Embed presentation
Download as PDF, PPTX
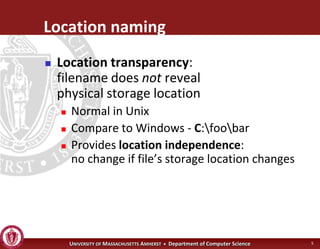
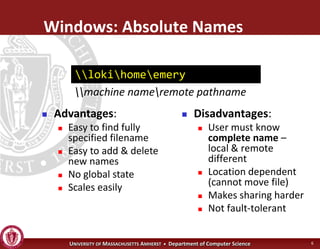
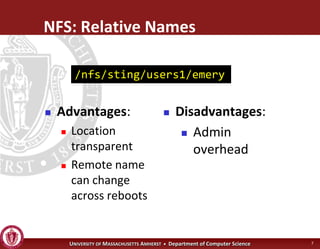
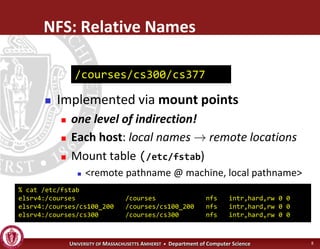
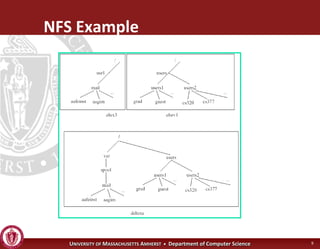
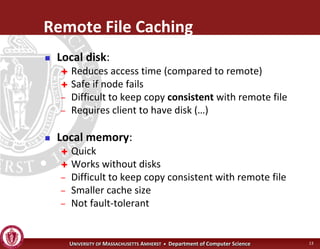
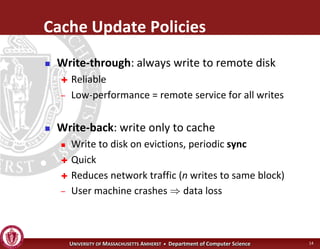
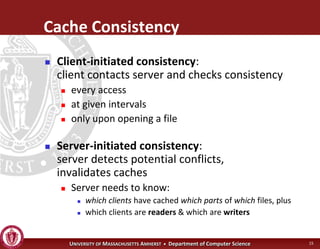
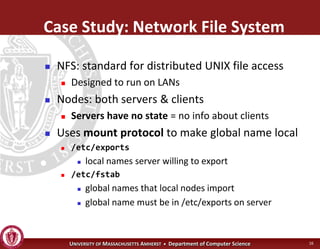
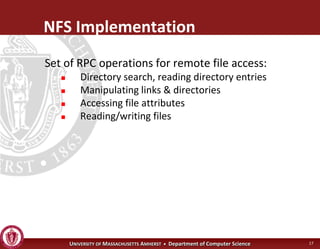
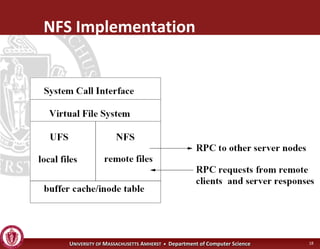
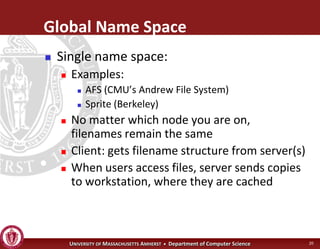


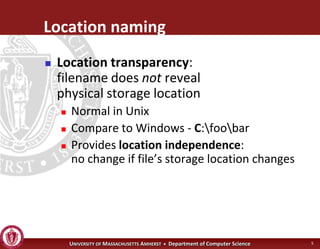
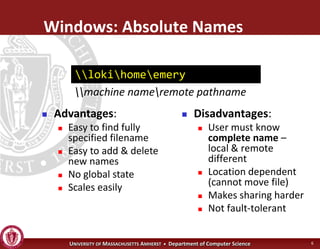
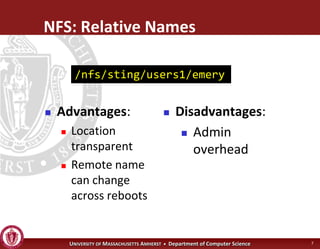
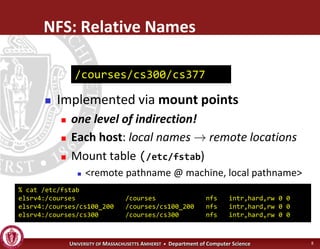
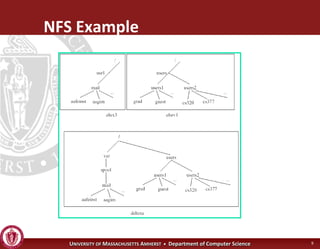
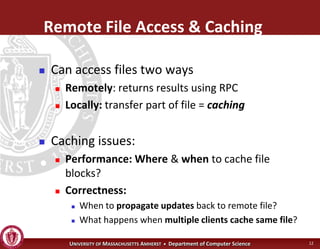
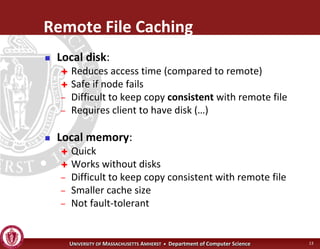
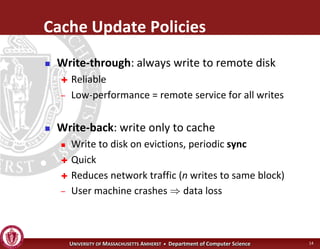
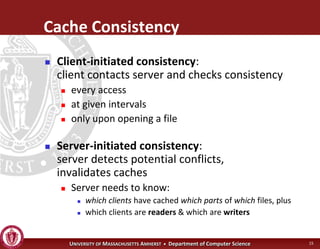
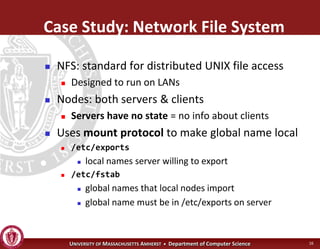
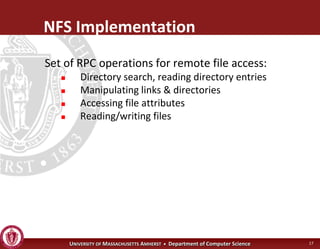
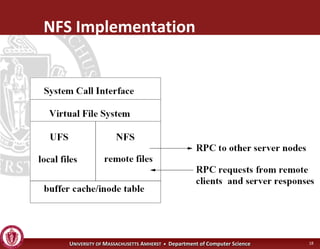
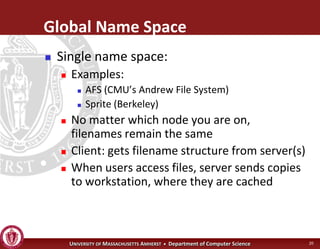
This document discusses distributed file systems and some of their key design considerations. It covers issues like naming and transparency in distributed file systems, different approaches to naming like absolute vs relative names, caching strategies like write-back vs write-through, and consistency models. It also provides examples of different distributed file systems like NFS, AFS, and Sprite and discusses some of their approaches.