Embed presentation
Download to read offline
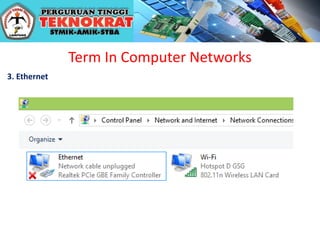
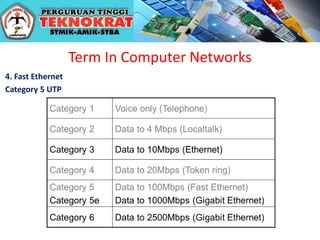
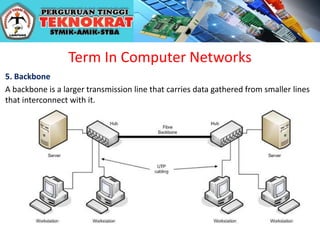
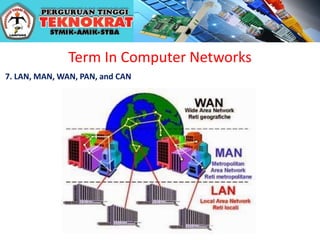
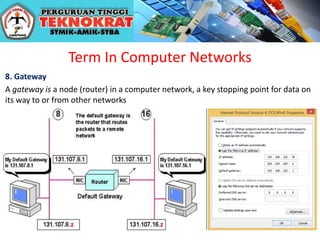


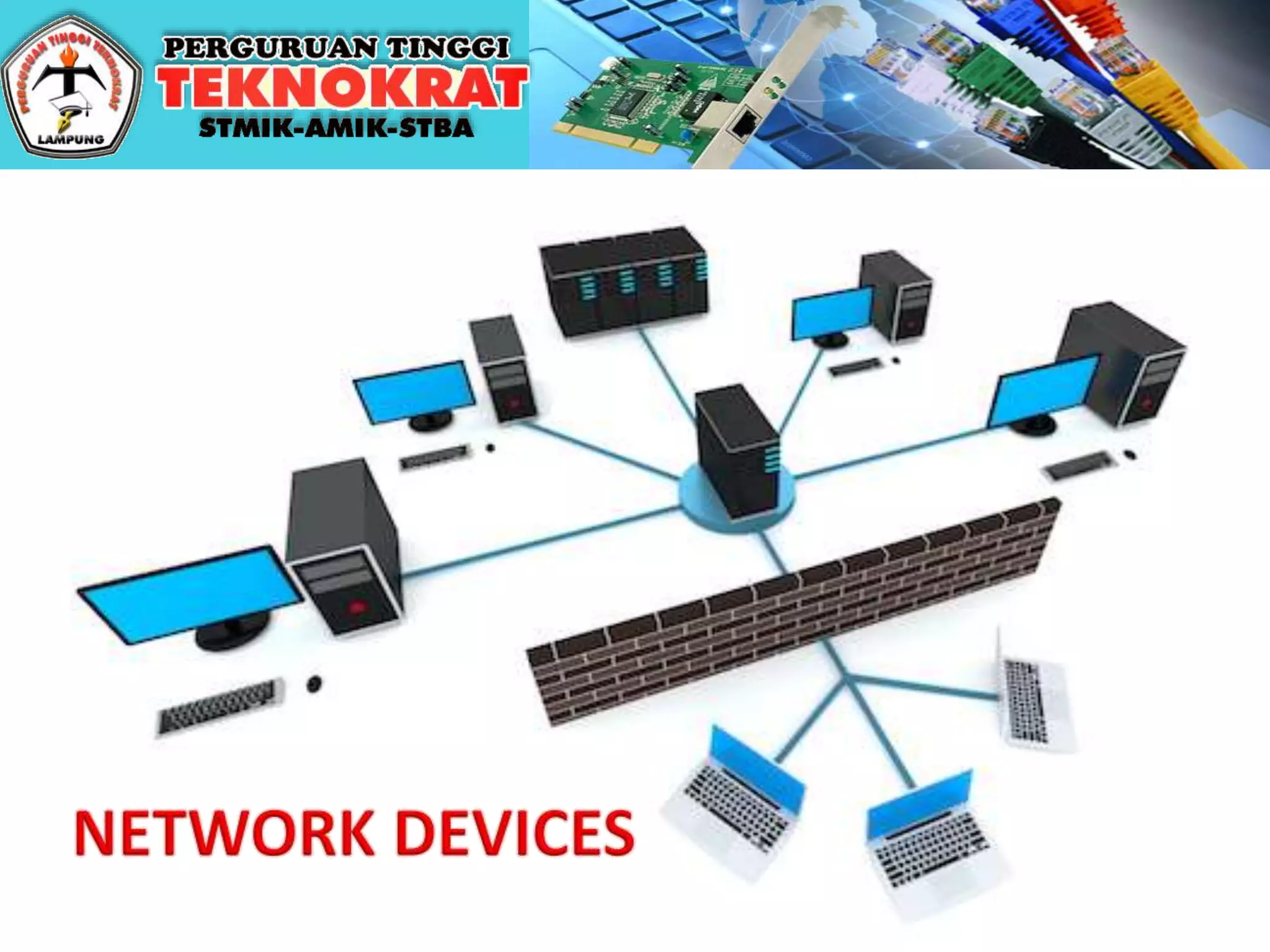
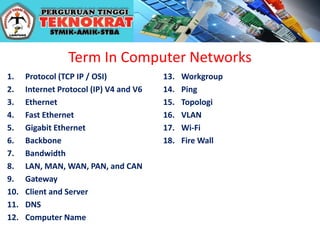
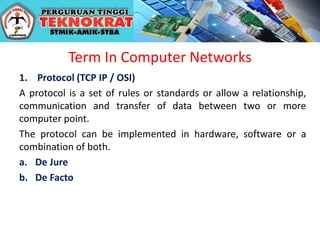
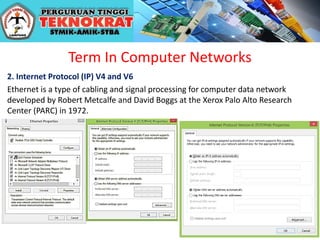
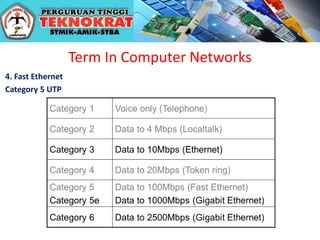
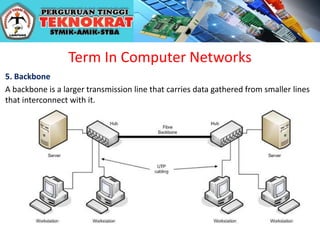
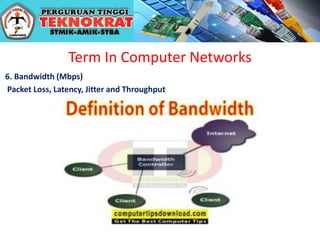
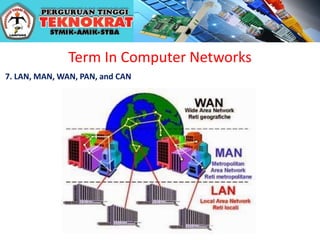
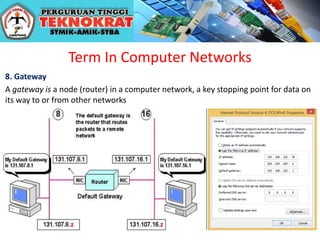
The document defines key terms related to computer networks, including protocols, IP versions, Ethernet, Fast Ethernet, bandwidth, and different types of networks. It provides definitions for protocols as sets of rules that allow communication between devices, and defines Ethernet as a type of cabling developed at Xerox PARC for computer networks. Backbones are described as larger transmission lines that carry data from interconnected smaller lines.