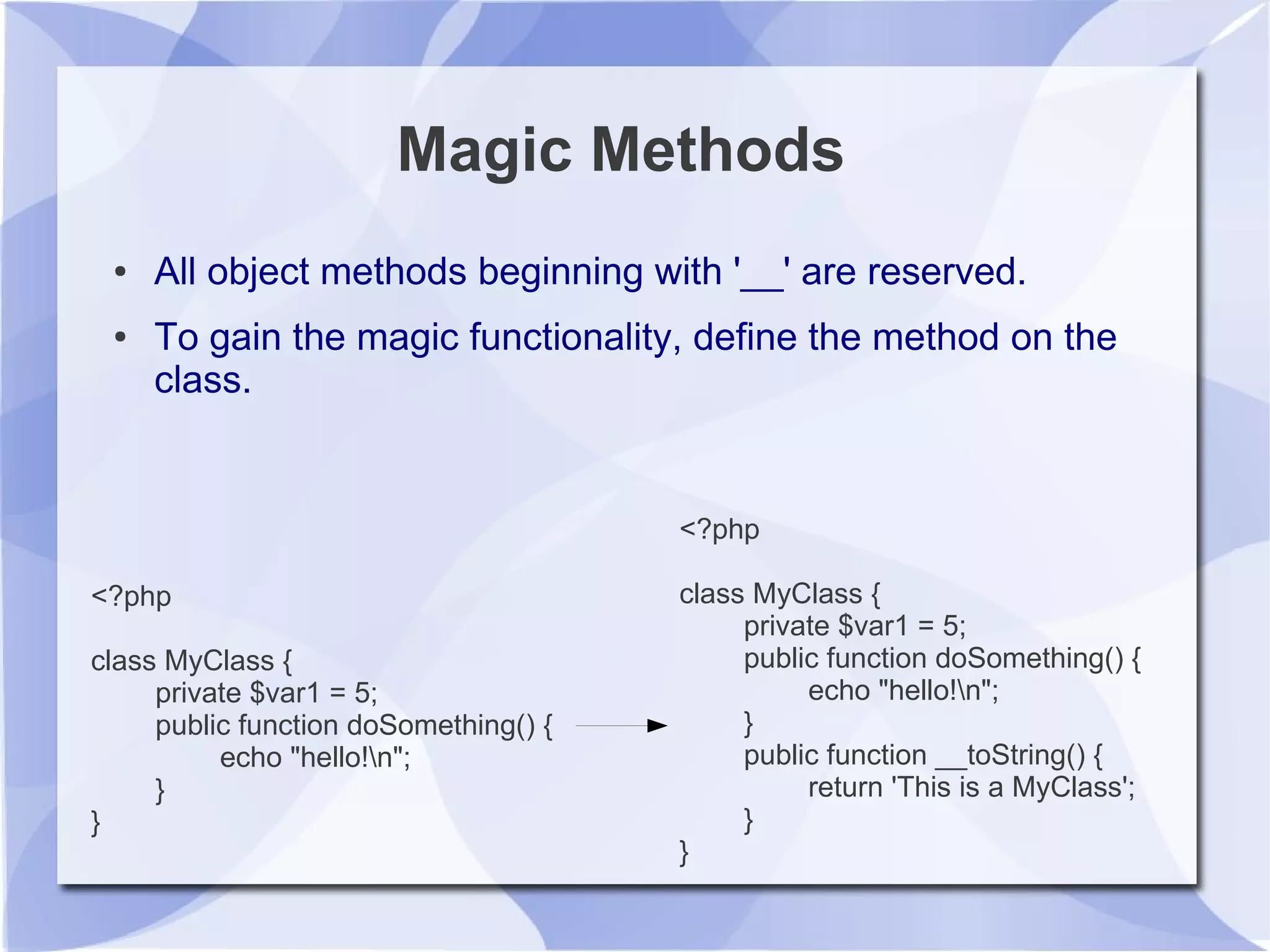
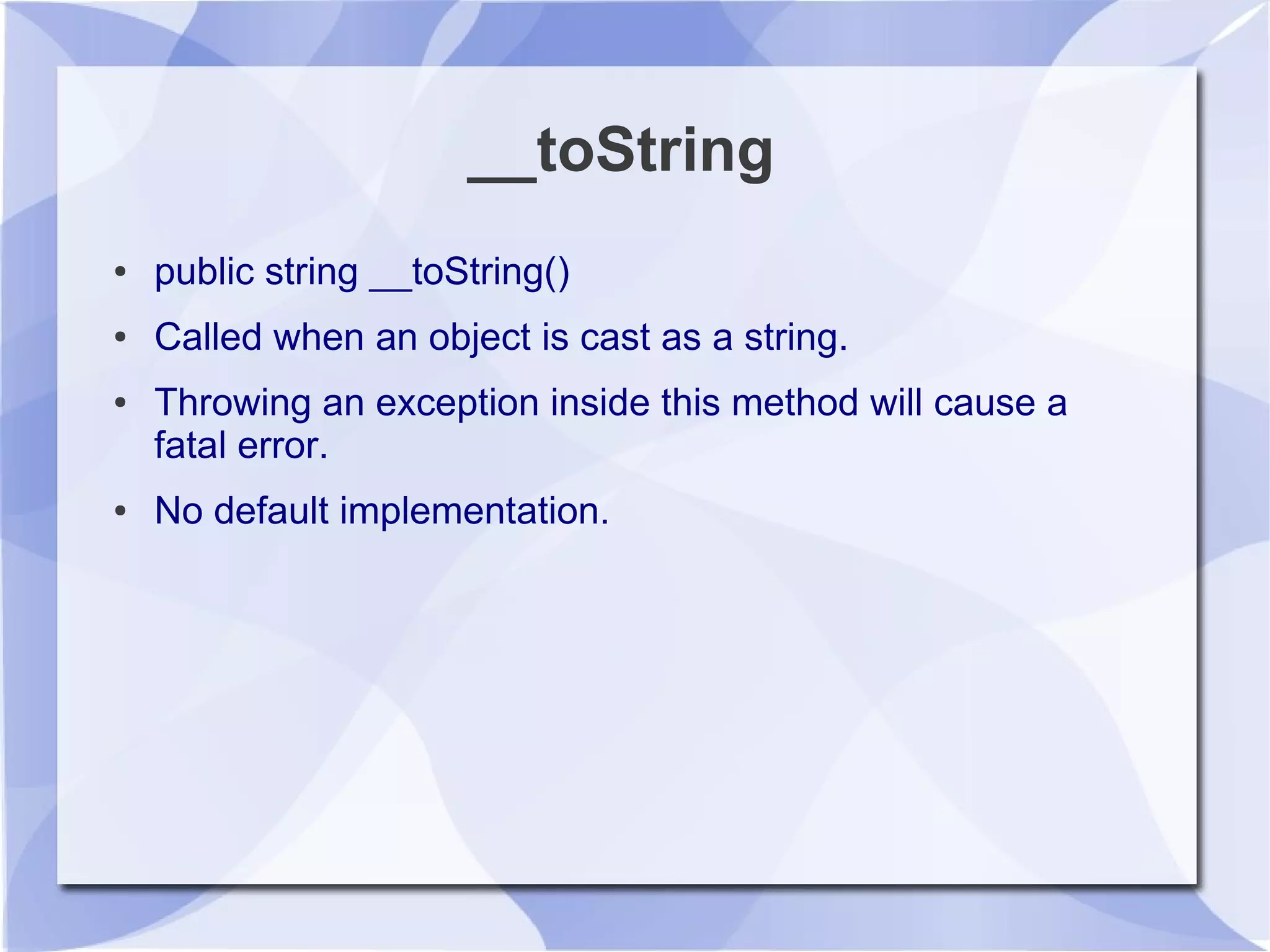
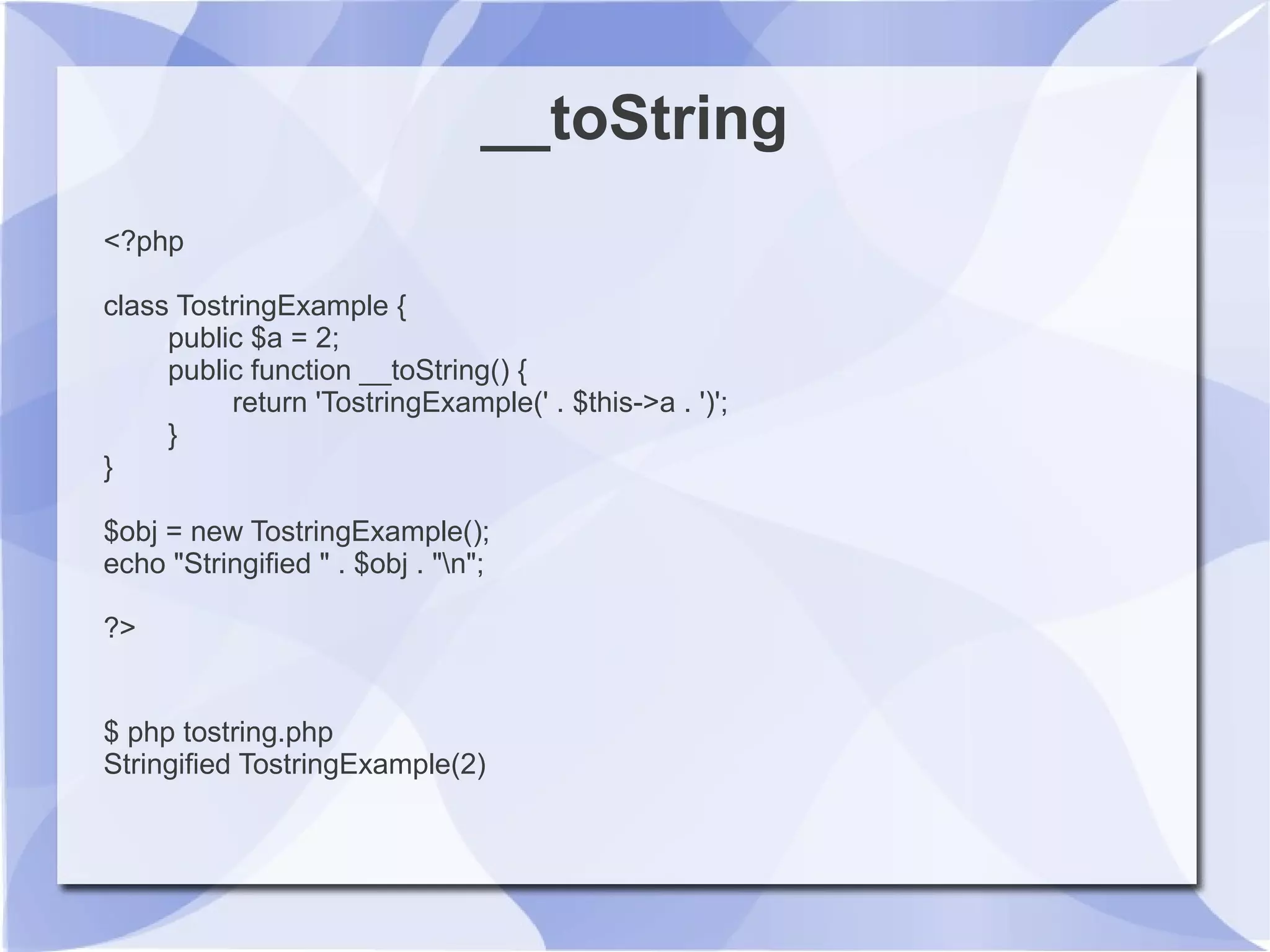
