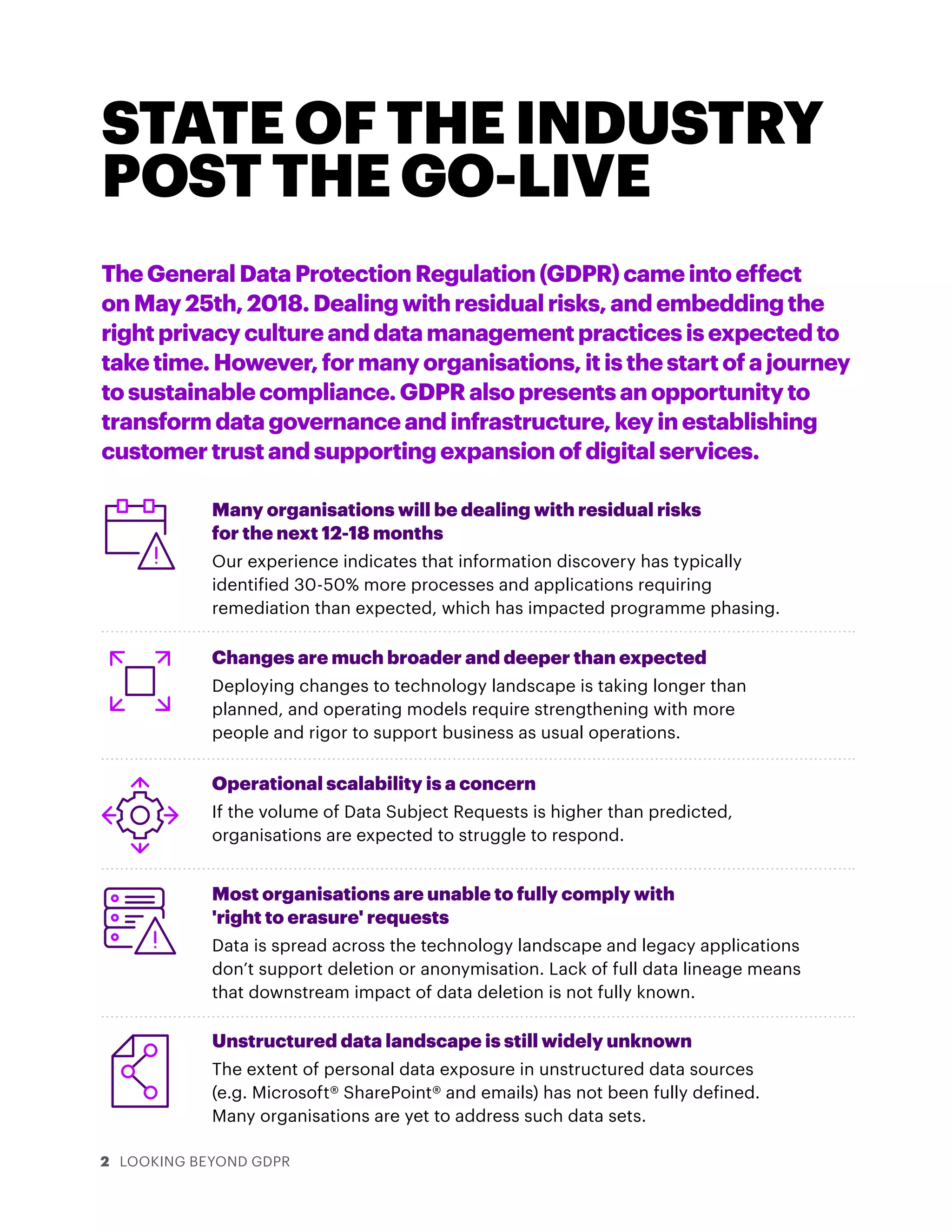
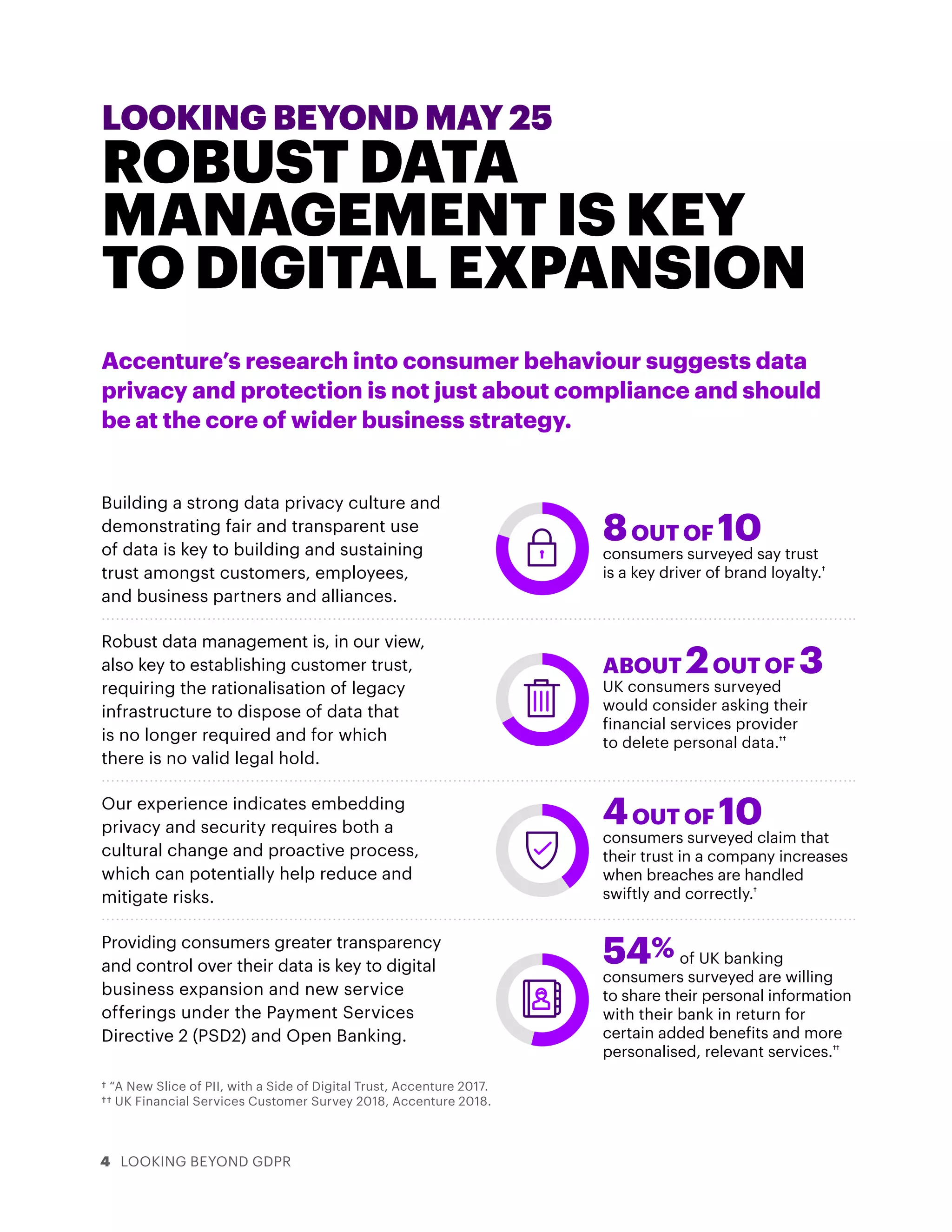
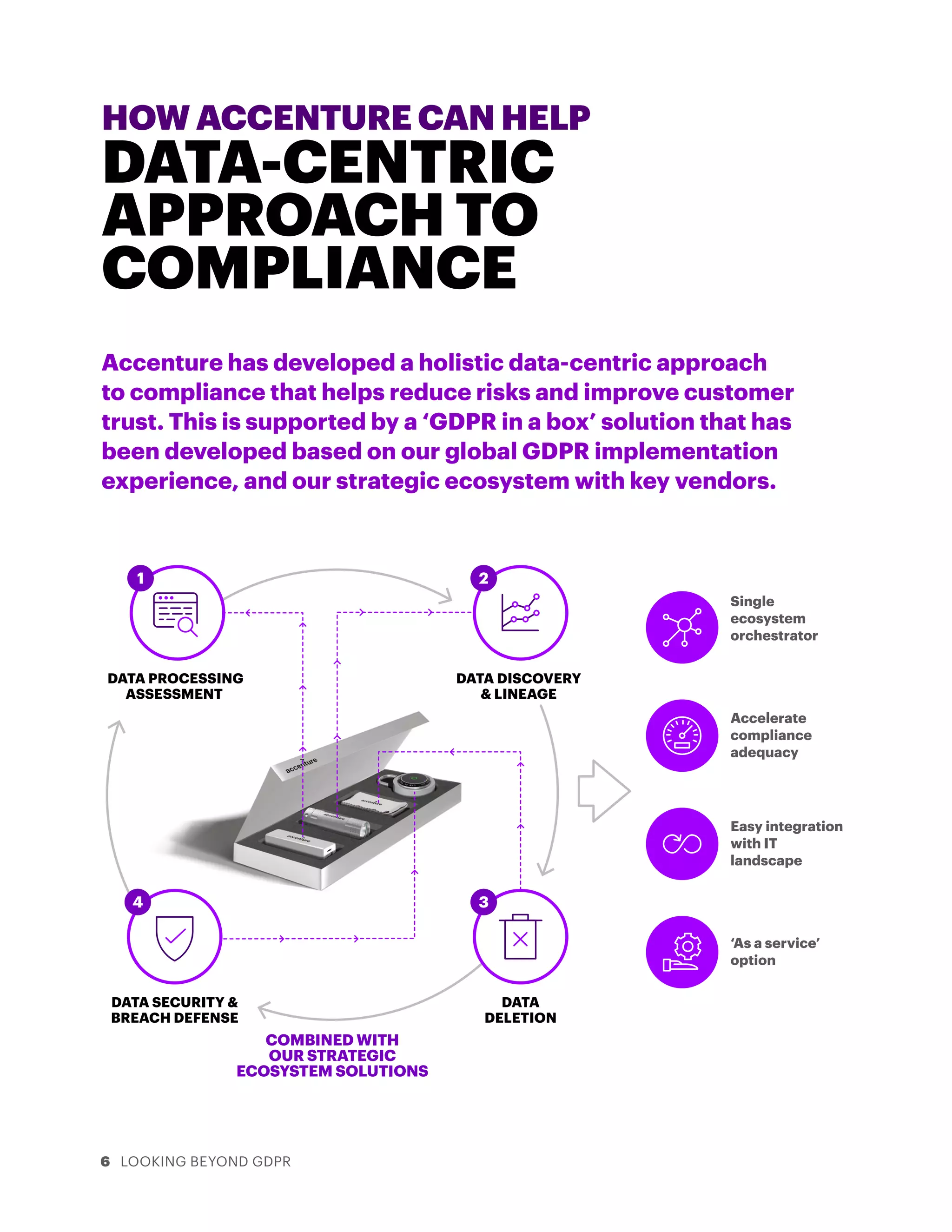
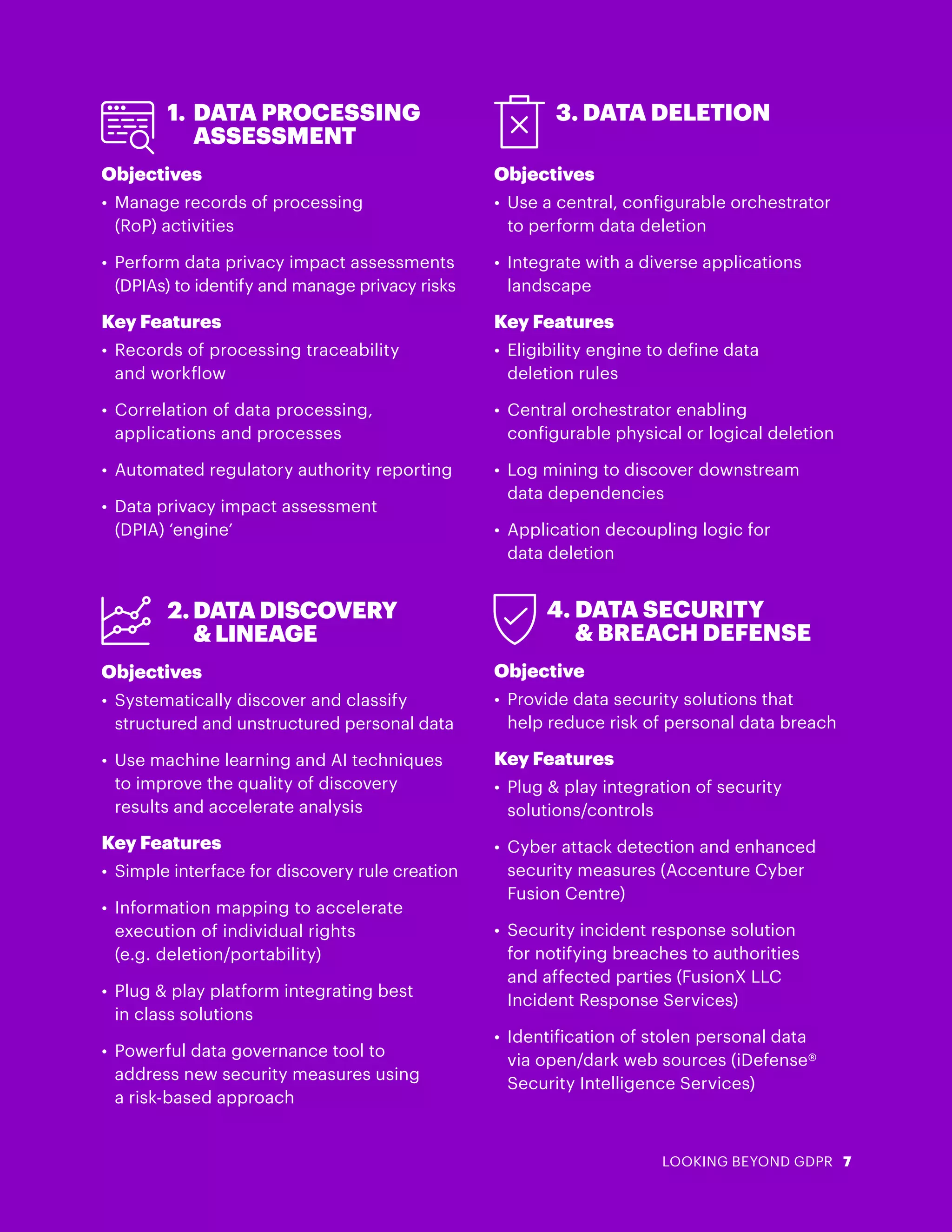
The document discusses organizations' experiences with GDPR compliance after the May 2018 deadline. It finds that many organizations are still dealing with residual risks and have uncovered more personal data than expected during their discovery processes. Specifically, organizations have struggled to fully comply with data deletion requests due to data being spread across systems without full lineage. The document advocates that organizations view GDPR not just as a compliance burden but as an opportunity to improve data governance, build customer trust, and enable digital expansion.