Secure Computing Architecture for Medical Software System Application
•Download as DOC, PDF•
0 likes•594 views
One of several documents describing an earlier version of the Secure Computing InFrastructure (SCIF) architecture and embodiment for a medical applicaton
Report
Share
Report
Share
Recommended
Understanding basics of software development and healthcare

The document discusses key principles for designing software for healthcare applications. It covers understanding the different layers of software, following a software development life cycle, using object-oriented design principles and use case modeling to define system requirements and functionality. Centralizing electronic health records across different systems and locations is proposed to improve patient care, data availability and information sharing between stakeholders.
Health confidence HIS

Health Confidence is a comprehensive hospital management information systems by IDT consulting & Systems. The system is developed to work on the cloud using Java EE based on Oracle database. Health Confidence is available in multi language and available to run in a multi org environment.
Add posting content Birla

The document discusses hospital management software and lists various targeted keywords related to healthcare software and their competition levels and monthly searches. It also provides contact information for Birlamedisoft, a company that provides medical software solutions for hospitals, laboratories, blood banks and other healthcare establishments. The company offers both web-based and offline software for functions like hospital management, laboratory information systems, and blood bank management.
The Electronic Medical Record - David Beausang

The document discusses findings from visiting hospitals around the world regarding electronic medical records (EMRs). It finds that while EMRs aim to provide a single version of patient data, validation of data is also needed. It also notes the importance of analyzing EMR data to support business planning. However, few hospitals have fully implemented EMR systems, and smaller, rural, and independent hospitals tend to lag in adoption levels. Integration of systems and data adjudication are seen as keys to realizing the benefits of EMRs.
Presentation 2010 mMD EMR\\EHR

mMD.net is an electronic health record and practice management software with features including health information exchange, a patient portal, mobile access, and integration with other systems. It uses a services-oriented architecture and can automatically share patient medical records between providers to facilitate referrals and consultations.
Patient prescription management system

This document outlines a patient prescription management system project. It lists the project supervisor and team members. It describes problems with the current paper-based system like confusion of data and lack of patient history records. The goals of the project are to computerize prescriptions and connect pharmacies, doctors, and labs to create an electronic patient record system. The proposed solution is an online prescription app with a website database and mobile interfaces for doctors and patients. The app will allow viewing of a patient's medical history and management of prescriptions electronically.
IRJET- Analysis of Hospital Resources with Mortality Rates using Apriori ...

This document describes a study that uses the Apriori algorithm to analyze relationships between hospital resources and mortality rates. The study uses the Apriori algorithm to mine frequent item sets and association rules from a hospital database containing fields like number of doctors, nurses, beds, etc. and mortality rates. The algorithm aims to discover rules around how hospital resources correlate with mortality rates. The results could help hospitals identify areas to improve and lower mortality rates.
Hospital Management System Abstract 2017

Cloud computing as an emerging computing mode can be applied to the District Medical Data Center. This is a new proposal raised in the paper. The rudiment of District Medical Data Center based on cloud computing is established. A comparison is made between the samples from the rudiment and the samples from the general systems.
Recommended
Understanding basics of software development and healthcare

The document discusses key principles for designing software for healthcare applications. It covers understanding the different layers of software, following a software development life cycle, using object-oriented design principles and use case modeling to define system requirements and functionality. Centralizing electronic health records across different systems and locations is proposed to improve patient care, data availability and information sharing between stakeholders.
Health confidence HIS

Health Confidence is a comprehensive hospital management information systems by IDT consulting & Systems. The system is developed to work on the cloud using Java EE based on Oracle database. Health Confidence is available in multi language and available to run in a multi org environment.
Add posting content Birla

The document discusses hospital management software and lists various targeted keywords related to healthcare software and their competition levels and monthly searches. It also provides contact information for Birlamedisoft, a company that provides medical software solutions for hospitals, laboratories, blood banks and other healthcare establishments. The company offers both web-based and offline software for functions like hospital management, laboratory information systems, and blood bank management.
The Electronic Medical Record - David Beausang

The document discusses findings from visiting hospitals around the world regarding electronic medical records (EMRs). It finds that while EMRs aim to provide a single version of patient data, validation of data is also needed. It also notes the importance of analyzing EMR data to support business planning. However, few hospitals have fully implemented EMR systems, and smaller, rural, and independent hospitals tend to lag in adoption levels. Integration of systems and data adjudication are seen as keys to realizing the benefits of EMRs.
Presentation 2010 mMD EMR\\EHR

mMD.net is an electronic health record and practice management software with features including health information exchange, a patient portal, mobile access, and integration with other systems. It uses a services-oriented architecture and can automatically share patient medical records between providers to facilitate referrals and consultations.
Patient prescription management system

This document outlines a patient prescription management system project. It lists the project supervisor and team members. It describes problems with the current paper-based system like confusion of data and lack of patient history records. The goals of the project are to computerize prescriptions and connect pharmacies, doctors, and labs to create an electronic patient record system. The proposed solution is an online prescription app with a website database and mobile interfaces for doctors and patients. The app will allow viewing of a patient's medical history and management of prescriptions electronically.
IRJET- Analysis of Hospital Resources with Mortality Rates using Apriori ...

This document describes a study that uses the Apriori algorithm to analyze relationships between hospital resources and mortality rates. The study uses the Apriori algorithm to mine frequent item sets and association rules from a hospital database containing fields like number of doctors, nurses, beds, etc. and mortality rates. The algorithm aims to discover rules around how hospital resources correlate with mortality rates. The results could help hospitals identify areas to improve and lower mortality rates.
Hospital Management System Abstract 2017

Cloud computing as an emerging computing mode can be applied to the District Medical Data Center. This is a new proposal raised in the paper. The rudiment of District Medical Data Center based on cloud computing is established. A comparison is made between the samples from the rudiment and the samples from the general systems.
Hospital management system business case

This document presents a business case for developing a Hospital Management System (HMS) software. The HMS would allow patients located far from hospitals to get online medical advice and treatment recommendations. It would automate major hospital operations like storing and retrieving patient records and billing. Two alternatives are considered: 1) Creating a mobile app for basic functions and 2) Providing doctor contact numbers for emergencies. The document outlines requirements, assumptions, risks, and metrics to measure the project's success in increasing customers and returns within three years.
Hospital Management System

This document describes a management system for a simple hospital. It includes graphical user interfaces for administrators, doctors, receptionists, and nurses. The interfaces allow users to register patients, manage patient and staff information, handle appointments and prescriptions, track medicine and finances, and generate reports. The system aims to digitize and streamline key processes in hospital management.
Health Data Share Service System using REST

The International Journal of Engineering & Science is aimed at providing a platform for researchers, engineers, scientists, or educators to publish their original research results, to exchange new ideas, to disseminate information in innovative designs, engineering experiences and technological skills. It is also the Journal's objective to promote engineering and technology education. All papers submitted to the Journal will be blind peer-reviewed. Only original articles will be published.
IRJET-Cloud Based Patient Referral System

1) The document describes a cloud-based patient referral system that allows patients to upload, manage, and share their health information with healthcare providers.
2) It allows patients to select providers based on their profile, ratings, and effectiveness of treatment, and for providers to view patient records and comment on them remotely.
3) The system aims to save patients time and money by reducing the need to travel physically by facilitating remote consultations and file sharing through the cloud.
"Hospital Management"

This document describes a hospital management system created by a team of students. It includes an introduction describing the need for improved healthcare systems. It then outlines the team organization and roles, as well as key modules like inpatient details, outpatient details, and a cashier system. Data flow diagrams and an entity-relationship diagram are provided to visualize how the system will function and organize patient data. The goals are to streamline operations, maintain accurate records, and improve customer service. Sources consulted in creating the system are also cited.
Public health information technology standards overview

The document summarizes the history and initiatives around establishing standards for health information technology and exchange in the US federal government from 2003-2010. It describes the Consolidated Health Informatics initiative which adopted messaging and vocabulary standards to allow federal agencies to share health information. It also discusses the Health Information Technology Standards Panel which worked to harmonize standards to enable information sharing and the certification criteria established in 2010 to ensure electronic health records can meet standards and achieve meaningful use.
Healthcare information technology

