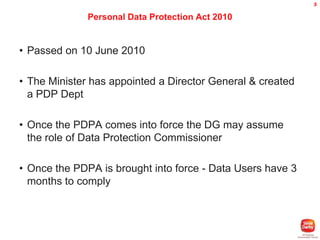
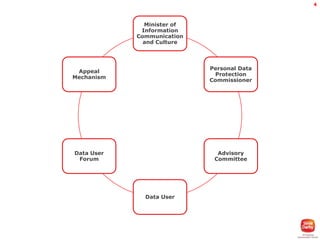
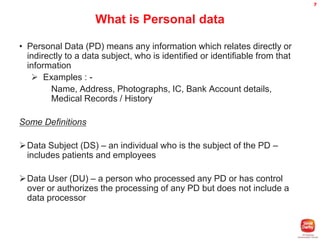
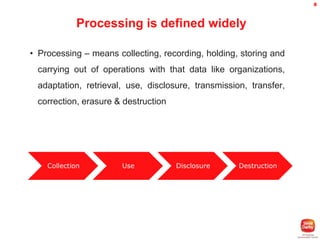
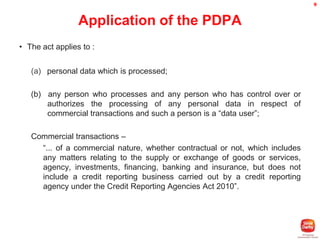
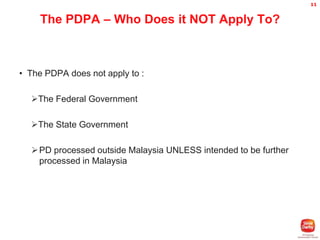
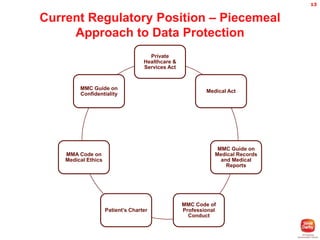
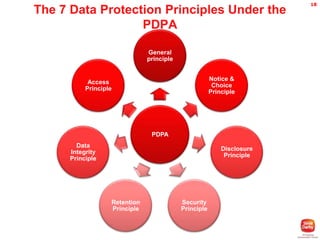
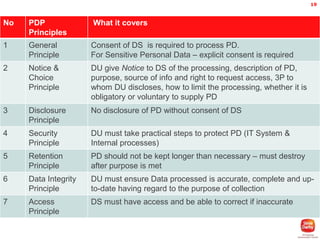
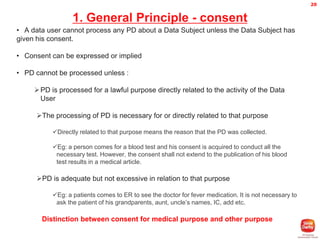
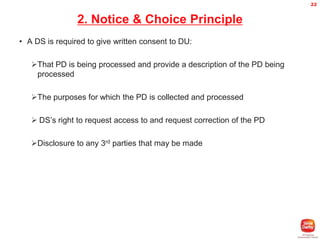
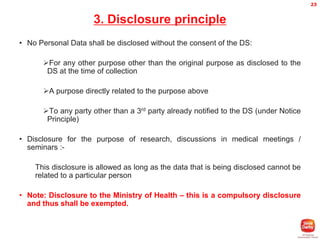
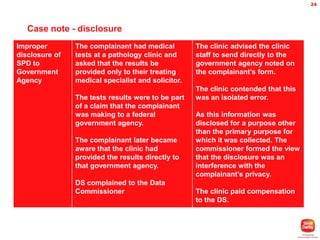
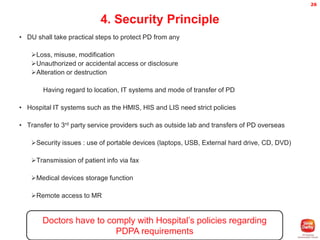
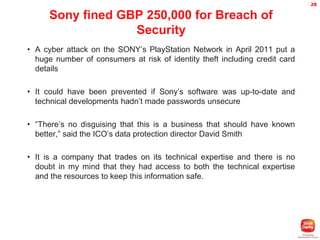
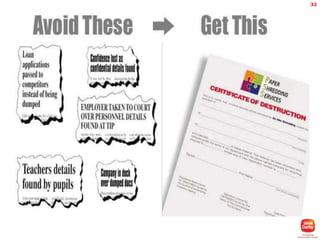
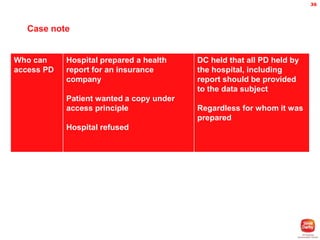
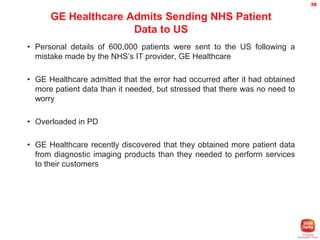
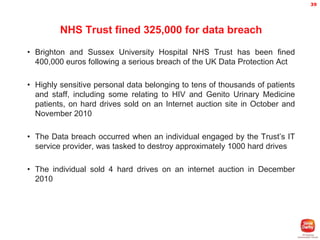
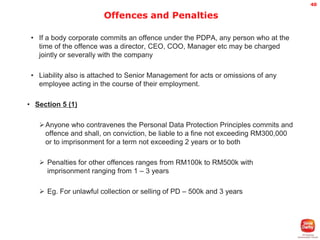
The document provides an overview of Malaysia's Personal Data Protection Act 2010. It discusses key aspects of the Act including the establishment of a Personal Data Protection Commissioner, the 7 data protection principles, and requirements around notice, consent, disclosure, security, retention, data integrity and access. It also discusses some examples of data breaches and penalties for non-compliance. The Act aims to regulate the processing of personal data and protect privacy as digital data and internet usage continues to grow significantly.