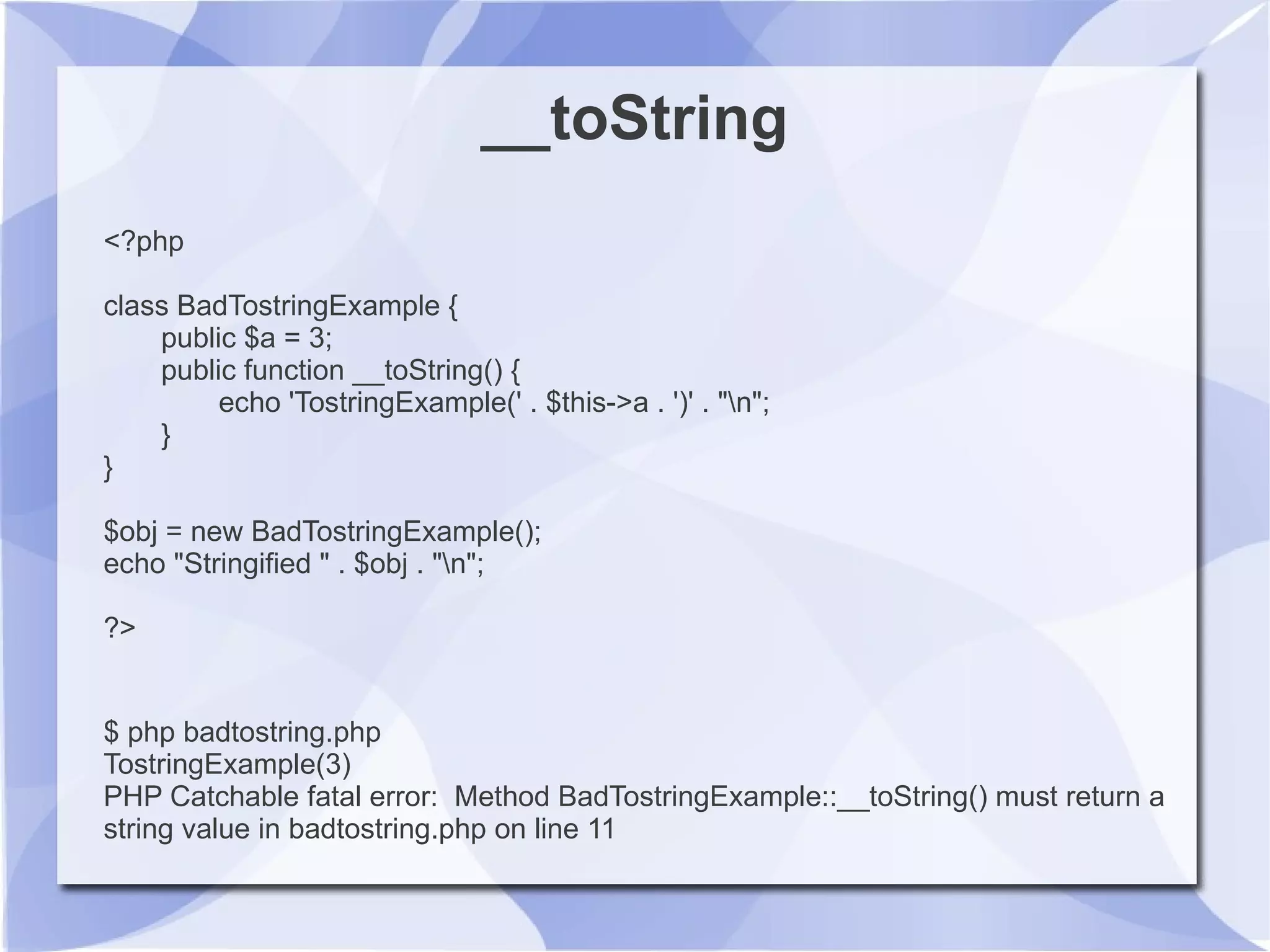
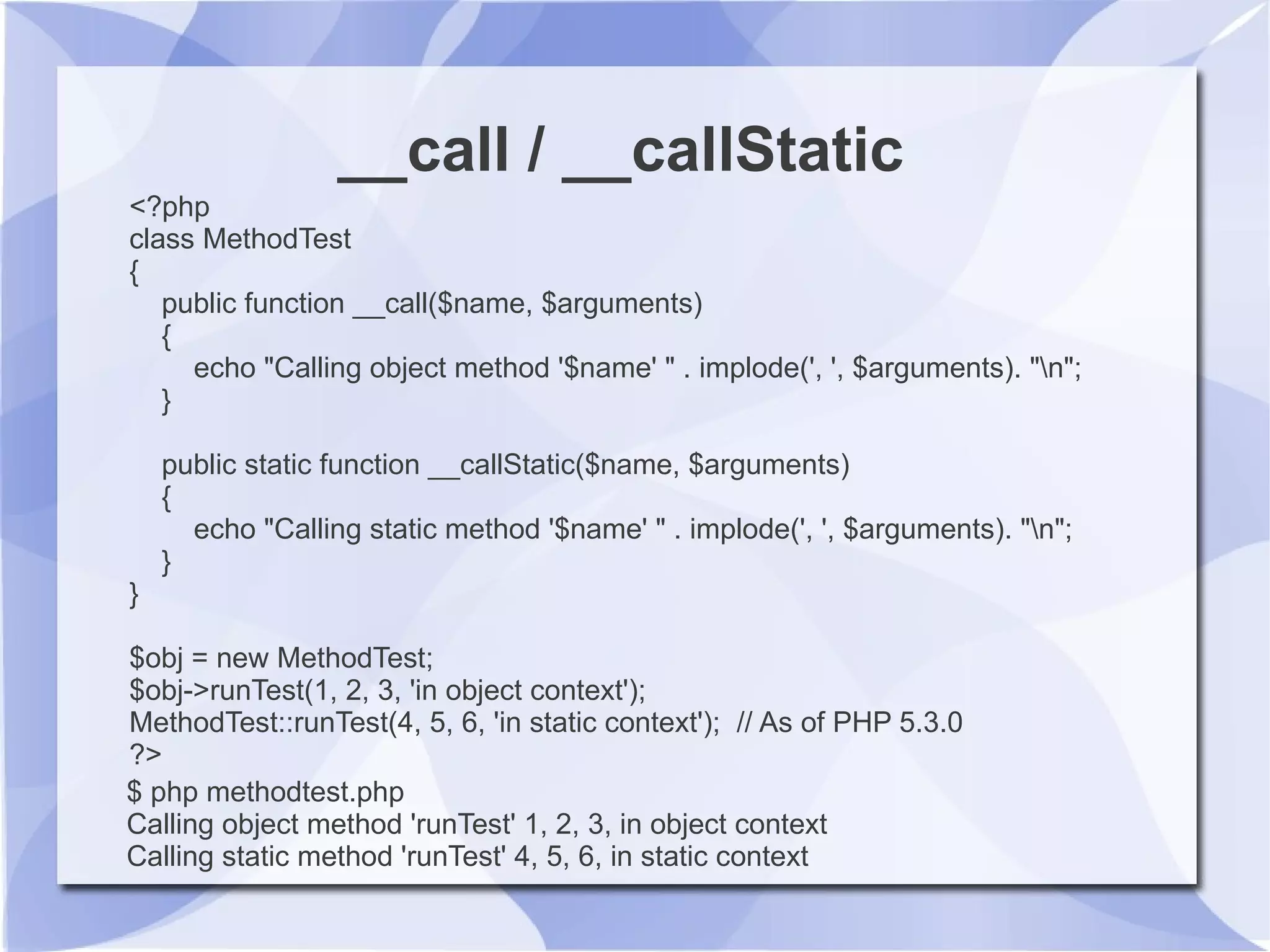
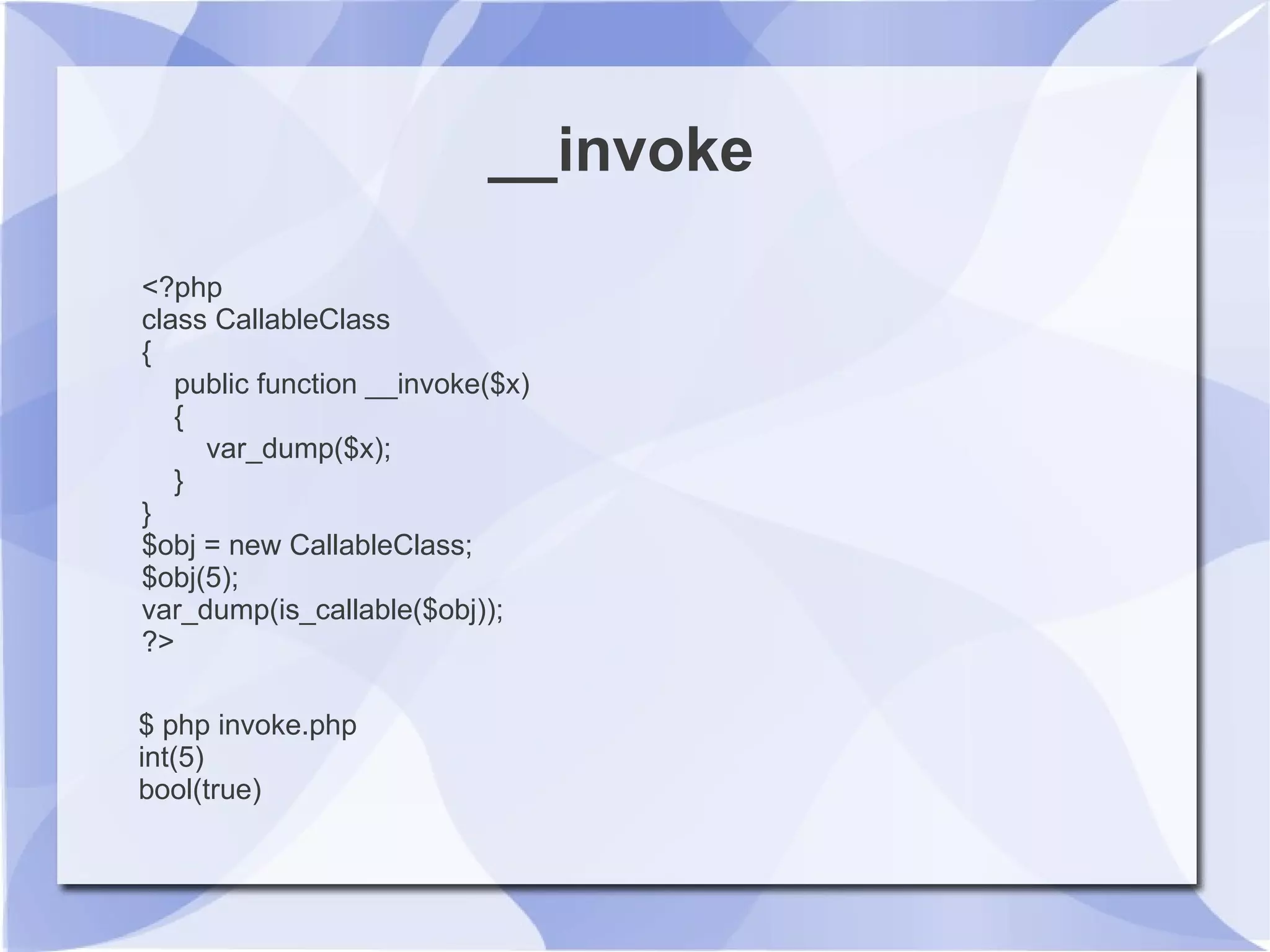