The document discusses healthcare information technology and its evolution. It defines common terms like EMR, EHR, HIS, HL7, DICOM and PACS. It states that computerized physician order entry (CPOE) can significantly reduce medication errors and preventable adverse drug events. The hospital information system (HIS) is described as an integrated system that manages administrative, financial and clinical data across different departments. Several standards organizations are working to develop standards for interoperability between different health IT tools and electronic medical records.
Hunterdon-afb2c83b09250cd10d8b7d9c89a66924(1)

Hunterdon Healthcare is a healthcare system with 26 facilities across four New Jersey counties serving over 350,000 patients annually. They rely on InterSystems Ensemble to connect their hospital information systems, electronic health records, and practice management systems. This allows physicians both inside and outside of the hospital to access a complete picture of patient information including lab results, improving communication and coordination of care. Ensemble integration has eliminated information gaps, decreased unnecessary testing, and automated notifications to primary care physicians of patient admissions, leading to better patient outcomes and satisfaction.
Hospital management software presentataion

This document contains information about Quanta, a hospital management software solution developed by Birlamedisoft. It includes overviews and screenshots of the various modules in Quanta such as patient registration, OPD, IPD, billing, reports, inventory, pharmacy, pathology, radiology and PACS. The document also provides information on Quanta's system architecture, integration capabilities, interfaces and compliance with standards.
Srs hospital management

This document provides a summary of the requirements for a Hospital Management System software project. It outlines several key sections and modules of the software, including patient registration and records, a human resources module, accounting and inventory tracking. The system is intended to automate all operations of a hospital and provide relevant information to doctors, administrators, and other users. It will integrate various aspects of hospital management and replace manual record keeping. The document describes the intended users, system dependencies, interface requirements, and overall features and modules of the hospital management system.
[PPT] Hospital management system - Quanta-his![[PPT] Hospital management system - Quanta-his](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[PPT] Hospital management system - Quanta-his](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This document provides an overview of Birlamedisoft's Quanta hospital information management system (HIMS). It includes menus and descriptions for modules related to patient registration, billing, laboratory, radiology, pharmacy, inventory, housekeeping, and more. Graphics display sample interfaces for registration cards, dashboards, imaging controls, and connectivity to various medical devices. The system aims to manage all clinical, administrative and financial aspects of healthcare facilities.
KeyStandards_FinalPresentation_04162015

This document discusses key standards for health information exchange and interoperability. It describes three stages of meaningful use that aim to improve healthcare quality, safety, and privacy. The document also presents a case example where a patient's medical history from one hospital was unavailable during an emergency at another hospital due to lack of interoperability. It proposes a PHIT application that would enable data exchange between different electronic health record systems using standards like HL7, FHIR, and SNOMED to address this issue.
Integrated Hospital Management System

We, InnovativeBD team are here to serve you with our fully integrated and user friendly Hospital Management System
OpenERP Health & Hospital Management System

This document describes a health and hospital management system that provides electronic medical records, hospital information systems, and health information systems. It allows doctors to store patients' clinical histories, prescriptions, lab results, and more. Hospitals can use it to manage resources, employees, billing, and inventory. It also provides functionalities for laboratory tests, patient registration and appointments, genetics, gynecology, billing, and tracking patients' lifestyles and socioeconomic data. The system offers flexibility, integration, security, and scalability at no licensing cost to users.
Java presentation

This document outlines a presentation for a hospital management system created by five group members. It includes sections on contents, introduction, scope, advantages, system requirements, design, appointment list, personal information, limitations, and conclusion. The introduction describes the system's ability to register patients, store their details, and facilitate computerized billing. The scope specifies it can be used in hospitals, clinics, and labs. Advantages include immediate access to data, a friendly interface, and time savings.
Hospital IT

A hospital IT department should have four functional units: computer services, project management, IT application support and training, and web services. A well-developed IT department and system can provide many benefits to a hospital like improved quality, safety and efficiency of care as well as cost savings. Currently, IT adoption in Indian hospitals varies with some major hospitals having comprehensive systems while most others still rely on paper records. Overcoming barriers like costs and implementing strategies around interoperability and standards can help advance health IT in India.
Feasibility Study of Hospital Management System

Cost Benefit Analysis and Feasibility study of Hospital Management System is performed in Project management. Alternative solutions to problems of the Hospital Management System is created.
Electronic Health Records Integration with Corrections Case Management

It is through this consolidated view of an offender that line officers and case workers concerned with all aspects of security – inmate, staff and public – develop a knowledge and understanding of the individual inmate.
Patient record management system by custom soft

CustomSoft Patient Record Management System provides powerful features to take care of all requirements of any type of hospitals. This System has features to manage all the aspects of a medical record management.
OpenGL Based Testing Tool Architecture for Exascale Computing

1) The document proposes an OpenGL based testing tool architecture for exascale computing to improve performance and accuracy of OpenGL programs.
2) It identifies common errors that occur when programming shaders in OpenGL Shading Language (GLSL) such as errors in file reading, compilation, linking, and rendering.
3) The proposed testing architecture divides the GLSL programming process into four stages - file reading, compilation, pre-linking/linking, and rendering - and validates each stage to detect errors and enforce error-free code.
Get To Know The Benefits Of Architecture Project Management Software

A group of computer science students developed architecture project management software to help handle entire construction jobs. Such software allows sharing of resources to minimize individual costs and reduces redundancy. It is important for construction projects to have detailed drawings and to learn from previous versions of software instead of always updating to the newest releases, which may not have all beneficial features of earlier versions. Architecture project management software provides an efficient way to create detailed digital drawings and manage complex construction projects.
Agile architecture upload

This document provides an outline for an agile software architecture workshop. It begins by defining software architecture and describing key concepts like requirements, design principles, and architectural patterns. It emphasizes that architecture should enable agility by traveling light with just enough design. The document proposes techniques for agile architecture like architectural katas, risk analysis, and evolving the architecture over time with experiments. It concludes by providing an example architectural pitch for a restaurant ordering system that emphasizes high-level design, risks, and timelines.
More Related Content
What's hot
Hospital management system business case

This document presents a business case for developing a Hospital Management System (HMS) software. The HMS would allow patients located far from hospitals to get online medical advice and treatment recommendations. It would automate major hospital operations like storing and retrieving patient records and billing. Two alternatives are considered: 1) Creating a mobile app for basic functions and 2) Providing doctor contact numbers for emergencies. The document outlines requirements, assumptions, risks, and metrics to measure the project's success in increasing customers and returns within three years.
Hospital Management System

This document describes a management system for a simple hospital. It includes graphical user interfaces for administrators, doctors, receptionists, and nurses. The interfaces allow users to register patients, manage patient and staff information, handle appointments and prescriptions, track medicine and finances, and generate reports. The system aims to digitize and streamline key processes in hospital management.
Health Data Share Service System using REST

The International Journal of Engineering & Science is aimed at providing a platform for researchers, engineers, scientists, or educators to publish their original research results, to exchange new ideas, to disseminate information in innovative designs, engineering experiences and technological skills. It is also the Journal's objective to promote engineering and technology education. All papers submitted to the Journal will be blind peer-reviewed. Only original articles will be published.
IRJET-Cloud Based Patient Referral System

1) The document describes a cloud-based patient referral system that allows patients to upload, manage, and share their health information with healthcare providers.
2) It allows patients to select providers based on their profile, ratings, and effectiveness of treatment, and for providers to view patient records and comment on them remotely.
3) The system aims to save patients time and money by reducing the need to travel physically by facilitating remote consultations and file sharing through the cloud.
"Hospital Management"

This document describes a hospital management system created by a team of students. It includes an introduction describing the need for improved healthcare systems. It then outlines the team organization and roles, as well as key modules like inpatient details, outpatient details, and a cashier system. Data flow diagrams and an entity-relationship diagram are provided to visualize how the system will function and organize patient data. The goals are to streamline operations, maintain accurate records, and improve customer service. Sources consulted in creating the system are also cited.
Public health information technology standards overview

The document summarizes the history and initiatives around establishing standards for health information technology and exchange in the US federal government from 2003-2010. It describes the Consolidated Health Informatics initiative which adopted messaging and vocabulary standards to allow federal agencies to share health information. It also discusses the Health Information Technology Standards Panel which worked to harmonize standards to enable information sharing and the certification criteria established in 2010 to ensure electronic health records can meet standards and achieve meaningful use.
Healthcare information technology

