses to integrate social and environmental concerns into their operations and interactions with stakeholders. CSR participants include owners, shareholders, and local governments. CSR aims to balance economic, ecological, and social impacts as a way to profit businesses, compensate for state inefficiencies, and remedy violations of natural rights through continuous reputation-building activities. Businesses take different approaches to organizing CSR such as independent programs, own funds, or solutions developed through collaboration.
Viewers also liked (19)
Top 5 Reasons European companies keep outsourcing IT services

Top 5 Reasons European companies keep outsourcing IT services
MediaWhiz POV: Conversion Optimization for Lead-gen Paths

MediaWhiz POV: Conversion Optimization for Lead-gen Paths
Similar to Pedagogic application of regular expressions
Minimal Introduction to C++ - Part II

This document provides an introduction to object-oriented programming concepts in C++ including classes, attributes, methods, constructors, destructors, operators, and access modifiers. It also lists some example problems solved in C++ using these concepts like classes for messages, circles, and machine epsilon. Exercises proposed include creating classes for spheres and counting triangles from random point data.
Determining The Barriers Faced By Novice Programmers

Most of the novice programmers find glitches at various phases while trying to complete a program in their Computer Science programming course. These phases can be while constructing the code, finding errors in the code at the time of compilation of the program, debugging these errors while executing the program. Novice programmers are unable to understand some of the concepts in programming. Computer Science programming course instructors are experiencing difficulty in finding these barriers faced by the students. These barriers are forcing students to drop programming course from their degree plan and becoming a concern to the professors teaching programming course. In this research ActivePresenter software is used. This software recorded the full motion video with crystal clear quality and helped in capturing screen shots automatically with a click of a mouse or pressing any key in the keyboard of the students who are trying to complete a programming assignment. By analyzing all the recordings collected from different students, these barriers are determined.
FLOSS Pilot Studies

This document describes a pilot study conducted to involve software engineering students in free and open source software (F/OSS) projects. The study implemented a F/OSS teaching and learning framework where students tested F/OSS projects over 12 weeks. Students found and reported bugs, and presented their testing activities. Student participation was evaluated using statistical analysis of testing data and online surveys. The framework provided students with practical software testing experience but had some challenges around specialization, collaboration, and evaluation. Lessons learned include benefits of flexible schedules and learning opportunities, as well as difficulties with communication and project management.
ID Unit Report 3

The document describes plans to revise instruction on adding fractions with unlike denominators based on formative assessment results. Key revisions include:
1) Providing more opportunities for students to model and manipulate fractions into simplest form using concrete models and drawings before using the abstract process.
2) Giving targeted small group instruction to help students visualize how finding the greatest common factor simplifies a fraction.
3) Analyzing pre- and post-test results and practice problems to identify weaknesses and tailor remedial instruction accordingly.
Alapcae math activities 2014 ged test

This document provides an overview of math activities and resources for migrating to the Common Core Standards and College and Career Readiness Standards for Adult Education. It discusses the key differences between the Common Core State Standards, College and Career Readiness Standards for Alabama, and standards for adult education. The presentation then outlines various math activities that cover topics like fractions, geometry, functions, equations, and more. Resources for teachers and students are also listed.
Organization strategies to increase development productivity

Organization Strategies to Increase Development Productivity discusses how to increase productivity through a student worker program. It outlines how the speaker's team at Oakland University hired and trained student workers to take on development work. Key aspects included identifying mentors, varying work tasks, setting expectations, and involving students in open source contributions. When implemented well, the student program provides hands-on learning opportunities for students and additional development capacity for the organization. One student speaker discussed his positive experience in the program, where he gained real-world skills while having a flexible work schedule around his classes.
Biomes WebQuest

This web quest asks 10th grade biology students to research different North American biomes and recommend one for reintroducing the fictional species "SpatulaTankWhozit". Students gather data on temperature, rainfall, plants and characteristics of temperate grassland, forest, alpine and taiga biomes. They organize the data and learn about the species. Using facts from their research, students create a PowerPoint and written recommendation to the North American Species Reintroduction Society on which biome is best for the species.
WebQuest for Biomes

This document provides instructions for a web quest assignment on biomes for 10th grade biology students. Students are tasked with researching different biomes, organizing the data, learning about a fictional species, and making a recommendation on which biome to reintroduce the species. They will complete excel sheets, a PowerPoint presentation, and paragraphs justifying their conclusion. The assignment is designed to teach students about biomes and scientific processes like gathering evidence and drawing conclusions.
MLApproachToProgramming.ppt

