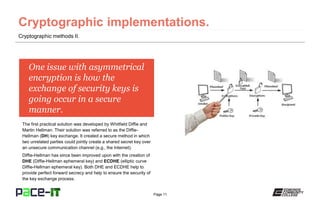
This document provides an overview of cryptographic methods, covering both symmetrical and asymmetrical encryption techniques and their vulnerabilities, particularly focusing on the significance of key security. It discusses various cryptographic implementations such as one-time pad, DES, AES, RSA, and PGP, along with key stretching techniques like bcrypt and PBKDF2 to enhance security against brute force attacks. Additionally, it touches on the importance of secure key exchange methods like the Diffie-Hellman algorithm and its improved versions.