The document discusses healthcare information technology and its evolution. It defines common terms like EMR, EHR, HIS, HL7, DICOM and PACS. It states that computerized physician order entry (CPOE) can significantly reduce medication errors and preventable adverse drug events. The hospital information system (HIS) is described as an integrated system that manages administrative, financial and clinical data across different departments. Several standards organizations are working to develop standards for interoperability between different health IT tools and electronic medical records.
Hunterdon-afb2c83b09250cd10d8b7d9c89a66924(1)

Hunterdon Healthcare is a healthcare system with 26 facilities across four New Jersey counties serving over 350,000 patients annually. They rely on InterSystems Ensemble to connect their hospital information systems, electronic health records, and practice management systems. This allows physicians both inside and outside of the hospital to access a complete picture of patient information including lab results, improving communication and coordination of care. Ensemble integration has eliminated information gaps, decreased unnecessary testing, and automated notifications to primary care physicians of patient admissions, leading to better patient outcomes and satisfaction.
Hospital management software presentataion

This document contains information about Quanta, a hospital management software solution developed by Birlamedisoft. It includes overviews and screenshots of the various modules in Quanta such as patient registration, OPD, IPD, billing, reports, inventory, pharmacy, pathology, radiology and PACS. The document also provides information on Quanta's system architecture, integration capabilities, interfaces and compliance with standards.
Srs hospital management

This document provides a summary of the requirements for a Hospital Management System software project. It outlines several key sections and modules of the software, including patient registration and records, a human resources module, accounting and inventory tracking. The system is intended to automate all operations of a hospital and provide relevant information to doctors, administrators, and other users. It will integrate various aspects of hospital management and replace manual record keeping. The document describes the intended users, system dependencies, interface requirements, and overall features and modules of the hospital management system.
[PPT] Hospital management system - Quanta-his![[PPT] Hospital management system - Quanta-his](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[PPT] Hospital management system - Quanta-his](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This document provides an overview of Birlamedisoft's Quanta hospital information management system (HIMS). It includes menus and descriptions for modules related to patient registration, billing, laboratory, radiology, pharmacy, inventory, housekeeping, and more. Graphics display sample interfaces for registration cards, dashboards, imaging controls, and connectivity to various medical devices. The system aims to manage all clinical, administrative and financial aspects of healthcare facilities.
KeyStandards_FinalPresentation_04162015

This document discusses key standards for health information exchange and interoperability. It describes three stages of meaningful use that aim to improve healthcare quality, safety, and privacy. The document also presents a case example where a patient's medical history from one hospital was unavailable during an emergency at another hospital due to lack of interoperability. It proposes a PHIT application that would enable data exchange between different electronic health record systems using standards like HL7, FHIR, and SNOMED to address this issue.
Integrated Hospital Management System

We, InnovativeBD team are here to serve you with our fully integrated and user friendly Hospital Management System
OpenERP Health & Hospital Management System

This document describes a health and hospital management system that provides electronic medical records, hospital information systems, and health information systems. It allows doctors to store patients' clinical histories, prescriptions, lab results, and more. Hospitals can use it to manage resources, employees, billing, and inventory. It also provides functionalities for laboratory tests, patient registration and appointments, genetics, gynecology, billing, and tracking patients' lifestyles and socioeconomic data. The system offers flexibility, integration, security, and scalability at no licensing cost to users.
Java presentation

This document outlines a presentation for a hospital management system created by five group members. It includes sections on contents, introduction, scope, advantages, system requirements, design, appointment list, personal information, limitations, and conclusion. The introduction describes the system's ability to register patients, store their details, and facilitate computerized billing. The scope specifies it can be used in hospitals, clinics, and labs. Advantages include immediate access to data, a friendly interface, and time savings.
Hospital IT

A hospital IT department should have four functional units: computer services, project management, IT application support and training, and web services. A well-developed IT department and system can provide many benefits to a hospital like improved quality, safety and efficiency of care as well as cost savings. Currently, IT adoption in Indian hospitals varies with some major hospitals having comprehensive systems while most others still rely on paper records. Overcoming barriers like costs and implementing strategies around interoperability and standards can help advance health IT in India.
Feasibility Study of Hospital Management System

Cost Benefit Analysis and Feasibility study of Hospital Management System is performed in Project management. Alternative solutions to problems of the Hospital Management System is created.
Electronic Health Records Integration with Corrections Case Management

It is through this consolidated view of an offender that line officers and case workers concerned with all aspects of security – inmate, staff and public – develop a knowledge and understanding of the individual inmate.
Patient record management system by custom soft

CustomSoft Patient Record Management System provides powerful features to take care of all requirements of any type of hospitals. This System has features to manage all the aspects of a medical record management.
What's hot (19)
Public health information technology standards overview

Public health information technology standards overview
Electronic Health Records Integration with Corrections Case Management

Electronic Health Records Integration with Corrections Case Management
Viewers also liked
OpenGL Based Testing Tool Architecture for Exascale Computing

1) The document proposes an OpenGL based testing tool architecture for exascale computing to improve performance and accuracy of OpenGL programs.
2) It identifies common errors that occur when programming shaders in OpenGL Shading Language (GLSL) such as errors in file reading, compilation, linking, and rendering.
3) The proposed testing architecture divides the GLSL programming process into four stages - file reading, compilation, pre-linking/linking, and rendering - and validates each stage to detect errors and enforce error-free code.
Get To Know The Benefits Of Architecture Project Management Software

A group of computer science students developed architecture project management software to help handle entire construction jobs. Such software allows sharing of resources to minimize individual costs and reduces redundancy. It is important for construction projects to have detailed drawings and to learn from previous versions of software instead of always updating to the newest releases, which may not have all beneficial features of earlier versions. Architecture project management software provides an efficient way to create detailed digital drawings and manage complex construction projects.
Agile architecture upload

This document provides an outline for an agile software architecture workshop. It begins by defining software architecture and describing key concepts like requirements, design principles, and architectural patterns. It emphasizes that architecture should enable agility by traveling light with just enough design. The document proposes techniques for agile architecture like architectural katas, risk analysis, and evolving the architecture over time with experiments. It concludes by providing an example architectural pitch for a restaurant ordering system that emphasizes high-level design, risks, and timelines.
Software Architecture and Project Management

The document discusses various archetype patterns related to modeling products, parties, and customer relationships in software applications. It describes archetypes for representing parties and their unique identifiers, as well as relationships between parties. Product archetypes are covered for modeling different types of products, identifiers like GTIN and ISBN, as well as packaging of multiple products together. The customer relationship management archetype pattern supports modeling customer communications and cases.
Modern Agile Software Architecture

Introduction 'Software Architecture'
Forms of Architecture
Architecture vs Design
Architectural Patterns
Design Patterns
Diagrams
Agile + Architecture
Principles - Architecture and Design
Recap
Conclusion
An architecture for effort estimation of solutions donatien koulla moulla

This document proposes an architecture for estimating the effort required for software projects based on open source software. It acknowledges that existing effort estimation models do not account for the differences in open source projects, including volunteer development teams and lack of formal management.
The proposed architecture includes estimating the effort to integrate open source components, the effort related to the number of code changes, and the effort related to code complexity. It also accounts for functional and non-functional requirements, as well as characteristics specific to open source software development like the voluntary nature of contributions. The total effort is estimated as the sum of efforts across each project activity.
Software Architecture and Agile: Is it Unrequited Love?