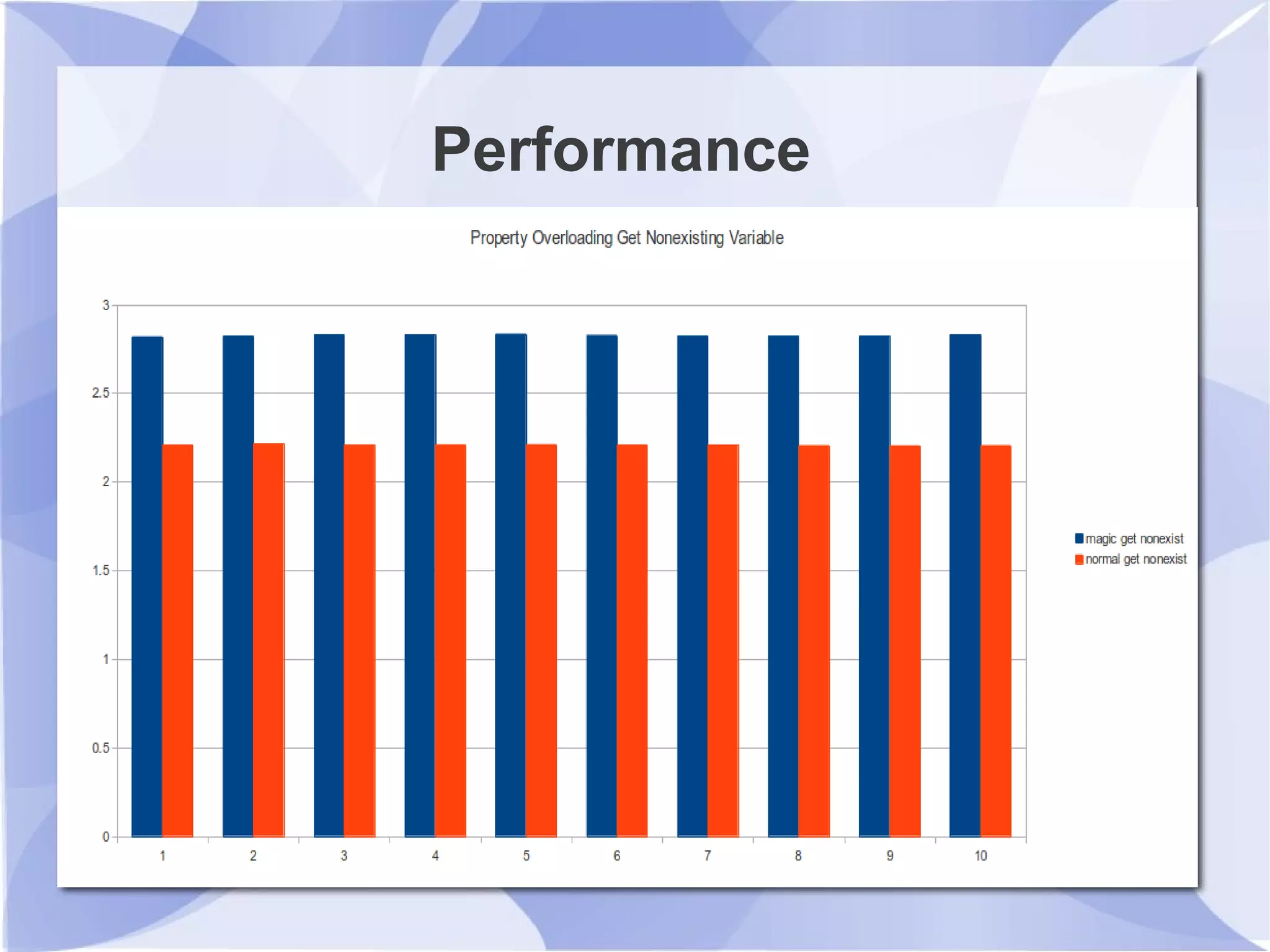
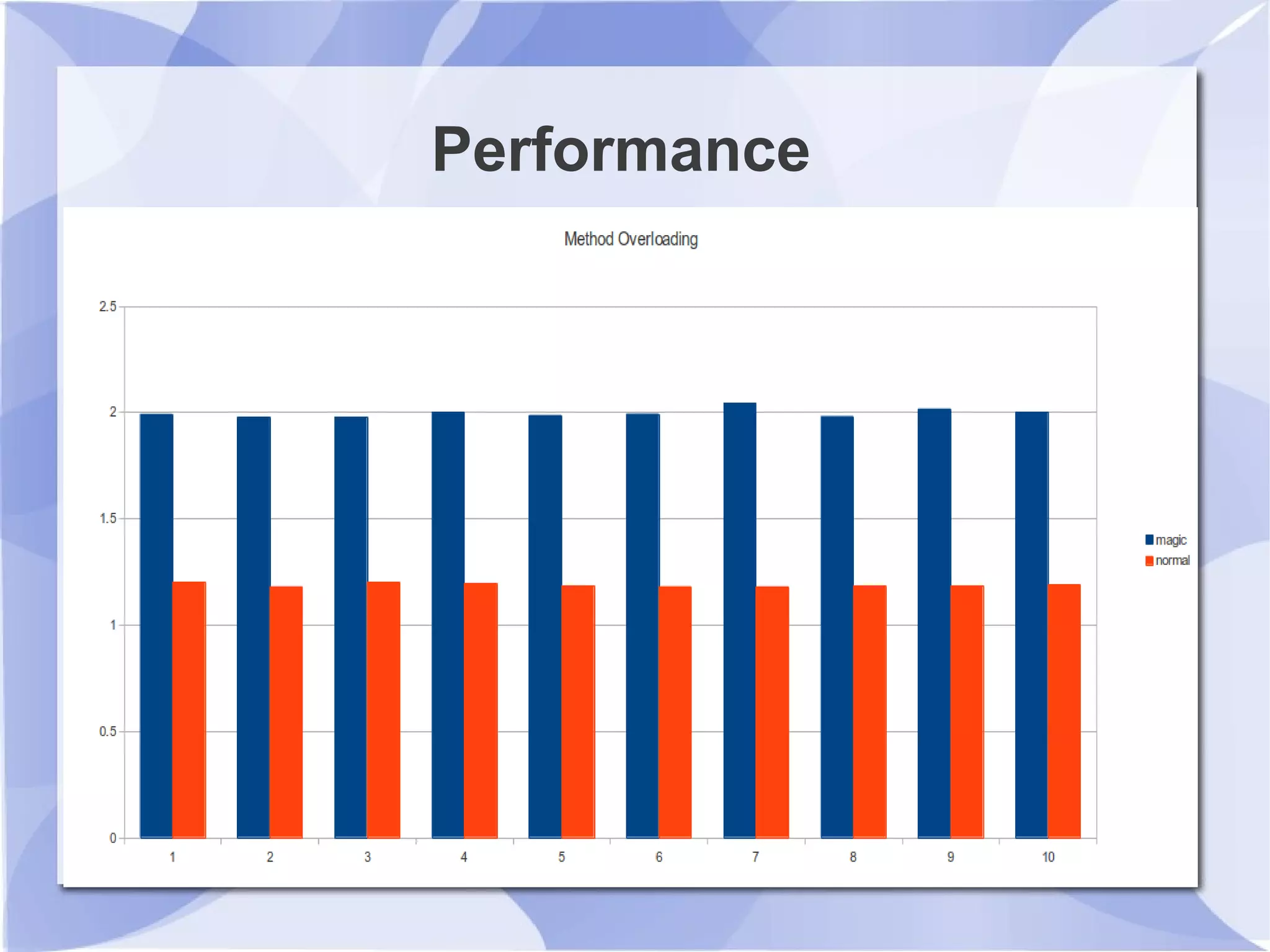