Machine learning ppt
college presentation on Machine Learning Programming releated them. explain each and every Point in detail so. thats why they are easily to explain in the
Ml approach toprogramming

This document proposes a Machine Learning Approach to Programming (MLAP) where programs are aware of their own design and functionality. Each class in an object-oriented program would contain information about itself encoded as attributes. This would allow the program to learn from usage, fix errors autonomously using an explanation-based learning engine and knowledge base, and optimize based on user preferences to provide a better experience. The approach aims to speed up development and error fixing but may increase memory usage and costs. The project is still in the implementation stage.
Problem solving content

The document provides guidance on solving physics problems using a general 5-step strategy and the KUDOS method for word problems. It begins with an overview of the learning objectives which are to learn a general problem-solving technique, how to solve word problems, how to prepare for exams, and tips for taking exams. Examples then demonstrate applying the 5-step general strategy and the KUDOS (Known, Unknown, Definitions, Output, Substantiate) method to solve sample physics problems step-by-step. The strategies provide a systematic approach to breaking down problems and connecting known information to unknowns through definitions and equations.
problem_solving in physics

The document provides guidance on solving physics problems using a general 5-step strategy and the KUDOS method for word problems. It begins with an overview of the learning objectives which are to learn a general problem-solving technique, how to solve word problems, how to prepare for exams, and tips for taking exams. Examples then demonstrate applying the 5-step general strategy and the KUDOS (Known, Unknown, Definitions, Output, Substantiate) method to sample physics word problems.
e-asTTle Staff Meeting PowerPoint

This document discusses how to effectively use e-asTTle, an online formative assessment tool, to promote learning. It addresses common misperceptions about testing and how e-asTTle challenges traditional approaches. Teachers are encouraged to create tests at appropriate difficulty levels for students and to use test results to identify strengths, gaps, and areas for further teaching to better inform student learning.
E as t-tle adv pp

This document discusses how to effectively use e-asTTle, an online formative assessment tool, to promote student learning. It addresses common misperceptions about testing and provides guidance on interpreting student test results to inform teaching. E-asTTle can be used to create appropriate tests, understand student performance, and target support. The document emphasizes that e-asTTle should provide challenging tests to reveal student strengths and gaps, and that results indicate a student's ability rather than just the number of questions correct.
MATH 107 Great Stories /newtonhelp.com

For more course tutorials visit
www.newtonhelp.com
Curve-fitting Project - Linear Regression Model
A. Summary For this assignment you will be collecting data which exhibits a relatively linear trend, finding the line of best fit, plotting the data and the line, interpreting the slope, and using the linear equation to make
Specs design

This summary provides an overview of two units on language testing and assessment:
Unit B4 discusses test specification design, including elements that should be included like samples and guiding language. It also examines the distinction between prompt and response attributes.
Unit C4 focuses on how test specifications evolve over time. It provides examples of a role-play assessment and how the scoring criteria and use of written plans changed between versions as instructors debated and tested the requirements. The unit proposes applying a reverse engineering workshop to critically analyze existing test tasks and improve testing practices.
Combining General and Genre-Specific Approaches to L2 Writing Instruction

The document discusses teaching writing abstracts to Japanese university students. It argues that abstract writing instruction should not only focus on genre-specific patterns but also general discourse patterns that are common across genres. The document illustrates how move analysis can be combined with discourse relational analysis to analyze both the specific structure of abstracts and their relationship to broader text structures.
Introduction to programming languages part 2

1) The document discusses object-oriented programming paradigms and how objects contain methods that define the actions that can be performed on that object. It gives examples like a file object containing methods for printing, copying, and deleting.
2) It explains that classes are used to define common methods for groups of similar objects, like all file objects.
3) Methods function similarly to functions in procedural languages but are contained within objects. Some example object-oriented languages mentioned are Java and C++.
Face Detection Using MATLAB (SUD)

This Presentation is for project work which will work on the "FACE DETECTION USING MATLAB".
This presentation will be prepared on the practical basis instead of theoretical knowledge. So result may vary on the basis of your practical work.
This Presentation is of standard format which is also beneficial for the engineering student for project work.
AshwiniCV- SAP Basis