Nobody would argue that Agile software development and software architecture don't go hand in hand together, and yet it seems that the software architecture community is much more interested in agile topics than the agile community is in software architecture topics. Is this a case of unrequited love?
This presentation explores this question and explores a few possible reasons why this perception of unrequited love between software architecture and agile might exist.
CP7301 Software Process and Project Management notes

UNIT I DEVELOPMENT LIFE CYCLE PROCESSES 9
Overview of software development life cycle – introduction to processes – Personal Software
Process (PSP) – Team software process (TSP) – Unified processes – agile processes –
choosing the right process Tutorial: Software development using PSP
20
UNIT II REQUIREMENTS MANAGEMENT 9
Functional requirements and quality attributes – elicitation techniques – Quality Attribute
Workshops (QAW) – analysis, prioritization, and trade-off – Architecture Centric
Development Method (ACDM) – requirements documentation and specification – change
management – traceability of requirements
Tutorial: Conduct QAW, elicit, analyze, prioritize, and document requirements using ACDM
UNIT III ESTIMATION, PLANNING, AND TRACKING 9
Identifying and prioritizing risks – risk mitigation plans – estimation techniques – use case
points – function points – COCOMO II – top-down estimation – bottom-up estimation – work
breakdown structure – macro and micro plans – planning poker – wideband delphi –
documenting the plan – tracking the plan – earned value method (EVM)
Tutorial: Estimation, planning, and tracking exercises
UNIT IV CONFIGURATION AND QUALITY MANAGEMENT 9
identifying artifacts to be configured – naming conventions and version control –
configuration control – quality assurance techniques – peer reviews – Fegan inspection –
unit, integration, system, and acceptance testing – test data and test cases – bug tracking –
causal analysis
Tutorial: version control exercises, development of test cases, causal analysis of defects
UNIT V SOFTWARE PROCESS DEFINITION AND MANAGEMENT 9
Process elements – process architecture – relationship between elements – process
modeling – process definition techniques – ETVX (entry-task-validation-exit) – process
baselining – process assessment and improvement – CMMI – Six Sigma
Tutorial: process measurement exercises, process definition using ETVX
Microservices: Architecture to Support Agile

1. Microservices architecture divides applications into small, independent components called microservices that can be developed, deployed and scaled independently.
2. This architecture aligns well with agile principles by allowing individual teams to focus on and deploy their microservice without coordination, enabling faster feedback and continuous delivery of working software.
3. By structuring the organization around business domains rather than technical components, microservices help drive organizational communication patterns that mirror the architecture, avoiding misalignment over time.
1 - Architetture Software - Software as a product

This document discusses software as a product and industry. It covers how software is a key component in modern technologies and industries. The software industry has grown significantly in recent decades. The document discusses different types of software such as embedded software, middleware, and software as a service. It also covers topics like software architecture, engineering, components, ecosystems, and the challenges in developing software. Overall, the document provides an overview of software as an industrial product and the software development industry.
Software Architecture and Project Management module III : PATTERN OF ENTERPRISE

This document discusses various software architecture patterns. It begins by covering communication patterns, including the forward-receiver and client-dispatcher-server patterns. It then discusses structural patterns, including decorator, proxy, bridge, composite and others. For each pattern, it provides descriptions, examples, and UML diagrams. The document is focused on explaining different types of architectural patterns for software design.
Why We Need Architects (and Architecture) on Agile Projects

This is an updated version of this talk which I will present at Agile 2013.
The rhythm of agile software development is to always be working on the next known, small batch of work. Is there a place for software architecture in this style of development? Some people think that software architecture should simply emerge and doesn’t require ongoing attention. But it isn’t always prudent to let the software architecture emerge at the speed of the next iteration. Complex software systems have lots of moving parts, dependencies, challenges, and unknowns. Counting on the software architecture to spontaneously emerge without any planning or architectural investigation is at best risky.
So how should architecting be done on agile projects? It varies from project to project. But there are effective techniques for incorporating architectural activities into agile projects. This talk explains how architecture can be done on agile projects and what an agile architect does.
Software Architecture and Project Management Module II archetype pattern

The document discusses various archetype patterns including the Party archetype, Customer Relationship Management (CRM) archetype, and Product archetype.
The Party archetype represents people and organizations and captures essential information about them. The CRM archetype aims to manage relationships between businesses and customers to understand and increase customer value. It focuses on having a unified customer view.
The Product archetype models goods and services that businesses sell. There are three broad categories of products: unique things, identical things, and identifiable things. The archetype can be specialized into pleomorphs like UniqueProduct and IdenticalProduct depending on business needs.
8 - Architetture Software - Architecture centric processes

The document discusses architecture-centric software development processes. It describes traditional waterfall and iterative development models, and notes that iterative models allow for more flexibility to changing requirements. Agile development methods like eXtreme Programming (XP) are discussed, which emphasize iterative development, collaboration, and rapid delivery of working software. Key practices of XP are outlined, including user stories, testing, pair programming, refactoring, and continuous integration. The role of architecture in agile processes is also addressed.
Model-Driven Software Engineering in Practice - Chapter 4 - Model-Driven Arch...

Slides for the mdse-book.com chapter 4: MODEL DRIVEN ARCHITECTURE (MDA)
Complete set of slides now available:
Chapter 1 - http://www.slideshare.net/mbrambil/modeldriven-software-engineering-in-practice-chapter-1-introduction
Chapter 2 - http://www.slideshare.net/mbrambil/modeldriven-software-engineering-in-practice-chapter-2-mdse-principles
Chapter 3 - http://www.slideshare.net/jcabot/model-driven-software-engineering-in-practice-chapter-3-mdse-use-cases
Chapter 4 - http://www.slideshare.net/jcabot/modeldriven-software-engineering-in-practice-chapter-4
Chapter 5 - https://www.slideshare.net/mbrambil/modeldriven-software-engineering-in-practice-chapter-5-integration-of-modeldriven-in-development-processes
Chapter 6 - http://www.slideshare.net/jcabot/mdse-bookslideschapter6
Chapter 7 - http://www.slideshare.net/mbrambil/model-driven-software-engineering-in-practice-book-chapter-7-developing-your-own-modeling-language
Chapter 8 - http://www.slideshare.net/jcabot/modeldriven-software-engineering-in-practice-chapter-8-modeltomodel-transformations
Chapter 9 - https://www.slideshare.net/mbrambil/model-driven-software-engineering-in-practice-book-chapter-9-model-to-text-transformations-and-code-generation
Chapter 10 - http://www.slideshare.net/jcabot/mdse-bookslideschapter10managingmodels
This book discusses how approaches based on modeling can improve the daily practice of software professionals. This is known as Model-Driven Software Engineering (MDSE) or, simply, Model-Driven Engineering (MDE).
MDSE practices have proved to increase efficiency and effectiveness in software development. MDSE adoption in the software industry is foreseen to grow exponentially in the near future, e.g., due to the convergence of software development and business analysis.
This book is an agile and flexible tool to introduce you to the MDE and MDSE world, thus allowing you to quickly understand its basic principles and techniques and to choose the right set of MDE instruments for your needs so that you can start to benefit from MDE right away.
The first part discusses the foundations of MDSE in terms of basic concepts (i.e., models and transformations), driving principles, application scenarios and current standards, like the wellknown MDA initiative proposed by OMG (Object Management Group) as well as the practices on how to integrate MDE in existing development processes.
The second part deals with the technical aspects of MDSE, spanning from the basics on when and how to build a domain-specific modeling language, to the description of Model-to-Text and Model-to-Model transformations, and the tools that support the management of MDE projects.
The book covers introductory and technical topics, spanning definitions and orientation in the MD* world, metamodeling, domain specific languages, model transformations, reverse engineering, OMG's MDA, UML, OCL, ATL, QVT, MOF, Eclipse, EMF, GMF, TCS, xText.
http://www.mdse-book.com
Software architecture in an agile environment

These are the slides used for the webinar "Agile Architecture", speaker: Raffaeel Garofalo. Available here:
https://vimeo.com/42069572
Microservices: Architecture for Agile Software Development

This document discusses microservices architecture and how it enables agility. It defines microservices as small, independent units that can be developed and deployed autonomously. The document argues that microservices align with the principles of the Agile Manifesto by allowing teams to work independently, facilitating continuous delivery, and making the architecture adaptable to change. Some benefits outlined are improved scalability, maintainability, and ability to replace services easily. The conclusion is that by structuring an organization and software architecture around microservices, greater agility can be achieved compared to a monolithic architecture.
Enterprise Architecture & Project Portfolio Management 1/2

This document discusses the relationship between enterprise architecture (EA) and project and portfolio management (PPM). It argues that EA and PPM have different but complementary perspectives in helping an organization translate strategy into realized value through portfolios and projects. The document provides examples of how EA and PPM can collaborate more effectively by having EA guide the enterprise towards its target state while PPM drives the enterprise strategically forward. It also provides a sample collaboration model where EA and the project manager work together on project architecture.
Transforming Software Architecture for the 21st Century (September 2009)

Evolving an important theme I've been working on and presenting all year, this new deck summarizes how enterprise architecture and large scale technology-based business solutions must transform to be more effective in the 21st century.
Contains material on a hypothesis for what's wrong with today's EA as well as potential solutions of merit such as emergent architecture, WOA, enterprise REST, open supply chains (APIs), mashups, and other models.
Presented this week in Oslo Norway to Bouvet's enterprise architecture council.
(In Agile) Where Do All The Managers Go?

