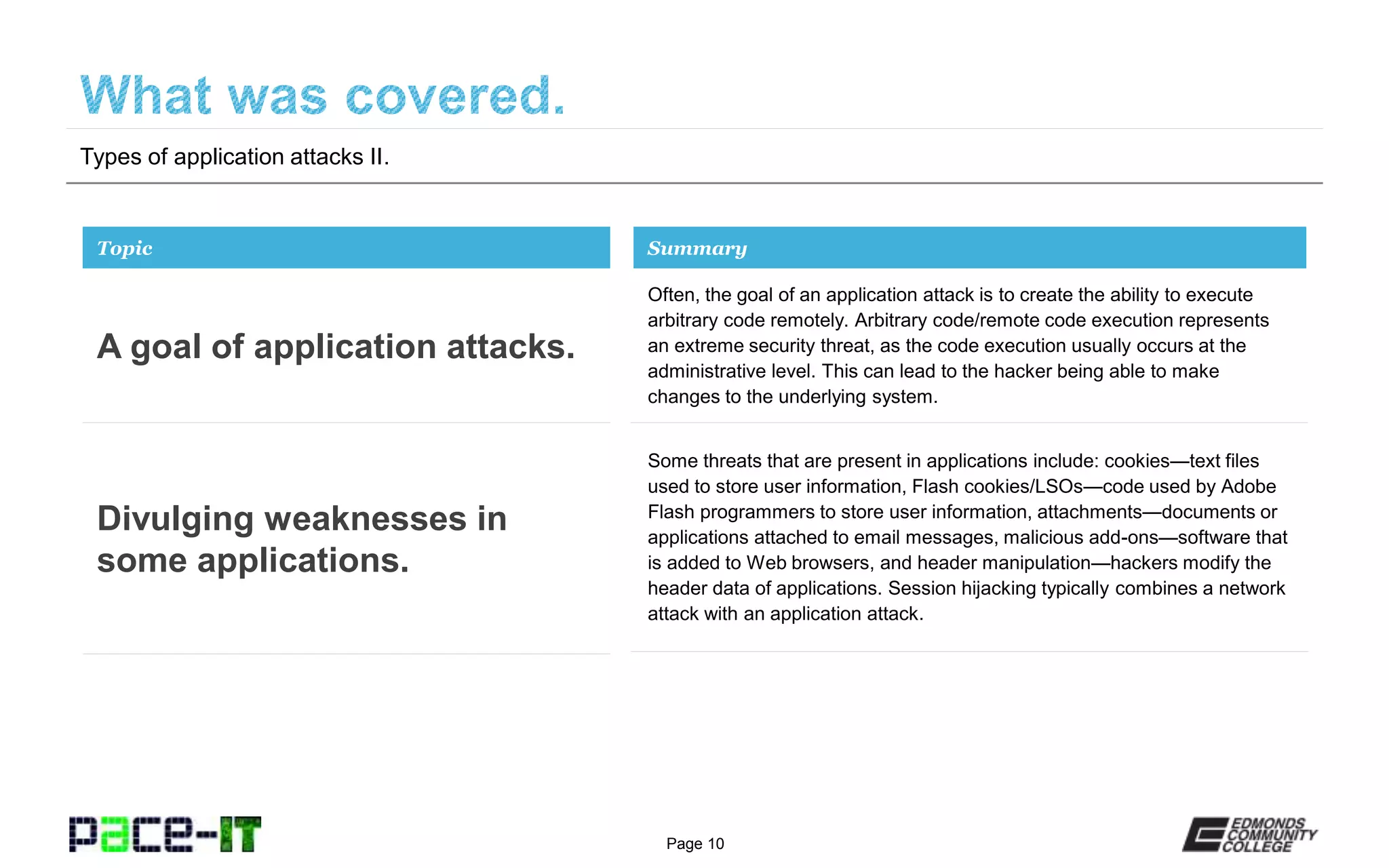
The document outlines various types of application attacks, including arbitrary code execution, cookie exploitation, session hijacking, and more, highlighting the potential security risks involved. It discusses how these attacks can allow hackers to manipulate applications and gain access to sensitive information. Lastly, the document emphasizes that the information presented is supported by funding from the U.S. Department of Labor's Employment and Training Administration.