Ashwini Panchal is seeking a challenging career in the IT industry utilizing her 3.1 years of experience in IT and 2.1 years of experience in SAP Basis. She has extensive skills in SAP Basis, Netweaver, ECC 6.0 and above, Oracle, and working on Windows and Linux platforms. She holds an M.Sc. in Mathematics and Scientific Computing and has worked on projects at Infosys, ADP, and Compliance Solution Center.
Similar to Pedagogic application of regular expressions (20)
Determining The Barriers Faced By Novice Programmers

Determining The Barriers Faced By Novice Programmers
Organization strategies to increase development productivity

Organization strategies to increase development productivity
Combining General and Genre-Specific Approaches to L2 Writing Instruction

Combining General and Genre-Specific Approaches to L2 Writing Instruction
More from john6938
Social Media Ethics.pptx

Social media has changed communication but also raises ethical issues around privacy, misinformation, and mental health. Key debates focus on balancing free speech against harmful content. Filter bubbles and confirmation bias can limit exposure to diverse views through algorithms that amplify aligned content. Disinformation spreads for political and financial gain using bots, fake accounts and doctored content, undermining trust and democracy. Hate speech and cyberbullying on platforms can seriously impact mental health.
Future of Information Ethics.pptx

The document discusses several issues relating to the future of information ethics, including privacy, surveillance, algorithmic bias, intellectual property, globalization, and augmentation. Specifically, it addresses the need for individuals to have control over their personal data and consent to its use (privacy), the debate around balancing privacy rights with security interests behind surveillance practices, how algorithms can perpetuate inequality if not designed carefully, balancing copyright with open-source licensing, challenges of cross-border data flows, and both current and future ethical challenges relating to new technologies.
Bioethics.pptx

Bioethics examines ethical issues arising from advances in biology and medicine. It focuses on topics like abortion, euthanasia, genetic testing, and human experimentation. Bioethics also explores the duties of health professionals and aims to protect vulnerable groups. It provides a framework for complex moral issues in healthcare. Key events in bioethics history include the first test-tube baby in 1978 and gene-edited children in 2018. U.S. laws like HIPAA and the Common Rule aim to protect privacy and informed consent while international guidelines promote human dignity. Autonomy, beneficence, and justice are important principles in bioethical decision making.
Surveillance and security.pptx

This document discusses the ethics of surveillance and security. It covers various ethical approaches, security concepts, types of surveillance, hacking techniques, legal frameworks, privacy concepts, stakeholders, social factors, and ethical dilemmas related to information security and privacy. Key topics include utilitarianism, deontology, virtue ethics, rights-based ethics, social contract theory, encryption, firewalls, intrusion detection, authentication, CCTV, data mining, internet monitoring, wiretapping, facial recognition, penetration testing, social engineering, phishing, vulnerability assessments, GDPR, CFAA, FISMA, the right to be forgotten, consent decrees, anonymity, data minimization, opt-in vs opt-out, information lifec
Introduction to Expert Systems.pptx

The document describes 4 different expert systems proposed by different teams to identify the author of an email. Each system analyzes word frequency, keyword frequency, and part-of-speech patterns after keywords in known and questioned texts to determine the author. The systems compare feature vectors representing writing style extracted from the texts to identify or verify the author.
Starbuck.pptx

The police collected 4 datasets of emails - 2 from Debbie before and after marriage, 1 from Jamie, and 1 large reference collection. They analyzed the datasets using linguistic analysis of word frequencies, keywords that occur more than expected, and patterns around keywords. Comparing these linguistic features across the datasets could determine if the same person wrote the questioned and known datasets.
Unit 4 Problem breakdown.pptx

The document discusses using an expert system to analyze linguistic patterns in written documents. It describes using an expert system to analyze a threatening email and other emails from a suspect's computer to identify similarities in word frequencies, keywords, and keyword order that could indicate the suspect authored the threatening email. The system would analyze the questioned, known, and reference documents to generate shared word frequency, keyword frequency, and keyword positional lists to help determine authorship.
Image_recognition.pptx

Barcodes and image recognition technology are examples of machine-readable representations of data. Barcodes use a pattern of bars and spaces that can be read by optical scanners to identify numbers and letters. Image recognition allows computers to identify objects in images through techniques like deep learning, which automatically extracts features from image data. Face recognition is a type of image recognition that extracts features from facial images and compares them to identify individuals, using algorithms like ResNet that represent faces as vectors and compare their Euclidean distances.
Algorithms.pptx

