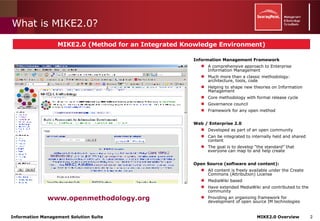
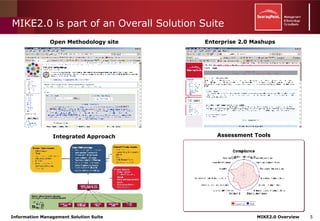
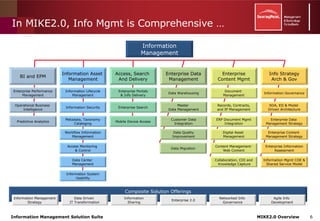
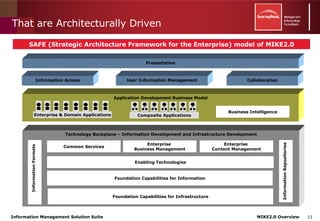
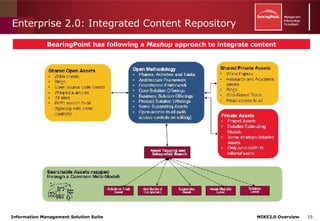
Mike2.0 is a comprehensive methodology aimed at improving enterprise information management through collaborative development and open-source solutions, addressing the complexities of data management and governance. It provides a structured framework for integrating information strategies, tools, and processes, focusing on standards and transparency to enhance data visibility and access. The initiative encourages community involvement to evolve solutions that tackle the challenges of modern information management.