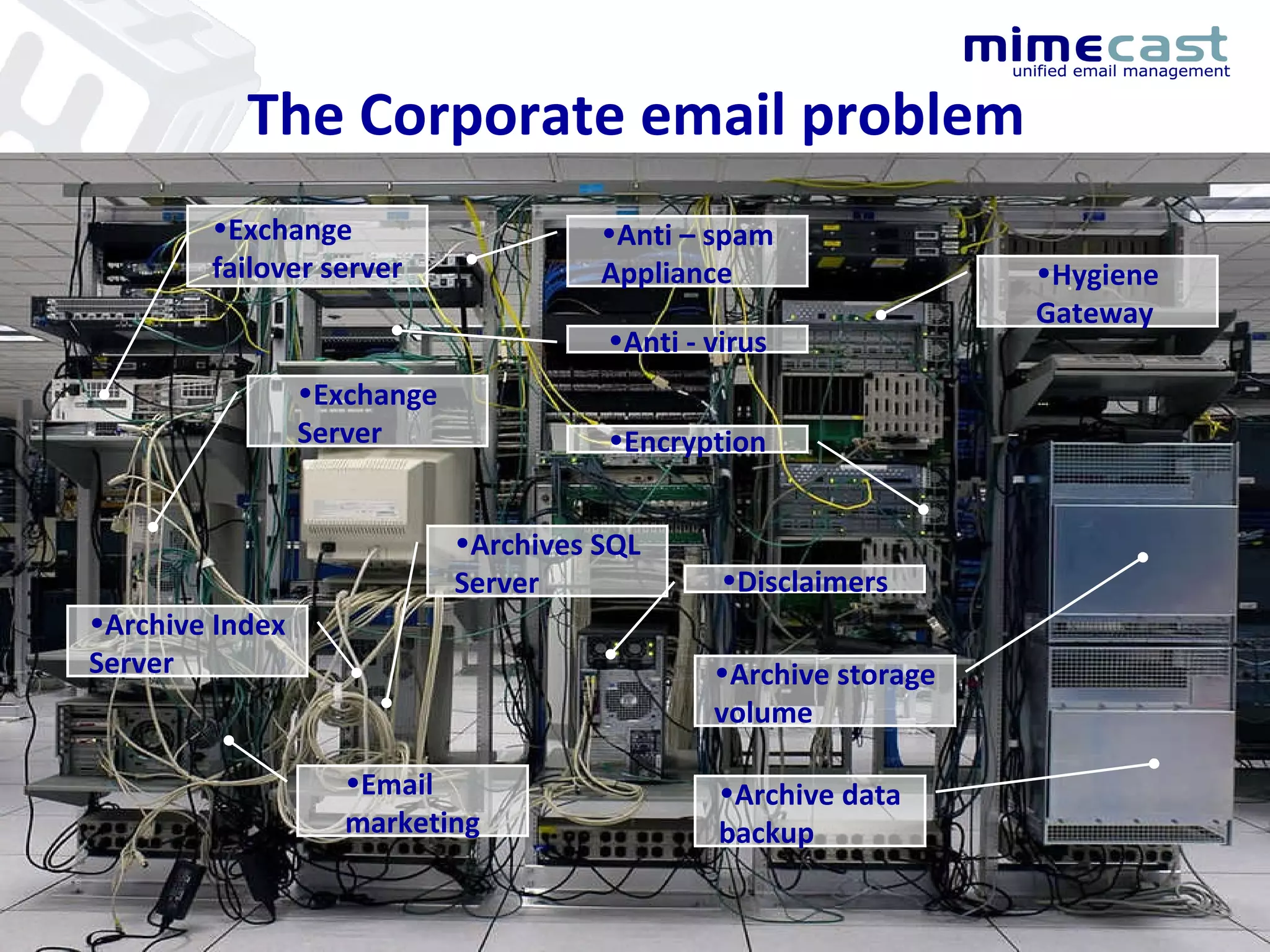
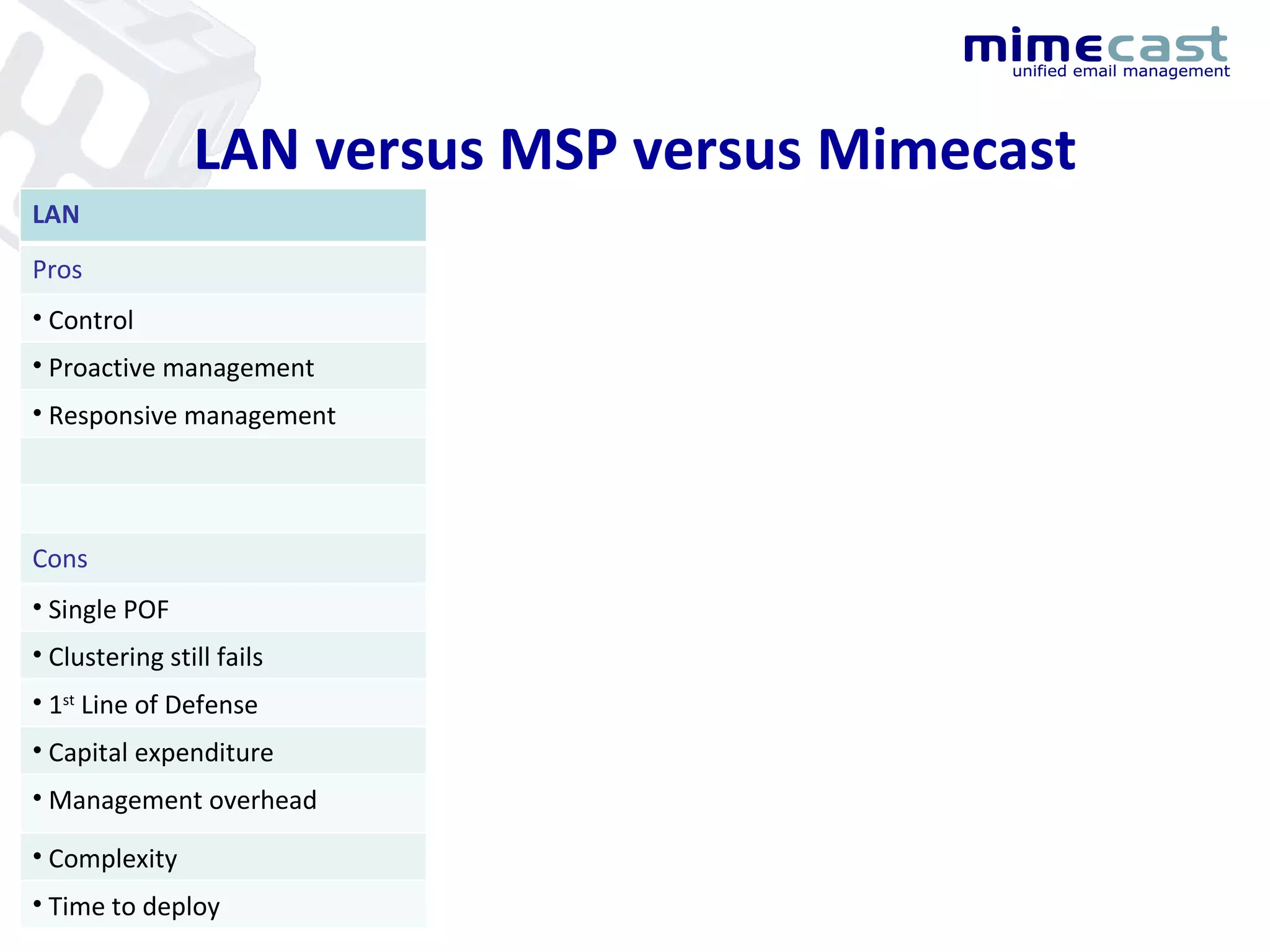
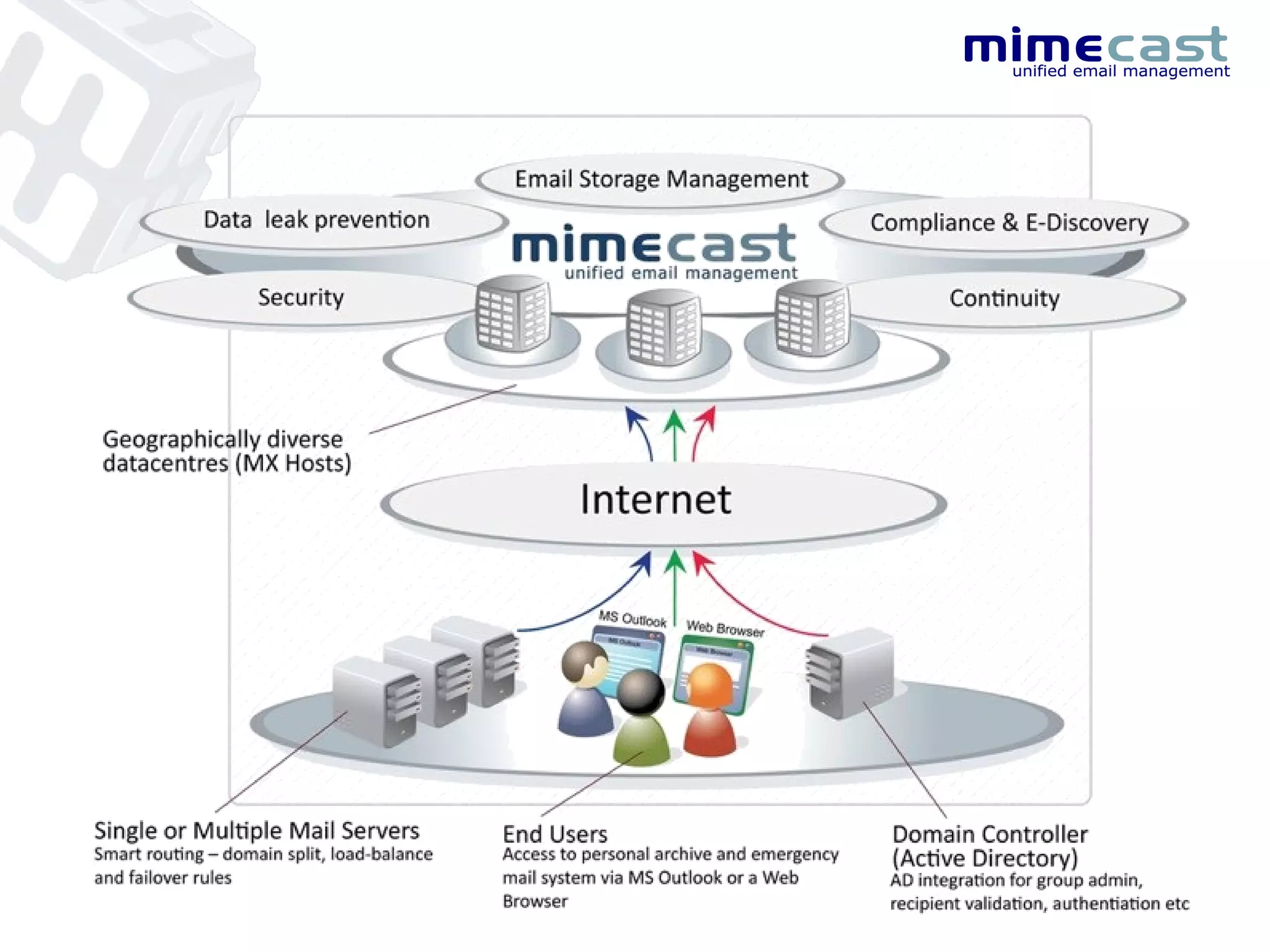