There are many sorting algorithms that can sort a list of numbers in ascending or descending order. Some common sorting algorithms include bubble sort, merge sort, and quicksort. Bubble sort has a computational complexity of O(n2) while merge sort and quicksort have better complexities of O(n log n). Stack and queue are abstract data types - stack follows LIFO (Last In First Out) while queue follows FIFO (First In First Out). Stack adds and removes elements from the top of the data structure, while queue adds to the tail and removes from the head.
Artificial_intelligence.pptx

Edge AI allows devices like self-driving cars to make decisions immediately using on-device processing rather than cloud-based processing, which introduces latency. Edge AI processes data and inferences locally on IoT and sensor devices. This enables applications like self-driving cars using computer vision to detect humans and stop in real-time. While Edge AI provides benefits like lower latency, security, and data privacy, it also faces limitations in processing power and operational complexity compared to cloud-based AI.
Image_generation.pptx

The document describes how to generate and review images using machine learning. To generate images, a model learns from original images, searches topics to generate new images on, and iterates generating and scoring images until a threshold is passed. To review generated images, both input and generated images are disassembled into pixels, quantified by color, analyzed for tendencies, which are then compared between input and generated images to find the generated image most similar to the original tendencies.
Computer_Graphics.pptx

Computer graphics refers to images and figures created using a computer. There are two main types: 2D computer graphics, which are two-dimensional images, and 3D computer graphics, which create three-dimensional virtual spaces and objects. Creating 3D computer graphics involves several steps: modeling virtual objects, adding textures, rigging for movement, lighting, animation, and rendering to convert the 3D scene to a 2D image. A challenge with creating realistic human figures with 3D computer graphics is the "uncanny valley" effect, where figures that are almost but not perfectly realistic can appear creepy. Advances in technology now allow for highly realistic 3D computer graphics that avoid this effect.
Security.pptx

The document discusses information security and protecting personal information. It defines information security as ensuring the confidentiality, integrity, and availability of information. Confidentiality means only authorized individuals can access information. Integrity means information has not been altered or destroyed. Availability means authorized individuals have access to information when needed without interruption. Security measures help protect against potential harm from others by restricting what others can do. However, security has weaknesses that can be exploited.
Gravitational_wave_detection.pptx

Gravitational wave detection and denoising algorithm uses machine learning to classify and filter noise from gravitational wave data. There are 22 main types of noise that can be identified using supervised and unsupervised learning algorithms. Unsupervised learning allows the computer to classify noise types on its own by finding inherent groupings or clusters in the data, while supervised learning uses labeled examples to efficiently perform classifications. The proposed method uses a variational autoencoder and invariant information clustering to learn features from spectrogram images of transient noise and then classify the noise types based on the learned features.
Embedded_Systems.pptx

This document discusses key considerations for designing real-time embedded systems to ensure predictability and avoid failure. It identifies four main problems: whether the architecture is suitable, if link speeds are adequate, if processing components are powerful enough, and if the operating system is suitable. For each problem, it provides details on how to evaluate them and ensure real-time requirements are met, such as keeping CPU and link utilization below 50% and using an RTOS with preemptive scheduling and low interrupt latency and scheduling variance.
Software_engineering.pptx

Python is the most widely used programming language in the world due to its simple syntax, wide platform support, and ease of use. It can be learned by both professionals and students. A survey by Stack Overflow found incredible growth in the number of visitors to Python questions on the site. Lisp is one of the oldest high-level programming languages still in use, known for its extensive use of parentheses in code. It was influential in the development of artificial intelligence. R is a programming language and software environment for statistical analysis and graphics. It provides many statistical and graphical techniques and is highly extensible.
Quantum_computers.pptx

Quantum computers can solve problems in hours that would take classical computers over 100 million years by leveraging the quantum state of superposition where multiple states exist simultaneously. Specifically, quantum computers could crack RSA encryption, which normally takes over 100 million years on classical computers, in just a few hours by applying this quantum superposition property.
NLP.pptx

