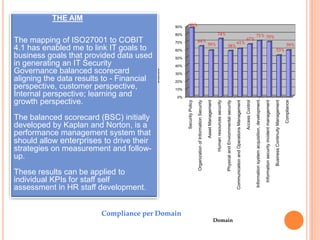
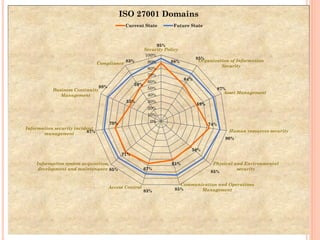
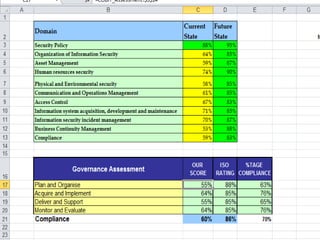
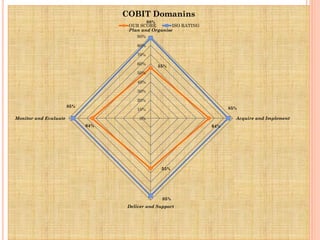
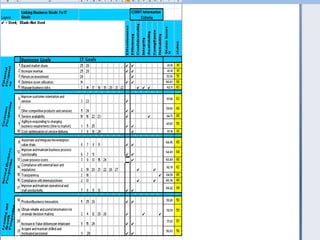
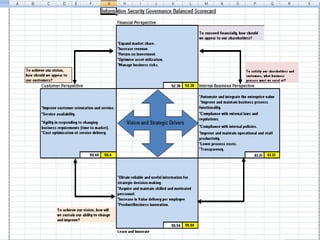
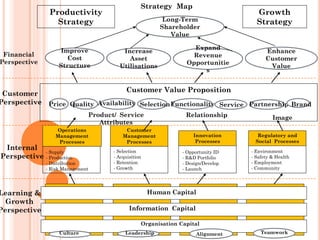
This document discusses mapping the ISO27001 information security standard to the COBIT 4.1 framework for enterprise governance and risk management. The mapping was used to generate a balanced scorecard for IT security governance. Current compliance levels for ISO27001 domains were measured at 64-88%. Future targets of 85-95% compliance were set. The balanced scorecard approach links IT security goals to business goals across financial, customer, internal process, and learning/growth perspectives. Individual staff can use the results for self-assessment and development.