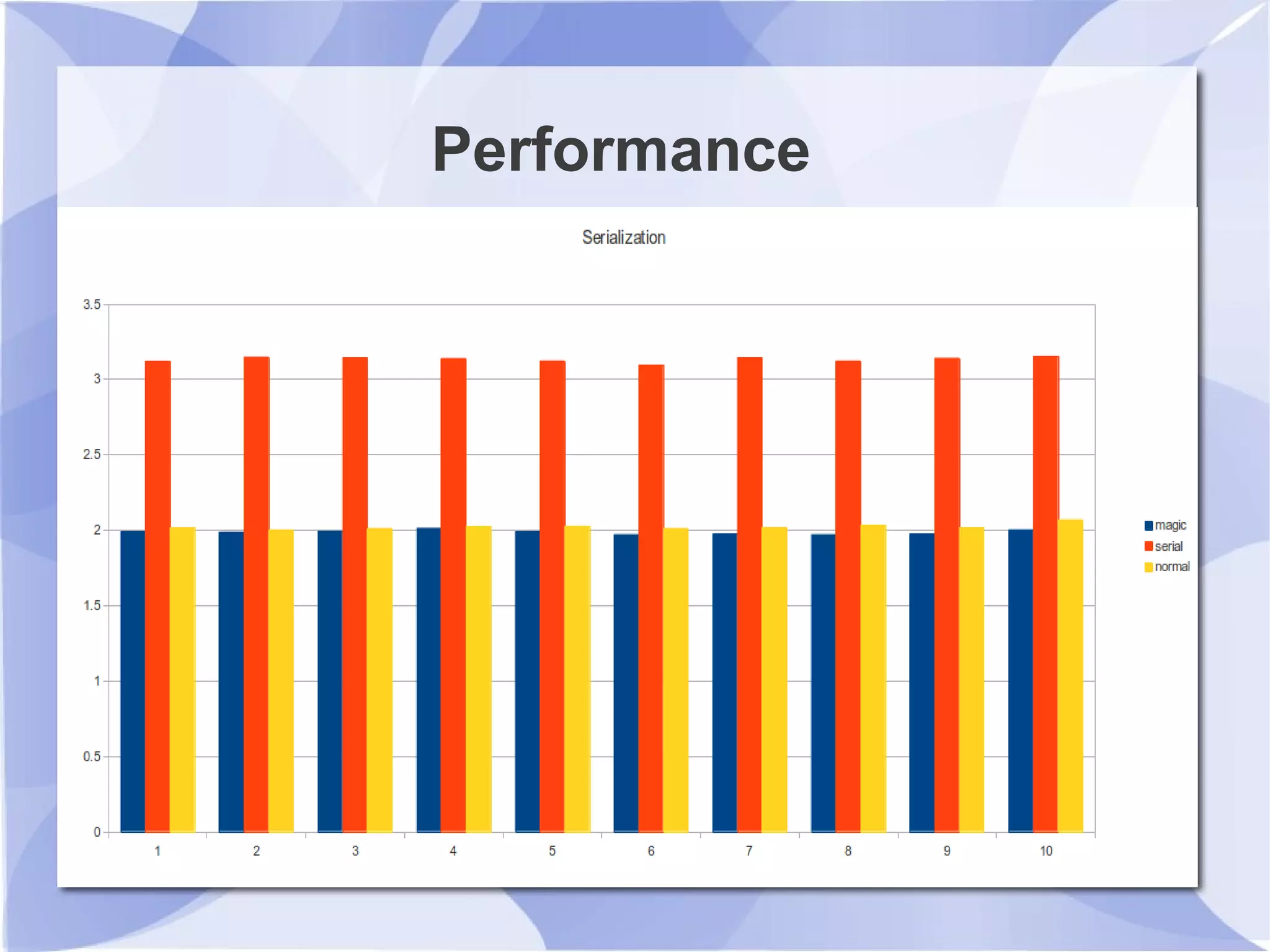
This document summarizes magic methods in PHP that allow for custom object behavior. It discusses methods for stringification (__toString()), object lifecycle (__construct(), __destruct()), property overloading (__get(), __set(), etc.), method overloading (__call(), __callStatic()), serialization (__sleep(), __wakeup()), cloning (__clone(), __set_state()), and object invocation (__invoke()). Examples are provided for each method. Performance benchmarks at the end show that magic methods have negligible overhead compared to normal method calls.