Neural networks like artificial neural networks (ANNs) and long short-term memory (LSTM) networks are commonly used in machine translation systems. ANNs mimic the human brain by recognizing relationships in vast amounts of data, similar to neural connections in the brain. The field of machine translation began in the 1950s with rule-based machine translation (RBMT) relying on linguistic rules and dictionaries. Statistical machine translation (SMT) developed in the late 1970s and analyzed existing human translations. More recently, neural machine translation (NMT) introduced in the last decade learns from each translation to improve. LSTM is a type of RNN with feedback connections that can process entire sequences of data over time and is well-suited for classifying
Sensors_SLAM.pptx

SLAM is a technology that uses sensors to allow objects like vehicles to simultaneously map their environment and locate themselves within it. It utilizes sensors such as LiDAR and cameras to create maps without relying on GPS. LiDAR SLAM is particularly accurate and commonly used for automated driving as LiDAR can measure distance and shape using reflected laser time.
More from john6938 (20)
Recently uploaded
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

(𝐓𝐋𝐄 𝟏𝟎𝟎) (𝐋𝐞𝐬𝐬𝐨𝐧 𝟏)-𝐏𝐫𝐞𝐥𝐢𝐦𝐬
𝐃𝐢𝐬𝐜𝐮𝐬𝐬 𝐭𝐡𝐞 𝐄𝐏𝐏 𝐂𝐮𝐫𝐫𝐢𝐜𝐮𝐥𝐮𝐦 𝐢𝐧 𝐭𝐡𝐞 𝐏𝐡𝐢𝐥𝐢𝐩𝐩𝐢𝐧𝐞𝐬:
- Understand the goals and objectives of the Edukasyong Pantahanan at Pangkabuhayan (EPP) curriculum, recognizing its importance in fostering practical life skills and values among students. Students will also be able to identify the key components and subjects covered, such as agriculture, home economics, industrial arts, and information and communication technology.
𝐄𝐱𝐩𝐥𝐚𝐢𝐧 𝐭𝐡𝐞 𝐍𝐚𝐭𝐮𝐫𝐞 𝐚𝐧𝐝 𝐒𝐜𝐨𝐩𝐞 𝐨𝐟 𝐚𝐧 𝐄𝐧𝐭𝐫𝐞𝐩𝐫𝐞𝐧𝐞𝐮𝐫:
-Define entrepreneurship, distinguishing it from general business activities by emphasizing its focus on innovation, risk-taking, and value creation. Students will describe the characteristics and traits of successful entrepreneurs, including their roles and responsibilities, and discuss the broader economic and social impacts of entrepreneurial activities on both local and global scales.
THE SACRIFICE HOW PRO-PALESTINE PROTESTS STUDENTS ARE SACRIFICING TO CHANGE T...

The recent surge in pro-Palestine student activism has prompted significant responses from universities, ranging from negotiations and divestment commitments to increased transparency about investments in companies supporting the war on Gaza. This activism has led to the cessation of student encampments but also highlighted the substantial sacrifices made by students, including academic disruptions and personal risks. The primary drivers of these protests are poor university administration, lack of transparency, and inadequate communication between officials and students. This study examines the profound emotional, psychological, and professional impacts on students engaged in pro-Palestine protests, focusing on Generation Z's (Gen-Z) activism dynamics. This paper explores the significant sacrifices made by these students and even the professors supporting the pro-Palestine movement, with a focus on recent global movements. Through an in-depth analysis of printed and electronic media, the study examines the impacts of these sacrifices on the academic and personal lives of those involved. The paper highlights examples from various universities, demonstrating student activism's long-term and short-term effects, including disciplinary actions, social backlash, and career implications. The researchers also explore the broader implications of student sacrifices. The findings reveal that these sacrifices are driven by a profound commitment to justice and human rights, and are influenced by the increasing availability of information, peer interactions, and personal convictions. The study also discusses the broader implications of this activism, comparing it to historical precedents and assessing its potential to influence policy and public opinion. The emotional and psychological toll on student activists is significant, but their sense of purpose and community support mitigates some of these challenges. However, the researchers call for acknowledging the broader Impact of these sacrifices on the future global movement of FreePalestine.
NIPER 2024 MEMORY BASED QUESTIONS.ANSWERS TO NIPER 2024 QUESTIONS.NIPER JEE 2...

