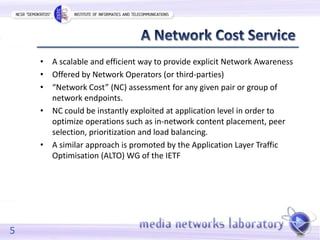
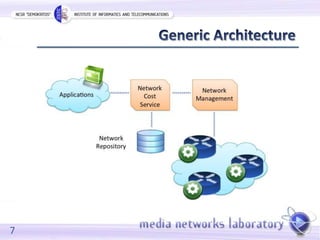
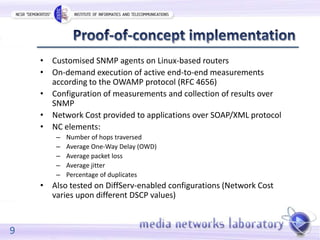
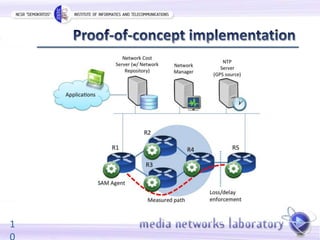
The document discusses a workshop on enhancing network-layer metrics for optimizing application performance through explicit network awareness, shifting from host-centric to content-centric communication. It emphasizes the need for scalable and efficient methods to assess network costs between endpoints, facilitating better peer selection and content distribution in contemporary architectures like P2P and CDNs. The proposed framework includes active measurements and addresses security and privacy concerns for querying entities.