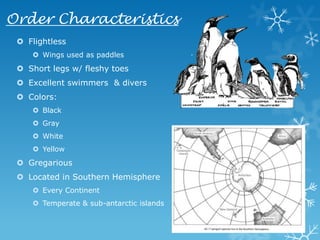
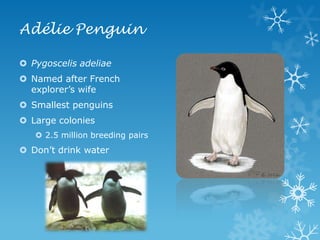
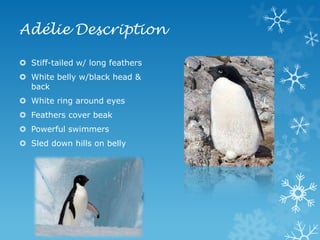
The document provides an overview of the classification and characteristics of penguins (order Sphenisciformes), including 17 to 18 recognized species and their habitats in the Southern Hemisphere. It specifically details the Adélie penguin, its physical description, diet, breeding behaviors, and nesting practices. Additionally, the document mentions the unique adaptations of penguins, such as their flightless nature and excellent swimming abilities.