NIPER JEE PYQ
NIPER JEE QUESTIONS
MOST FREQUENTLY ASK QUESTIONS
NIPER MEMORY BASED QUWSTIONS
skeleton System.pdf (skeleton system wow)

🔥🔥🔥🔥🔥🔥🔥🔥🔥
إضغ بين إيديكم من أقوى الملازم التي صممتها
ملزمة تشريح الجهاز الهيكلي (نظري 3)
💀💀💀💀💀💀💀💀💀💀
تتميز هذهِ الملزمة بعِدة مُميزات :
1- مُترجمة ترجمة تُناسب جميع المستويات
2- تحتوي على 78 رسم توضيحي لكل كلمة موجودة بالملزمة (لكل كلمة !!!!)
#فهم_ماكو_درخ
3- دقة الكتابة والصور عالية جداً جداً جداً
4- هُنالك بعض المعلومات تم توضيحها بشكل تفصيلي جداً (تُعتبر لدى الطالب أو الطالبة بإنها معلومات مُبهمة ومع ذلك تم توضيح هذهِ المعلومات المُبهمة بشكل تفصيلي جداً
5- الملزمة تشرح نفسها ب نفسها بس تكلك تعال اقراني
6- تحتوي الملزمة في اول سلايد على خارطة تتضمن جميع تفرُعات معلومات الجهاز الهيكلي المذكورة في هذهِ الملزمة
واخيراً هذهِ الملزمة حلالٌ عليكم وإتمنى منكم إن تدعولي بالخير والصحة والعافية فقط
كل التوفيق زملائي وزميلاتي ، زميلكم محمد الذهبي 💊💊
🔥🔥🔥🔥🔥🔥🔥🔥🔥
How to Download & Install Module From the Odoo App Store in Odoo 17

Custom modules offer the flexibility to extend Odoo's capabilities, address unique requirements, and optimize workflows to align seamlessly with your organization's processes. By leveraging custom modules, businesses can unlock greater efficiency, productivity, and innovation, empowering them to stay competitive in today's dynamic market landscape. In this tutorial, we'll guide you step by step on how to easily download and install modules from the Odoo App Store.
Bossa N’ Roll Records by Ismael Vazquez.

Bossa N Roll Records presentation by Izzy Vazquez for Music Retail and Distribution class at Full Sail University
Contiguity Of Various Message Forms - Rupam Chandra.pptx

Contiguity Of Various Message Forms - Rupam Chandra.pptx
Elevate Your Nonprofit's Online Presence_ A Guide to Effective SEO Strategies...

Whether you're new to SEO or looking to refine your existing strategies, this webinar will provide you with actionable insights and practical tips to elevate your nonprofit's online presence.
220711130083 SUBHASHREE RAKSHIT Internet resources for social science

Internet resources for social science
Temple of Asclepius in Thrace. Excavation results

The temple and the sanctuary around were dedicated to Asklepios Zmidrenus. This name has been known since 1875 when an inscription dedicated to him was discovered in Rome. The inscription is dated in 227 AD and was left by soldiers originating from the city of Philippopolis (modern Plovdiv).
Educational Technology in the Health Sciences

Plenary presentation at the NTTC Inter-university Workshop, 18 June 2024, Manila Prince Hotel.
Recently uploaded (20)
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum
THE SACRIFICE HOW PRO-PALESTINE PROTESTS STUDENTS ARE SACRIFICING TO CHANGE T...

THE SACRIFICE HOW PRO-PALESTINE PROTESTS STUDENTS ARE SACRIFICING TO CHANGE T...
NIPER 2024 MEMORY BASED QUESTIONS.ANSWERS TO NIPER 2024 QUESTIONS.NIPER JEE 2...

NIPER 2024 MEMORY BASED QUESTIONS.ANSWERS TO NIPER 2024 QUESTIONS.NIPER JEE 2...
How to Download & Install Module From the Odoo App Store in Odoo 17

How to Download & Install Module From the Odoo App Store in Odoo 17
Contiguity Of Various Message Forms - Rupam Chandra.pptx

Contiguity Of Various Message Forms - Rupam Chandra.pptx
Elevate Your Nonprofit's Online Presence_ A Guide to Effective SEO Strategies...