Management is so important on agile delivery teams that we do it every single day, but that doesn't imply that we
need team managers. Having said that, there are still some manager roles needed, albeit far fewer than in the past, when we scale agile both tactically and strategically within our IT organizations. So where do the rest of the
managers go?
This presentation examines what happens to traditional managers when their organization adopts agile and lean strategies. We work through the implications of several critical forces that enable us to thin out the ranks of middle management. First, agile methods push many technical management tasks into the hands of the team, thereby taking that work away from managers. Second, leadership tasks are assigned to new team roles such as the Product Owner, the Team Lead/Scrum Master, and the Architecture Owner. Third, the move away from a project-based mindset to a product-based one results in stable teams that require far less functional/resource management. Fourth, application of business intelligence technologies to implement automated team and portfolio dashboards reduces the need for manual status reporting.
Some management-oriented work remains. Teams that haven't yet automated reporting will find that someone needs to track and report progress. Large teams, also known as program teams, will likely need a Program Manager or more accurately a Program Coordinator. To support IT-level functions you are likely to need people in roles such as Portfolio Manager, Operations Manager, Help Desk Manager, and Community of Practice (CoP) Lead. Managers are still clearly needed, but in practice there tends to be far fewer management positions within agile organizations than what we find in traditional ones. This implies that many existing managers will need to reskill and transition into one of the new agile roles. The good news is that there is room for everyone within agile if they're willing to learn new skills and change with the times.
Viewers also liked (20)
OpenGL Based Testing Tool Architecture for Exascale Computing

OpenGL Based Testing Tool Architecture for Exascale Computing
Get To Know The Benefits Of Architecture Project Management Software

Get To Know The Benefits Of Architecture Project Management Software
An architecture for effort estimation of solutions donatien koulla moulla

An architecture for effort estimation of solutions donatien koulla moulla
Software Architecture and Agile: Is it Unrequited Love?

Software Architecture and Agile: Is it Unrequited Love?
CP7301 Software Process and Project Management notes

CP7301 Software Process and Project Management notes
Software Architecture and Project Management module III : PATTERN OF ENTERPRISE

Software Architecture and Project Management module III : PATTERN OF ENTERPRISE
Why We Need Architects (and Architecture) on Agile Projects

Why We Need Architects (and Architecture) on Agile Projects
Software Architecture and Project Management Module II archetype pattern

Software Architecture and Project Management Module II archetype pattern
8 - Architetture Software - Architecture centric processes

8 - Architetture Software - Architecture centric processes
Model-Driven Software Engineering in Practice - Chapter 4 - Model-Driven Arch...

Model-Driven Software Engineering in Practice - Chapter 4 - Model-Driven Arch...
Microservices: Architecture for Agile Software Development

Microservices: Architecture for Agile Software Development
Enterprise Architecture & Project Portfolio Management 1/2

Enterprise Architecture & Project Portfolio Management 1/2
Transforming Software Architecture for the 21st Century (September 2009)

Transforming Software Architecture for the 21st Century (September 2009)
Similar to Secure Computing Architecture for Medical Software System Application
Computer Information Systems and the Electronic Health Record

Paper-based health records are being replaced by electronic health records (EHRs) to improve patient care. A clinical information system (CIS) is a collection of applications that provides centralized access to patient information across locations. Choosing a CIS requires input from all users and consideration of costs, which can range from $1-2 million for small hospitals to over $1 billion for large hospitals. Ensuring security of patient data and regular system updates are also important factors in selecting and implementing a CIS/EHR.
Conceptual model final

This document proposes a two-step conceptual model for an anonymous patient-researcher matching system. It describes a three-user class account structure that allows patients to remain anonymous while still managing their data and preferences. The classes include anonymous users, confidential users who provide encrypted identity information, and physician/researcher users who are verified. It also outlines a four-step engagement method for anonymous communication between matched patients and researchers. The goal is to increase data quantity and quality for research by addressing privacy concerns and promoting trust in the system.
Computer based patient record for anaesthesia

The document discusses computer-based patient records for anesthesia. It notes that Cushing-Codman made the first ether chart for keeping anesthesia records. Computerization allows for easy retrieval of data which is an important advantage. Hospital information systems can have a monolithic or "best-in-breed" model. The monolithic system has smooth interoperability but some components may be inferior. Electronic health records provide tools for provider communication and access to population data for research. Specialty electronic health records have been developed including for anesthesia, emergency departments, and intensive care units.
Nur 3563 group project team 6 ehr

The document discusses various aspects of electronic health records (EHRs), including their components, cost, structure, safety considerations, and education. It describes the eight main components that make up an EHR: health information and data; results management; order entry management; decision support; electronic communication and connectivity; patient support; administrative processes; and reporting and population health management. It also addresses how to structure an EHR for ease of use, the costs associated with EHR software, implementation, hardware, and ongoing support, and the importance of safety measures to protect patient information. Finally, it outlines strategies for training all staff on a new EHR system in a short period of time.
Week 1 dq1

This document outlines training that could be provided to hospital staff to avoid improper access of celebrity health records. It proposes the following training:
1. During orientation, all employees who can access patient information must be trained on confidentiality, privacy and security rules.
2. Patients' information can only be accessed by staff directly involved in their treatment, and all access is logged.
3. Monthly audits of access records would detect any improper browsing of files. Violators would face discipline.
The training aims to educate staff and put accountability measures in place to ensure patients' confidential health information is appropriately protected.
Blockchain-Based AI-Assisted Hospital Management System

This document describes a proposed blockchain-based hospital management system that incorporates machine learning and other technologies. The system would allow hospitals to securely store patient medical records and enable patients to access their records anywhere. It also includes features for online prescription management, medicine purchasing, and data analytics to help governments and organizations monitor health trends. The system is designed to address issues with conventional systems by providing centralized, transparent access to data while preserving patient privacy through blockchain and other security measures.
Final case study

mMR is a mobile medical records application developed by Kloud Data that allows healthcare professionals to access patient records from mobile devices. The application provides access to a patient's full medical history, test results, prescriptions, notes and can be used to discharge patients. It has a user-friendly interface compatible with Android and iOS devices. The application ensures security by not storing patient data locally and requiring authentication. Implementing mMR provides doctors access to patient information anytime, improves hospital operations and supports high-quality patient care both inside and outside of hospitals.
Ehr by jessica austin, shaun baker, victoria blankenship and kayla boro

This document provides an overview of electronic health records (EHR) including what they are, key components, considerations for implementation, and security and costs. It discusses that EHRs provide a centralized digital patient record accessible by healthcare providers. The eight essential components that must be included are things like health information, order entry, decision support, and administrative functions. Proper implementation requires input from various stakeholders like medical staff, IT, and leadership. Security and privacy are also important considerations, as are the financial costs of purchasing and maintaining an EHR system.
PATIENT MANAGEMENT SYSTEM project

This document describes a patient management system project for a university. The system aims to automate a hospital's manual patient record keeping system. It will computerize patient, doctor, and hospital details to make record keeping more efficient. The system will allow scheduling appointments, tracking medical bills and patient rooms. It will generate reports on patient information and utilize databases to store records. Diagrams including data flow diagrams and entity-relationship diagrams are provided to illustrate the system's design and data structure.
Kairon overview

The document proposes an architecture and process for nationwide patient-centric consent management. It discusses the need for improved electronic consent management given the limitations of paper-based consent. The proposed approach uses an internet-based consent service that stores a patient's consent preferences in one place and can provide the most current preferences to any record holder. This allows patients to manage consent in a centralized way without needing to interact directly with each individual record holder. The proposed architecture aims to balance the needs of patients, providers, and other stakeholders to enable greater data sharing while respecting patient privacy preferences.
Audit trails

1) The document discusses the implementation of electronic medical records (EMRs) on mobile devices and the security risks this poses. It proposes adding audit checks throughout the EMR access and usage process to monitor for abnormal behavior.
2) Role-based access control (RBAC) is introduced to limit employee permissions to only what is needed for their role. This prevents unauthorized access to patient information.
3) While privacy of medical records is important, the document argues that patients should have access to their own records upon request rather than going through lengthy processes. However, most patients currently lack the health literacy to manage their own records securely.
Priv&security&profin electrcommunicationsrev9 23

This document summarizes privacy, security, and professionalism considerations for digital communications among health care professionals and between professionals and patients. It discusses how HIPAA and state laws apply to electronic communications. Encryption is recommended but not required under HIPAA. Professionals must take care to send information to the right recipient and patient. Communications should maintain professional standards regardless of format. Guidance from medical societies can help set policies for using digital tools. The document also briefly discusses FDA regulation of mobile medical apps and acceptance of data from patients.
Unified Medical Data Platform focused on Accuracy