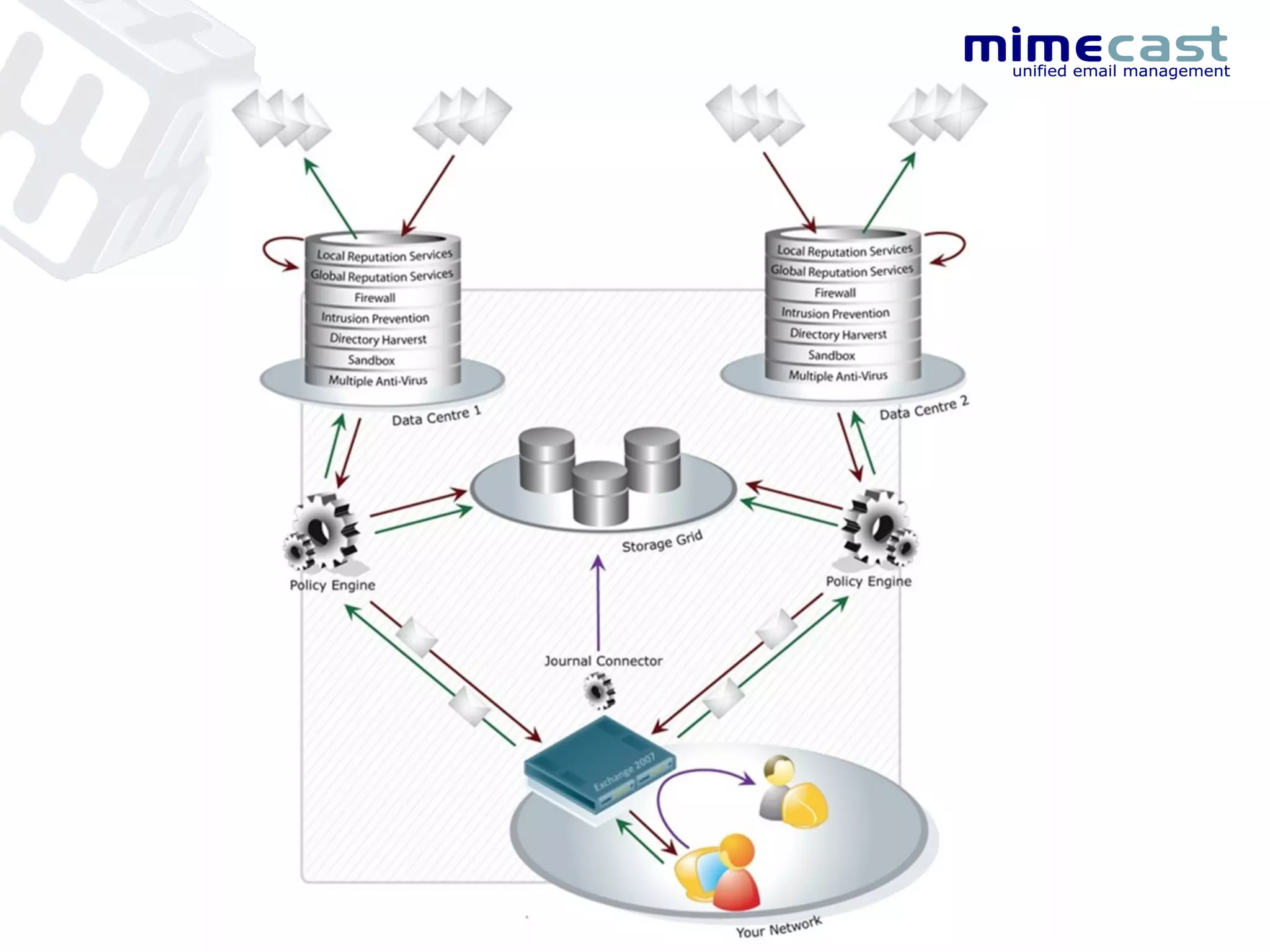
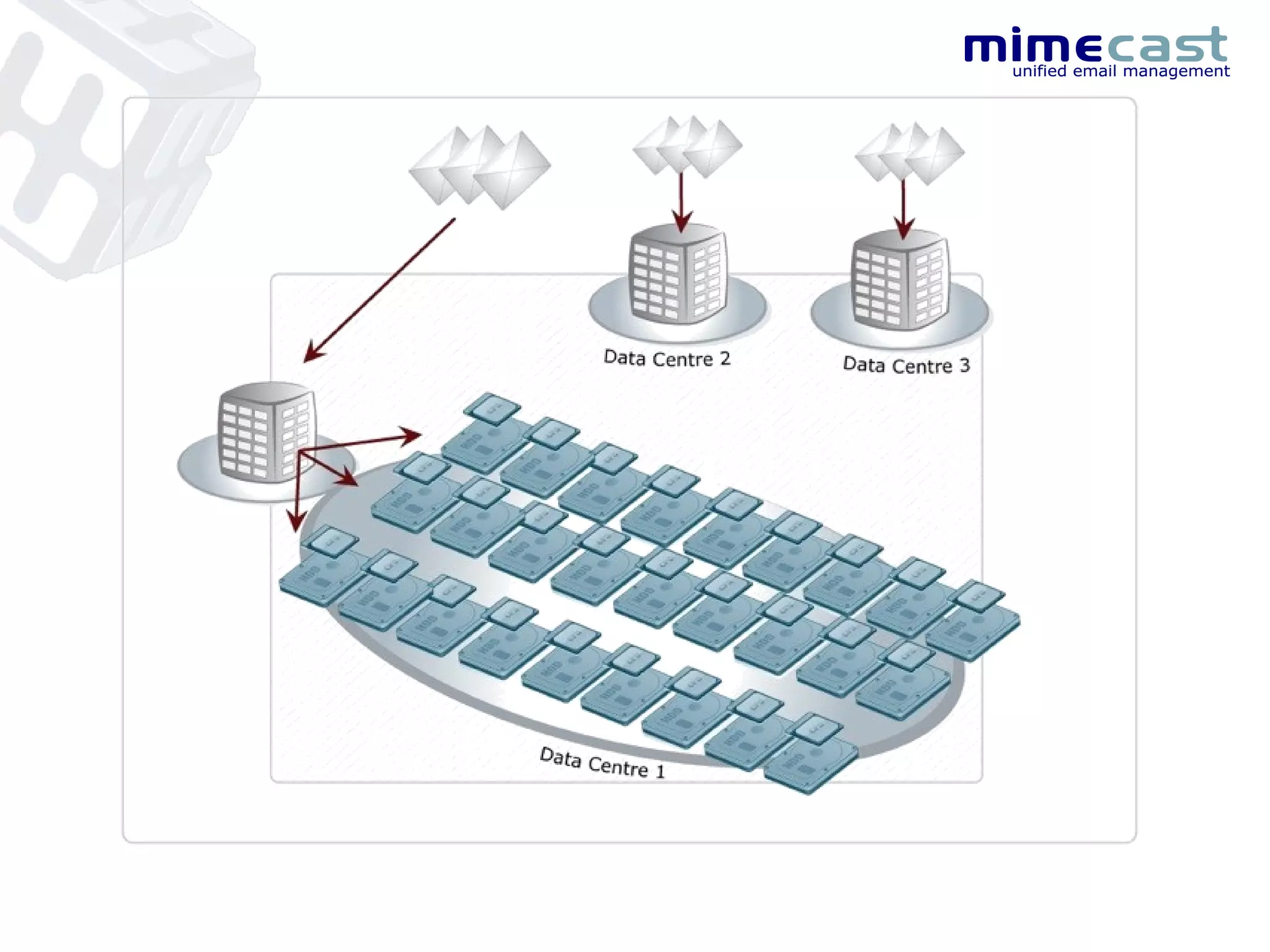
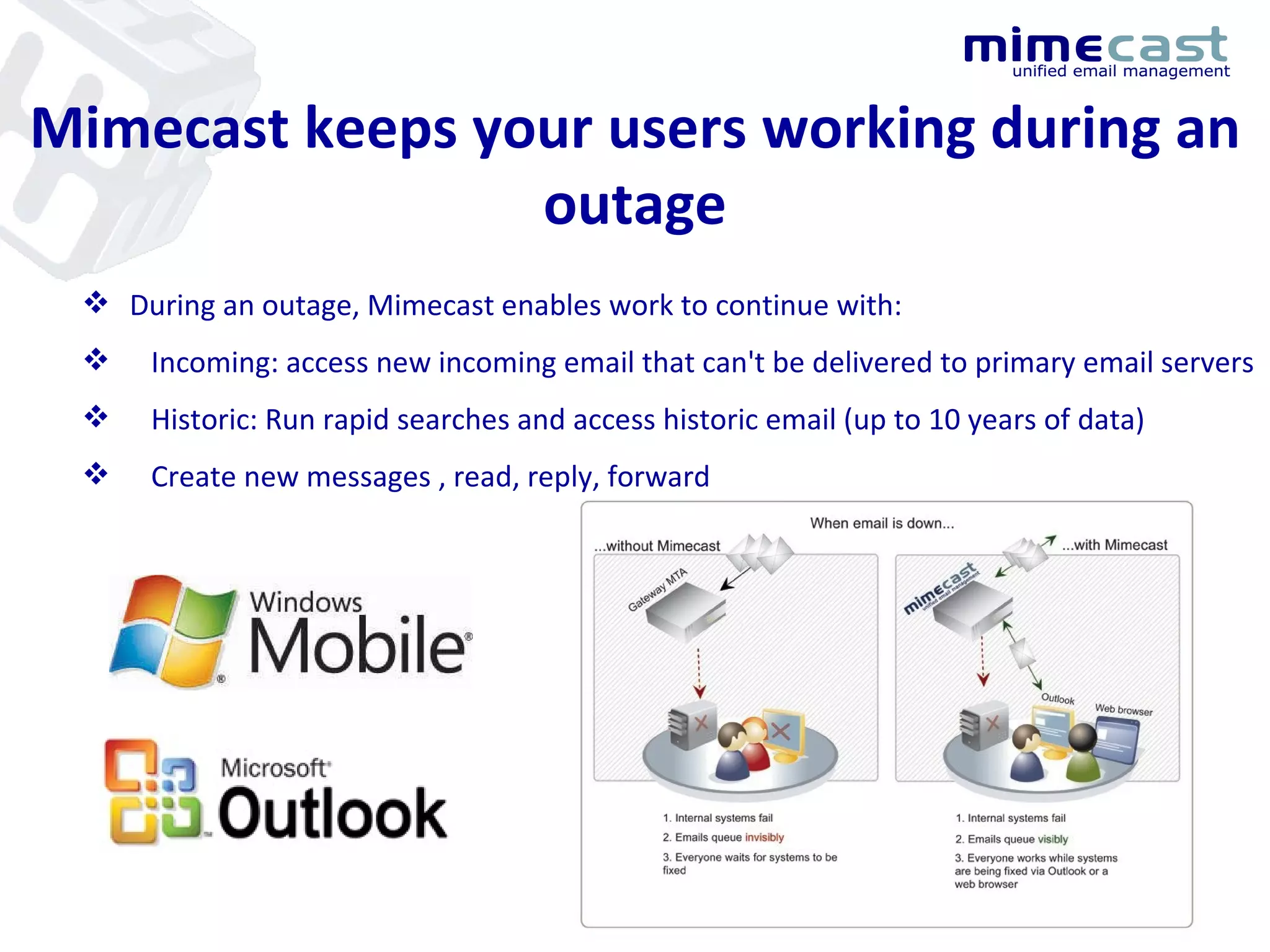
