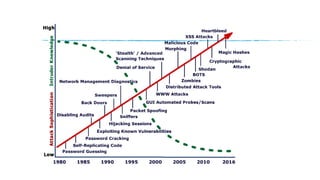
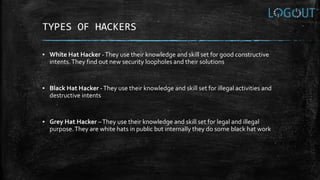
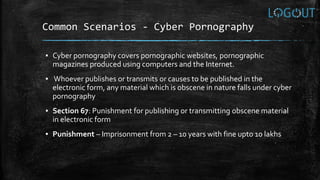
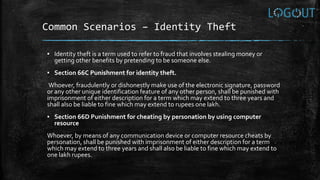
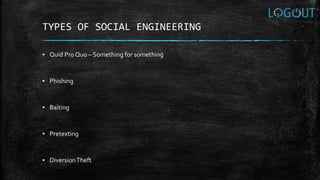
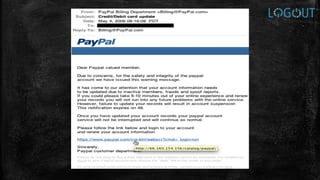
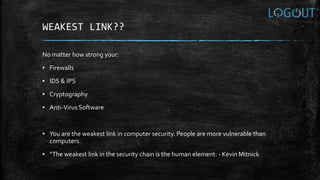
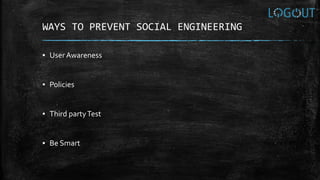
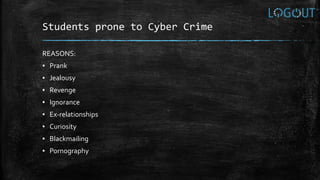
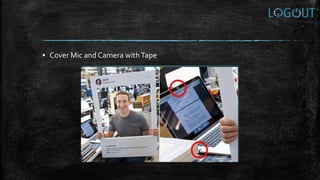
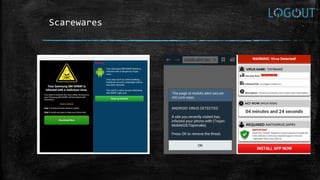
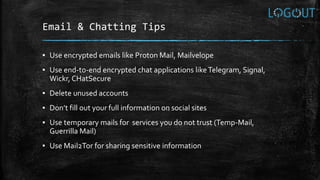
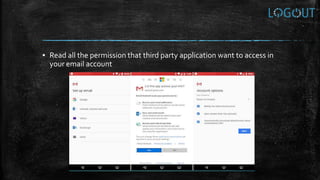
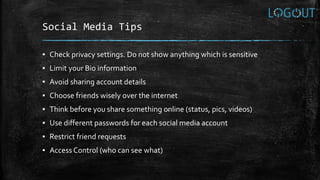
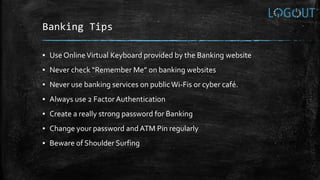
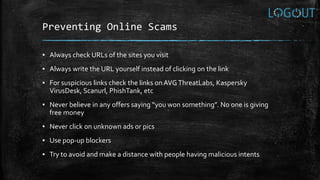
This document provides an introduction to cyber security fundamentals and awareness. It begins with an introduction by the author Apurv Singh Gautam, who works in network penetration testing and security. The document then covers topics like the need for security, what hacking is, types of hackers, hacking strategies, cyber crimes and associated laws, social engineering techniques and the human element as the weakest link. It concludes with many tips for safe computing, internet surfing, mobile security, password protection, email/chatting securely, using social media safely, banking securely and preventing online scams. The goal is to raise awareness about cyber security risks and best practices.