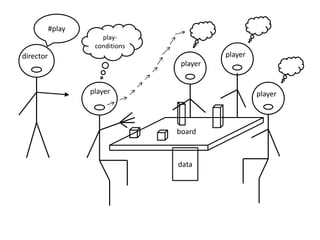
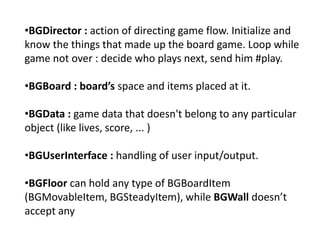
MetaBoard is a framework for board games that models the core components of many classic games like Pacman, Tetris, and Minesweeper. The framework represents games as a board space with items that move according to rules, similar to a board game played with physical pieces. It defines common player roles like moving pieces and tracking game state, and allows new games to be created by subclassing components like boards, pieces, data, and directors that orchestrate the game flow. Examples show how Pacman, Tetris, and Minesweeper could be implemented using the core framework components of players, boards, data, and directors.