Elevate Your Nonprofit's Online Presence_ A Guide to Effective SEO Strategies...
220711130083 SUBHASHREE RAKSHIT Internet resources for social science

220711130083 SUBHASHREE RAKSHIT Internet resources for social science
Juneteenth Freedom Day 2024 David Douglas School District

Juneteenth Freedom Day 2024 David Douglas School District
Pedagogic application of regular expressions
- 1. John Blake Japan Advanced Institute of Science and Technology Pedagogic application of regular expressions /bbetweenW+(?:w+W+){1,2}?tob/gi;
- 2. Overview 02 Introduction • Probabilistic parsing • Rule-based pattern matching • Regular expressions Pedagogic applications • Modality detector • Error detector • Other: tagged corpora, pronunciation of “ed”
- 3. Probabilistic parsing 03 • Dynamic algorithms • Machine learning • Training sets (e.g. Stanford POS parser) Extremely powerful, but requires significant knowledge of computational linguistics and huge time investment so…
- 4. Rule-based pattern matching 04 1. There is a man on your left. T / F If true, a man is on your left. Stop. If false, proceed to 2. 2. There is a woman on your left. T / F If true, there is a woman on your left. Stop. If false, there is nobody on your left. Stop. True/false statements
- 5. Rule-based pattern matching 05 Decision-tree algorithm There is a man on your left. There is a woman on your left. No.Yes. STOP Yes. STOP No. There is nobody on your left. STOP Assumptions: 1. Only adults are present 2. There is no third gender
- 6. Rule-based pattern matching 06 There is a man. /bmanb/; There is a woman. /bwomanb/; Regular expressions (regexp|regex) The discrete words “man” and “woman” will be identified, generating a “true” result.
- 7. Regular expressions (Regex) 07 e.g. /bmaybeb/gi; – escape (from normal characters) i – case insensitive b – boundary g – greedy 1. I think that maybe he can understand. T/F 2. He may be able to understand T/F 3. Maybe, he can understand. T/F 4. Maybelline is a company name. T/F 5. Maybe, he said maybe. T/F
- 8. Pedagogic applications 08 Modality detector Online error detectors - Common error detector (Morrall, 2000-14) - Corpus-based error detector (Blake, 2012-15) Other applications - Annotation highlighter - Ideas for pronunciation, grammar and vocab
- 9. 09 Situation App. 1 Students graduate students, researchers Aim write research articles Problems lack of familiarity of genre, lack of language, lack of content.
- 10. 10 Tentative language & approximation Type Examples Modal verbs may, might, would, can Lexical verbs seem, appear, suggest Modal adverbs perhaps, probably, possibly, Modal adjectives probable, possible, uncertain Modal nouns assumption, claim, possibility # Approximation 49% Almost a half, nearly 50%, less than 1 in 2 App. 1
- 11. 11 Material mismatch Students from different faculties studying tentative language (hedging) and approximation in academic writing use generic materials prepared by teacher. App. 1
- 12. 12 Lack of face validity Some students do not want to “waste time” dealing with materials not appropriate to their major. They expect materials tailored to their exact needs. App. 1
- 14. 14 Solution: Modality detector Individualized instruction • Student selects appropriate text • Student inputs relevant text • Regex identifies hedges & approximation • Execute command labels & highlights App. 1
- 15. 15 Warning: False positives More complex regex reduce false positives App. 1
- 16. 16 Piles of unmarked homework Responding to written work takes too much time, and is repetitive since many students make the same surface-level mistakes. App. 2
- 17. 17 No time to respond Teachers are expected to: • Identify the location of errors • Explain the errors (if necessary) • Correct the errors (if necessary) All of which take lots of time. App. 2
- 18. 18 Solution: Error detector Identification Student inputs own work Regex identifies expected errors Explanation Execute command selects and displays prepared explanation Correction Student corrects work and submits improved version App. 2
- 19. 19 Error classification App. 2 Type Description Accuracy factual and language errors Brevity too many words Clarity vague or ambiguous terms Objectivity emotive language Formality abbreviations, contractions, & informal terms An ethnographic survey of the literature on writing scientific research articles revealed five key criteria (Blake & Blake, 2015)
- 20. 20 App. 2
- 21. 21 Specific example Error • One of the + singular noun Regex • /bone of theb/gi; Execute • Check that the phrase one of the is followed by a plural noun App. 2
- 22. 22 False positives harnessed in learning process by forcing student engagement App. 2