An AI-based Decision Platform built using unified data model, incorporating systems biology topics for unit analysis using semi-supervised learning models
Scary acronyms

This document provides an overview of key regulatory and legal issues related to health IT, including various acronyms. It summarizes regulations from HIPAA, HITECH, the FTC, FDA, ECPA, SCA, FCC, and CMIA. HIPAA and HITECH establish privacy and security rules for health information. The FTC protects consumer privacy and enforces data breach notification. The FDA regulates medical devices, including some software. ECPA/SCA limit sharing of electronic communications. The FCC regulates communications carriers. CMIA is California's health privacy law.
MEDBLOCK

This document proposes a medical records management system called MedBlock that uses blockchain technology. The system aims to allow patients secure access to their medical information across different healthcare providers in an immutable and verifiable way. It also aims to help streamline the medical insurance claims process by allowing insurance agencies to securely access authenticated patient records and invoices on the system. The system would use blockchain properties like encryption, authentication, and smart contracts to record medical records and control access permissions. This could help reduce insurance fraud and improve the response time for claims. The proposed system aims to address current issues with medical record security, accessibility, and insurance claim processing.
Evaluation of A CIS

This is a group project for a BSN course on information and technology. i hope you enjoy it; we have worked hard on it throughout the course.
It's time for open source design in healthcare

From strategy to user interface to operational code, the best solutions are often found in the open-source design model which is consistent with the
philosophy of sharing best practices and innovations in care delivery to improve health, with benefits for individual patients as well as the entire population.
IRJET- MedBlock System for Securing Medical Records

This document proposes a blockchain-based system called MedBlock to securely store and share medical records. The system aims to address limitations in current healthcare record systems related to privacy, security and data sharing. MedBlock uses blockchain technology and encryption to securely record medical transactions in an immutable ledger. It allows doctors to upload encrypted medical records and patients to access and share records through decryption keys. The system architecture includes modules for doctors and patients. If implemented, MedBlock could provide more secure, private and tamper-proof management of healthcare data compared to traditional electronic medical record systems.
IRJET- MedBlock System for Securing Medical Records

This document proposes a blockchain-based system called MedBlock to securely store and share medical records.
The system aims to address limitations in current healthcare record systems by using blockchain for tamper-proof storage of encrypted medical data. It allows doctors and patients to access records while ensuring privacy and consent. The system architecture includes modules for doctors to add patient details and visit records, and for patients to view and share their medical history. If implemented, MedBlock could improve security, consent, and access to healthcare data compared to traditional electronic medical record systems.
Health Informatics, ambiquitous Devices for Health Monitoring

Health monitoring devices, Cloud application technologies helping Chronic Patients for Regular monitoring. Specially Diabeties, Cancer, High Blood pressures.
Similar to Secure Computing Architecture for Medical Software System Application (20)
Computer Information Systems and the Electronic Health Record

Computer Information Systems and the Electronic Health Record
Blockchain-Based AI-Assisted Hospital Management System

Blockchain-Based AI-Assisted Hospital Management System
Ehr by jessica austin, shaun baker, victoria blankenship and kayla boro

Ehr by jessica austin, shaun baker, victoria blankenship and kayla boro
IRJET- MedBlock System for Securing Medical Records

IRJET- MedBlock System for Securing Medical Records
IRJET- MedBlock System for Securing Medical Records

IRJET- MedBlock System for Securing Medical Records
Health Informatics, ambiquitous Devices for Health Monitoring

Health Informatics, ambiquitous Devices for Health Monitoring
More from W Fred Seigneur
1995 roads report_broschure-the_advent_of_client-server_telephony_networks

Robust Open Architecture Distributed Switching (ROADS) Model for voice switching.
ROADS and "Intelligent Networking" was to voice networks what Software Defined Networking (SDN) and "White Box Switches" are for Data Networking today.
Ashburn medical group screens

One of several documents describing an earlier version of the Secure Computing InFrastructure (SCIF) architecture and embodiment for a medical applicaton
Db relationships

One of several documents describing an earlier version of the Secure Computing InFrastructure (SCIF) architecture and embodiment for a medical applicaton
Mamouth white paper

This document provides a draft white paper from Mammoth, Inc. for Medsoft Medical Systems regarding a proposed secure system. It includes sections on requirements compliance, proposed system architecture, concept of operations, and draft privacy and security policies. The system would provide doctors with handheld devices integrated with security cards for encrypted and authenticated access to medical records and applications via the internet. All communications and access would be strictly controlled and monitored by the security cards and servers to ensure privacy, integrity and availability of patient data.
Fred GWU Grad Certificate class project

One of several documents describing an earlier version of the Secure Computing InFrastructure (SCIF) architecture and embodiment for a medical applicaton
Kick starter project secure computing infrastructure for real-time embedded ...

This document describes different pledge levels for supporting a project to develop a secure computing infrastructure for real-time embedded applications. Higher pledge levels provide increased benefits like acknowledgement in reports, project updates, merchandise, access to the development team, and at the highest levels, participation in project meetings and testing. The highest pledge level of $15,000 provides the opportunity for a computer vendor to supply development systems and participate in all platform development phases.
Cyber security innovation imho v5

This document discusses computer security innovation and proposes a Secure Computing Infrastructure (SCIF) as a foundational solution. Some key points:
- Current computer security approaches are unsustainable and non-scalable as they do not build security in from the beginning.
- Operating systems and applications lack basic immune systems and are not written robustly, leading to vulnerabilities.
- The document proposes a SCIF that uses components like the Parallella board running seL4 microkernel with Erlang virtual machine to securely run applications and provide fault tolerance.
- A phased approach is outlined to prototype and field trial the SCIF as a more secure computing foundation.
Cyber security innovation_imho v4

This document summarizes Fred Seigneur's presentation on computer security innovation at the 2014 Cybersecurity Innovation Forum. The presentation discussed foundational weaknesses in current operating systems and applications due to a lack of built-in security. It proposed that developing a Secure Computing Infrastructure (SCI) using a separation kernel, Erlang virtual machine, and hardware security could help address these weaknesses by building security in from the beginning. A phased approach was outlined to develop an SCI prototype using the Parallella board.
Cyber Security Innovation IMHO v4

A presentation on securing cyberspace, starting with the Foundation
Cyber security innovation imho

This document discusses weaknesses in current computer security approaches and proposes a new "Secure Computing Infrastructure" (SCI) approach. It notes that operating systems and applications currently lack basic immune systems to defend against attacks. The SCI would integrate existing components like a separation kernel and Erlang virtual machine to create a more secure fault-tolerant environment. A phased approach is proposed beginning with a feasibility study and moving to proof of concept, field trials, and eventual full implementation. The goal is to develop a foundational security solution that is taught more widely in education.
Kingdom ofgod

The document discusses meditations on the Kingdom of God presented by Fred Seigneur to the Tuesday Home Group. It defines the Kingdom of God as the dominion or domain of God, which includes the spiritual realm over which God reigns as sovereign. It explores how one can see and enter the Kingdom by being born again of water and spirit. The Kingdom of God is likened to many believers linking up through yielding control of their lives to God, represented by cell phone towers or satellite beams providing coverage. This state of being in the Kingdom places one under the protection of God's wings.
More from W Fred Seigneur (14)
1995 roads report_broschure-the_advent_of_client-server_telephony_networks

1995 roads report_broschure-the_advent_of_client-server_telephony_networks
Kick starter project secure computing infrastructure for real-time embedded ...