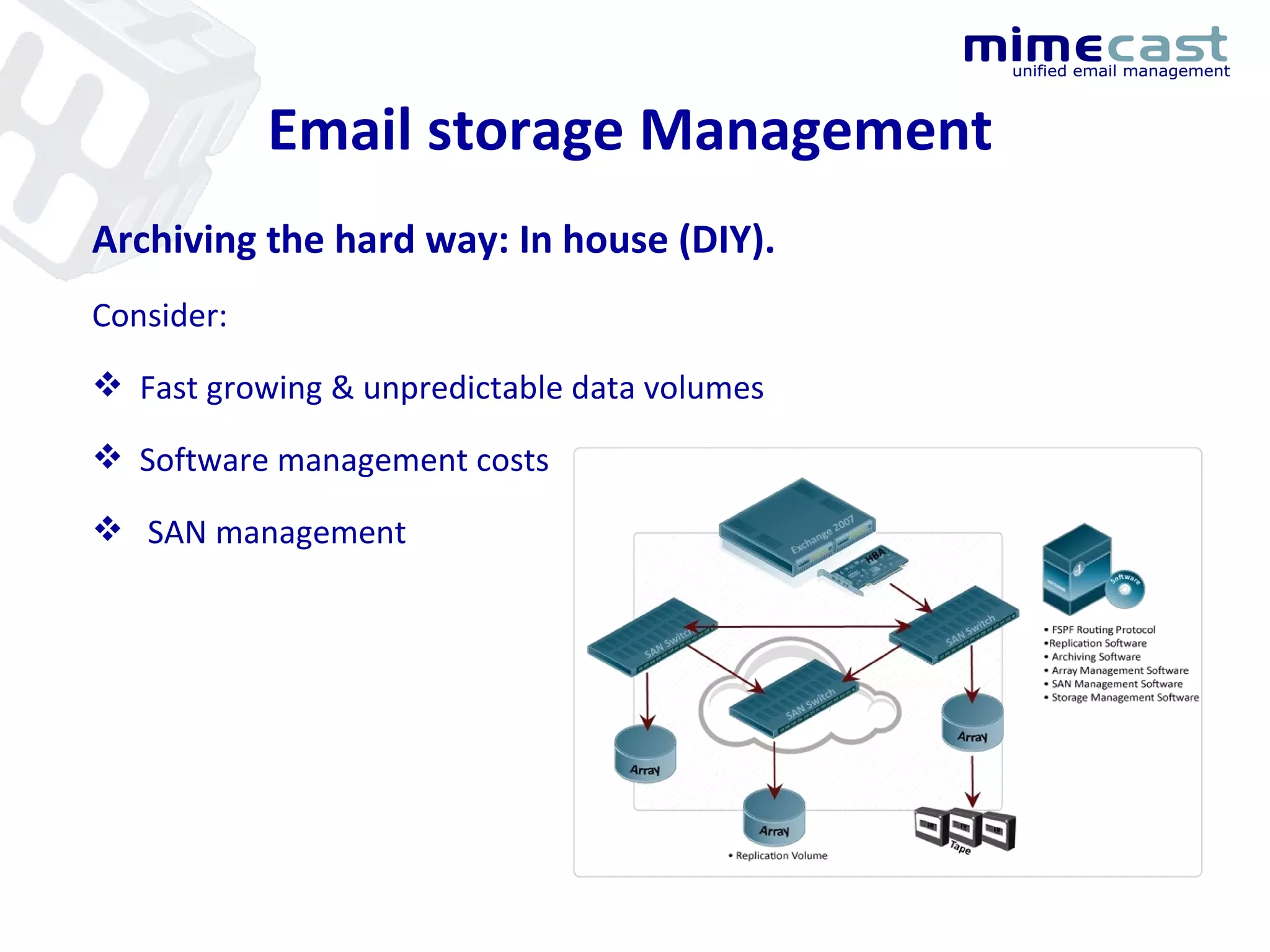
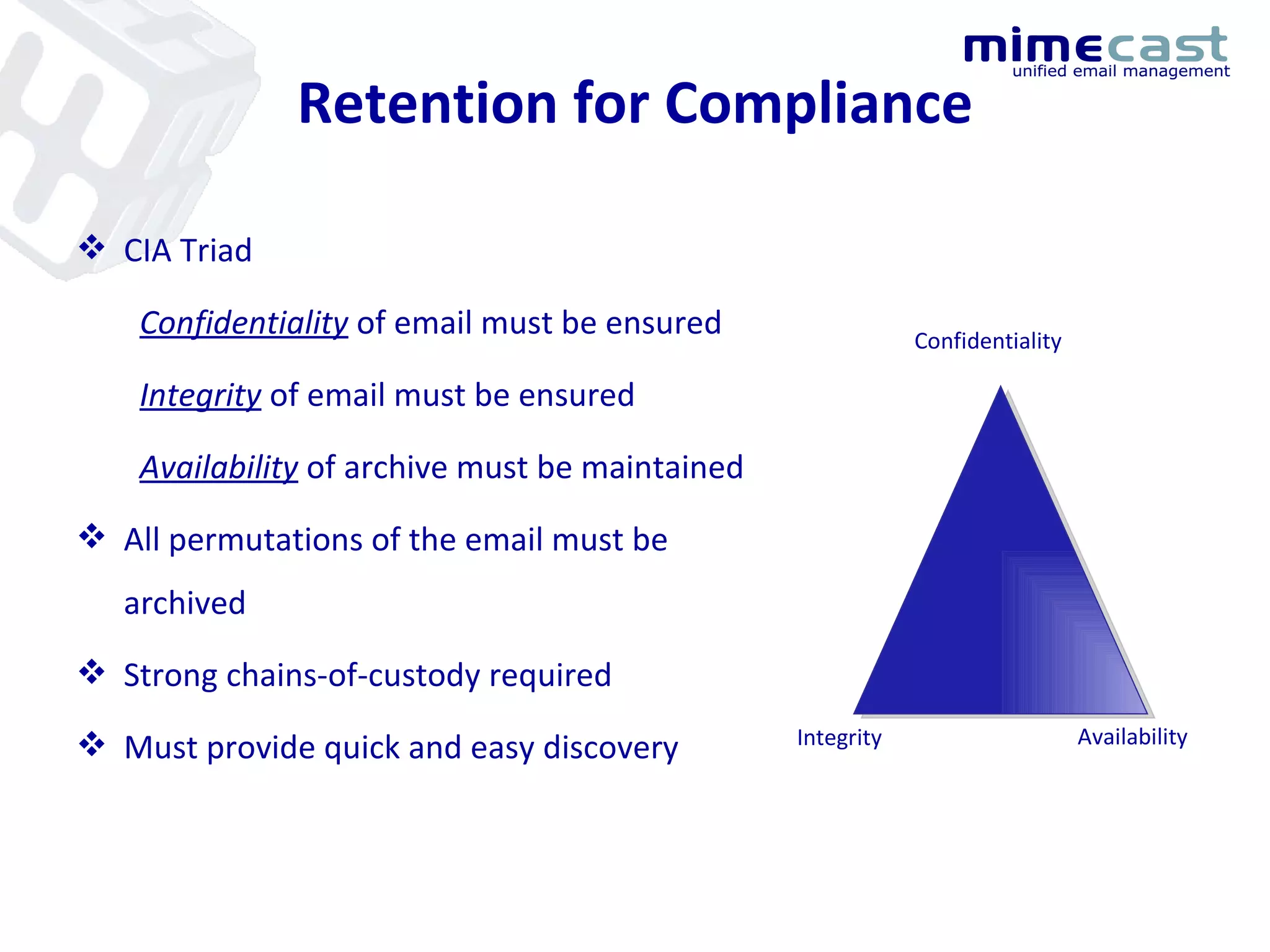
This document provides an agenda for a Mimecast company introduction presentation. The presentation will cover Mimecast's email security and archiving software-as-a-service, including its unified email management platform, continuity capabilities, compliance features, and customer case studies. Mimecast's solution aims to reduce costs and complexity for email management while providing security, archiving, e-discovery and other email functions through a single cloud-based platform.
![[email_address] +27(0)41 3640264 +27(0)711647617](https://image.slidesharecdn.com/mimecastsalespresentation-12976665481143-phpapp01/75/Mimecast-Presentation-1-2048.jpg)