- 23. 23 Difficult-to-read tags Introduction Purpose Method Results Discussion <segment features='problem;introduction;rhetorical_moves' state='active'>We address the problem of model-based object recognition.</segment> <segment features='purpose;rhetorical_moves' state='active'>Our aim is to localize and recognize road vehicles from monocular images or videos in calibrated traffic scenes.</segment> <segment features='method;rhetorical_moves' state='active'>A 3-D deformable vehicle model with 12 shape parameters is set up as prior information, and its pose is determined by three parameters, which are its position on the ground plane and its orientation about the vertical axis under ground-plane constraints.</segment> <segment features='purpose;rhetorical_moves' state='active'>An efficient local gradient-based method is proposed to evaluate the fitness between the projection of the vehicle model and image data, which is combined into a novel evolutionary computing framework to estimate the 12 shape parameters and three pose parameters by iterative evolution.</segment> <segment features='background;introduction;rhetorical_moves' state='active'>The recovery of pose parameters achieves vehicle localization, whereas the shape parameters are used for vehicle recognition.</segment> <segment features='method;rhetorical_moves' state='active'>Numerous experiments are App. 3
- 24. 24 Difficult-to-read tags Introduction Purpose Method Results Discussion <segment features='problem;introduction;rhetorical_moves' state='active'>We address the problem of model-based object recognition.</segment> <segment features='purpose;rhetorical_moves' state='active'>Our aim is to localize and recognize road vehicles from monocular images or videos in calibrated traffic scenes.</segment> <segment features='method;rhetorical_moves' state='active'>A 3-D deformable vehicle model with 12 shape parameters is set up as prior information, and its pose is determined by three parameters, which are its position on the ground plane and its orientation about the vertical axis under ground-plane constraints.</segment> <segment features='purpose;rhetorical_moves' state='active'>An efficient local gradient-based method is proposed to evaluate the fitness between the projection of the vehicle model and image data, which is combined into a novel evolutionary computing framework to estimate the 12 shape parameters and three pose parameters by iterative evolution.</segment> <segment features='background;introduction;rhetorical_moves' state='active'>The recovery of pose parameters achieves vehicle localization, whereas the shape parameters are used for vehicle recognition.</segment> <segment features='method;rhetorical_moves' state='active'>Numerous experiments are App. 3
- 25. 25 Easy-to-read tags Introduction Purpose Method Results Discussion http://www.jaist.ac.jp/~johnb/Movehighlighter.html App. 3
- 26. 26 Ideas for you and your students Pronunciation: Regular “ed” • Regular “ed” /t/, /d/, /id/ • th [voiced or voiceless] Grammar: • Tenses: e.g. perfect continuous: been + ing • Quantifiers : [U] much, little; [C] many, few; [U/C] lots of , a lot of Vocabulary: • Colours: red, blue crimson red, cobalt blue, • Body parts: hand, eyes, leg hand out, eye up, leg it
- 27. 27 Regular “ed” False positives: • learned /d/ /id/ Pron Preceeding sound Potential regex /id/ d, t /(d|t)edb/gi; /t/ voiceless consonants /(s|f)edb/gi; /d/ voiced consonants /(z|v)edb/gi; /d/ Vowel /(ow|i|ay)edb/gi; Pronunciation of “ed” is dictated by the sound of the preceeding letter(s). | – Boolean “or” so x|y means either x or y d|ted means d or ted but by adding brackets (d|t)ed means ded or ted
- 28. 28 Pronunciation of “th” Pron Feature Potential regex /𝜹/ Voiced initial th /btha(n|t|) b/gi; /bthe(b|ir|m|re|se|y) b/gi; /bthisb/gi; /btho(se|ugh|) b/gi; /bthusb/gi; /𝜽/ Voiceless initial th /bth/gi; /t/ th pronounced as t /bthomas|thames|thyme/gi; Pronunciation of “th” can be predicted by the law that for function words the initial th is pronounced as a voiced sound.
- 29. References 29 Blake, J. (2012, November 28-30). Corpus-based academic written error detector. Conference proceedings of the 20th International Conference on Computers in Education. Nanyang Technological University, Singapore. Blake, X. and Blake, J. (2015, January 29-31). Academic literacy: Mentor and mentee perspectives. Poster presented at 35th International Conference of ThaiTESOL, Bangkok, Thailand. Morrall, A. (2000-2014). Common Error Detector. [Online tool] http://www2.elc.polyu.edu.hk/cill/errordetector.htm
- 30. Any questions, comments or suggestions? johnb@jaist.ac.jp