Kick starter project secure computing infrastructure for real-time embedded ...
Recently uploaded
Recycled Concrete Aggregate in Construction Part III

Using recycled concrete aggregates (RCA) for pavements is crucial to achieving sustainability. Implementing RCA for new pavement can minimize carbon footprint, conserve natural resources, reduce harmful emissions, and lower life cycle costs. Compared to natural aggregate (NA), RCA pavement has fewer comprehensive studies and sustainability assessments.
22CYT12-Unit-V-E Waste and its Management.ppt

Introduction- e - waste – definition - sources of e-waste– hazardous substances in e-waste - effects of e-waste on environment and human health- need for e-waste management– e-waste handling rules - waste minimization techniques for managing e-waste – recycling of e-waste - disposal treatment methods of e- waste – mechanism of extraction of precious metal from leaching solution-global Scenario of E-waste – E-waste in India- case studies.
Optimizing Gradle Builds - Gradle DPE Tour Berlin 2024

Sinan from the Delivery Hero mobile infrastructure engineering team shares a deep dive into performance acceleration with Gradle build cache optimizations. Sinan shares their journey into solving complex build-cache problems that affect Gradle builds. By understanding the challenges and solutions found in our journey, we aim to demonstrate the possibilities for faster builds. The case study reveals how overlapping outputs and cache misconfigurations led to significant increases in build times, especially as the project scaled up with numerous modules using Paparazzi tests. The journey from diagnosing to defeating cache issues offers invaluable lessons on maintaining cache integrity without sacrificing functionality.
ISPM 15 Heat Treated Wood Stamps and why your shipping must have one

For International shipping and maritime laws all wood must contain the ISPM 15 Stamp. Here is how and why.
Understanding Inductive Bias in Machine Learning

This presentation explores the concept of inductive bias in machine learning. It explains how algorithms come with built-in assumptions and preferences that guide the learning process. You'll learn about the different types of inductive bias and how they can impact the performance and generalizability of machine learning models.
The presentation also covers the positive and negative aspects of inductive bias, along with strategies for mitigating potential drawbacks. We'll explore examples of how bias manifests in algorithms like neural networks and decision trees.
By understanding inductive bias, you can gain valuable insights into how machine learning models work and make informed decisions when building and deploying them.
ACEP Magazine edition 4th launched on 05.06.2024

This document provides information about the third edition of the magazine "Sthapatya" published by the Association of Civil Engineers (Practicing) Aurangabad. It includes messages from current and past presidents of ACEP, memories and photos from past ACEP events, information on life time achievement awards given by ACEP, and a technical article on concrete maintenance, repairs and strengthening. The document highlights activities of ACEP and provides a technical educational article for members.
DEEP LEARNING FOR SMART GRID INTRUSION DETECTION: A HYBRID CNN-LSTM-BASED MODEL

As digital technology becomes more deeply embedded in power systems, protecting the communication
networks of Smart Grids (SG) has emerged as a critical concern. Distributed Network Protocol 3 (DNP3)
represents a multi-tiered application layer protocol extensively utilized in Supervisory Control and Data
Acquisition (SCADA)-based smart grids to facilitate real-time data gathering and control functionalities.
Robust Intrusion Detection Systems (IDS) are necessary for early threat detection and mitigation because
of the interconnection of these networks, which makes them vulnerable to a variety of cyberattacks. To
solve this issue, this paper develops a hybrid Deep Learning (DL) model specifically designed for intrusion
detection in smart grids. The proposed approach is a combination of the Convolutional Neural Network
(CNN) and the Long-Short-Term Memory algorithms (LSTM). We employed a recent intrusion detection
dataset (DNP3), which focuses on unauthorized commands and Denial of Service (DoS) cyberattacks, to
train and test our model. The results of our experiments show that our CNN-LSTM method is much better
at finding smart grid intrusions than other deep learning algorithms used for classification. In addition,
our proposed approach improves accuracy, precision, recall, and F1 score, achieving a high detection
accuracy rate of 99.50%.
Computational Engineering IITH Presentation

This Presentation will give you a brief idea about what Computational Engineering at IIT Hyderabad has to offer.
Harnessing WebAssembly for Real-time Stateless Streaming Pipelines

Traditionally, dealing with real-time data pipelines has involved significant overhead, even for straightforward tasks like data transformation or masking. However, in this talk, we’ll venture into the dynamic realm of WebAssembly (WASM) and discover how it can revolutionize the creation of stateless streaming pipelines within a Kafka (Redpanda) broker. These pipelines are adept at managing low-latency, high-data-volume scenarios.
2008 BUILDING CONSTRUCTION Illustrated - Ching Chapter 02 The Building.pdf

2008 BUILDING CONSTRUCTION Illustrated - Ching Chapter 02 The Building
Literature Review Basics and Understanding Reference Management.pptx

Three-day training on academic research focuses on analytical tools at United Technical College, supported by the University Grant Commission, Nepal. 24-26 May 2024
Recycled Concrete Aggregate in Construction Part II

Using recycled concrete aggregates (RCA) for pavements is crucial to achieving sustainability. Implementing RCA for new pavement can minimize carbon footprint, conserve natural resources, reduce harmful emissions, and lower life cycle costs. Compared to natural aggregate (NA), RCA pavement has fewer comprehensive studies and sustainability assessments.
Recently uploaded (20)
basic-wireline-operations-course-mahmoud-f-radwan.pdf

basic-wireline-operations-course-mahmoud-f-radwan.pdf
Recycled Concrete Aggregate in Construction Part III

Recycled Concrete Aggregate in Construction Part III
Optimizing Gradle Builds - Gradle DPE Tour Berlin 2024

Optimizing Gradle Builds - Gradle DPE Tour Berlin 2024
ISPM 15 Heat Treated Wood Stamps and why your shipping must have one

ISPM 15 Heat Treated Wood Stamps and why your shipping must have one
DEEP LEARNING FOR SMART GRID INTRUSION DETECTION: A HYBRID CNN-LSTM-BASED MODEL

DEEP LEARNING FOR SMART GRID INTRUSION DETECTION: A HYBRID CNN-LSTM-BASED MODEL
Harnessing WebAssembly for Real-time Stateless Streaming Pipelines

Harnessing WebAssembly for Real-time Stateless Streaming Pipelines
2008 BUILDING CONSTRUCTION Illustrated - Ching Chapter 02 The Building.pdf

2008 BUILDING CONSTRUCTION Illustrated - Ching Chapter 02 The Building.pdf
Engineering Drawings Lecture Detail Drawings 2014.pdf

Engineering Drawings Lecture Detail Drawings 2014.pdf
Literature Review Basics and Understanding Reference Management.pptx

Literature Review Basics and Understanding Reference Management.pptx
Recycled Concrete Aggregate in Construction Part II

Recycled Concrete Aggregate in Construction Part II
Generative AI leverages algorithms to create various forms of content

Generative AI leverages algorithms to create various forms of content
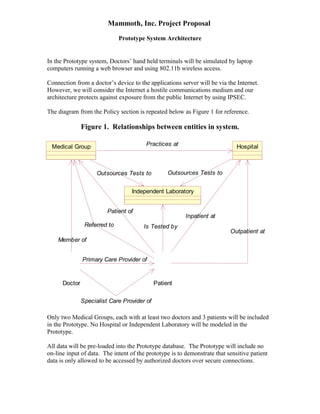
Secure Computing Architecture for Medical Software System Application
- 1. Mammoth, Inc. Project Proposal Prototype System Architecture In the Prototype system, Doctors’ hand held terminals will be simulated by laptop computers running a web browser and using 802.11b wireless access. Connection from a doctor’s device to the applications server will be via the Internet. However, we will consider the Internet a hostile communications medium and our architecture protects against exposure from the public Internet by using IPSEC. The diagram from the Policy section is repeated below as Figure 1 for reference. Figure 1. Relationships between entities in system. Medical Group Referred to Member of Doctor Hospital Practices at Outsources Tests to Outsources Tests to Independent Laboratory Is Tested by Patient Outpatient at Inpatient at Patient of Primary Care Provider of Specialist Care Provider of Only two Medical Groups, each with at least two doctors and 3 patients will be included in the Prototype. No Hospital or Independent Laboratory will be modeled in the Prototype. All data will be pre-loaded into the Prototype database. The Prototype will include no on-line input of data. The intent of the prototype is to demonstrate that sensitive patient data is only allowed to be accessed by authorized doctors over secure connections.
- 2. Mammoth, Inc. Project Proposal Prototype System Architecture Figure 2 below shows the logical architecture of the prototype. Figure 2. Prototype Logical Architecture Since the equipment in the logical prototype will likely is not available, the prototype physical architecture is shown in Figure 3 below. Laptops will be used to simulate each of two doctors from two Medical Groups. One host will serve web pages for both Medical Groups.
- 3. Mammoth, Inc. Project Proposal Prototype System Architecture Figure 3. Prototype Physical Architecture Data will be stored on disk on the Linux host. Doctors will authenticate themselves using userid and password. Data will only be provided to Doctors who are authorized to access it, based on their login. SSL or other encryption will protect all data transfers from being observed while it traverses the Internet or the wireless Access Point. Furthermore sensitive patient data will only be transmitted using PGP encryption using the public key of the Doctor who is logged in. Thus, even if an authorized Doctor’s userid and password are compromised, the data will be useless unless the perpetrator alsh has the Doctor’s private key and pass phrase. Appropriate PGP keys will be installed on devices for each doctor. If an unauthorized user acquires the laptop the thief will still need the doctor’s userid, password and pass-phrase.
- 4. Exhibit A Privacy Policy In the case of medical information, the issue is potential violation of the Doctor-Patient confidence, which is a privilege protected by law. The violation of this privilege can result in loss of a doctor’s or group of doctor’s right to practice medicine as well as damage suits from patients, and possible criminal charges. Therefore, we make the following assumptions: · Doctors, Hospitals, Labs and their professional and support personnel are aware of the risks of violating patient privacy. The requirement on Medsoft/Mammoth is to ensure that automated systems developed and marketed by the Medsoft/Mammoth team do not compromise Doctor-Patient Privilege. · Individual client organizations (Doctors’ Offices) may exercise their own Privacy Policy. Individual users, who are certified by the procedures and mechanisms described in the Concept of Operations and elsewhere in this document, are at liberty to reveal or protect information obtained from automated systems just as they are with existing paper and automated records. Description of Subjects and Objects In order to define a Privacy Policy, we first defined Subjects, Objects and Relationships, which were then used to create rules defining cases where it is acceptable for information relating to a specific patient to be revealed to a particular Medical Group/Doctor. The diagram below is an initial model of the entities involved in transactions involving Medsoft. The principal actors (subjects) are the Doctor and the Patient. The objects to be protected are medical records relating to individual patients. Other entities in the model are Medical Groups, Hospitals and Independent Laboratories. Sensitive patient information is maintained by each of these entities, with all rights to such information being authorized by the Patient and protected by Doctor-Patient Privilege. A-1 Mammoth, Inc. Proprietary Information
- 5. Exhibit A Privacy Policy Practices at Outsources Tests to Outsources Tests to Is Tested by Medical Group Referred to Member of Patient of Each Patient has at least (and most often only) one Primary Care Physician. Normally insurance companies require that there be a single Primary Care Physician, although the Patient has the right to create this relationship with more than one Doctor. This model accommodates such a situation, however, in this case the Privacy Policy permits Patient information to be shared only by written consent of the Patient. Within this model, all doctors are considered to belong to one and only one Medical Group. Doctors who provide service independently from such a group are considered to belong to a group of one, that particular Doctor’s practice. Other Medical Groups/Doctors may provide specialist care to the patient after a referral from the patient’s Doctor. While a Patient has the right to consul a specialist independently (without being referred by a Primary Care Physician), this case is modeled identically to the case where a Patient independently consults more than one Medical Group/Doctor. A-2 Mammoth, Inc. Proprietary Information Doctor Hospital Independent Laboratory Patient Outpatient at Inpatient at Primary Care Provider of Specialist Care Provider of
- 6. Exhibit A Privacy Policy Hospitals provide inpatient and outpatient care to Patients. The inpatient or outpatient relationship between Patient and Hospital is established by the Doctor’s act of admitting the Patient to the Hospital (as an inpatient), or referring the Patient to the Hospital for outpatient services. The authority to admit Patients to a Hospital is based on the fact that one or more Doctors in a Medical Group Practices at a particular Hospital. Similarly, a Doctor who is a Member of a Medical Group may (through the Medical Group) Outsource Tests to an Independent Laboratory. The term Independent Laboratory is a generic term for all such organizations that do blood work, x-rays, etc. Such organizations may also provide interpretative services (such as a radiologist’s reading of an X-ray or Cat Scan). Patient Information Access Policy Patient Information Stored by Patient Information Provided to Access to Patient Information Permitted Only If Medical Group Doctor Doctor is currently a Member of Medical Group AND Patient is currently a Patient of Medical Group Hospital Medical Group Patient was admitted as an Inpatient at Hospital by a Doctor who is a Member of the requesting Medical Group which Practices at the Hospital OR Patient was referred as an Outpatient at Hospital by a Doctor who is a Member of a Medical Group which Practices at the Hospital OR Patient authorizes information release by Hospital to Medical Group (in writing). A-3 Mammoth, Inc. Proprietary Information
- 7. Exhibit A Privacy Policy Patient Information Access Policy Patient Information Stored by Patient Information Provided to Access to Patient Information Permitted Only If Independent Laboratory Medical Group Note: parentheses below denote grouping of logical operations (The requesting Medical Group Outsources Tests to Independent Laboratory for Patient. AND The specific test(s) for the specific Patient for which results are being requested was/were outsourced to the Independent Laboratory by a Doctor who is a Member of the requesting Medical Group) OR Patient authorizes information release by Independent Laboratory to Medical Group (in writing). Medical Group Other Medical Group Patient was Referred to the other Medical Group by a Doctor who is a Member of the requesting Medical Group OR Patient authorizes the other Medical Group to release information to the requesting Medical Group (in writing). A-4 Mammoth, Inc. Proprietary Information
- 8. Exhibit B Security Policy All access to and modification to information secured under this Security Policy will: · Be limited to authorized individuals and procedures protected under the Security Mechanisms, which implement the Privacy Policy defined in Exhibit A, above and this Security Policy. · Be in accordance with the Clark-Wilson Integrity Model, which is restated (from the referenced document) for clarity in Tables 1, 2 and 3 below. The Draft System Architecture document, above, explains how trusted Transformation Procedures (TPs) are developed using Mammoth’s development procedures and executed in a secure environment, using the Mammoth Secure Server Card (SSC). More details will be provided in the next draft of this White Paper. Table 1 Clark-Wilson Integrity Model Definitions Acronym Expansion Meaning CDI Constrained Data Item A set of data items that have been validated (by a TP) and are in accordance with specifications. IVP Integrity Verification Procedure An integrity verification procedure is used to demonstrate that CDIs are valid and are in accordance with specifications. IVPs can be computer code or they can be manual procedures. Audit work programs are classic examples of IVPs, as are input validation programs. TP Transformation Procedure A transformation procedure transforms a set of valid data items (CDI) into another valid set. It may also transform non-validated data items (UDI) into valid data (CDI). This means that a transformation procedure must itself have the properties of a CDI. UDI Unconstrained Data Item A UDI is a set of data items that have not been validated or proved to comply with specifications. B-1 Mammoth, Inc. Proprietary Information
- 9. Exhibit B Security Policy Table 2 Clark-Wilson Integrity Model The Five Certification Rules Rule Number Rule C1 All IVP’s must properly ensure that all CDI’s are in a valid state at the time the IVP is run. C2 All TP’s must be certified to be valid. That is, they must take a CDI to a valid final state, given that it is in a valid state to begin with. For each TP, and each set of CDI’s that it may manipulate, the Security Officer must specify a “relation”, defines that execution. A relation is thus of the form: (TPi, (CDIa, CDIb, CDIc...)), where the list of CDI’s defines a particular set of arguments for which the TP has been certified. C3 The list of relations in E2 must be certified to meet the separation of duty requirement. C4 All TP’s must be certified to write to an append-only CDI (the log) all information necessary to permit the nature of the operation to be reconstructed. C5 Any TP that takes a UDI as an input value must be certified to perform only valid transformation, or else no transformations, for any possible value of the UDI. The transformation should take the input from a UDI to a CDI, or the UDI commercial is rejected. B-2 Mammoth, Inc. Proprietary Information
- 10. Exhibit B Security Policy Table 3 Clark-Wilson Integrity Model The Four Enforcement Rules Rule Number Rule E1 The system must maintain the list of relations specified in rule C2, and must ensure that the only manipulation of any CDI is by a TP, where the TP is operating on the CDI as specified in some relation. E2 The system must maintain a list of relationships of the form: (UserID, TPi, (CDIa, CDIb, CDIc.)), which relates to a user, a TP, and the data objects that TP may reference on behalf of that user. It must ensure that only executions described in one of the relations are performed. E3 The system must authenticate the identity of each user attempting to execute a TP. E4 Only the agent permitted to certify entities may change the list of such entities associated with other entities: specifically, the list of TP’s associated with a CDI and the list of users associated with a TP. An agent that can certify an entity may not have any execute rights with respect to that entity. B-3 Mammoth, Inc. Proprietary Information
